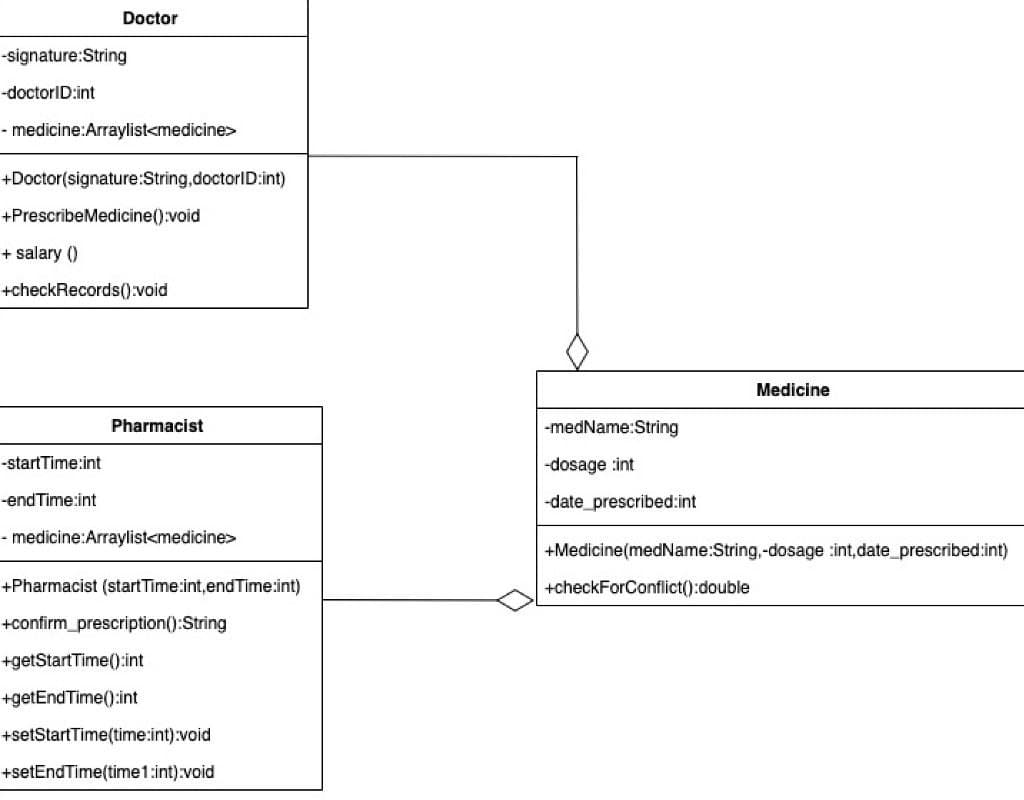
Doctor signature:String doctorID:int medicine:Arraylist Doctor(signature:String,doctorID:int) -PrescribeMedicine():void - salary () checkRecords():void Medicine Pharmacist -medName:String startTime:int -dosage :int endTime:int -date_prescribed:int medicine:Arraylist +Medicine(medName:String,-dosage :int,date_prescribed:int) -Pharmacist (start Time:int,end Time:int) +checkForConflict():double -confirm_prescription():String -getStartTime():int -getEnd Time():int -setStartTime(time:int):void setEndTime(time1:int):void
Q: Q-1: Write a program in Assêmbly language using MIPS instruction set that will display the following...
A: The complete code is given in the next step For a more valid approach, input is asked from user, abo...
Q: How can a modern pipelined computer run a program rapidly and efficiently?
A: Pipe-lining is actually the technique of rearrangement of the Central processing unit's numerous har...
Q: ARM assembly Translate the ARM instructions in bold into a 32 bit integer. Please give an example...
A: Here i write the instruction in 32 bit format with example: ========================================...
Q: What is the Application Layer's role in networking?
A: Your answer is given below. Introduction :- The Application Layer is the seventh of the OSI model'...
Q: What is your definition of VLAN, and what are some of the most common types you are familiar with?
A: Intro A VLAN (virtual local area network) is a subnetwork that may be used to join together grouping...
Q: 1a Distinguish between the following pairs of compilers: (i). Cross-compiler and Source-to-so...
A: The answer to the following question:-
Q: Fundamentals of Algorithm Devise an algorithm that finds the sum of all the integers in a list.
A: We are going to write an algorithm which will find out sum of all integers in a list. Please refer t...
Q: What are the essential features of OSPF?
A: Introduction features of OSPF
Q: What Exactly Is 3-tier Architecture?
A: Three tier architecture is a kind of software application architecture which is known to be well est...
Q: What security policy would mitigate the use of no encryption or hashing to regulate data flow and un...
