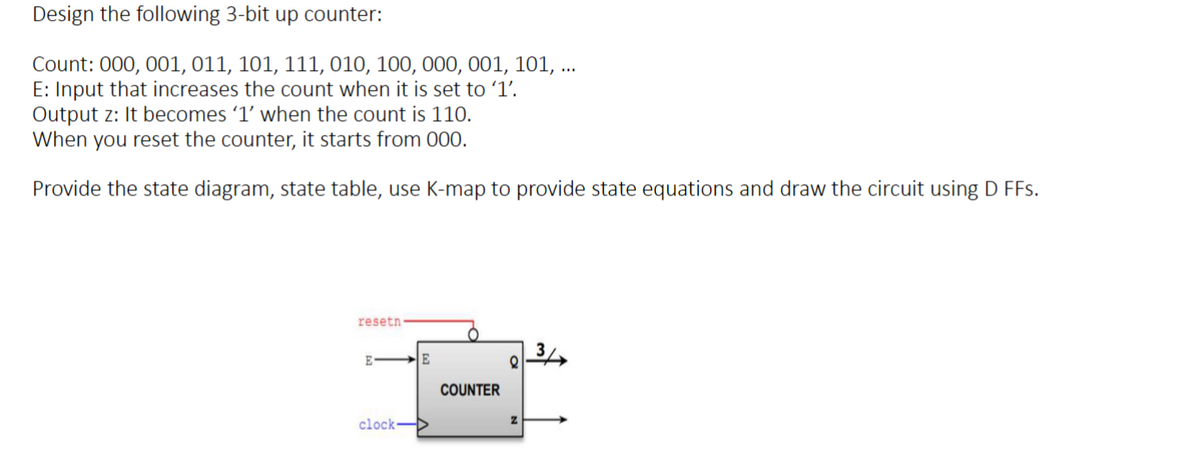
Design the following 3-bit up counter: Count: 000, 001, 011, 101, 111, 010, 100, 000, 001, 101, ... E: Input that increases the count when it is set to '1'. Output z: It becomes '1' when the count is 110. When you reset the counter, it starts from 000. Provide the state diagram, state table, use K-map to provide state equations and draw the circuit using D FFs.
Q: What do you call the information that has been copied from random access memory (RAM) to virtual…
A: Random access memory(RAM): RAM is the hardware in a computing device where the operating system…
Q: As a result of their decentralized character, wireless networks present a number of difficulties.…
A: Introduction: Wireless networks have become increasingly popular due to their flexibility and…
Q: There is a persistent round-trip delay between the sender and the recipient, and the sender is aware…
A: Yes, timers are still required in the rdt 3.0 protocol, even if the sender is aware of the constant…
Q: me ways the bank ensures that you can get to your information and/or execute transactions whenever…
A: Load balancing and fault tolerance are two important concepts in the design and operation of systems…
Q: Task instruction In cell D13 creat a formula using the MAX function to calculate the maximum…
A: The solution is given below with output screenshot
Q: Consider some of the obstacles that must be overcome while designing the infrastructure for a…
A: Introduction: When designing the infrastructure for a brand-new service's data systems, there are a…
Q: What specific function does each component of the kernel serve within the context
A: The kernel is the central component of an operating system responsible for managing system resources…
Q: This is the wrong answer, the list is list = {1, 2, 3, 4, 5, 6, 7, 8, 9, 10} NOT {10, 9, 8, 7, 6, 5,…
A: - We need to talk about the number of times inner loop executes for the list to do value changes.
Q: Define a function breadthFirst, which performs a breadth-first traversal on a graph, given a start…
A: Dear Student, The completed code along with implementation and expected output is given below -
Q: How do these three(CIA Triad) principles work together? Can you think of any situations where one of…
A: Dear Student, The detailed answer to your question with required explanation is given below -
Q: By comparing the UML model with the EER model, you will be able to explain the differences between…
A: By comparing the UML model with the EER model, you will be able to explain the differences between…
Q: te the Movie class. The UML diagram of the class is represented below: 1. Implement the class…
A: Dear Student, The required code along with implementation and expected output in Java is given below…
Q: How does availability change when MTTR goes to zero? Can this scenario be explained in sufficient…
A: Introduction In the field of information technology, availability is a crucial metric that is used…
Q: Because of their one-of-a-kind architecture, wireless networks are susceptible to a diverse set of…
A: Our ability to connect and communicate has been revolutionized by wireless networks, which offer…
Q: What do you call information that has been copied from random access memory (RAM) to virtual memory…
A: The answer is given in the below step
Q: In a linked-based implementation of the ListInterface with a head reference and tail reference…
A: Here is your solution -
Q: Answer E2) Could you perhaps elaborate on the differences between "digitized" and "disseminated"?
