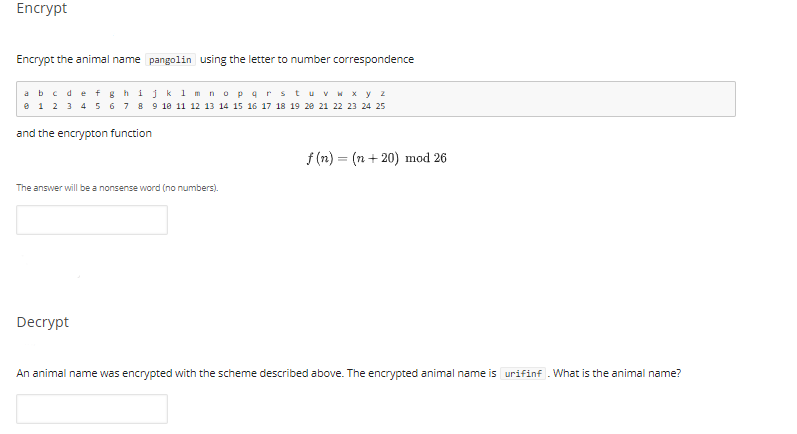
Encrypt the animal name pangolin using the letter to number correspondence abcdef shijk 1 mnopar stuvw x y z e 1 2 3 4 5 678 9 18 11 12 13 14 15 16 17 18 19 28 21 22 23 24 25 and the encrypton function f (n) = (n+ 20) mod 26 The answer will be a nonsense word (no numbers). Decrypt An animal name was encrypted with the scheme described above. The encrypted animal name is urifinf . What is the animal name?
Q: Is this a tautology? ((p v q)^¬p) –→ q O True False
A: A preposition logic is a statement in which it states whether it is True or False. There are…
Q: how many 11 - strings (that is, bit strings of length 11) are there which: a. start with sub -…
A: Given: how many 11 - strings (that is, bit strings of length 11) are there which: a. start with sub…
Q: olve each of the following:
A: The first three parts will be answered. 1) a) Given floating point IEEE 754 Single precision 32-bit…
Q: omputer Engineering Lab Please me solve this erro in the below coder:Error Message -> IndexError:…
A: I have provided errorless code in step2
Q: Is this a tautology? ((p V q)^¬p) → q O True O False
A: Tautology
Q: The function that is not implemented by the karnaugh map shown below is XYI WZ 00 01 11 10 00 X 01 X…
A: Here in this question we have given a k-map and we have to find that which function can't be…
Q: Implement the topology provided Implement backpropagation for 100 (for two input 200) random…
A: The rand () function generates the next random number in the sequence. The number generated is the…
Q: Let M be the turning machine defined by 1 B 90 (q1X.R) (q3, Y.R) 91 (q1,0,R) (q2.Y.L) (q1,Y.R) 92…
A: Given: Given the transition function of a Turing machine we have to trace Computation for the…
Q: Rules of encryption are as follows:
A: Program structure Import necessary classes from the util and io package in the program. Create the…
Q: 2. Simplify the following Boolean expressions, using four-variable maps: (a) F1=w'z + xz + x'y +…
A: Part a) =========
Q: by the following pro symbo S: S = FQQ | FaaQ H = N F = DDba | MDabMb N = bMG | GGbR T = MEaa | aabND…
A: A non-terminal is said to be reachable if it is included in derivation of any string of the…
Q: Given a systematic (15, 11) cyclic code with a generator polynomial: G(x)=x++x³+1 Question: In…
A: The question is to find the terms included in syndrome polynomial.
Q: A Boolean function F(A,B.C.D) is described by E2,3,8,10,11,12,14,15.lf using K-map the function is…
A: Karnaugh maps are a representation method for simplification of Boolean functions of up to six…
Q: Express F as product of maxterms: F(a,b,c) = (a+b)c
A: Let's try to solve all the given options and see the result:
Q: Two aspirants talking to each other use the RSA algorithm to encrypt their messages. They encrypt…
A: Introduction:
Q: Using only string methods, devise a way to determine if a nucleotide sequence is a palindrome in the…
A: As no programming language is mentioned, so I am using Python. In step 2, you will get the code. In…
Q: Describe the condition for the jump to occur in the following code segment: Cmp eax, 3 jnb loc…
A: The answer for the above code segment is given below:
Q: Here is the encryption key for an affine transformation like we saw in lecture: C = 5P + 2. This…
A: Solution:
Q: Two aspirants talking to each other use the RSA algorithm to encrypt their messages. They…
A: Introduction:Here we given the following data as follows :
Q: 3. Give the following FAs over the alphabet Σ = {0,1,2} a-) A DFA for { strings in which the number…
A: Below is the Answer-
Q: What is the correct postfix expression of the given infix expression below (with single digit…
A: The right answer will be option(b) 2439-*86/*+ Explanation:- for converting the infix to postfix you…
Q: Define the following variant of the Fibonacci sequence called Fib3 in C programming language : ●…
A: This code works fine in less as you said.