A: Encryption It is the process of sending data in a way that guarantees confidentiality. The encrypti...
Q: What exactly is HDLC?
A: Intro HDLC (High-level Data Link Control) is a collection of protocols or rules that are used to sen...
Q: When compared to the explicit heap storage recovery necessary in C++, what are the arguments for and...
A: For: Implicit heap storage recovery eliminates the creation of dangling pointers such as deletion by...
Q: What Exactly Is the Spanning Tree Protocol? Could you please explain your background in this field?
A: Intro When a network topology has loops, the Spanning Tree Protocol (STP) is employed to prevent thi...
Q: When it comes to linking conditions with actions, a decision table makes things much easier. explain
A: - linking conditions with actions in decision table - decision table are made up of columns which ar...
Q: Why should you check the value of a StreamReader object's EndOfStream property before invoking the R...
A: NOTE :- Below i explain the answer in my own words by which you understand it well. There just ...
Q: When a computer needs a piece of information, does it immediately perform the memory fetch operation...
A: The procedures that are conducted when reading a piece of information from memory should be addresse...
Q: omain names: benefits and drawbacks??
A: Q: What are benefits and drawbacks of domain name system.
Q: What Exactly Is Beaconing?
A: Intro the question is about What Exactly Is Beaconing and here is the solution in the next step. ...
Q: In the case of public key encryption, if you use both the signature and encryption features, which k...
A: Intro the question is In the case of public-key encryption if you use both the signature and encrypt...
Q: Sobel Edge Detection Prewitt Edge Detection 2 different Laplacian operators 2 different Sharpen oper...
A: It is defined as a simple & powerful object-oriented programming language developed by Microsoft...
Q: What other questions must be addressed before deciding if database as a service is right for your li...
A: Introduction: Database: Individual facts, statistics, or pieces of information, frequently numerical...
Q: What is the difference between a bgp recursive lookup and a site of origin (soo)?
A: Intro BGP SOO is an extended community attribute of the BGP routing protocol that stands for BGP Sit...
Q: How can IoT change/influence your future with technology and everyday interactions with it?
A: IoT stands for Internet of things, which can things are worked using the internet.These devices can ...
Q: Solve the problem in C++ (The Rectangle class) Design a class named Rectangle to represent a recta...
A: Code: #include <iostream>using namespace std; class Rectangle{ // Two double data fields he...
Q: StormWind Studios is administrated by you, and you are in charge of it. You are in the process of in...
A: EXPLANATION: IPAM stands for Internet Protocol Address Management. It is responsible for administeri...
Q: c). Compare and contrast Deterministic Finite Automata (DFA) and Non-deterministic Finite Automata (...
A: An automaton is an abstract self-propelled computing device which follows a predetermined sequence o...
Q: What other questions must be addressed before deciding if database as a service is right for your li...
A: How it is usable or not ?? 1) Usability Consider how user-friendly the system will be for all thos...
Q: piece of information, d
A: Cache Memory Cache memory is a sort of memory that works at an extremely fast rate. It's utilized t...
Q: When a computer needs a piece of information, does it immediately perform the memory fetch operation...
A: Introduction: According to the question, the operations that occur when reading data from memory sho...
Q: What Exactly Is A Smart Card, Chip Card, Or Integrated Circuit Card (icc)?
A: Intro ICC or IC cards are physical electronic authorization devices that are used to control access ...
Q: 51) What is the distinction between a switch, a hub, and a router?
A: Intro Essentially, a switch is a more efficient and smarter form of a hub that has additional functi...
Q: Communication models that are comparable to each other include linear and interactive models.
A: Introduction: We must discover the commonalities between the linear and interactive models of commun...
Q: Write a program to calculate simple interest. The output should be display as Enter Principal Amount...
A: NOTE - I have used Java programming language to solve the given problem. Here I have taken input fro...
Q: Joe’s Catering Service Joe’s Catering Service provides meals for a few local hospitals. They would l...
A: ANSWER:-
Q: What Is the Difference Between a Broadcast Domain and a Collision Domain?
A: Introduction The question is about the Difference Between a Broadcast Domain and a Collision Domain ...
Q: using the java code below, create a new program that asks for Employees ID, then, takes the base pay...
A: As per the requirement program is completed. Note: Based on the employee table basepay and hours wor...
Q: Is there a limit to what can be done in cyberspace? What does a virtual domain's physical border mea...
A: Introduction: In cyberspace, there are, indeed, boundaries. It is necessary to develop a link betwe...
Q: Domain names: benefits and drawbacks??
A: A website may be accessed without the IP address by using the Domain Name System (DNS). The domain n...
Q: Because no new licenses have been issued in the interim, CRLS must be renewed, regardless of when an...
