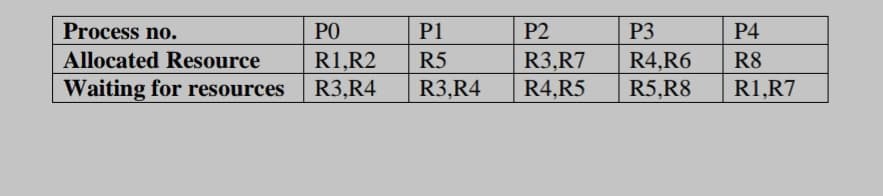
Draw a wait for graph to detect deadlock in given situation.
Q: Question:: What's the difference between Stored Procedures and Scripts? WWhat is the purpose of each...
A: Answer: I have given answered in the brief explanation
Q: Instructions: Identify the following if it is UNIQUE IDENTIFIER or NOT. Company / Organization Name...
A: INTRODUCTION: A unique identifier is one that is guaranteed to be distinct from all other identifie...
Q: Convert each of the following arguments into formal statements e,g define sentences existentially an...
A: Answer: First, break the argument into premises and a conclusion. P1 = if you do the homework you wi...
Q: Given the following memory chip configurations find the requested information: An EPROM chip has a c...
A: a) Organisation - 16K *8 8 - Data Pins and 14- address Pins b) Organisation - 16*4 4 - Data Pi...
Q: Considering a linked list A that has the following elements: 1, 9, 4, 7, 2, 15, 23, 26, 11, 8. Write...
A: Code - Output -
Q: What is CCT, exactly?
A: Answer :-
Q: Exercise-2: Design an algorithm that takes two arrays, and returns true if the arrays are disjoint, ...
A: - Solving the first question. Kindly post the remaining separately. - We are solving the disjoint ar...
Q: Is "work position" an UNIQUE IDENTIFIER or NOT?
A: Answer : Is "work position" an UNIQUE IDENTIFIER or NOT? Solution : No. Work position is not an U...
Q: Write a javascript program to prove that symbols are immutable.
A: Required:- Write a Javascript program to prove that symbols are immutable. Approach:- Make 2 objects...
Q: the Boolean expression for the follow
A: Groups (3,7) B.C (5,7) A.C (6,7) A.B
Q: Case Exercises Amy walked into her office cubicle and sat down. The entire episode with the blond ma...
A:
Q: Do parallel/distributed databases have a distinct advantage over centralized ones?
A: Hello student, greetings from my side. Hope you are doing well.
Q: I am trying to make a discord NSFW filter bot that: -Automatically removes messages that are flagge...
A: Below i have answered:
Q: When did the first desktop computer appear?
A: Here is your answer.
Q: Write a Java program to find the number of words in the user entered String. for example:- i/p : "Aw...
A: Required:- Write a Java program to find the number of words in the user entered String. for example:...
Q: What About Microsoft Exchange?
A: Introduction The question is about Microsoft Exchange and here is the solution in the next step.
Q: Hello, Can someone please help me with this homework assignment?! I seem to keep messing it up... Th...
A: My explanation is in the comments. Read the comments of printIntersection method.
Q: Describe a real-world CSP, the solution it offered, and the local and global impact it had.
A: Constraint fulfillment issues are mathematical problems that are described as a set of objects whose...
Q: As a worst-case scenario, the whole institute might be destroyed if a war takes place. What would yo...
A: Summary: - Hence, we have discussed all the points.
Q: Identify the following if it is UNIQUE IDENTIFIER or NOT. Name Age Phone Number
A: - We need to know if the identifiers shown are unique or not.
Q: O Create a cell array named CA containing six cells to store the short form of the first six month n...
A: A cell array is a data type with indexed data containers called cells, where each cell can contain a...
Q: ******Describe the scheduling techniques that the operating system can employ to manage I/O demands ...
A: INTRODUCTION: Operating systems use disc scheduling to schedule I/O requests that arrive at the dis...
Q: examples of telecommunication service providers that sell or provide same product or service in Mala...
A: Maxis Communication Celcon (Axiata) Digi Communication
Q: Consider the MIPS I format instruction. This format is divided into 4 fields as shown here. A B C D ...
A: 1) All MIPS instructions are encoded in binary.and are 32 bits long. 2) All instructions have an op...
Q: Draw the adjacency list and adjacency matrix Draw BFS and DFS trees Apply BFS and DFS algorithms
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any ...
Q: 10). In is fixed. interrupts the starting address
A: According to the question vectored interrupts helps makes starting the service to assign for the dis...
Q: What's the difference between Stored Procedures and Scripts? What is the purpose of each? How does e...
A: Stored procedures and scripts are two different SQL constructs used to perform SQL statements within...
Q: Identify databases that should have been Unified but are not. (Example: the BMV database and the IRS...
A: The answer is
Q: Question 1: List two advantages and two disadvantages of having international standards for network ...
A: Below is the advantages & disadvantages of above query. I hope this will meet your requirements.
Q: Write a Java program to find the number of words in the user entered String. for example:- i/p : "Aw...
A: We are going to write a java program which will count the number of words in the user entered string...
Q: i want a feasabily report to fix a problem within a gated community from manual to a website
A: How to write a feasibility study 1.Describe the project. 2.Outline the potential solutions resulting...
Q: Write a Java program that prompts the user to enter a security code that matches a specific pattern....
A: Thw java code is an given below : Java Code: import java.util.*;import java.io.*;import java.lang.*;...
Q: What exactly are secondary images, and what do they imply?