A: Introduction The field of information technology is concerned with the management, processing, and…
Q: search the internet and find a “suspicious” volume encryption product. Identify and discuss the…
A: To identify potentially suspicious or unreliable volume encryption products based on their product…
Q: Do you realize how important management of information security is in today's world?
A: Protecting sensitive data, systems, and assets from illegal access, use, disclosure, interruption,…
Q: How to : Enter a Folumar in cell E4, using the IF fuction, that returns a value of YES if cell D4 is…
A: One of the most used functions in Excel is the IF function, which enables you to compare values…
Q: Community and Service Networking in human services? Why is it useful?
A: In this question, it is asked why are community and service networking in human services useful.…
Q: A loop that iterates across a list of objects is referred to as a for construct. As a consequence of…
A: Introduction: In programming, a for loop is a control flow statement that iterates over a sequence…
Q: The keyword that represents an active high tri-state buffer is _____
A: The above questions are related to Verilog, a hardware description language (HDL) used to model…
Q: Examine the three IPv6 migration alternatives.
A: With the depletion of IPv4 addresses, organizations must move to IPv6. Several IPv6 migration…
Q: "In a buffer register, when the LOAD control signal is enabled or active, the input from W bus is…
A: 1. In digital circuits, a buffer register is a type of register that is used to store data…
Q: When individuals speak about a data structure, they are referring to the way in which information is…
A: A storage that is used to store and arrange data is called a data structure. It is a method of…
Q: Part 1. a) Create a 1D array of integers to store 50 integers. b) Store values from 0 to 49 in the…
A: In this question, there are two parts In the first part, 50 integers must be added to the String and…
Q: Resolve the following problem by following all the steps: a* x + b = 0
A: The flowchart to solve the equation:
Q: Create your own Wikipedia page Wikipedia is one of the backbones of the Internet, and it has a…
A: Wikipedia is a free, which refers to the one it is open content online encyclopedia created through…
Q: Suppose a new CPU generation doubles cores every 18 months. What off-chip memory bandwidth will be…
A: To calculate the off-chip memory bandwidth needed in three years, we'll first determine the number…
Q: at are the components that make up the interface of an Abstract Data Type? Here is the space where…
A: Abstract data type Introduction: ADT is a type (or class) of object whose behavior is defined by a…
Q: begin = System.nano Time(); //we measure in nanoseconds. // put your code here. end = System.nano…
A: In this question, there are two parts for a java program Two separate java programs are provided In…
Q: Write a Python program that prompts the user for their age, what high school they attended, and if…
A: Dear Student, The required code along with inline comments and expected output is given below -
Q: How would you approach developing a real-time operating system if you were writing the code for one?…
A: The answer is given in the below step
Q: Write a program that takes as input the speed of a car e.g 80. If the speed is less than 70, it…
A: As the programming language is not mentioned here w are using Python The Python code is given below…
Q: In cell D12, use the quick analysis tool to create a formula that uses the SUM fuction to total the…
A: Answer the above question are as follows
Q: The following are the necessary tables for a Bank Database customer table: | customer_id |…
A: To communicate with a MySQL database, one uses a statement or command called a MySQL query. It is…
Q: 5.1.Draw the logic circuit diagram for each of the fo gates are used. (a) A + B + C (b)ABC (c)AB + C
A: “Since you have posted multiple questions with multiple sub parts, we will provide the solution only…
Q: I'd be interested in learning about the many parts that go into constructing a conventional…
A: An operating system is an interface between users and the hardware of a computer system. It is a…
Q: 5. Match the SQL views on the left with their common usage on the right 1. 2. 3. 4. 5. 6. 7. 8. 9.…
A: According to the information given:- We have to match the mentioned statement to correct option..
