$nasm -f elf .asm; ld -m elf i386 -s -o demo .0 mov len BOV MSg MOV ebx, 1 main.asm:2: error: symbol len' undefined main.asm:3: error: invalid combination of opcode and operands ld: cannot find .o: No such file or directory int Oxs0 int Ox80 section .data msg db Hello, world!',exa
Q: Select the correct answer: The illustration with a request queue (0-199), by using the SCAN…
A: Question about calculating head movement of cylinders Request queue(0-199) Using SCAN disk…
Q: a. How is a 16-bit memory address divided into tag, line number, and byte number?( 16 bitlik bir…
A: a. It is given that the machine is a byte addressable 216with bytes. This indicates the memory…
Q: 1. 2. 3. path="/files" 5. 6. 10. 11. import os 7. 8. from openpyxl import load_workbook 12. 13. 15.…
A: Below I have provided Python Programming. Also, I have attached the screenshot of the code and…
Q: 1. Which of the following is the fastest approach for large amount of data 1/O? a. Polling direct…
A: Option d: Memory-mapped I/O is suitable for devices which move quantities of data quickly. Option…
Q: How many bytes starting at address Ox401080 in memory/heap are being modified while running the…
A: The correct answer is 8 option D 8 bytes starting at address 0x401080 in memory/heap are being…
Q: of address (676)8 with primary partition (four 16 bytes en
A: What is the size in octal of MBR of address (676)8 with primary partition (four 16 bytes entries)?…
Q: DOS file names are in what format 255.3 128.3 3.8 8.3
A: DOS file names are in 8.3 format other format are not any file name .
Q: 7. Write a program for the paper computer that will read two numbers and print the absolute value of…
A:
Q: The free space bitmap looks like this: 1010 0000 0000 0000: The system always searches for free…
A: One block size is 4 KiB. Initial bitmap: 1010 0000 0000 0000
Q: Virtual Memory lets us isolate programs so they can’t share/corrupt data. What is an advantage of…
A: as we can see in the question statement itself, isolate programs can't share or corrupt data. so…
Q: . _____ method is used to map logical addresses of variable length onto physical memory. a. Paging…
A: Dear Student, In segmentation the memory is divided into segments and the logical addresses are…
Q: Operand addq %rcx,(%rax) subq %rdx,4(%orax) imulq $16, (%orax,%rdx,4) incq 8(%rax) decq %rcx subq…
A: byte register Bytes 0-3 Bytes 0-1 Byte 0%rax %eax %ax %al%rcx %ecx %cx %cl%rdx %edx %dx %dl%rbx %ebx…
Q: Computer Science 1. List all lines in all .c files in the current working directory that
A: Answer has been explained below:-
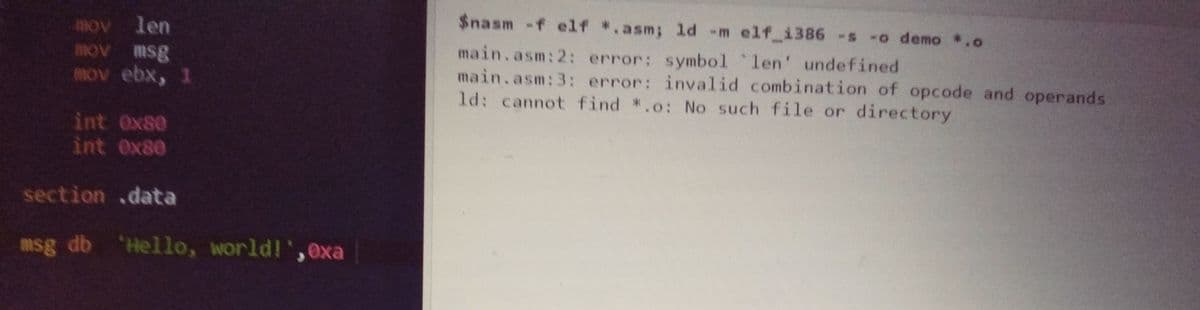
Q: $nasm -f elf . asm; ld -m elf_i386 -s -o demo.o len AORE msg AO MOV ebx, 1 main.asm:2: error: symbol…
A: section .data msg: db 'Hello world!',10 ; 'Hello world!' plus a linefeed character len: equ…
Q: c) Suppose a disk has 300 cylinders, numbered from 0 to 299. The drive is currently serving an I/O…
A: (i) SSTF Total head movements- 10+24+10+75+10+18+3+18=168
Q: What is buffering? a. The blocks read from disk are directly accessed b. The blocks read from disk…
A: Given : What is buffering?
