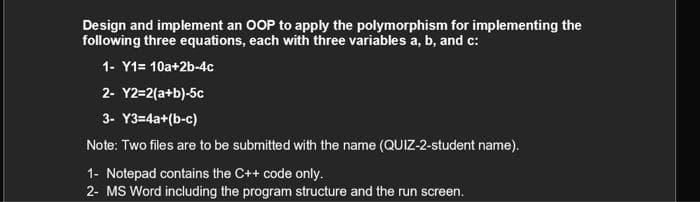
Design and implement an OOP to apply the polymorphism for implementing the following three equations, each with three variables a, b, and c: 1- Y1= 10a+2b-4c 2- Y2=2(a+b)-5c 3- Y3=4a+(b-c)
Q: Suppose that we are using PDDL to describe facts and actions in a certain world called JUNGLE. In th...
A: The Answer is start from step-2.
Q: 3 Evaluate the determinant for the following matrix: 1 1 O A. 8 о в. -2 O C.5 O D. -4
A: We are given a 2X2 matrix and we are going to find out its determinant. Please refer to the image fo...
Q: Describe some potential network layer services that a single packet may get. Do the same for a packe...
A: The following network layers can provide hypothetical services are: Guaranteed delivery Guaranteed ...
Q: These days, blockchain and cryptocurrency are all the rage. What is the fundamental technology of th...
A: let us see the answer:- Introduction:- Let us first under what is blockchain and cryptocurrencies:- ...
Q: Using the example of making a phone call, explain the functionality of Network APIs in a concise man...
A: Introduction: An API defines data structures and subroutine calls for adding new features to an exis...
Q: Given Prefix Expression: (а) * — + АВCD (b) + — а * ВCD Convert to INFIX!
A: Given Prefix Expression: (a) * -+ A B C D (b) +-a * BCD Given prifix expressions.
Q: Examine the basic ideas that apply to all sorts of software systems.
A: Fundamental principles of software systems: Manage the entire development of the software Manages t...
Q: what are the theorems of direct proof?
A: The theorems of direct proof is a way of showing the truth or falsehood of a given statement by a s...
Q: The use of the SSTF disk scheduling technique entails what risks?
A: The Answer for the given question start from step-2.
Q: How does one go about assigning an access key to a Button control?
A: Introduction: A button control is given an access key.
Q: Asymmetric and symmetric encryption techniques each have advantages and disadvantages. What factors ...
A: Intro The symmetric key cryptography as the name suggests is symmetric. What does this mean? This s...
Q: A positive whole number n > 2 is prime if no number between 2 and n (inclusive) evenly divides n Wri...
A: Python program: from math import sqrt def prime(n): divisor = 2 found = False max_diviso...
Q: S.edu/teaching/algorithms/). enotes the book by Dasgupta, Papadimitriou, and Vazirani uestion 1: Let...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Write the code of the ff C-Programming Write a program that will compute and compare the BMI of one ...
A: The inputs will be weight and height and then we calculate the BMI and use an if-else ladder to find...
Q: Create a java program that enters 5 adjectives. Count and print all the adjective that ends with the...
A: Algorithm: for (initialExpression; testExpression; updateExpression){ // body of the loo...
Q: Do you believe that wireless applications are the ones that stand to benefit the most from error cor...
A: Error correction It is best utilised with wireless apps or networks and is a terrific challenge. The...
Q: A computer has an average main memory access time of 60 ns. We want to reduce this time to 20 ns by ...
A: A computer has an average main memory access time of 60 ns. We want to reduce this time to 20 ns by ...
Q: Write a complete C++ program that asks the user to input information for at least 10 students. Use s...
A: Answer the above questions are as follows:
Q: .In a Merkle hash of depth 6 (with up to 64 leaves Lo...Le3) what are the complementary nodes for L1...
A: We need to find the complementary nodes for L19.
Q: What are the primary benefits of employing a database-driven approach?
A: Introduction: Strategic decisions are made based on data analysis and interpretation when a company ...
Q: What is the difference between a database management system and a database?
A: Introduction: Here we are required to explain what is the difference between a database management s...
Q: 6. Convert the decimal number 120.125 to IEEE 754 32-bit single precision floating point binary form...
A: 1. First, convert to the binary (base 2) the integer part: 120 and Divide the number repeatedly b...
Q: Using UML designs, create a diagram for the maintainability of a software app
A: UML design for the maintainbility of software app
Q: It is critical to distinguish between wireless networking issues that may exist when two stations ar...
A: Introduction: The primary issue is that everything emits the same network frequency, from cellphone...
Q: Use real-world examples to demonstrate data manipulation, forgeries, and online jacking.
A: The act of altering or adjusting data to spread the word about it more coordinated and decipherable ...
Q: in java eclipse ide can you insert the numbers in the code pleas
A: import java.util.Scanner; public class Main{ public static void main(String[] args) { Scanner ...