Q: This is a simple cipher to linear S-box: P2 P1 Po +) kz k, ko X2 X1 Xo 3 x 3 S-box Co = Xo O X1 C1 =…
A:
Q: Given two numbers: n: number of consecutive letters beginning at a k: string length Output all…
A: Given two numbers: n: number of consecutive letters beginning at a k: string length Output all…
Q: a) For a bit string S, let S denote the complement, obtained by swapping every 1 for a 0 and every 0…
A: Introduction: DES Algorithm: The Data Encryption Standard (DES) is a symmetric-key block cipher…
Q: Simplify the function F represented by the following Kmap into 4 terms 9 literals SOP expression: AB…
A: The K map layout is given by: The K map using minterms as given in the figure is given by: The…
Q: using kmp algorithm for string matching find the pattern p= (0010) availability in the text…
A: For the string matching problem, Knuth-Morris and Pratt implement a linear time algorithm. By…
Q: Please me solve this erro in the below coder: Error Message -> IndexError: list assignment index…
A: The above error is occurring because you have declared the list answer = [ ] of 0 length but we…
Q: Let A = {c, n, b}, B = {x, y} and C = {0, 1}. Find A)A X B X C B)C X B X A C)B X C X C
A: Here in this question we have given three set and based on these set we have asked to do some…
Q: make a MIPS function called _compare that compares two strings stored in $a0 and $a1, if they are…
A: Make a MIPS function called _compare that compares two strings stored in $a0 and $a1, if they are…
Q: In time 7 after trace computation for string * :aabbbcccdd machine in state q3 q5 O q6 O q4 O Answer…
A: - We have to trace the state in which the machine will be after 7 times for the string aabbbcccdd.…
Q: A language has an alphabet of four letters x¡, i = 1,2,3,4, each occurring with probability1/4 Find…
A:
Q: An animal name has been encoded using the letter to number correspondence bedefs hijk 1nopars e 1 23…
A:
Q: The Reflection algorithm can be used to encrypt a C-string (character array terminated with the null…
A: Ans a. String be encrypted to by the Reflection algorithm?“Call me at 662-2002 Ext 85393” So in…
Q: QUESTION 1 "Given strings: spring and nursing , what would be the sequence of operations produced by…
A: According to the information given:- We have to find the correct option to satisfy the statement.
Q: Let E = {0, 1} and A, B be the list of three strings each. Verify below PCP has a solution or not?…
A: The Answer is in below Steps
Q: The function that implements karnaugh map shown below is АBICD 00 00 01 1 11 10 01 X X 1 X 11 1 1 1…
A: The given karnaugh table has AB defined for downside and CD defined for rows :: if we select the…
Q: Let U={x|x is a positive integer and equal less than 10}, A= {x|x is a postive integer less than 10…
A:
Q: Consider the hex strings A=0x274dce4716a5705c and B=0x98d54fc92cd0eed0. a) What is A O B in…
A: a. A = 0x274dce4716a5705c (Hexadecimal) B = 0x98d54fc92cd0eed0 (Hexadecimal) A ⊕ B =…
Q: For the following netlist write a code in python for VLSI placement with simulated annealing M2…
A: import Module import PortIn import PortOut import PortClk import ConfigParser from ordereddict…
Q: c) Simplify the expression [(a'^b)v (a v b')]v (a'nb ^c) by using the laws of Boolean algebra. d)…
A: Simplified the given boolean expression
Q: Recall that a bit string is a string of Os and 1s Describe the following sequence recursively.…
A: Answer is given below-
Q: Implement the modular exponentiation (a.k.a. fast exponentiation) function mod_exp (b, n, m) to…
A: ANSWER : a) def fast_exp(b, e, m): r = 1 if 1 & e: r = b while e: e…
Q: Diffie-Hellman Key exchange is based on the difficulty of solving the Discrete Logarithm Problem.…
A: Answer in step 2
Q: The prefix search of the expression 8 (3- 1) + 2 x 5 is O a. 8 ÷ 3 – 1+2\tims5 O b. +-318 x 25 O c.…
A: Correct Option d. None
Q: In any bit string, the longest consecutive run length is the maximum number of consecutive 1's or…
A: Solution is :
Q: Write a Python code that returns the reverse complement of a given DNA sequence E -NM AA ||| B IA 深…
A: A string s is passed to the method reverseComplement which contains the DNA sequence. we need to…
Q: 4. Let n be a positive even integer. How many functions f: {0, 1}" {0,1}" are there that satisfy…
A: Answer: I have given answered in the handwritten format in brief explanation.