Q: In the context of operating systems, which of the following statements is/are correct with respect…
A: The answer is
Q: nsider the following scenario: ere are outstanding I/0 requests for blocks on the following…
A: In SCAN algorithm, all the request will be satisfied which are in direction of movement of head.…
Q: A e sy wih elevel deectory wtrcts is implemted ona dik with disk dock sie of K bytes The disk is…
A: The answer is here
Q: Example-8.6 Suppose that a block is 1K Byte and that a disk address is 4 bytes. Suppose that files…
A: Solution Here each block can hold 28 = 256 address ( = 1 KB / 4 B ) Hence , third level indirect…
Q: mgsters hold the most active pagr entres and able take I80 s, what must the hit ratio be t ive ry If…
A: The hit ratio to be achieve an effective access time of 125ns is
Q: movlw movwf Cirf rw Loop: addwf. temp1,0%3: btfsc incf decfsz COUNTER, 1 goto Addlw Movwf NOP OX03…
A: Dear Student, movlw 0x03 will store the value of 0x03 in register W. movwf COUNTER will move the…
Q: 4- Open a new COM file and assemble the following code: MOV MOV BН. 3 RPT: ADD CL, 5 DEC JNZ HLT CL,…
A: According to the given information. we have to run the program and fill the table.
Q: 31 The disk scheduling algorithm that suffers from starvation is SSTF SCAN FCFS LOOK
A: Here in this question we have asked that which disk scheduling algorithm suffer from starvation.
Q: Write an AVR C program to read the content of location OX005F of EEPROM into PORTB. Solution:…
A: Given,
Q: Thrashing b. Three allocation methods which refers to how disk blocks are allocated for files…
A: Note: There are multiple questions are given in one question. According to the rule, you will get…
Q: the hexadecimal address of dueDate ?
A: The hexadecimal address of due Date
Q: The NX (“no execute”) bit can also be supported by modern CPUs. To force a CPU to avoid running the…
A: Please see the next step for answer.
Q: Source string: Array1 '8886' what is the value in destination string ? Destination string: Array2…
A: Here, given condition is to copy string of array1 to array 2 . In the given statement SUB DI, 2…
Q: 5.How many bytes in the memory will be occupied by short int array[10] 10 Bytes 20 Bytes 40 Bytes…
A: Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: CBLOCK 0x000 ; i, j, k ; ENDC ORG 0 goto…
A: Actually, given question regarding assembly programming.
Q: Assume that you have a program that has a part at the beginning that is sequential in nature (for…
A: Answer:-
Q: What are the contents of the file registers WREG, 0x010, 0x020, 0x410, 0x420, after the following…
A: Given:
Q: 000 memor L, cache (Firs n the L, cach iss penalty fror các
A:
Q: The following data segment starts at memory address 1700h (hexadecimal) .data printString moreBytes…
A: Need to find the hexadecimal address of DueDate for the given data segment which starts at memory…
Q: after the execution of Line 18 in the fo1loving code? Ensure you ansver includes the "S" aign - e.g…
A: It is defined as high-speed memory storing units. It is an element of the computer processor. It can…
Q: A kernel object that is 5 KB in size will be stored in a(n) Q-KB slab. What should be the value of…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: must be declared for using gcc tell linker entry point $nasm -f elf *.asm; 1d -m elf_i386 -s -o demo…
A: The code is
Q: Computer Science Create a PowerShell script that handles the following information. The script must…
A: In this question we have to write a Power Shell script with the help of looping and array for the…
Q: Which of the following is/are restriction(s) in classless addressing ? a. The number of addresses…
A: All a, b, c are restrictions in classless addressing as per definition of classless addressing.
Q: Consider the following ls -l output: -rwxr-xr-- 2 fred users 0 Jan 26 13:08 22…
A: 1) The output of ls -l shows perrmisson given to a file sample.mp3 2) -rwxr-xr-- 2 fred users…
Q: ________ allows only committed data to be read, but does not require repeatable reads a. Read…
A: Repeatable read allows only committed data to be read and further requires that no other transaction…
Q: For the following data definition: .data value: .word 15 letters: .byte 'T', 'i', 'm' num:…
A: Given The answer is given below.
