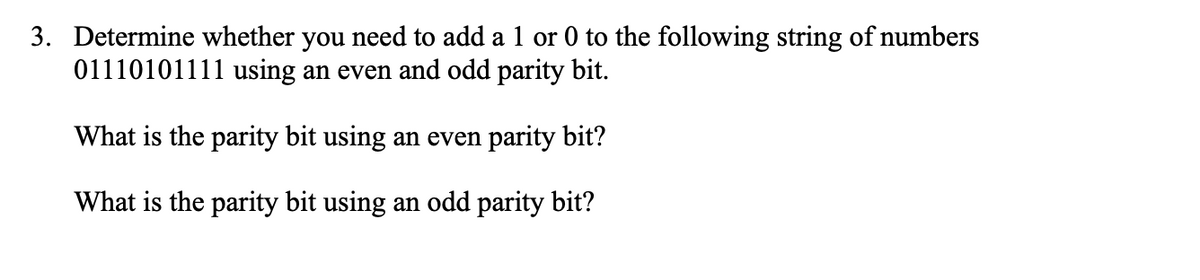
Determine whether you need to add a 1 or 0 to the following string of numbers 01110101111 using an even and odd parity bit. What is the parity bit using an even parity bit? What is the parity bit using an odd parity bit?
Q: Memory 12200 12201 12202 12203 12204 Content %3D AA EE FF 22 What result is produced in the…
A: To find result for the following execution instruction. a. LEA SI, [DI + BX + 5] b. LDS SI,[200]
Q: What are some of the most effective firewall administration techniques? Explain.
A: Introduction: Best Firewall Practices and How to Put Them in Place Every time a firewall rule is…
Q: escribe DBMS backup and recovery.
A: Introduction: Backup and Recovery in DBMS - In the event that our data becomes damaged due to system…
Q: Discuss various techniques to preventing Man-in-the-Middle (MITM) attacks from intercepting wireless…
A: Introduction: An eavesdropping assault in which attackers intercept control between two or more…
Q: Describe the reasons why an application developer might choose to run an application via UDP rather…
A: Meaning: TCP: It is a computer language that is built around connections. UDP: It is a…
Q: 5.37 Consider the following relation that holds data about employee assignments: ASSIGNMENT…
A: the solution is an given below :
Q: 5.2: Time Write a program that requests the current time and a waiting time as two integers for the…
A: The above program is in C++ is given below:
Q: Compare and contrast database management systems with file-based systems, and describe each with…
A: Introduction: The inquiry seeks to distinguish between a database management system and a file-based…
Q: Describe the following: Data tampering Thesaurus of Data Duties are separated. Language…
A: Intro Data diddling and Data dictionary Data diddling - Data diddling is a type of cybercrime where…
Q: Q: If data is to be sent from an input device to a memory buffer starting at address A000H and…
A: Intro DMA Channels The 8237 has four separate DMA channels each channel with two 16 bit registers…
Q: or tasks to be preferred to execute digital video editing ope
A: The major steps preferred to execute digital video editing operations are:
Q: h respect to your responsibilities as project manager, for development of web technologies, with…
A: Respect to your responsibilities as project manager, for development of web technologies, with…
Q: So, what may happen to a message when it is transmitted over an unstable TCP connection, and what…
A: The Answer is in step-2.
Q: Explain why, while building the architecture of a large system, you typically employ numerous…
A: Architecture patterns: Normally, while designing the architecture of a large system, several…
Q: Question 1 Analyze the following code: import java.util.*; public class Test { public static void…
A: Below is the complete solution with explanation for the given code in detail.
Q: Sound is one of the most important elements of multimedia. Calculate the file size for a monaural…
A: Bit a rate case in point: Soon turns are typically expressed in units (bps), kilobits per hour…
Q: Discuss what data governance is and why it is important to have executives involved in data…
A: The process of regulating the availability, accessibility, integrity, and security of data in…
Q: What's the difference between open-source development and conventional evolutionary prototyping?
A: Open-source software development: Open-source software development is the process by which…
Q: n with attributes A1, A2, ..., An. As a function of n, tell how many superkeys R has, if The only…
A: Introduction A super key is an attribute (or combination of attributes) that is used to identify…
Q: PYTHON Using regular expression 1. Get the list of words by extracting all the words between ( and…
A: # Using regeximport re # initializing stringstring = "The (best) way to learn any programming…
Q: What is the maximum power drain of a PCle Version 2.0 expansion card?
A: Introduction: PCIe slots link your motherboard to your PC's most vital components and offer critical…
Q: Distinguish and describe the three security objectives: confidentiality, integrity, and…
A: Intro In order to maintain confidentiality, data, objects, and resources must be shielded against…
Q: O(N) is the order of growth execution time of the index-based add operation when using the ABList…
A: Expecting ABList is based on top of a cluster and LBList is based on top of a Linked List:
Q: What is the primary motivation for switching from IPV4 to IPV6? Identify two significant changes…
A: IPSEC is a feature of the IPv6 protocol that can be used with proper critical infrastructure. IPv6…
Q: 1. A. Define .NET Framework class library. B. List any three namespaces defined in .NET Framework…
A: 1. Standard java in the.NET Platform: The Factory standard library (FCL) is a compilation of…
Q: What exactly do you mean when you say "thread salvation"?
A: Introduction: In order to do two or more tasks at the same time, threads are employed.
