e error in 100 words. Decriotion is need
Q: In this lesson, i want you to make the passive buzzer sing. I want you to write a code in C language…
A: Answer:- Component Required:(1) x Sintron Uno R3(1) x Passive buzzer(2) x F-M wires (Female to Male…
Q: Explain BasIc concepts of data WarehousIng?
A: Building and using a data warehouse is known as data warehousing. Data from several heterogeneous…
Q: Real-world examples should be used to illustrate the significance of dynamic programming.
A: In the given question Dynamic Programming is a technique in computer programming that helps to…
Q: Examine the distinct development approaches used in the creation of the Windows and Android…
A: SOLUTION:A computer's operating system is a piece of software that allows the machine to work. It…
Q: When it comes to computers, architecture and computer-based organisation are two different ideas.
A: Answer:- Introduction: Computer-based architecture: It involves the way physical components/units…
Q: What does "virtualization" in the context of cloud computing really mean?
A: Cloud computing is a general term for anything that involves delivering hosted services over the…
Q: Why are segmentation and paging commonly confused? What is the meaning of the term thrashing?
A: Intro Thrashing: Thrashing is the state that occurs in a virtual storage system when there are an…
Q: Think about how crucial wireless networks are in today's developing countries. Wireless technologies…
A: Introduction: Wireless networking is one of the most widely used and rapidly expanding technologies…
Q: Wireless networking offers advantages and disadvantages. Because of security concerns, should…
A: The Answer is in step2
Q: It is crucial to define OLAP's function in descriptive analytics.
A: A computing technique called OLAP (online analytical processing) enables users to quickly and…
Q: A deeper examination of how wireless networks are used in developing nations is worthwhile. In…
A: Introduction: Wi-Fi is a wireless technology that connects computers, tablets, cellphones, and other…
Q: What three criteria must a profitable and effective network possess to be successful? Provide an…
A: Definition: A network is created when several computers are connected in order to share resources,…
Q: In terms of throughput speed, wireless networks are faster than wired networks, but they are slower…
A: Business networks are complex, and many things can go wrong, disrupting network performance. End…
Q: Refer to the data types listed in Table 2-6 for these questions.A) If a variable needs to hold…
A: Lets see the solution.
Q: Is there a difference between static and dynamic type checking?
A: Type:- Also, known as datatype. example, int, float, double, Boolean. there are divided into…
Q: Why are segmentation and paging commonly confused? What is the meaning of the term thrashing?
A: Answer:- Thrashing is the state that occurs in a virtual storage system when there are an excessive…
Q: Describe in detail three advantages and disadvantages of paging as a memory management strategy.
A: Given Give three specific benefits and drawbacks of using paging as a memory management approach.
Q: Why is a JVM's method area shared by all of the threads running inside of it, in your opinion?
A: Introduction: Java Virtual Machine (JVM) = JVM is the engine that powers Java Code. => It…
Q: This section will concentrate on the three-sphere paradigm for system management. Avoid employing…
A: Administration of computer systems based on a model with three spheres: The following problems may…
Q: What are the most recent methods for defending your database against online attacks?
A: INTRODUCTION: A database is a planned grouping of material that has been arranged and is often kept…
Q: How do you recognise when it is advantageous to organise processes and programmes into subsystems…
A: Given: Solution: Advantages of Distributed Processing 1. Useful Distributed units are efficient over…
Q: hes and database keyword searches vary significantly from one another. What are the main variations…
A: Introduction: Keywords are key words or concepts in your research question or thesis. Choosing the…
Q: Wide area networks (WANs) and local area networks (LANs) compete in terms of usefulness, technology,…
A: Introduction: WANs and LANs are contrasted in terms of utility, technology, and management. A local…
Q: Think about how crucial wireless networks are in developing countries. Why are some firms moving…
A: According to the following, WIFI networks, as wireless communication is often known, offer far more…
Q: How can linked lists represent adjacency lists inside a graph? Give an instance. No coding is…
A: Introduction: To represent the graph in Adjacency List, we use an array of a list. The length of the…
Q: Think about how crucial wireless networks are in today's developing countries. Wireless technologies…
A: Wireless technologies have taken the role of cables and conventional local area network(LANs) in a…
Q: Do you think that each thread running on a virtual machine is using the same JVM method area?