Q: Your job is to decrypt this intercepted message, CQNTNHRBDWMNACQNVJC, which is believed to reveal…
A: 1. To decrypt the intercepted message NEXYIYECEHTIRISNEHPK, we need to reverse the route cipher.…
Q: Wireless networks are susceptible to a wide range of difficulties due to the characteristics that…
A: Answer is
Q: Can all of an organization's IT infrastructure issues be solved by using cloud computing?
A: In this question we need to explain whether cloud computing can solve all the Information Technology…
Q: Is the modern person easily duped by a Mechanical Turk? What distinguishes modern-day Turks from…
A: In the context of computing, a Mechanical Turk refers to a system that uses humans to perform tasks…
Q: MISD machines are systolic arrays. Systolic arrays form "wavefronts" of data processing units. When…
A: Answer is
Q: Write a generator that accepts a string as an input and yields each character in the string, one at…
A: As the programming language is not mentioned we are using Python The Python code is given below with…
Q: To what goal does the implementation of a microkernel in an operating system take place? Is this…
A: Introduction: The implementation of a microkernel in an operating system is a design approach that…
Q: Problem For the purposes of collecting entropy or obtaining cryptographically robust pseudo-random…
A: Use the EGADS API as described in the detail in next step:
Q: Write an article comparing various CPU Scheduling Algorithms.
A: Please find the detailed answer in the following steps.
Q: Use the pseudocode methods below to answer the questions starting on the next page. FIRST…
A: Given: From the given pseudocode methods, we have to choose which method corresponds to each of the…
Design the following 3 bit up counter:
Count: 000, 001, 011, 101, 111, 010, 100, 110, 000, 001, 101
typo in the image
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- Design a circuit that takes three bits, X2, X1, X0 as input and produces one output, F. F is 1 if and only if 2<=X<=5 when X = (X2, X1, X0) is read as an unsigned integer. For example, if X2=1, X1=0, and X0=0, then the unsigned binary value is 100, which is 4, so the output would be 1. Your Assignment For This Problem Includes the Following Design the necessary circuit using Logisim to implement the situation described above. Use Kmaps for simplification. Be VERY careful to get the correct functions for your output before simplifying and designing the circuit with Logisim. You should minimize the circuit. Your circuit should have three inputs and one LED output. All inputs (X2, X1, X0) and output (F) should be labeled (in Logisim, not by hand). Please use these names to indicate the inputs and output so all projects are consistent. You should also include your name as a label on the circuit. Test your circuit to be sure it is working correctly.you need to design and draw a 3-bit synchronous binary up/down counter for experiment 5. You need to add a bit named "M" for the excitation table that helps it switch between up and down mode and draw the state transition diagram, excitation table, k-map and circuit diagram with T-flip flops. When M = 0, it will perform up counter. When M = 1, it will perform down counter.In this problem, you should design a two-bit comparator. This circuit should have three outputs named l, g, and eq. The circuit should get two digits binary numbers (00, 01, 10, 11), and the output should change based on these rules:• If first number > second number then g = 1, l = 0, and eq = 0• If first number < second number then g = 0, l = 1, and eq = 0• If first number = second number then g = 0, l = 0, and eq = 1Your circuit will have 4 input (2 bit for the first number, and 2 bits for the second number)a. Draw the truth table for the comparator for unsigned numbers b. Show the circuit.
