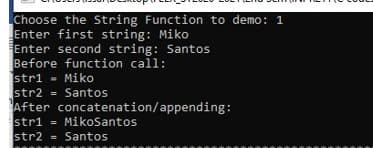
(C PROGRAMMING ONLY) Make a code with the string function of strcat (with user input) THE REQUIRED OUTPUT IS INDICATED IN THE PICTURE. (THE OUTPUT SHOULD BE EXACTLY LIKE IN THE PICTURE)
Q: Need typed solution How many 10 bit strings have an equal number of 0's and 1's? How many have 8(on...
A: Total bit strings 10. Bit strings contains 0's and 1's.
Q: Show the value that gets stored in the indicated variables(s) after the given sequence of statements...
A: The answer is given below.
Q: Please answer it in Python Write a function convertir_liste that takes as an argument a list of str...
A: Python Program: # Given list of stringsstringList = ['1', '12.3', '4.12'] # Display the given listpr...
Q: Write a function, to be included in an unsorted linked list class, called replaceItem, that will rec...
A:
Q: The edge-detection function ( detectEdges ) described in Chapter 7 and shown below returns a black a...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: rite an AVR assembly program that verifies the functionality of the rotations as described in the AV...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: Start Page Microsaft Visual Basic 2010 Express OVisual Basic 2010 Express Get Started Latest News we...
A: 1. Standard bar position changer tool (the three vertical dots) 2. Title bar 3. Menu bar 4. Start Ne...
Q: P7. Consider the network fragment shown below. x has only two attached neighbors, w and y. w has a m...
A:
Q: Create a HTML page called q3.html. This page should contain a HTML form that itself contains three t...
A: The code is given below.
Q: The most effective way to run several operating systems on a single computer at the same time is to ...
A: Introduction: Virtualization is a computing technique that makes use of virtualized hardware and so...
Q: I'm creating a python script that needs to parse a master boot record.
A: Solution: Python code for parsing a master boot records code: #!/usr/bi#!/n/python3 import struct ...
Q: 1)Handling the retransmitted packet for estimation timeout interval. 2)Play with WireShark.
A: Solution :: Packet retransmission is the re-sending of packets that have been damaged or lost duri...
Q: C language. Design Pattern Write a description of the Factory design pattern credit card: Your as...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: Create a Python program that will repeatedly ask the user to enter integers (positive integers only)...
A: As per the requirement program is completed. Algorithm: Step 1: Read the numbers from the user up to...
Q: Given the data word 10100111110 and the divisor 10111, a. Show the generation of the codeword at the...
A: Below is the answer to above question. I hope this will meet your requirement....
Q: u will create a class “Node” with the following private data attributes: line – line from a file (st...
A: #include "linkedlist.h"#include <iostream>#include <fstream> int main() {// create linke...
Q: Determine the outcome of the following expressions as either TRUE or FALSE 7 5 && 7 == 2 - _______...
A: Introduction: A logical operator is a symbol or word used to connect two or more expressions such t...
Q: What's the difference between Stored Procedures and Scripts? What is the purpose of each? How does e...
A: Introduction: A stored procedure (also known as a proc, storp, sproc, StoPro, StoredProc, StoreProc,...
Q: What exactly is a device driver, and how does it function?
A: Intro Driver for a device A device driver is a computer application that is used to run or control a...
Q: start Get positive integer from user, call it A. Get positive integer from user, call it B. C = A B ...
A: According to me correct answer will be Option 4. A**A EXPLANATION answer of flow chart will be in ex...
Q: 1.1. 1.2. B 2. Use Dijkstra's algorithm to find the shortest path from vertex, (a) 'A' to 'L', (b) 2...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: What are some of the applications of SSH? Make a list of SSH acronyms and define them briefly. Comp...
A: Introduction: SSH is a cryptographic protocol that allows servers to communicate securely over an in...
Q: Write a program that lets the user click the refresh button to display four cards from a deck cards.
A: import javafx.application.Application; import javafx.stage.Stage; import javafx.scene.Scene; import ...
Q: Get a string of alphabetic characters and return the value of the counter variable. The counter is i...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: ask 3. Remove white spaces and special symbols rogram asks user to input a string to remove white sp...
A: import java.util.Scanner; public class Main{ public static void main(String[] args) { Scanner ...
Q: Write a class named TestScores. The class constructor should accept an array of test scores as its a...
A: c ++ code is an given below : #include <iostream> using namespace std; class TestScores { priv...
Q: What exactly is translation software, and how does it function? Give examples of the many categories...