A: Given: Virtual Machine for Java (JVM)Java code is driven by the JVM. Java bytecode is transformed…
Q: What precisely is "scrubbing" in the context of RAID systems, and why is it so crucially important
A: Scrubbing is a strategy for correcting mistakes that utilizes a foundation interaction to do visit…
Q: Can MAC addresses on two network interfaces be shared? Or not? Can an IP be shared across two…
A: A Media Access Control or- MAC address is a one-of-a-kind identification number given to every…
Q: An associative cache is what?
A: Given: The primary memory is seen as two fields in an associative cache. These areas are for tags…
Q: A company's network may connect up to 70 different workstations in three different locations using a…
A: Given: There will be two different issues when 1000 Mbps NICs are used in place of 100 Mbps NICs.One…
Q: One method for breaking into a network is the rerouting of malicious traffic across VLANs. It's…
A: One method for breaking into a network is the rerouting of malicious traffic across VLANs. It's…
Q: How does the Model-View-Controller paradigm fit into the overall structure of web applications?…
A: Introduction: Model, View, and Controller: Model, View, and Controller (MVC) is an architectural…
Q: How do you handle a dispute when two devices on your local network have the same MAC address? That…
A: Introduction: Is it feasible for two machines to have MAC addresses that conflict with one another?…
Q: Why are segmentation and paging commonly confused? What is the meaning of the term thrashing?
A: Definition: Thrashing is a state in which there are too many paging operations happening in a…
Q: Describe how Application Programming Interfaces (APIs) may be used to assist the integration of new…
A: API integration is especially important for companies that serve multiple cloud applications and…
Q: Voice and video traffic are handled differently than other types of data, for reasons that should be…
A: Introduction: For obvious reasons, the network treats audio and video differently than other data…
Q: Let's say a bank uses snapshot isolation database technology to protect its database. Do you provide…
A: When bank uses snapshot isolation database technology. It might use store the data using the image.
Q: Write a program for Execution Time of a Python Program
A: The program for the execution time of a python program are as follows :
Q: Briefly describe one of the cache protocols that is accessible.
A: In the given question cache is hardware or software that is used to store something, usually data,…
Q: Explain the purpose of data compressiontechniques.
A: A reduction in the amount of bits required to represent data is known as the data compression. Data…
Q: Why may stack systems describe arithmetic expressions using reverse Polish notation?
A: what is the reverse polish notation : In the reverse polish notation the expression is written in…
Q: A deeper examination of how wireless networks are used in developing nations is worthwhile. In…
A: Given: Wi-Fi is a wireless technology that connects computers, tablets, smartphones, and other…
Q: What kind of computations do experts believe will be performed exclusively by artificial…
A: Introduction: An artificial intelligence (AI) system, computer-based simulation of human…
Q: Could you kindly clarify what you mean by the term "partitioning" in regard to computer operating…
A: Introduction: Partitioning can give considerable advantage to a wide variety of applications by…
Q: Between the operating system and a user application, two totally different representations of a…
A: Introduction: Virtual machines (VMs) let you run an operating system in a separate app window on…
Q: When is it beneficial to break up large computer programmes and processes into subsystems? What…
A: It is not a novel concept to use network segmentation as a means of increasing network security. As…
Q: Wireless networks are widely used in developing countries. Wireless technologies are displacing…
A: We have to explain that wireless networks are widely used in developing countries. Wireless…
Q: In terms of throughput speed, wireless networks are faster than wired networks, but they are slower…
A: Wireless networking serves as a connection between various equipment locations in residences,…
Q: Let's say a bank uses snapshot isolation database technology to protect its database. Do you provide…
A: Given: Tabase that has been organised in such a way that it can be accessed and examined in a short…
Write error in 100 words. Decriotion is needed. And complete.