Q: Consider the following decoding tree diagram and choose the correct source code Start 0. S1 S2 S3 $4…
A: Decode a tree To decode a tree , a path is taken from root node to the required leaf node and store…
Q: Let S be the set of bit strings of length four or more. For example, 10011l e S, 00111100 e S, or…
A: A relation is an equivalence relation if it satisfies all of the conditions Reflexive: a,a∈R ∀a∈R…
Step by step
Solved in 2 steps

- Substitution ciphers are encryption/decryption algorithms that replace one letter or number with another. The first attested use of a substitution cipher in military affairs was by Julius Caesar, described by him in Gallic Wars (cf. Kahn pp83-84). In caesar cipher , you replace each letter by 3rd letter on. If it is out of bound (later than Z), then round to the head (letter A) and continue the shift. For example:meet me after the toga party PHHW PH DIWHU WKH WRJD SDUWB Please write a program in Java to implement the Caesar Cipher: a. Implement the encryption algorithm. Ask the user to input one all lower case normal sentence (called plaintext) using the nextLine method, and then output the encrypted text (called ciphertext). b. Implement the decryption algorithm. Ask the user to input one encrypted sentence (i.e. ciphertext) using the nextLine method, and then output the decrypted text (i.e. plaintext).FIX ME: In C language Update this function to display the string of 16 bits using the following pattern: 11111 111111 11111 (5) (6) (5) */ void printbits(unsigned short wrd) { int testbit(unsigned short wrd, int bit_to_test); int i; for (i = 15; i >= 0; i--) { printf("%1d", testbit(wrd, i)); if (!(i % 4)) printf(" "); } printf("\n"); }A data.frame: 6 × 2 train_label distance <fct> <dbl> 2 1 3.9301694 3 1 5.8230155 4 1 0.4738137 5 1 1.3395091 6 1 0.4699036 7 1 0.9272197 Write a Python code to sort collectbased on distance in ascending order (from lowest to highest) and only show the first 9 rows and call it Nine_neighbors
- A binary number is to be transfromed by appending three 0's to the end of the number. For example , 11101 is transformed to 11101000. Which of the following best dewcribes the relationship between the transformed number and the original.- The transfromed number is 3 times the value of the original number- The transformed number is 4 times the value of the original number- the transformed number is 8 times the value of the original number- The transformed value is 1000 times the value of the original numberC programming Implement an encoder. When completed, your program should be able to accept a short sentence from the user and display an encrypted version of it. For simplicity, let us assume one case of letters throughout, say CAPITALS. We can use a substitution method to scramble a sentence and then use the reverse of this process to recover it. If we take two rows of the alphabet and shift the bottom row along a specified amount (our key), we can then read the letters in our sentence from the top row and use the substituted letter from the bottom row to form the encrypted sentence. A B C D E F G H I J K L M N O P Q R S T U V W X Y Z X Y Z A B C D E F G H I J K L M N O P Q R S T U V W In the example above, the key is 3, hence the second row is shifted by three characters along. Take, for instance, the sentence “HELLO”. Each letter of your message should be replaced by the letter in the alphabet that comes three letters before. For “HELLO” that would be: EBIIL Your program is required…Transcribed Image Text As the Halloween evening is approaching you and your friend decided to decorate the house in such a way that there is N snow globes in a row, numbered 1 through N from left to right. Each globe can be in two colours "blue" or "white". Initially, all the globe are "blue". You decided to reach a state described by a given a binary string S with length N for each valid i, if the ith character of S is '1', the jth globe should be "white", and if it is '0', the ith bulb should be "blue". Develop a C++ code to find the minimum number of globes to be in the "blue" state Input Output 53 10110