- Write VHDL code for a modulo-13 counter (counting sequence is 010, 110, …. 1210). The counter has the following features: an asynchronous Active Low Reset a value R can be loaded into the counter, using the signal Ld (Load) The signal Ld is active Low Draw the schematic of your counter, showing the inputs and outputs. Show the number of bits for R, Q (output of the counter), Ld.Write VHDL code for a modulo-13 counter (counting sequence is 010, 110, …. 1210). The counter has the following features: an asynchronous Active High Reset a value R can be loaded into the counter, using the signal Ld (Load) The signal Ld is active High Draw the schematic of your counter, showing the inputs and outputs. Show the number of bits for R, Q (output of the counter), Ld.4 bit 2’s Complement Multiplier INPUT A: 4 bit 2’s Complement number INPUT B: 4 bit 2’s Complement number OUTPUT: the product of A x B represented as a 8 bit 2’s Complement number You are only allowed to use the basic gates: NOT, AND, OR, XOR. You may however, use these basic gates to build your own custom circuits (i.e. Adder). You are NOT ALLOWED to use Logisim’s built in circuits. Each custom circuit is to be implemented as a sub-circuit as discussed in class. PART 4: Using the 3 subcircuits you built in Parts 1-3, built a 4 bit 2’s Complement multiplier that uses the inversion method discussed in class. Name this circuit: SignedMultiplier HINTS: INVERSION METHOD: 1) If input A is negative, invert it. If input A is positive, leave it alone. 2) If input B is negative, invert it. If input B is positive, leave it alone. 3) Multiply A and B. 4) If both A and B originally had the same sign (both positive or both negative), do nothing. 5) If A and B originally had different signs…
- 4 bit 2’s Complement Multiplier INPUT A: 4 bit 2’s Complement number INPUT B: 4 bit 2’s Complement number OUTPUT: the product of A x B represented as a 8 bit 2’s Complement number You are only allowed to use the basic gates: NOT, AND, OR, XOR. You may however, use these basic gates to build your own custom circuits (i.e. Adder). You are NOT ALLOWED to use Logisim’s built in circuits. Each custom circuit is to be implemented as a sub-circuit as discussed in class. PART 1: Build a 4 bit controlled 2’s Complement Inverter as a subcircuit named 4BitInverter PART 2: Build a 8 bit controlled 2’s Complement Inverter as a subcircuit named 8BitInverter PART 3: Build a 4 Bit UNSIGNED Multiplier as a subcircuit named UnsignedMultiplier PART 4: Using the 3 subcircuits you built in Parts 1-3, built a 4 bit 2’s Complement multiplier that uses the inversion method discussed in class. Name this circuit: SignedMultiplier HINTS: INVERSION METHOD: 1) If input A is negative, invert it. If input A…4 bit 2’s Complement Multiplier INPUT A: 4 bit 2’s Complement number INPUT B: 4 bit 2’s Complement number OUTPUT: the product of A x B represented as a 8 bit 2’s Complement number You are only allowed to use the basic gates: NOT, AND, OR, XOR. You may however, use these basic gates to build your own custom circuits (i.e. Adder). You are NOT ALLOWED to use Logisim’s built in circuits. Each custom circuit is to be implemented as a sub-circuit as discussed in class. PART 1: Build a 4 bit controlled 2’s Complement Inverter as a subcircuit named 4BitInverterDesign a circuit that has two inputs X, and S, where X represents an 8-bit BCD number, S is a sign bit. The circuit has one output Y, which is the Binary representation of the signed-magnitude BCD number. A negative output is represented in the Binary 2’s- complement form. You need to think of two design alternatives. Submission guidelines: 1. You should write a report that at least contains the following sections: 1. Problem definition. 2. Design alternatives : 2.1. Alternative 1 block diagram 2.2. Alternative 2 block diagram 3. Design selection criteria 4. Detailed circuit design of the selected alternative. 5. Verilog modules, and simulation results for all modules, and for the whole circuit of the selected alternative .
- Build a circuit that takes four bits as input: W, X, Y, Z. Treat WX as a 2-bit unsigned binary number, and treat YZ as a second 2-bit unsigned binary number. Your circuit should generate the output corresponding to the product of WX and YZ. You will need 4 bits of output for this problem.For example, if your input was 1011, your inputs correspond to 2 and 3. That product is 6, so your output will be 0110.Create a truth table for this problem, show all k-maps and minimizations, and build the corresponding (minimized) circuit. Use XOR, XNOR, NAND, and NOR as appropriate if it reduces the number of gates used.Type your question here • Design a 3-bit synchronous counter using J-K FFs only.This is a seven segment display. can you implement this on multisim and and show the letters M A H D I J A N on the display using jk flip flops. we need 555 timer counter. frequency should be 1hz.

