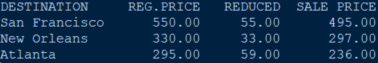
DESTINATION San Francisco New Orleans Atlanta REG. PRICE 550.00 330.00 295.00 REDUCED 55.00 33.00 59.00 SALE PRICE 495.00 297.00 236.00
Q: While downloading free or almost free software, do you think it's OK to provide some of your…
A: A danger to a company's stability and well-being is posed by using information technology to achieve…
Q: Program slice—that? what's Discuss program segmentation.
A: The process of identifying and isolating program elements pertinent to a specific activity or…
Q: What other sorts of firewalls are available to pick from in addition to those that are based on a…
A: Answer is
Q: Create a style rule for anchor elements within the main element that sets the font color value to…
A: 1) A style rule for anchor elements within the main element is a set of CSS instructions that…
Q: "Access Point" in wifi means what? What happens?
A: "Access Point" as it relates to wifiSimply said, an access point is a location that offers wireless…
Q: How can we stay anonymous online?
A: Introduction : Anonymous online refers to using the internet without revealing one’s identity. It…
Q: Operating Systems Question 3 What is the biggest downside of remote procedure calls employing at…
A: 1) At most once semantics means that the RPC client will send the request to the server, and the…
Q: Then, static and route testing metrics are explained, and the section after that shows how project…
A: Route testing and static testing: Static testing may be code-free or code-based. Problems in code,…
Q: Question 5: Koenigsberg, today Kalingrad, is a confluence of two rivers, and includes an island. In…
A: This is a well-known mathematical problem called the Seven Bridges of Koenigsberg, which was first…
Q: Provide a summary of the TOR Network.
A: We have to understand the TOR Network Let's understand and hope this helps if you have any queries…
Q: Why do waterfall models restrict iterations?
A: The waterfall model restricts iterations because it assumes that all requirements are fully defined…
Q: How can I safely remove a 250-gigabyte solid state disk from a computer without harming its…
A: Let's talk about SSD quickly before we get into the technique for properly removing it from your…
Q: How can you apply a computer's central processor unit's traits to an example?
A: Introduction: The central processing unit, or CPU, is a component of all different kinds of…
Q: Given string inputStr on one line and integers idx1 and idx2 on a second line, output "Match found"…
A: Your java program is given below as you required with an output. Algorithm : The code reads in the…
Q: PLS HELP ME : Write expressions of relational algebra to answer the following queries Find MaMH…
A: The question asks for relational algebra expressions to answer various queries. Relational algebra…
Q: CHALLENGE ACTIVITY 4.7.2: If-else statements. 454192.2153518.qx3zqy7 Jump to level 1 Write multiple…
A:
Q: Assess the challenges you will have while developing the framework, and then analyze the concerns…
A: Introduction: Since it offers so many benefits to businesses of all kinds, cloud computing has…
Q: Many advantages come along with social media usage and network connectivity.
A: 1. Connect. Social media interaction isn't enough. Social media is about connecting people. In my…
Q: Population and Economic Growth Loop : As employment opportunities increase in a city, people are…
A: This particular question belongs to Computer Science and Engineering. Computer Science is an…
Q: TOR Network
A: The TOR network, short for "The Onion Router," is an anonymity network that was initially developed…
Q: Modulo Rules. Find the remainders. a = 222; b = 13 10 Answer 13
A: To find the remainder when a number is divided by another number, you can use the modulo operator…
Q: How can you tell whether your data is safe while using cloud services? Can we guarantee their…
A: Cloud services: Cloud services are services that are delivered over the internet from a cloud…
Q: classes (sections). Each section is a course and there can be many sections for a course. You can…
A: Here's an ERD for the mini case +--------------+ +--------------+ | Course…
Q: Assumptions regarding the culprit of an unlawful conduct committed online
A: Cybercrime—also known as computer crime or computer terrorism—occurs when a computer is used to…
Q: swaps
A: make a flowchart for this problem:Create a program that swaps 2 numbers value.
Q: Despite powering all components, my laptop's BIOS was upgraded, but it still doesn't show. Problem?