A: Introduction: Translation software, in the context of text translation, refers to any program that a...
Q: Fredwick wants a program in which he can continuously enter Some positive integer values and the pro...
A: Write a C++ program in which the user can continuously enter some positive integer values and the pr...
Q: It is unknown what factors had a part in the evolution of computer security into the present era of ...
A: Intro The elements listed below have aided in the growth of computer security into current informat...
Q: For the following Computer Science question: Does the following Set-UID program have a race conditio...
A: The Answer for the given question in step-2.
Q: Task 2. Capitalize and reverse Program asks user to input a string to capitalize and reverse each wo...
A: Language C++ #include<bits/stdc++.h> using namespace std; int main() ...
Q: 2.15 (Geometry: area of a hexagon) Write a program that prompts the user to enter the side of a hexa...
A: Given: To write a python program to find the area of hexagon.
Q: Write an expression using Boolean operators that prints "Eligible" if user_age is greater than 17 an...
A: Boolean Operars: Boolean operators only work with the boolean values 0and or true or false. Boolean ...
Q: are thinking of creating a new cryptocurrency, and you want the block chäin tổ have the wing paramet...
A: Hey there, I am writing the required solution of the questin mentioned above. Please do find the sol...
Q: a. Ifa new class Extend PartTime and FullTime class. What type of inheritance is used here for exten...
A: Multiple inheritance is used here for extending these classes. No, it is not possible to do it in JA...
Q: What is your understanding of Data security?
A: Kindly Note: As per our guidelines we are supposed to answer first question. Kindly repost other que...
Q: What security flaws are exploited and how may these issues be addressed in the future in the case of...
A: Introduction: Data damage is defined as any decrease in integrity or data acquisition. Damage to a c...
Q: For any given AVL tree T of n elements, we need to design an algorithm that finds elements x in T su...
A: B) O(mlogn)
Q: Show the value that gets stored in the indicated variables(s) after the given sequence of statements...
A: Control structures are used to determine the path of execution and control the execution of instruct...
Q: Which of the flip-flops accurately represents computer memory? Computer science
A: Introduction: Data storage elements include flip-flops and latches. A flip-flop is a device that kee...
Q: Write the output of the following program segment: fort int i-1:i 5: i if i- 3) contimme; System.out...
A: Let's understand functionality of continue statement in Java: Continue statement is used in loops to...
Q: What is social engineering, and how is it used by cybercriminals? Without any further explanation
A: Given: social engineering and how cybercriminals use this technique?
Q: Java Programming Lab I want to get the number of duplicates elements which is present in an user ent...
A: Write a JAVA program to input the elements of an array and find the number of duplicate elements pre...
Q: Design a PDA which will accept the language consisting of strings over the alphabet ∑={a,b} where nu...
A: Task : L = {w, w belongs to {a,b}* and number of a's and b's are not equal to each other} Create t...
Q: In a lucky draw contest, there is a total of 1000 participant Each participant is given a registrati...
A: ALGORITHM:- 1. Take the input from the user. 2. Generate the random number. 3. Check if both are equ...
Q: Write a Python program to show the use of the isinstance() function to check whether the value 0.5 i...
A: I give the code in Python along with output and code screenshot
Q: Define a function named sharpen that performs this operation: The function should expect an image an...
A: Screen shot of code:
Q: make a c++ program and compute for this A jogger starts a course at a steady rate of 8 kph. Five mi...
A: Introduction: Here we are required to create a C++ program that will calculate the time will the sec...
Q: 6. You are going to play WAR against the computer. This can be super basic. You can have the user "d...
A: Generate a random number from 2 to 14 (where 11 represents J, 12 represents Q, 13 represents K, 14 r...
Q: Do parallel/distributed databases have a distinct advantage over centralized ones?
A: Let's see the solution
(C
Make a code with the string function of strcat (with user input)
THE REQUIRED OUTPUT IS INDICATED IN THE PICTURE. (THE OUTPUT SHOULD BE EXACTLY LIKE IN THE PICTURE)
Step by step
Solved in 3 steps with 2 images

- most_frequent_word() takes a string as the input parameter and returns two values; the word that appears most frequently in that string and the total number of times that word appears in that string. In case of a tie, return the first word that appears in the string. Hint: you can use the unique_words function that you wrote in (4). Sample outputs:>>> data = “chapter one hottest day summer so far drawing close drowsy silence lay over large square houses privet drive cars usually gleaming stood dusty drives lawns once emerald green lay parched yellowing”>>> word = most_frequent_word(data)>>> print(word)('lay', 2)>>> data_2 = "a cat in a hat and a big black bear on a big black rug">>> word = most_frequent_word(data_2)>>> print(word)('a', 4)Choose one answer from the following options: Question: Which function would be most useful for determining if a certain word is contained in a string representing a sentence? Answers: a) strcspn b) strchr c) strstr d) strrchrexcel vba Program a function that removes all occurrences of the selected character from the text string. Therefore, the function will have two parameters, one for entering a cell with text and the other for entering a character that needs to be omitted.