Q: Q1. What are the primary challenges for distributed query optimization?
A: Intro The evaluation of a large number of query trees, each of which produces the requisite query…
Q: 1. Write C++ code for Gaussian elimination method and solves the following electric circuit…
A: The row reduction strategy for solving linear equations systems is known as the Gaussian elimination…
Q: In TCP, the value of the window size is determined by O A. The Internet bandwidth size O B. The…
A: TCP stands for Transmission Control Protocol in which it gives authority to two or more computers to…
Q: Analyze the impact of the AI application/use in a global context
A: To analyze the impact of the AI application.
Q: Write a method named mean that accepts as a parameter an ArrayList of real numbers, and returns the…
A: Java program to find the average mean of the Array list
Q: 11.1. Exercise 1 Consider the already designed calculator GUI in the Lab 09, add event handling on…
A: The above code is solved in Java GUI is below:
Q: Consider the function f:Z→Z defined by f(x)=3x? - 1. Find f-(10), f"(13), Let f:R -> R be defined by…
A:
Q: Compute the delay time generated by the following subroutine, if you know that CPU frequency is 5…
A: Solution:- Delay Proc Near
Q: nat exactly is the difference between active an ers when it comes to vulnerability scanning?
A: Below the difference between active and passive vulnerability scanners when it comes to…
Q: Analyze factors that impact business strategy within the AI application/use
A: Factors that impact business through Artificial intelligence.
Q: example for c# code with comments of One- Dimensional Arrays.
A: I have provided C# CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOTS--------
Q: efine the ICMP and Describe briefly its anplicatio
A: ICMP is a protocol that reports errors and produces a concerning message to the source host. IPv4…
Q: What is the difference between a thread at the user level and a thread at the kernel level?…
A: The operating system does not recognize threads at the user level while the operating system…
Q: Q3) write True or False answer for the following statements. Correct the false statements a) BGP is…
A: Introduction: We need to find if the given statements are true or false: According to business…
Q: Explain briefly the application of embedded systems.
A: Introduction: An embedded system is a type of computer system that combines computer hardware and…
Q: Problem 3: Give asymptotic estimates, using the O-notation, for the following functions: (а) 4n' +…
A:
Q: Is this true or false? Linux only has a rudimentary file system based on MINIX.
A: Linux: Linux is an operating system that follows an open-source methodology. It can run on servers,…
Q: How do you see our world without computers and internet?
A: Life without computers can be very painful. It would be like hell. There will be no fun. Everything…
Q: 50 to = 0, t1 = 1, tn = 6t,-1 – n. 9tn-2 +
A: The solution to the given question is:
Q: Give two reasons why you believe it is critical for a computer programmer to learn about computer…
A: There are several causes for this: 1)If a particular computer programmer wants to determine what has…
Q: Describe how a CBIS could be utilised to cut costs or improve profits in the industry of your…
A: Industry preference: In an ideal world, a thorough macroeconomic and sectorial study would precede…
Q: Analyze the following code: public class Test { public static void main (String[] args) { int [] x -…
A: The correct option is: The program displays 1 2 3 4
Q: Describe the internet of things in your own words. What is the difference between these two…
A: The Answer start from step-2.
Q: An array T[-1.35][-2..15] is stored in the memory along the row with each element occupying 4 bytes.…
A: Here we calculate the Total number of elements stored in T and number of bytes allocated to T by…
Step by step
Solved in 2 steps

- A(n) __________ is an integer stored in double the normal number of bit positions.Are you able to differentiate between the least significant bit and the most significant bit in a given set of data?1. Using even parity, add parity bits to the following bit patterns: a. 0110 100 b. 1011 011 c. 0000 000 2. Using odd parity, add parity bits to the following bit patters: a. 0110 100 b. 1011 011 c. 0000 000
- In single precision (IEEE-754 standard), 8 bits are used for storing the exponent (the bias is 127), and 23 bits are used for storing the mantissa. (a) What are the smallest and the largest positive numbers that can be stored in single precision? (b) What is the smallest value of the mantissa that can be stored?271. In Return to Zero (RZ), the signal changes not between bits but a. before the bit b. after the bit c. doesn d. during the bitWhat is 4365 - 3412 when these values represent signed 12-bit octal numbers stored in sign-magnitude format? The result should be written in octal. Show your work.
- Write down the bit pattern assuming that we are using base 15 numbers in the fraction instead of base 2. (Base 16 numbers use the symbols 0–9 and A–F. Base 15 numbers would use 0–9 and A–E.) Assume there are 24 bits, and you do not need to normalize. Is this representation exact?By using 2’s Complement arithmetic, write the following decimal numbers to equivalent8-bit signed numbers and perform the addition. Write the final result after the addition by showing yoursteps. (check the image for reference) i. 6 ii. 14 iii. 15 iv. -6+ 3 + (-5) + (-25) + ( -9)Write down the bit pattern assuming that we are using base 30 numbers in the fraction instead of base 2. (Base 16 numbers use the symbols 0–9 and A–F. Base 30 numbers would use 0–9 and A–T.) Assume there are 20 bits, and you do not need to normalize. Is this representation exact?
- Find the complement of the following bit string: 100011010 (write down the sequence of 0's and 1's without any blank space). hints:answer is 9 bitCan you distinguish between the most significant and least significant bits?Repeat "List the ASCII code for the 10 decimal digits with an even parity bit in the leftmost position." with odd parity.