A: Introduction: Secondary image means a spurious or ghost image, in addition to the bright primary ima...
Q: to install an autonomous server room that runs without human intervention. A lights-out server room ...
A: For detecting a fire, I would use an air-aspirating detector. It may be more expensive, but it is on...
Q: Please help to write 2 pages on Emations and user experience. The subject is Human computer interact...
A: Introduction: Human-computer interaction (HCI) is a multidisciplinary topic of research that focuses...
Q: What are your thoughts on VMware cloud computing?
A: Intro VMware is a virtual machine. Virtual machine helps us install a specify OS on our machine w...
Q: A + B[AC + (B + C’)D]
A: Distributive law:- A(B+C)= A.B + A.C Other basic law applied:- A.A=A , (A+1)=1
Q: What security flaws are exploited and how may these issues be addressed in the future in the case of...
A: The answer is given below:-
Q: In this assignment you are to implement OOP principles you learned in a single mini project. 1. Defi...
A: PROGRAM EXPLANATION: Create an interface Measurable. Define a single abstract method in this interf...
Q: Need SML help for coding. I need to define a function called decimal (val decimal = fn: string -> in...
A: Function: int binary_To_Decimal(string num){ int decimal_value = 0; int x = 1; int length = num.le...
Q: Alice and Bob use the ElGamal scheme with a common prime q = 131 and a primitive root a = 6. Let Bob...
A: Answer is given below-
Q: Is there a difference between a system subsystem and a logical division?
A: Introduction: Subsystem: A unit or piece of equipment is part of a more extensive system. For examp...
Q: Question No 2 There are many programming languages for specific software solution, then justify give...
A: Answer :-
Q: 7-Write a procedure that returns the list that contains everything except for the last element of th...
A: first we have to write scheme code and then run that code on an scheme compiler: As per the example ...
Q: Is there a difference between a system subsystem and a logical division?
A: Answer: Yes, In System subsystem can be defined as is a predefined environment which generally coord...
Q: What is the definition of an inline function?
A: Introduction: An inline function is one for which the compiler transfers the code from the function ...
Q: What is the definition of an inline function
A: Introduction: An inline function is one for which the compiler transfers the code from the function ...
Q: Instructions: Identify the following if it is UNIQUE IDENTIFIER or NOT. Dat
A: According to the Question below the Solution:
Q: A rocket is launched vertically. At time t= 0, the rocket's engine shuts down. At that time, the roc...
A: Code: time=0:0.5:30;heights=height(time); %bplot(time,heights) %c the rocket starts to fall%back tow...
Q: import bridges.base.ColorGrid; import bridges.base.Color; public class Scene {
A: Constructors in java 1. Types of constructors a. Default Constructorb. Parameterized Constructor2.co...
Draw a wait for graph to detect deadlock in given situation.
Step by step
Solved in 3 steps with 1 images

- In the event of an impasse, it becomes necessary to terminate said processes, thereby leading to the subsequent consequences:A segment of code that cannot be entered and executed by more than one process at the same time is called _________________. deadlock critical section semaphore mutex A process that does not enter a critical section but also prevents other processes from entering is creating _______________. deadlock mutual exclusion lockout starvation Multiple processes that block each other indefinitely from entering a critical section are creating _____________. mutual exclusion starvation deadlock logout Using semaphores. s = 0 initially.Process p1 executes the sequence: P(s); V(s); P(s); V(s);Process p2 executes the sequence: V(s); V(s); P(s); V(s); After both processes terminate, s=________. 3 1 0 2 A monitor is a low-level kernel function that implements a priority queue. True or false Processes can access and modify monitor variables without having to call the monitor's functions. True False The correct monitor implementation of c.wait…There are two methods available for terminating processes and, accordingly, overcoming deadlocks:
- Can a single-threaded process deadlock by itself? Please elaborate on your answer.please select only correct option : 1) In ………………. only one process at a time is allowed into its critical section * a, Synchronization b, Mutual Exclusion c, Deadlock d, All of the given 2) To avoid race condition, ____ process(es) at a time can manipulate the shared variable. * a, One b, Two c, Three d, None 3) Process synchronization can be done through * a, Hardware b, Software c, Both Hardware and Software d, None of the given 4) For better memory-space utilization ________ is used a, Dynamic loading b, Static loading c, Dynamic linking Static linking d, All of the given 5) Peterson algorithm is restricted to ___ processes * a, One b, Three c, Five d, None of the givenTerminating processes and breaking deadlocks are accomplished via the use of two different ways.
- Suppose we have three processes P0, P1, and P2. Process P0 executes statement S0 and process P1 executes statement S1 and process P2 executes statement S2. Use wait and signal to ensure the following: S2 is always executed before S1 and S1 is always executed before S0S0.2) ______ is a situataion where one process is withheld due to other process. a) multi operating b) dead lock c) multi-programmingA system has three processes (P1,P2, P3) and three resources (R1,R2, R3). There is one instance of R1 and R2. There are three instances of R3. P1 holds an R1 and is requesting an R3. P2 holds an R3 and is requesting an R1. P3 holds two instances of R3 and an R2. Does a deadlock exist? Justify your answer.
- There are two techniques for stopping processes and resolving impasses:It is recommended that, in the event of a standstill, those processes be terminated, which will result in the following outcomes:ProcessBurst Time Priority Arrival TimeP1 10 3 0P2 1 1 0P3 2 5 0P4 1 4 0P5 5 2 0For the set of processes directly above, draw a Gantt chart for the FCFS Scheduling Algorithm.