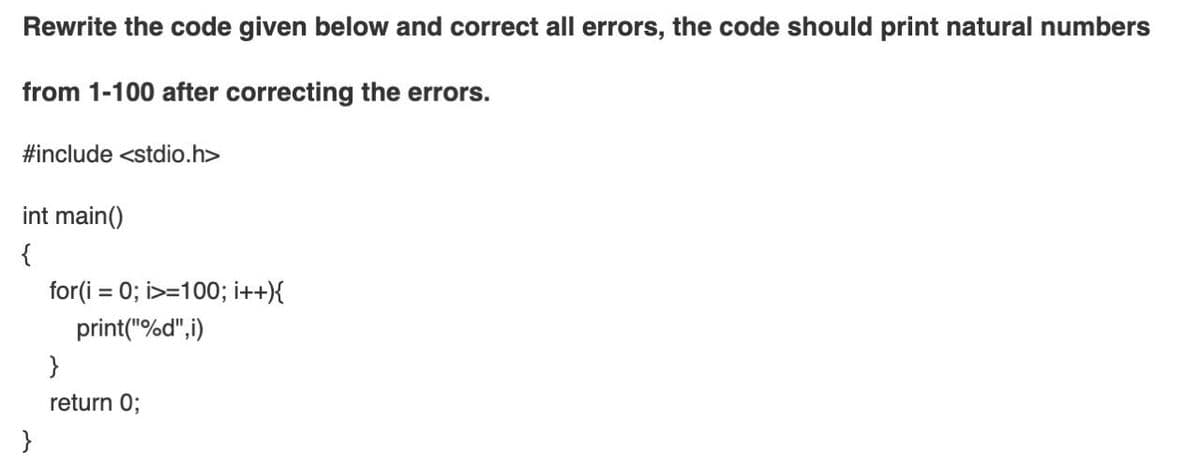
Step by step
Solved in 2 steps with 1 images

- This Code print the first occurrences of x, Modify the code to print the last occurrences of x and print how many times it exists? ( with explanation for each line if possible) many thanks.Rewrite the following code segment using a multiple selection statement in JavaI want a code like this, but it's a subtraction
- Consider the following statement:int* p, q;This statement could lead to what type of misinterpretation?Can you help me with the codes required for this assignment? the programming langauge is Java. (Sort three integers) Write a program that prompts the user to enter three integers and display the integers in non-decreasing order. Sample output:Enter three integers: 10 2 7 2 7 10In last program I forget to talk about remainder and quotient. Take 2 numbers and find these in java
- Consider the code below. char letters[26]; for(int i = 0; i < 26; i++) { letters[i] = 'A' + i; } printf("%c", letters[24]); printf("%c", *(letters + 4)); printf("S"); What does this code print?Rewrite the program with a little bit of changes in the codes... #include <stdio.h> int READING ();int ADDING (int NUM1, int NUM2);int SUBSTRACT (int NUM1, int NUM2);int MULTIPLY (int NUM1, int NUM2);float DIVIDE (int NUM1, int NUM2);void PRINT (int NUM1, int NUM2, int TOTAL, int SUBS, int MUL, float DIV); int main(){ int NUM1, NUM2, TOTAL, SUBS, MUL; float DIV; NUM1 = READING (); NUM2 = READING (); TOTAL = ADDING (NUM1, NUM2); SUBS = SUBSTRACT (NUM1, NUM2); MUL = MULTIPLY (NUM1, NUM2); DIV = DIVIDE (NUM1, NUM2); PRINT (NUM1, NUM2, TOTAL, SUBS, MUL, DIV); return 0; } int READING (){ int NUM; printf("Please enter a number "); scanf("%d", &NUM); return NUM;} int ADDING (int NUMBER1, int NUMBER2){ int TOT; TOT = NUMBER1 + NUMBER2; return TOT;} int SUBSTRACT (int NUMBER1, int NUMBER2){ int SUB; SUB = NUMBER1 - NUMBER2; return SUB;} int MULTIPLY (int NUMBER1, int NUMBER2){ int MUL;…What is the run-time (T(n)) and complexity of the following code segment? int y = 0; for ( int a= 0; a< n; ++a ) { for ( int b= 0; b < a; ++b) y += j;}