A: Upgrading the BIOS on a laptop can be an important step in keeping the device up to date and…
Q: In what ways may one use simulation models to represent problems that cannot be reduced to a single…
A: Simulation models may simulate two categories of challenges. Simulations address difficult problems.…
Q: Assess all of the hurdles and barriers you will face when building the framework, as well as the…
A: Introduction: Cloud computing has pros and cons and a reliable, user-friendly architecture.…
Q: Iterative Waterfall Model stages? The Iterative Waterfall Model works too. Describe. Your guess?
A: One of the software development models is the iterative model.In this approach, completing one phase…
Q: waterfall model iterations
A: The waterfall model is a linear sequential software development model that consists of distinct…
Q: Is an access point a switch or hub for bandwidth? Explain
A: To transfer network data from one device to the target device, a switch only fully comprehends a…
Q: Suppose that a programming language uses dynamic scoping. Consider the following code segment in…
A: Answer for both the flows given below with explanation
Q: What kinds of firewalls exist in addition to those that are centered on a network?
A: Introduction: A firewall is a security device or software that monitors and controls the incoming…
Q: The top five most common network architectures should be described. In your view, which one is more…
A: For the solution, see the following steps: The advantages of star topology 1) Compared to Bus…
Q: How can you protect your PC from power surges?
A: SPARKS OF ENERGY: A quick spike in voltage is what we call a power surge, sometimes called transient…
Q: As a starting point, define virtualization and describe the differences between the various flavors…
A: Using virtualization: It is a method that enables the user to run several Operating Systems on…
Q: Other firewalls beyond network-based?
A: This question discusses non-network-based firewalls. Routers don't monitor traffic, but firewalls…
Q: Complete the following procedure and answer the accompanying questions. 1. On an HP Pavilion dm3z…
A: Note : As per the bartleby policy we can answer single question at a time. If you want the solution…
Q: Provide your thoughts on the four most important takeaways from the reading you did on continuous…
A: Given: CONTINUOUS EVENT SIMULATION A Continuous event simulation refers to a type of simulation in…
Q: what happens and how it's done when people do illegal stuff on the internet. How can you avoid being…
A: Introduction: The internet has become an integral part of our daily lives, and it has transformed…
Q: Can you provide any examples of how dynamic programming is used?
A: Dynamic Programming is the most efficient method for designing solutions to optimization issues.…
Q: explain integrity's three p and provide the regulation
A: Integrity is the discipline of being honest, reliably, and unfalteringly adhering areas of strength…
Q: How can a static picture become a collection of numbers? How does one go
A: Introduction: In today's digital age, images and videos are ubiquitous. However, they are not just…
Q: Consider the issues and challenges that occur with each of the possible solutions, as well as the…
A: Cloud computing is the term used to describe the delivery of different services through the…
Q: Discuss the hazards of online credit card money transfers.
A: When a credit card number is added to a mobile wallet, it is encrypted and concealed behind a…
Q: Why do companies want physical firewalls?
A: your inquiry is Create a list of the reasons why a corporation might require firewalls for physical…
Q: In what ways may simulation models be utilized to simulate a wide variety of problems?
A: Simulation models are mathematical representations of real-world systems that allow users to test…
Q: this is my code, but after automatically check it, it shows smt went wrong(image one) image two is…
A: There is a mistake in the addTweet() method. When a new tweet is added, the index should be set to…
Q: You must warn customers about the hazards of using credit cards for online money transfers.
A: 8 Tips for Online Credit Card Security (1) You may lessen your risk if you have only one account.…
Q: How can you get trustworthy information on the internet?
A: The internet is a vast source of information that can be both helpful and harmful at the same time.…
Can you please answer the following question?