- Given two binary strings,return their sum (also a binary string).For example,a = "11"b = "1"Return "100".""" def add_binary(a, b): s = "" c, i, j = 0, len(a)-1, len(b)-1 zero = ord('0') while (i >= 0 or j >= 0 or c == 1): if (i >= 0): c += ord(a[i]) - zero i -= 1 if (j >= 0): c += ord(b[j]) - zero j -= 1 s = chr(c % 2 + zero) + s c //= 2Write Python Code Farmer John is worried for the health of his cows after an outbreak of the highly contagious bovine disease COWVID-19.In order to limit transmission of the disease, Farmer John's N cows ( 2<=N<=105) have decided to practice "social distancing" and spread themselves out across the farm. The farm is shaped like a 1D number line, with M mutually-disjoint intervals (1<=M<=105) in which there is grass for grazing. The cows want to locate themselves at distinct integer points, each covered in grass, so as to maximize the value of D, where D represents the distance between the closest pair of cows. Please help the cows determine the largest possible value of D. INPUT FORMAT (file socdist.in): The first line of input contains N and M. The next M lines each describe an interval in terms of two integers a and b, where 0<=a<=b<=1018. No two intervals overlap or touch at their endpoints. A cow standing on the endpoint of an interval counts as standing on…Binary Search? When Jojo was a little kid, his teacher asked him a question. What was the answer of 1^2+2^2+3^2+...+N^2? Of course that problem was hard enough for a primary student. Buts ince he is a university student, and he knows that the answer is 1/6∗N∗(N +1)∗(2N +1), such problem is to easy for him. Now Jojo came up with a new problem. If he has an integerM, what is the smallest integer N such that 1^2 + 2^2 + 3^2+ ...+N^2 is greater than or equal to M. After thinking for some time, he came up with a solution, but his solution takes a lot of time. Since you are his nemesis, he challenges you to solve the problem quicker than him. Of course you accept his challenge! Format InputThe first line is an integer T representing the number of test cases.For each test case there will be 1 line consisting of an integerM. Format OutputFor each test case output “Case #X: N”. X is the test case number andN is the smallest integer such that 1^2 + 2^2 + 3^2+ ...+N^2is greater than or equal to…
- Computer Science you are given a string X of length n and another string Y of length m ≤n. Say,the indexes p1, p2, p3, p4 and q1, q2, q3, q4 form two sub-sequences, i.e., 0 ≤ p1 < p2 < p3 < p4 < nand 0 ≤q1 < q2 < q3 < q4 < n; then, they are non-overlapping if p4 < q1.The task is to count the maximum number of non-overlapping sub-sequences of X that are thesame as Y . Thus, if X = GAXTYAWBGTAUGBTABGRGTAXB and Y = GTAB, then the answer is3 as shown by the red fonts. We cannot select the underlined GTAB as it overlaps with a red GTAB(i.e., among overlapping sub-sequences, you can select only one of them).Describe an O(m + n) time algorithm to obtain the count. Write a pseudo-code.Using foldl, define a function num2int :: [Int] -> Int -> Int that converts a list of numbers and the number n into an integer of base n. >num2int [3,4,5,6] 10 3456 >num2int [1,1,0,1,0,0,0,1,0,1,0,1,1,0] 2 3456 num2int :: [Int] -> Int -> Int num2int x y = foldl (\acc (a,b) -> ___a___ + b*y^a) 0 (___b___ (\x y ->(x,y)) [0..] (___c___ x)) fill in blank spaces of a , b , and cA number of the form a + ib, in which i2 = -1 and a and b are real numbers, is called a complex number. We call the real part and b the imaginary part of a + ib. Complex numbers can also be represented as ordered pairs (a, b). The addition and multiplication of complex numbers are defined by the following rules: (a + ib) + (c + id) = (a + c) + i(b + d ) (a + ib) * (c + id) = (ac - bd) + i(ad + bc) Using the ordered pair notation, these rules are written as: (a, b) + (c, d) = ((a + c), (b + d )) (a, b) * (c, d) = ((ac - bd ), (ad + bc)) C++ has no built-in data type that allows us to manipulate complex numbers. Construct a data type, complex Type, that can be used to process complex numbers. Overload the stream insertion and stream extraction operators for easy input and output. We will also overload the operators + and * to perform addition and multiplication of complex numbers. If x and y are complex numbers, we can evaluate expressions such as x + y and x * y.