Q: Show the value that gets stored in the indicated variables(s) after the given sequence of statements...
A: Control structures are used to determine the path of execution and control the execution of instruct...
Q: What exactly is grid computing? What are the benefits and drawbacks?
A: Intro Grid computing is the method of using several computers to work together to accomplish common ...
Q: create an ERD and database creation script for a hypothetical conference of ornithologists. The name...
A: Her i explain the erd and write database script in simple format: ==================================...
Q: for the home page of your school's website. Write the CSS to configure a grid layout for the wirefra...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: What is mean by digital envelope.Explain its working.
A: To be determine: Describe about digital envelope
Q: "Machine learning is an empirical science," says the author. What is the meaning of this statement?
A: Introduction: Machine learning is the study of computer algorithms that learn on their own. Machine ...
Q: You will be building a linked list. Make sure to keep track of both the heac (1) Create three files ...
A: #include "ContactNode.h"//#include "ContactNode.cpp" #include <iostream>#include <string>...
Q: (C PROGRAMMING ONLY) Make a code with the string function of strcat (with user input) THE RE...
A: The required code for the C program using the strcat function is provided in the next step.
Q: Write a complete C++ program that asks the user to input information for at least 10 students. Use s...
A: INTRODUCTION: Here we need to write a C++ program.
Q: What is the purpose of the database reorganisation?
A: Introduction: A database is a logically ordered collection of data that is kept on a computer and ac...
Q: Need typed solution How many 10 bit strings have an equal number of 0's and 1's? How many have 8(on...
A: Total bit strings 10. Bit strings contains 0's and 1's.
Q: Many large organisations' database systems have been hacked, resulting in client information theft. ...
A: Database security: Database security is a set of tools, policies, and procedures for ensuring and ma...
Q: Is there a single mechanism that database designers should be aware of that has the potential to hav...
A: Introduction: Developers and DBAs work together to design the database. Database designs may be crud...
Q: Give the output of the following program segments. int x- 10; do X-x+ 6; System.out printin(x); whil...
A: The Question requires to Provide the Output Generated for the Given segment of Program Code : Given...
Q: 1)Handling the retransmitted packet for estimation timeout interval. 2)Play with WireShark.
A: Solution :: Packet retransmission is the re-sending of packets that have been damaged or lost duri...
Q: Make a list of at least ten methods for protecting your network from malicious and damaging assaults...
A: Introduction: A good network security system helps business reduce the risk of falling victim of da...
Q: How do you use the computer mouse to drag and drop a control to a different location on the form?
A: Answer: It's very easy to use the mouse to drag and drop. Let's start with some points to clarify th...
Q: When surfing online, you get some strange data on an apparently secure website, and you realize you ...
A: The answer is given below.
Q: What is the most significant distinction between mainframe operating systems and laptop operating sy...
A: Introduction: The following is the distinction between operating systems on a mainframe and operatin...
Q: с1 c2 c3 c4 xi1 0.4 0.2 0.7 0.0 xi2 0.1 0.1 01 0.3 xi3 0.5 0.7 0.2 0.7 -Use the cosine amplitude met...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Which data-hiding techniques are the most difficult obstacles for law enforcement officers to overco...
A: Intro Each country establishes law enforcement agencies to prevent and reduce crime.
Q: Referring to the ArrayBoundedQueue implementation in Chapter 4. What is the order of growth executio...
A: referring to the ArrayBoundedQueue implementation , what is the order pf growth execution time of th...
Q: are thinking of creating a new cryptocurrency, and you want the block chäin tổ have the wing paramet...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: What is the first step in dealing with a data corruption issue as a course of action? Computer scie...
A: Introduction: When data is corrupted, it becomes unusable, unreadable, or otherwise unavailable to a...
