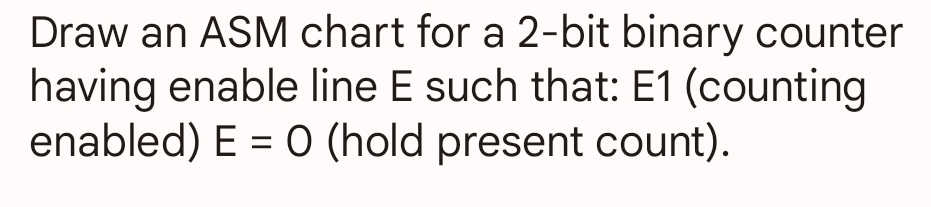
Draw an ASM chart for a 2-bit binary counter having enable line E such that: E1 (counting enabled) E = 0 (hold present count).
Q: What evaluation approaches would you work to gauge the effectiveness of a machine learning model?
A: evaluation approaches would you work to gauge the effectiveness of a machine learning model given in…
Q: What is the primary advantage of DBPSK and what is its disadvantage?
A: INTRODUCTION: The networking of computers:A computer network is a group of networked computers.…
Q: How might an operating system's architecture change as a result of being able to support a large…
A: How might an operating system's architecture change as a result of being able to support a large…
Q: What is the advantage and disadvantage of angle modulation.
A:
Q: Normalize the data (use mean and mean absolute deviation). Use a 3 nearest-neighbor algorithm to…
A: Solution :
Q: You are to write a short program using dictionaries. Create a dictionary object that will store key…
A: The complete python code is below:
Q: Problem4: Assume two banks want to establish a secure communication channel so that they can share…
A: Python used to answer this question
Q: What steps would you suggest taking to protect the company's network against hackers?
A: Cybersecurity Network Protection: We hear from companies facing cyber attacks every day. Most…
Q: matlab code for 3-D surface z=5x^2+0.5y^2 with -2<x<=2 and -2<=y<=2
A: Editable Matlab soruceCode: % We define vectors x & y : x = points between the -2 and…
Q: Recent audit findings indicate that asset management was not given enough attention or training…
A: Introduction: InvestmentsIn every organisation, good management of investments is vital for growth.…
Q: Consider the following piece of code. animals = {'a': "ant", 'b': "baboon", 'c': "cat"}…
A: The solution is given in the below step with explanation
Q: onsider the following piece of code. animals = {'a': "ant", 'b': "baboon", 'c': "cat"} animals['d']…
A: The correct answer is given below with explanation
Q: et the processes P1, P2, P3, P4, and P5 be given. They arrive in the system at the same time in this…
A: Check step 2 detail explanation with Answer,
Q: In a nutshell, how would you protect your company's network against cyberattacks?
A: Cybersecurity network protection We hear from companies facing cyber attacks every day. Most of…
Q: 9. Write the following code segment in MARIE's assembly language: Sum = 0; for X = 1 to 10 do Sum =…
A: The answer for the above question is given in the following step for your reference.
Q: Define the term medium access control mechanism
A: Define the term medium access control mechanism answer in below step.
Q: Write MATLAB code to define variable t as p= 3.9; then evaluate: ep-9.65p³
A: We will be using MATLAB to solve the above problem:
Q: Are you familiar with adding data about users to a database?
A: Introduction: A database is an organised collection of structured information or data that is often…
Q: Use JFLAP to draw the required state diagram. Name the JFLAP project file as Q2.jff and upload it as…
A: The complete code using JFLAP diaagram Turing Machine is below
Q: Define - AMAT.
A:
Q: that affect the user experience. Are they essentially the same thing? Under what circumstances does…
A: Dear Student, The answer to your question with required explanation is given below -
Q: When it comes to developing effective information systems strategies, how useful is the Porter…
A: Introduction: The strategic position of the organisation and its related strategies are determined…
Q: How many different types of cyber threats will your business be able to prepare for if you implement…
A: Introduction: Cybersecurity: Internet and digitally reliant enterprises are changing cyber security…
Q: Distinguish between band FM and wide band
A: We need to distinguish between band FM and wide Band FM.
Q: Draw an ASM chart for a 2-bit binary counter having enable line E such that: E1 (counting enabled) E…
A:
Q: Discuss State Assignment.
A:
Q: Distinguish between band FM and wide band FM.(Dec'13)
A: Introduction: In contrast to private signals that are sent to specific receivers, broadcasting is…
Q: How do you check to see whether a record in a database really exists?
A: We can check it using Exists operator Any record in a subquery can be checked for existence using…
Q: Define Bit Time and Baud Rate.
A: The question is to define Bit Time and Baud Rate.
Q: What is direct-mapped cache?
A:
Q: Explain What is State Reduction.
A:
Q: What is one possible conflict or issue that can arise from the commodification of users by social…
A: Solution : Introduction : Social media platforms have greatly facilitated people's daily lives in…
Q: Define What is Transition Table?
A:
Q: Give recommended steps for the design of a clocked synchronous sequential networks.
A: In this question we will understand how to design CSSN (Clocked Synchronous Sequential Network)…
Q: Mention Application of ASM chart.
A: Introduction In this question we are asked about the application of ASM chats
Q: What is the difference between error and exceptions in java?
A: Difference between error and exceptions in java Both exceptions and errors are the subclasses of a…
Q: When working with 1024K words, how many address bits are required?
A: GIVEN: A software programme called a database management system (DBMS) is used to store and retrieve…
Q: What are the various memory technologies?
A:
Q: 2-b) Explain why differential pulse code modulation (DPCM) coding with exponenti difference-values…
A: Differential pulse code modulation is a method of simple to computerized signal transformation. This…
Q: Step1. The following code copies a string from source to target: .data source BYTE "This is the…
A: Assembly Language: Low-level programming languages like assembly languages are created to…
Q: Illustrate your algorithm by showing on paper similar to Fig. 8.3, page 198 in the textbook (make…
A: This is very simple. Here is how the Radix Algorithm works. Given array is 45, 98, 3, 82, 132, 71,…
Q: 6. What is the 2 type of security? 7. What is computer security example? 8. What are security…
A: According to Bartleby Guidelines we need to answer only three sub questions so I have answered first…
Q: C language (Linux environment
A: Introduction C programming language is a type of programming language which provides the basic…
Q: What are the types of pulse modulation systems and define them?
A: Answer the above question are as follows
Q: Explain what a "real-time system" is for those who have never heard of it before.
A:
Q: Evaluate the following expression. Give the final value of x. Your answer is either a 1 or a 0 if…
A: The correct answer is given in the below step with explanation
Q: Which tool is helpful for finding entries that match a specified pattern in Linux system logs?…
A: The complete answer is below":
Q: Real-time scheduling: In a system consisting of two processes, P1 and P2, suppose process P1 has a…
A: Hi please find the solution below and I hope it would be helpful for you.
Q: What is the primary advantage of DBPSK and what is its disadvantage?
A:
Q: -. In a distributed database system, account A is stored in database A at location A and account B…
A: Given that, There are two accounts that are Account A and Account B. $100 transferred from Account…
Step by step
Solved in 2 steps with 2 images

- A(n) _____ operation transforms a 0 bit value to 1 and a 1 bit value to 0.Take the 127-bit binary BCH code with a 6-bit target distance and the 128-bit binary field extension F 128. How big is the code, and is there a minimum separation you can promise?A repetition code is an [n, 1] Code in which the n - 1 parity bits are repetitions of the information bit. Is this repetition code a linear code ? What is the minimum distance of the code ?please given step by step solution.
- In ___________ there is always a transition at the middle of the bit, but the bit values are determined at the beginning of the bit. If the next bit is 0, there is a transition; if the next bit is 1, there is none. a. Manchester b. differential Manchester c. both (a) and (b) d. neither (a) nor (b)Take the 127-bit binary BCH code with a 6-bit target distance and the 128-bit binary field extension F 128. How large is the code, and is there a minimum distance you can guarantee?Parity is a function in which the output depends on the number of 1s in the input. For an even parity function, the output is 1 if the input has an even number of ones. Suppose a ROM is used to implement an even parity function with a 4-bit input. Which of A, B, C, or D represents the contents of the ROM?
- Recognize the differences between ternary and three binary connections.Design a sequence detector of the pattern 0100 where the circuit accepts a serial bit stream *X" as input and produces a serial bit stream *2° as outputWhenever the bit pattern *0100* appears in the input stream, it outputs 2 = 1: at all other times, 2 = Q Overlapping occurrences of the pattern are also detected,Consider the Cyclic Redundancy Check (CRC) algorithm discussed in Section 6.2.3 of the textbook. Suppose that the 4-bit generator (G) is 1011, that the data payload (D) is 10011101 and that r = 3. What are the CRC bits (R) associated with the data payload D, given that r = 3?
- In a Von Neumann architecture, groups of bits have no intrinsic meanings by themselves. What a bit pattern represents depends entirely on how it is used. The following table shows bit patterns expressed in hexadecimal notation.In CRC, if the dataword is 5 bits and the codeword is 8 bits, how many 0s need to be added to the dataword to make the dividend? What is the size of the remainder? What is the size of the divisor? What is the maximum effect of a 2-ms burst of noise on data transmitted at the following rates?Under the Binary Convolutional Codes for a 100-bit codeword how many check bits are needed? What is the code rate in this example?

