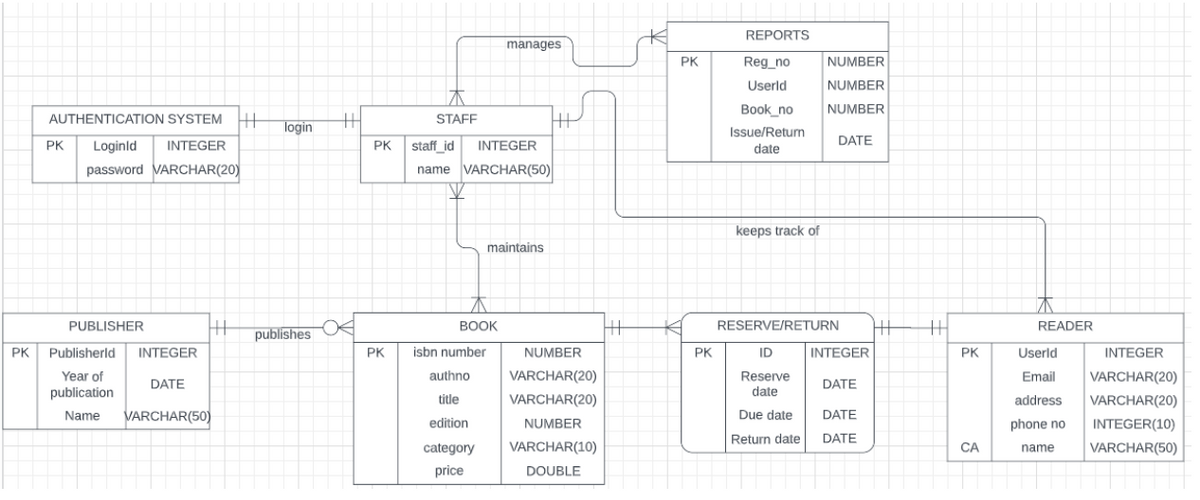
Enhanced entity-relationship (EER) Diagram of Library Management System Please explain the flow of this EER Diagram in words or any way that you want to explain. Thank you so much
Enhanced entity-relationship (EER) Diagram of Library Management System Please explain the flow of this EER Diagram in words or any way that you want to explain. Thank you so much
Chapter7: Developing An Excel Application
Section: Chapter Questions
Problem 3RA
Related questions
Question
Enhanced entity-relationship (EER) Diagram of Library Management System
Please explain the flow of this EER Diagram in words or any way that you want to explain. Thank you so much
Transcribed Image Text:PK
AUTHENTICATION SYSTEM H
PK Loginld INTEGER
password VARCHAR(20)
HH
PUBLISHER
Publisherld
INTEGER
Year of
publication
DATE
Name VARCHAR(50)
login
publishes
TH
STAFF
PK staff_id INTEGER
name VARCHAR(50)
maintains
PK
BOOK
manages
isbn number
authno
title
edition
category
price
HP
NUMBER
VARCHAR(20)
VARCHAR(20)
NUMBER
VARCHAR(10)
DOUBLE
HH
PK
PK
REPORTS
Reg_no
Userld
Book no
Issue/Return
date
keeps track of
RESERVE/RETURN
ID INTEGER
Reserve
DATE
date
Due date
DATE
Return date
DATE
NUMBER
NUMBER
NUMBER
DATE
HH TH
PK
CA
READER
Userld
INTEGER
Email VARCHAR(20)
VARCHAR(20)
address
phone no
INTEGER(10)
name
VARCHAR(50)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage