det 104 -2 10 321
Q: What are the two most prevalent technologies used in wireless networks?a
A: in the following section we will be discussing about the two most prevalent technologies used in…
Q: 192.168.3.55/24 and then 192.168.70.134/29
A: The answer is
Q: your ow words to derir "sub-band coding describe the role it plays in MP3 file compression. the…
A: Codes for sub-bands :- Sub-band coding (SBC) is a term used in the field of signal processing…
Q: Why is the waterfall model's maximum number of iterations limited?
A: Introduction: Waterfall model : A linear and sequential approach to building a system. The waterfall…
Q: Please in C Language (CYBER SECURITY) Write a program that uses an existing text file (text.txt) to…
A: Below I have provided an c program for the given question. Also, I have attached a screenshot of the…
Q: Consider using Structured English to describe processes that fall outside the scope of a systems…
A: As The word describes Structured English is basically structured. It is also called Pseudo Code (In…
Q: There are several methods for gaining access to files. What benefits and drawbacks come with…
A: Global system offers index and direct file access. It's also called Direct or Relative Access. Index…
Q: What are the most crucial things to think about while implementing an ALL-IP network? List the top…
A: IP Networks: Any collection of devices having the same network structure and individual IP addresses…
Q: Why is the waterfall model's maximum number of iterations limited?
A: Waterfall Model: The Waterfall Model is a linear or sequential technique to task control and works…
Q: Add an if branch to complete double pennies()'s base case. Sample output for below program: Number…
A: Algorithm: 1. Create a function and declare its parameters. 2. Initialize total_pennies to 0. 3. If…
Q: It is crucial to educate customers on how to defend themselves from efforts at session hijacking.…
A: Stolen sessions: Sessions are hijacked. An attacker may hijack a user's session, stealing their…
Q: What are the essential three elements for a network to function properly? Please take a time to…
A: The answer for the above question is given in the below step
Q: USE FOR LOOP Given a line of text as input, output the number of characters excluding spaces,…
A: Steps: 1. Take input string from user. 2. Set count to zero 3. use for loop to count the characters…
Q: Digital memory comes in a variety of forms, including cache memory, random access memory (RAM),…
A: A hard disk drive (HDD) is an obsolete storing contraption that uses mechanical platters and a…
Q: Haskell 1. Show how the meaning of the following curried function definition can be formalized in…
A: Hi please find your solution below and I hope you would find my solution helpful As per guidelines I…
Q: Code in Python Write a function, print_integers_less_than(n), which takes an integer parameter n…
A: Python : Python is a high-level and object-oriented programming language. it is used for web…
Q: If the original list has n items, how many times can the list be cut in half using merge sort?
A: Similar to how it operates on an array, it also operates on a linked list. The list is split into…
Q: You might find it useful to use structured English when discussing processes that aren't part of the…
A: English with a structure: Iterations, decision structures, sequential structures, and case…
Q: What factors are taken into account when designing and implementing storage architecture?
A: Introduction: a procedure for putting something into action or making it effective, such as the…
Q: List at least three benefits of the spiral model over the waterfall strategy. Please include a…
A: The major distinction between a waterfall and repeated model is that the former is applied to short…
Q: What three factors make a network effective and successful? Let's examine each nem independently.
A: It is defined as a process that consists of two or more computers that are linked in order to share…
Q: Which of the five layers of the Internet protocol stack is the topmost? How does each of these…
A: Internet protocol stack A protocol stack refers to a set of protocols that are running concurrently…
Q: What is the SizeMode attribute's default value for the PictureBox control?
A: The PictureBox control is utilized for showing pictures on the structure. The Picture property of…
Q: How many layers are there in the Internet protocol stack in total? Are there any particular duties…
A: I have given answer below with explanation and example.
Q: 1. Design a class that holds the following personal data: name, address, age, and phone number.…
A: The correct answer for the above mentioned question is given in the below steps for your reference.
Q: Which of the five layers of the Internet protocol stack is the topmost? How does each of these…
A: Open System Interconnection(OSI) model is used to standardize how a computing or telecommunication…
Q: The ideal position for a systems analyst would involve working in an IDE or a general CASE…
A: What is an IDE?An integrated development environment (IDE) is software for building applications…
Q: uch to your dismay, you find upon entering the boardroom that the cable will not fit into any of the…
A: According to the information given:- We have to describe the mentioned scenario When you walk into…
Q: The throughput loss of wireless networks is greater than that of conventional networks. What is the…
A: Introduction: Cabled network A network that uses physical wires and cables to connect its computers…
Q: How important is it to have a consistent user experience while developing the SoS interface? How…
A: The phrase "universal interface" was used to socialize the four sub-goals. Self-illustrative…
Q: How can you secure Jenkins?
A: Jenkins Jenkins is utilized wherever from workstations on corporate intranets to powerful servers…
Q: Create a program using python How many dvd, tv, dvd player and controllers were sold? Must Have a…
A: Below I have provided an python program for the given question. Also, I have attached a screenshot…
Q: List at least three benefits of the spiral model over the waterfall strategy. Please include a…
A: The spiral model is one of the most significant Software Development Life Cycle models for risk…
Q: Operating Systems Issue 3: In your opinion, what is the at most once semantics for remote procedure…
A: NOTE: ACCORDING TO COMPANY POLICY, WE CAN SOLVE ONLY 1 QUESTION. YOU MAY RESUBMISSION THE QUESTION…
Q: Operating Systems Issue 3: In your opinion, what is the at most once semantics for remote procedure…
A: NOTE: ACCORDING TO COMPANY POLICY, WE CAN SOLVE ONLY 1 QUESTION. YOU MAY RESUBMISSION THE QUESTION…
Q: What are the most crucial things to think about while implementing an ALL-IP network? List the top…
A: Here are a few things to think about with an ALL-IP network. Three significant ALL-IP network…
Q: It is conceivable that using structured language is useful when describing processes that are not a…
A: Conceivable basically means can be imagined or in simple words possible. In Structured Language the…
Q: What is the main distinction between procedural and object-oriented programming?
A: Programming is a a technique to create set of instructions executed by computer system to achieve…
Q: List down 10 operating system and describe each.
A: An Operating System is the core of the computer system as it manages software and hardware…
Q: Do you know what "static" and "function" mean?
A: Java Java is an object-oriented programming language that creates applications for several…
Q: For the given IP address 196.62.146.174/27, answer the following questions: a. Subnet Mask b. Number…
A: Answer: Given 196.62.146.174/27 And we need to find the following answer
Q: Write Pseudo-code of MOCell?
A: MOCell stands for MultiObjective Cellular genetic algorithm. It is a family of cellular genetic…
Q: Why happens scope creep so often while developing an information system?
A: Scope creep : Scope creep (also referred to the requirement creep) is the board's phrase for the…
Q: What aspects need to be considered while choosing a solution for a physical network's protection?…
A: Introduction: Topology covers the physical and logical configuration of a local area network in…
Q: If you wanted to use JavaScript to find the element on the page, which strategy would you use to…
A: In this question we have to discuss what code need to be executed in JavaScript to find the element…
Q: I want solution flowchart
A: Given Pseudocode/code: Start Step 1: Declare Student_Name[10], Student_Score[10][5],i=0,j=0,sum=0…
Q: Look at how wireless networks are used in developing nations. Why do some businesses choose wireless…
A: Yes, wireless networks play a vital role in underdeveloped countries. Because it offers greater…
Q: What does it mean when someone refers to an assembly language in this way?
A: Programming Language Programming language consists of Syntax and Semantics which makes it two basic…
Q: Subnet Mask Number of Subnets Block size for the subnet peu
A: The answer is
Q: There are several methods for gaining access to files. What are the advantages and disadvantages in…
A: I haven answer below with diagram screenshot.
Please and thank find the value
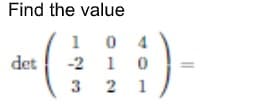
Step by step
Solved in 2 steps