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Table Name:- Employee Empid EmpName Department ContactNo EmailId EmpHeadId 101 Isha E-101 1234567890 isha@gmail.com 105 102 Priya E-104 1234567890 priya@yahoo.com 103 103 Neha E-101 1234567890 neha@gmail.com 101 104 Rahul E-102 1234567890 rahul@yahoo.com 105 105 Abhishek E-101 1234567890 abhishek@gmail.com 102 Table :- EmpDept DeptId DeptName Dept_off DeptHead E-101 HR Monday 105 E-102 Development Tuesday 101 E-103 Hous Keeping Saturday 103 E-104 Sales Sunday 104 E-105 Purchage Tuesday 104 Table :- EmpSalary EmpId Salary IsPermanent 101 2000 Yes 102 10000 Yes 103 5000 No 104 1900 Yes 105 2300 Yes Table :- Project ProjectId Duration p-1 23 p-2 15 p-3 45 p-4 2 p-5 30 Table :- Country cid cname c-1 India c-2 USA c-3 China…Create a stakeholder register for a Greek restaurantGo to the Collectibles section of eBay (http://collectibles.shop.ebay.com/) and pick any subcategory that looks interesting to you. Find an auction that is just about to end and bookmark it. When the auction has ended, return to the auction page and click on “Bid History.” (If you have an eBay account, you have the option for searching “Completed Listings.”) Your assignment is to use the bid history to construct a demand curve. (You will have to “reorder” the bids a bit to figure this out. Try to figure out the maximum price that each of the bidders is willing to pay, and then use that information to construct the demand curve. See this example for how to get from a bid history to a demand curve.)HELPFUL NOTES: Only count the highest bid for each bidder. If one bidder bids $25 but then later bids $50 and then never bids again, it must be that his maximum willingness-to-pay is $50; the $25 bid is irrelevant. If the bidder had been willing to bid more than $50, he probably would have…
- BASIC JQUERY...Make a simple portfolio using JQuery (link below), provide much detail as possible by using the given examples in the link in creating the portfolio .... https://www.w3schools.com/jquery/jquery_examples.asp?fbclid=IwAR0WWFC39ucCIUMykf0-bRja1lMcI0vBQoGdy6V_NuWH-1cZMTMf2l6Tndw16 Examples of the user touchpoints include: Select one: a. Transaction Points b. Service Points c. All other answers are correct. d. Information Pointsplease answer with proper explanation and step by step solution. i request not copy from online site. Question: What is the relationship between f(n) = 2^n and g(n) = 2^(n–1)? Answer choices: a. f = O(g) b. f = Ω(g) c. None of the these d. f = ϴ(g)
- Given the following XML file student.xml <?xml version="1.0" encoding="UTF-8"?> <Myclass transacted= ”123”> <studlist> <student Rating= “average” > <firstName>John</firstName> <lastName>Smith</lastName> <email>jsmith@gmail.com</email> <mobile>0211223344</mobile> </student> <student Rating= “top 10” > <firstName>Ali</firstName> <lastName>Faizal</lastName> <email>ali@gmail.com</email> <mobile>0211223345</mobile> </student> </studlist> <Details> <location>Block15</location> <floor>First</floor> <roomno>909</roomno> </Details> </Myclass> Write an DTD document for the above xml file. What is the document root?Don't say its violates ur term of service. Provide correct solution and get upvotes.How many Web sites can you think of that usecrowdsourcing, that is, have nonemployeesprovide the value?
- Delete all the salesmen who make less than 200 in commission, including those who have not earned any commission EMP Table: Field --------------------------------------- EMPNO ENAME JOB MGR HIREDATE SAL COMM DEPTNO DEPT Table: Field ------------------------------- -------- -------------------------------------------------------------------- DEPTNO DNAME LOCThe Great Bear Lodge is a hotel with an adjoining indoor waterpark and indoor minature golf center. The hotel sells packages which include overnight hotel stays with waterpark passes and minature golf passes. The hotel also has a plicy of selling daily passes to the indoor waterpakr and daily passes to the indoor minature golf center (in other words people do not need to stay at the hotel to use the indoor waterpark or indoor minature golf center.) Hotel guests may also choose to reserve just a hotel room without purchasing the waterpark or minature golf center passes. Great Bear Lodge is offering an incentive for the month of April. They are offering a package in which guests who reserve an overnight stay with the waterpark pass package will receive a free pass to the minature golf center. The total price for this package is $225 per night. The typical pricing for each of these sold independently are: One night hotel stay: $180, Daily Waterpark pass: $90, Minature Golf…Which of the following is not the principles for improving the way that mixes operate: A. Use a single mix. B. Uniform transactions. C. Client-side should be automated. D. Fees should be all-or-nothing.