Q: Q1. An executable file for a certain assembly language program has been uploaded to memory via the…
A: Given: Write the necessary debug command to run this program. Write a necessary debug command to…
Q: Can u explain this code in detail. I will Upvote :
A: Explanation The above code accepts the size of the file and the size of a page. Using the size of…
Q: Typing ps alone lists the current running processes. lab3.c can be compiled as, gcc –o lab3 lab3.c.…
A: Note : As per policy i can answer one question at a time . Kindly resubmit the question separately .
Q: We pointed out that I/O buses do not need separate address lines. Construct a timing diagram similar…
A: The control signal can be either “error” or “ack.” so, it can be added with the control signal for…
Q: Write short notes on any 4 of the following: [4x4] a. Thrashing b. Three allocation methods which…
A: Solution:
Q: Mnemonic, Operands ADDWF 1, d ANDWF 1, d CLRF f CLAW COMF 1,d DECF f. d DECFSZ 1.d INCF 1, d INCFSZ…
A: It is defined as a low-level programming language for a computer or other programmable device…
Sort out MISP code bugs
Step by step
Solved in 2 steps

- in fedora 37 1. Create a directory named Module9 and navigate to that directory. 2. Copy the file pay.dat from Module8 to Module9. Here it is again, just in case: 0001:John Smith:15.40 0002:Jane Smith:15.41 0003:George Jungle:12.10 0004:Ursula Jungle:16.11 3. Using a pipe symbol for filtering and sort the data to stdout. Enter: cat pay.dat | sort 4. Now, on your own, using a pipe symbol for filtering and sort the data in descending order to stdout and append that to a file named SortPay.dat. 5. Copy pay.dat to three files named: pay10,dat, pay12.dat, and pay02.txt. You may need to use multiple commands. 6. Use pattern matching to locate only pay02.txt. 7. Enter the command to remove pay2.dat and redirect both stdin and stdout to a file named RemovePay.txt. 8. Run the command in step 7 again. 9. Display the contents of RemovePay.txt 10. Take screen captures please explain each step and take screenshotsCan someone please look at my script and explain why the data is not being read and entered into my pretty table? Any help is appreciated. Script is below. I am getting an empty pretty table as my output. # Python Standard Library import os from prettytable import PrettyTable myTable = PrettyTable(["Path", "File Size", "Ext", "Format", "Width", "Height", "Type"]) dirPath = input("Provide Directory to Scan:") i f os.path.isdir(dirPath): fileList = os.listdir(dirPath) for eachFile in fileList: try: localPath = os.path.join(dirPath, eachFile) absPath = os.path.abspath(localPath) ext = os.path.splitext(absPath)[1] filesizeValue = os.path.getsize(absPath) fileSize = '{:,}'.format(filesizeValue) except: continue # 3rd Party Modules from PIL import Image imageFile = input("Image to Process: ") try: with Image.open(absPath) as im: # if success, get the details imStatus = 'YES' imFormat = im.format imType = im.mode imWidth = im.size[0] imHeight = im.size[1] #print("Image Format: ", im.format)…Minix Suppose a file is on a filesystem using a 1K block size. This file is maintained on thedisk using i-nodes as is typical on many UNIX filesystems (as described on pages 286-287 and789-790 of your text). Suppose there are seven direct pointers, and then a pointer to one singlydirect block, a pointer to a doubly indirect block, and a pointer to a triply indirect block. Suppose aprogram creates and opens a file in this filesystem, and then seeks to the following positions,writes a character, and then exits. Identify how many disk blocks, (both data and indirect blocks)must be allocated to store the data for the file. (Note that a-c each represent a different file.)a. Seek to 9000b. Seek to 300000c. Seek to 67,000,000How big would a file need to be to require the triply indirect pointer?