Step by step
Solved in 2 steps with 1 images

- In this problem, we wish to build a repository of functions that a developer can assemble to build a complex program. Therecan exist several versions of a function, each with its metadata. Function metadata includes the developer's full name and emailaddress, the language it is implemented in and a set of keywords related to the functionality fulfilled by the function. Theversions of a function can be represented as a directed acyclic graph. To manage the repository, we use a remote invocationbased gRPC that allows a client to interact with a server and execute the following operations:1. add_new_fn: to add either a brand new function or a new version to an existing function;2. add_fns: to add multiple functions streamed by the client (note that multiple versions of a function are not allowed);3. delete_fn: to delete a function (this might require reordering the versions of the function);4. show_fn: to view a specific version of a function;5. show_all_fns: to view all versions of a…Using Haskell or I will give negative on it Write a function which computes the image of R under a (ACST,p.12), where Ris a relation from A to B and a is an element of A based on the representationspecified in (*)I have to create a small library in the C programming language to do Minifloat The minifloat should be a code. sensible representation and stay consistent throughout a library.The internal representation (e.g. a struct) does not have to match the external representation (e.g. just a binary pattern, or a pointer to an abstract data type). do not return a pointer to a local static variables in a function. Instead, allocate on the heap with malloc and then return the pointer to that. The following pictrures are more of the requirements. 1. add - Add two Minifloat numbers and return the result. 2. mult - Multiply two Minifloat numbers and return the result. 1. Abstract data type e with proper header and source files. 2. sub - Subtract two Minifloat numbers and return the result. 3. div - Divide two Minifloat numbers and return the result. 4. Input checking and rejection of out-of-bounds or improperly formatted Minifloat numbers by returning predefıned special values. These values should…
- In early implementations of FORTRAN language, a compiler may choose to use staticallocation (i.e., allocation in the static area) for local variables and parameters, effectively arrangingfor the variables of different invocations to share the same locations, and thereby avoidingany run-time overhead for creation and destruction of stack frames. However, such an implemen-tation changes the meaning of recursive function calls.Provide a simple example and explain how its meaning changes under the “FORTRAN” semanticsas stated above, compared with standard semantics found in languages like C, Python, and Java.Make a C++ program that incorporates recursion to solve the following problem. Theprogram has to compile and execute under the UNIX gcc or g++ environments.For this program have it accept a sequence of k characters from the user and use the characters to produce a k concentric squares. Assuming an index origin of 1, the outermost square is made up of the letter a[k], thesquare inside that is made from the letter a[k-1], the square inside that is made from the lettera[k-2], and so on, with the innermost square made from the letter a[1]. For example, if k=5, andthe values of a are("B","U","C","K","Y") then the executed program should display:Y Y Y Y Y Y Y Y YY K K K K K K K YY K C C C C C K YY K C U U U C K YY K C U B U C K YY K C U U U C K YY K C C C C C K YY K K K K K K K YY Y Y Y Y Y Y Y YMake a C++ program that incorporates recursion to solve the following problem. Theprogram has to compile and execute under the UNIX gcc or g++ environments.For this program have it accept a sequence of k characters from the user and use the characters to produce a k concentric squares. Assuming an index origin of 1, the outermost square is made up of the letter a[k], thesquare inside that is made from the letter a[k-1], the square inside that is made from the lettera[k-2], and so on, with the innermost square made from the letter a[1]. For example, if k=5, andthe values of a are("B","U","C","K","Y") then the executed program should display:Y Y Y Y Y Y Y Y YY K K K K K K K YY K C C C C C K YY K C U U U C K YY K C U B U C K YY K C U U U C K YY K C C C C C K YY K K K K K K K YY Y Y Y Y Y Y Y Y Please make main the first function in the program by protyping any other functions, and if possible make the concentric squares recursive situation its own class.
- One of the most difficult concepts to grasp is that of abstract data types (ADTs). Do ADTs have any advantages? How can the concept of heredity aid in issue solving?Write a small library in the C programming language to do Minifloat (Links to an external site.) (8-bit binary floating-point numbers) operations. Notes You have to come up with a sensible representation and stay consistent throughout a library. The internal representation (e.g. a struct) does not have to match the external representation (e.g. just a binary pattern, or a pointer to an abstract data type). Be careful of memory leaks. For example, do not return a pointer to a local static variables in a function. Instead, allocate on the heap with malloc and then return the pointer to that. Minimum requirements Meeting these requirements will collect the regular points. add - Add two Minifloat numbers and return the result. mult - Multiply two Minifloat numbers and return the result.The idea of "abstract data types" (ADTs) is vague. Do ADTs have any advantages? What role does the concept of heredity have in resolving issues?
- give a condition for the situation when it is possible to share aFinite State Machines substructure among multiple FSM structures. The condition should be necessaryn and sufficient. Give at least two reasons why shared sub-FSMs are beneficial.(a) Design a PDA P that recognizes the language L = {x#y : x, y ∈{1}∗∧ |x| > |y|} over the alphabet Σ = {1, #}. Draw a state diagram according to the format of the textbook and the slides,i.e., start with an empty stack. Furthermore, ensure that every move either pushes or pops, but not both.(b) Obviously, you can easily create a CFG for such a trivial language like L. Here, you are asked to not just produce any CFG for L, but follow the procedure PDA-to-CFG to obtain such a grammar. Even for such a simple PDA, the grammar would be a bit lengthy. Therefore, we make one modification. You don’t have to write any rules that involve variables that generate the empty language. Such rules would have no effect anyway.Memory usage. Compare the memory usage of BST with the memory usage of BinarySearchST and SequentialSearchST for N key-value pairs, under the assump- tions described in Section 1.4 (see Exercise 3.1.21). Do not count the memory for the keys and values themselves, but do count references to them. Then draw a diagram that depicts the precise memory usage of a BST with String keys and Integer values (such as the ones built by FrequencyCounter), and then estimate the memory usage (in bytes) for the BST built when FrequencyCounter uses BST for Tale of Two Cities.