A: Introduction: The CRL (Certificate Revocation List) is a list of revoked certificates. They are publ...
Q: What Are Data Pockets Made Of?
A: Intro Packets are made up of two parts: the header and the payload (or data). Information about the...
Q: Using mathematical induction prove that 4" < n! if n is an integer greater than 8.
A: Note: As per our guidelines we are supposed to answer only one question. Kindly repost other questio...
Q: How many different types of memory are utilised in a Cisco router?
A: Intro When it comes to today's most demanding network services such as IP communications, video, Cus...
Q: What is the structure of a real cache hierarchy?
A: The Answer is in given below steps
Q: 6. The octal numhor (0:
A: This question is answered as follows we will regroup all these in a pair of three
Q: what is the formula for finding the number of nodes in a full binary tree
A: A perfectly balanced tree can be called when all the children nodes of right hand side and left hand...
Q: Question 2 For the shown finite state automata below: 93 start 92 1- State whether this is a DFA or ...
A: Here, we are going to check whether given FSA is DFA Or NFA. And also we are going to write the tran...
Q: Exercises Suggest a suitable domain of discourse and then express as a formula using the universal q...
A: According to the information given:- We have to write suitable domain of discourse and the express t...
Q: Though there are fresh certificates, even if no revocation requests have been created, a CRL must be...
A: Introduction: The CRL (Certificate Revocation List) is a database of revoked certificates. They have...
Q: What Exactly Is A Database Server?
A: Intro the question is about What Exactly Is A Database Server and here is the solution in the next s...
Q: 171. A network administrator is troubleshooting an EIGRP problem on a router and needs to confirm th...
A: Let's see the command need to display the required information
Step by step
Solved in 2 steps

- The __str__ method of the Bank class (in bank.py) returns a string containing the accounts in random order. Design and implement a change that causes the accounts to be placed in the string in ascending order of name. Implement the __str__ method of the bank class so that it sorts the account values before printing them to the console. In order to sort the account values you will need to define the __eq__ and __lt__ methods in the SavingsAccount class (in savingsaccount.py). The __eq__ method should return True if the account names are equal during a comparison, False otherwise. The __lt__ method should return True if the name of one account is less than the name of another, False otherwise.code: public class PasswordGeneratorAndStorage {/*** Adds an application to the applications ArrayList. If index is -1, add application* to the end of applications. Else is index is within the size of applications, add* application at that index in applications. Otherwise, return. However, if applications * or application is null, return.* * @param applications* @param application* @param index*/public static void addApplication(ArrayList<String> applications, String application, int index) {// TODO: FILL IN BODY}/*** Generates a random password of length passwordLength and adds it to the end of* passwords if index is -1, or adds it to the index of passwords if index is within the* size of passwords (similar to how the addApplication adds an application). To generate* the random password, use rand to generate a random int within the size of characters. You* can then use this int to grab the char at that index in characters and concatenate that* to your String password variable.…Computer Science Part 2: Client Program with ArrayList Create a second client program. This program will contain an ArrayList of StudentGrades objects. The program will perform the following tasks: Create an instance of an ArrayList that will store three StudentGrades objects. Each element in the ArrayList represents student grades for a test (assessment). This means that each StudentGrades object stored by the ArrayList element represents the grades achieved by students for a single test. Prompt the user for the number of students in the class. The prompt text is: Enter the number of students in the course: [Keyboard Input] Add three new StudentGrades objects to the ArrayList. The StudentGrades objects should be populated with random values from 0 to 100. Use the enhanced for loop to print each of the StudentGrades objects to the console. Print a line containing the following text: “LAST ELEMENT BEFORE REMOVE:”. Print the value of the final element in the ArrayList under the heading.…
- 1. Declare a (local) variable of type Person, create a new Object and assign the variable to this object. 2. Declare an ArrayList variable which can hold objects of type Person 3. Create a new ArrayList with objects of type Person and assign it to the existing variable persons.Write a Java class Course for dealing with courses. Your class must have the following features: Course - name: String - lineNumber: int - symbol: String - sections: ArrayList + Course() + Course(name: String, lineNumber: int, symbol: String) + getName(): String + getLineNumber(): int + getSymbol(): String + getSections(): ArrayList + addSection(section: Section): void + Override toString() method: you have to return needed data Fields values. addSection(section: Section) method add a section (number and the teacher for this section) to the array list of sections. Note: sectionNumber will be generated automatically. Write a Java class Section for dealing. Your class must have the following features: Section - number: int - teacher: Teacher - students: ArrayList + Section() + Section(number: int, techer: Teacher) + getNumber(): int + getTeacher(): Teacher + getStudents(): ArrayList + addStudent(student: Student): void + Override toString() method: you have to return needed data…****************************Instructions***************************** Add a "copy constructor" to your dynamic-array student. Remember, the prototype looks like: Classname(const classname& otherObject); Update your test program to use the copy constructor. e.g., CourseTypeList list2(list1); ********************************************************************* Submit: Updated test program, implementation and header files (.cpp and .h) for CourseListType and CourseType zipped into a single file. //courseTypeList.h #ifndef COURSELISTTYPE_H_INCLUDED#define COURSELISTTYPE_H_INCLUDED #include <string>#include "courseType.h" class courseTypeList { public:void print() const;void addCourse(std::string);courseTypeList(int n);~courseTypeList(); private:int NUM_COURSES;int courseCount;courseType *courses;}; #endif // COURSELISTTYPE_H_INCLUDED =============================================== //courseTypeList.cpp #include <iostream>#include <string>#include…
- Computer Science //iterator() creates a new Iterator over this list. It will//initially be referring to the first value in the list, unless the//list is empty, in which case it will be considered both "past start"//and "past end". template <typename ValueType>typename DoublyLinkedList<ValueType>::Iterator DoublyLinkedList<ValueType>::iterator(){//return iterator(head);} //constIterator() creates a new ConstIterator over this list. It will//initially be referring to the first value in the list, unless the//list is empty, in which case it will be considered both "past start"//and "past end". template <typename ValueType>typename DoublyLinkedList<ValueType>::ConstIterator DoublyLinkedList<ValueType>::constIterator() const{//return constIterator(head);} //Initializes a newly-constructed IteratorBase to operate on//the given list. It will initially be referring to the first//value in the list, unless the list is empty, in which case//it will be…Java Programming Define a class CollectionBooks. This class has a data member list of type Book using the ArrayList collection. Define method add. This method add the any object to list. Define printAll. This method display all the added object in the list. Define printAll. This method display all the added object in the list. · Define int count. This method returns the number of objects added in the list. Define Book search(Object e). This method returns the object being search if not found return null. Define void remove(int index). This method remove the object in a list Add a main method with the following menu:1 – Add 2 – Count 3 – Print4 – Search 5 – Delete 6 - ExitJava Program This assignment requires one project with two classes. Class Employee Class Employee Attributes (all private): id: String lastName: String firstName: String salary: int Executable Class create an array of Employee objects. create an ArrayList of Employee objects from that array. use an enhanced for loop to print all employees as shown in the sample output. create a TreeMap that uses Strings for keys and Employees as values. this TreeMap should map Employee ID numbers to their associated Employees. process the ArrayList to add elements to this map. print all employees in ID # order as shown, but do so using the TreeMap's forEach method and a lambda expression
- Use the ArrayList class Add and remove objects from an ArrayList Protect from index errors when removing Practice with input loop Details: This homework is for you to get practice adding and removing objects from an ArrayList. The Voter class was used to create instances of Voters which held their name and a voter identification number as instance variables, and the number of instances created as a static variable. This was the class diagram: The constructor takes a string, passed to the parameter n, which is the name of the voter and which should be assigned to the name instance variable. Every time a new voter is created, the static variable nVoters should be incremented. Also, every time a new voter is created, a new voterID should be constructed by concatenating the string “HI” with the value of nVoters and the length of the name. For example, if the second voter is named “Clark Kent”, then the voterID should be “HI210” because 2 is the value of nVoters and 10 is the number…private static final List<Polynomial> polyList = new ArrayList<>(); //main here public static void main(String[] args) { processPolyList(); } //=============================================================================================== // method: fromFile / returns: Arraylist // description: Opens a file takes a String and tokenizes it into an ArrayList of of expressions //=============================================================================================== public static ArrayList<String> f# define stemmer functionstemmer = SnowballStemmer('english') # tokenise datatokeniser = TreebankWordTokenizer()tokens = tokeniser.tokenize(data) # define lemmatiserlemmatizer = WordNetLemmatizer() # bag of wordsdef bag_of_words_count(words, word_dict={}): """ this function takes in a list of words and returns a dictionary with each word as a key, and the value represents the number of times that word appeared""" for word in words: if word in word_dict.keys(): word_dict[word] += 1 else: word_dict[word] = 1 return word_dict # remove stopwordstokens_less_stopwords = [word for word in tokens if word not in stopwords.words('english')] # create bag of wordsbag_of_words = bag_of_words_count(tokens_less_stopwords) Use the stemmer and lemmatizer functions (defined in the cells above) from the relevant library to find the stem and lemma of the nth word in the token list. Function Specifications: Should take a list as input and…