- Given helper function: (Hint: This function is to be used to complete the docstring of the function below)def is_number(value: str) -> bool: """Return True if and only if value represents a decimal number. >>> is_number('csc108') False >>> is_number(' 108 ') True >>> is_number('+3.14159') True """ return value.strip().lstrip('-+').replace('.', '', 1).isnumeric()QUESTION: Complete the docstring using the information provided. def convert_data(data: List[list]) -> None: """Convert each string in data to an int if and only if it represents a whole number, and a float if and only if it represents a number that is not a whole number. >>> d = [['abc', '123', '45.6', 'car', 'Bike']] >>> convert_data(d) >>> d [['abc', 123, 45.6, 'car', 'Bike']] >>> d = [['ab2'], ['-123'], ['BIKES', '3.2'], ['3.0', '+4', '-5.0']] >>> convert_data(d) >>> d…IN C Programming Language...THANKS Write a function that replaces a given string with ‘*’ within a given text if that string is a full word, or the beginning or end of a word. Test your function with a suitable main.ATM machines allow 4 or 6 digit PIN codes and PIN codes cannot contain anything but exactly 4 digits or exactly 6 digits. Your task is to create a function that takes a string and returns true if the PIN is valid and false if it's not. Examples validatePIN("1234") ➞ true validatePIN("12345") ➞ false validatePIN("a234") ➞ false validatePIN("") ➞ false Notes ● Some test cases contain special characters. ● Empty strings must return false.
- Write a function isPar to test if a string is a palindrome. Multiple functions.isPar "radar" → true isPar "aaba" → falseA string is passed as argument to a function named hS, the function also returns a string which is the first half of the string given as argument, i.e. from index 0 to l/2 where l is the length of the string. Language: C++1. strcmp( str1, str2 ); returns the value 0 if str1 and str2 are equal. a. true b. false 2. The strlen function returns the _________. a. number of characters in a string, including the null terminator b. number of characters in a string, not including the null terminator
- insert_substrings_into_string(s, substrs): This function takes a string s and a string substrs. The substrs string will contain 0 or more comma-separated substrings. The string s will contain text with 0 or more special placeholder character sequences. These placeholder character sequences will always begin with the percent character %, followed by one or more digits (which form a non- negative number). The function will create a new string from the original string s where all the placeholder character sequences in s are replaced by the substrings in the string substrs. The placeholder %0 should be replaced by the first substring in substrs (i.e., everything before the first comma, if such a comma exists). The placeholder %1 should be replaced by the second substring in substrs (i.e., everything between the first and second comma, if such a comma exists), and so on. The new string should then be returned. Note: If a placeholder sequence refers to an invalid index (e.g., %10 when there…A 3-character string, userString, is read from input. Replace the first character in userString with '=' if the first character is alphabetic. Replace the second character in userString with '$' if the second character is alphabetic. If neither condition is true, userString is not changed. Ex: If the input is gwv, then the output is: =$v #include <iostream>#include <string>#include <cctype>using namespace std; int main() { string userString; getline(cin, userString); /* Your code goes here */ cout << userString << endl; return 0;}#include <iostream>#include <string>#include <iomanip>using namespace std;// structurestruct Hat{string brand;string color;float price;};// Customer structurestruct Customer{string fullName ;int age ;Hat hat; // Hat structure (nested in Customer)};int main(){// declare 5 variables of CustomerCustomer customer_1,customer_2,customer_3,customer_4,customer_5;cout<<"Welcome to Hats For U!\n";cout<<"Customer 1\n";cout<<"Enter customer's Full Name: ";getline(cin,customer_1.fullName);cout<<"Enter customer's age: ";cin>>customer_1.age;cout<<"Enter the brand of hat: ";cin>>customer_1.hat.brand;cout<<"Enter the hat color: ";cin>>customer_1.hat.color;cout<<"Enter the hat price(RM): ";cin>>customer_1.hat.price; cout<<"Hat 2\n";cout<<"Enter customer's Full Name: ";getline(cin,customer_2.fullName);getline(cin,customer_2.fullName);cout<<"Enter customer's age:…