- Understanding how to interpret (or trace) an existing PowerShell script is vital when searching for PowerShell scripts on the Internet that suit a particular administrative need. Trace the PowerScript script shown in below and write a short memo describing what it will do after being executed: $list = get-childitem | sort-object foreach (objItem in $list) {if ($objitem.attributes - contains "directory") {$fgc="cyan" }elseif ($objItem.Extension -eq ".ps1") {$fgc="blue" }elseif ($objItem.Extension -eq ".exe") {$fgc="green" }elseif ($objItem.Extension -eq ".zip") {$fgc="red" }elseif ($objItem.Extension -eq ".rar") {$fgc="red" }else { $fgc="yellow" }write-host $objItem.name, $objItem.Length, objItem.LastWriteTime-foregroundcolor $fgcCreate File comparators that arrange files in ascending/descending order of file size, ascending/descending order of file name, and ascending/descending order of last modification date. Employ these comparators in LS, a programme that accepts a command-line input and lists the files in the current directory in a certain order, such as "-t" to sort by timestamp.To break ties, support several flags. Be certain you use a reliable sort.Make steps on how to encode it Output: org_contents = """I WOULD NOT LIKE THEM HERE OR THERE. I WOULD NOT LIKE THEM ANYWHERE. I DO NOT LIKE GREEN EGGS AND HAM. I DO NOT LIKE THEM, SAM-I-AM.""" with open('decrypted.txt', 'r') as f: contents = f.read() assert(org_contents == contents)
- Modify pipe4.cpp so that it accepts a message from the keyboard and sends it to pipe5. //pipe4.cpp (data producer) #include <unistd.h> #include <stdlib.h> #include <stdio.h> #include <string.h> int main() { int data_processed; int file_pipes[2]; const char some_data[] = "123"; char buffer[BUFSIZ + 1]; pid_t fork_result; memset(buffer, '\0', sizeof(buffer)); if (pipe(file_pipes) == 0) { //creates pipe fork_result = fork(); if (fork_result == (pid_t)-1) { //fork fails fprintf(stderr, "Fork failure"); exit(EXIT_FAILURE); } if (fork_result == 0) { //child sprintf(buffer, "%d", file_pipes[0]); (void)execl("pipe5", "pipe5", buffer, (char *)0); exit(EXIT_FAILURE); } else { //parent data_processed = write(file_pipes[1], some_data, strlen(some_data));…CODE IN JAVAYou have 01 computer and a file containing 10 billion random 64-bit numbers. The goal is to take the top 5000 highest values from the file.Assuming that each comparison would take 10ns and disk reading takes no time.dataarr DWORD 10 DUP (?)str byte "generating Random numbers",0.codemain PROCmov ESI, OFFSET arrmov ECX ,LENGTHOF arrcall myexitmain ENDPmy PROClea edx,strcall writestringcall randomizeL1:call random32mov [esi],eaxadd esi,type arrloop L1retmy ENDPend main (2) Write another procedure that takes 10 32-bit signed numbers from user and store them in anotherarray named arr1(3) Display values from any array on screen (4) Display a string at 5 different secreen locations(5) Display a string in 10 random foreground and background colorsCall all of these procedures in your main in the same sequence
- Question 5: findWrite a simple version of the Linux find program: find all the files in a directory tree whose namematches a string.Some hints:·Look at ls.c to see how to read directories.·Don’t try to find any files in the “.” and “..” directories.·Changes to the file system persist across runs of QEMU; to get a clean file system run makeqemu.Your solution is correct if produces the following output (when the file system contains a file a/b):$ make qemu ...init: starting sh$ echo > b$ mkdir a$ echo > a/b$ find . b./b./a/b$2. Exploring envp:a. Modify showEnvp.c so it reports envp addresses in the same style as showArgs2 displays argv addresses. Save a copy of the output in a file – you’ll need to refer to it in part b. Provide a program listing, a status statement and 6-8 lines of output, but not all the output. (2)b. Inside your program use putenv to define one environment variable and setenv to redefine another. Do these values appear in the array envp or __environ or both? (2)c. Based on the program output sketch a data structure diagram for envp. You only need to include the first 3 environment variable values (2) Hand in a commented listing of your program, proof of testing and a status report. On your cover page, aside from your name, the course code, lab section and the assignment #. Make sure you include your student number. If I have to look it up to verify that you are doing the correct exercise - 2 marks off. If you do the wrong exercise 2 more marks will be deducted showEnvp.c#include…True or False: Logical extractions are bit-by-bit copiesof the file system, including deleted data.

