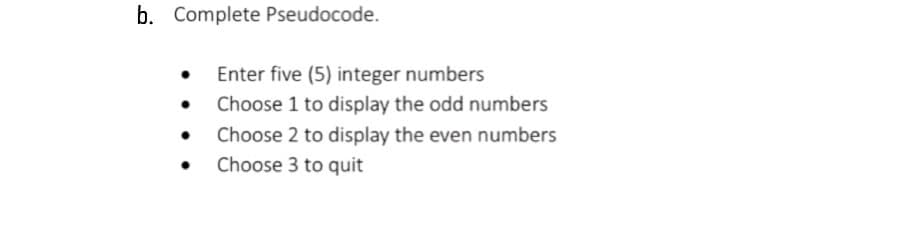
Enter five (5) integer numbe Choose 1 to display the odd Choose 2 to display the ever Choose 3 to quit
Q: How can Virtual Network Functions, which are implemented in software, improve the network's…
A: Virtual Network Functions (VNFs) are software-based network services that replicate the…
Q: The architecture of a CPU may consist of a universal register, a singular accumulator, or a stack.…
A: The CPU, the computer's brain, can be designed based on different architectures - Universal…
Q: It makes flexible multiprocessor systems available. The system's complexity grows with its…
A: What is multiprocessor systems: Multiprocessor systems are computer systems that have multiple…
Q: Please detail the numerous dangers HTTPS safeguards against and the steps it takes to do so.
A: Hypertext Transfer Protocol Secure (HTTPS) is an encrypted version of the HTTP protocol used for…
Q: Write a program that continues accepting user inputs as float numbers until the input is an empty…
A: In this program, we use a while loop to continuously accept user inputs until an empty string is…
Q: Create a CRUD matrix to check the consistency between your domain model class diagram (create it)…
A: To check the consistency between the domain model class diagram and the list of use cases provided,…
Q: Explain how contemporary cloud computing usage have helped the world.
A: Contemporary cloud computing has revolutionized the way individuals and organizations store,…
Q: What are the various types of polymorphism that are possible? What are the most significant…
A: The idea of polymorphism in object-oriented programming ( also abbreviated as OOPs ) enables…
Q: Given the following snippet of kernel code: int4 v1 = (int4) (2, 0, -1, 3); int4 v2 = (int4) (-1, 2,…
A: In the realm of programming, kernels are crucial elements in parallel computing environments. They…
Q: } public String getPassword() { return password; } public void setUserName(String userName) {…
A: Dear Student,Our goal here is to output the customer's password. To achieve this, the cust object…
Q: dosage = 100 time_since_last_dose = 7 is_nighttime = False took something_cross_reactive = False…
A: According to the information given:-We have to follow the instructions in order to get the desired…
Q: 5. What is the difference between the reliability and the availability of a system?
A: “Since you have posted multiple questions, we will provide the solution only to the first question…
Q: driving
A: Dear Student,An auto driving car requires many different tasks to be completed, such as computer…
Q: Create a programme REMOVE_DUPLICATES that removes sequentially occurring duplicate entries in a list…
A: Start with an input list L.Create an empty list called result to store the non-duplicate…
Q: How many different types of polymorphism are there? Can you explain the key distinctions between the…
A: Polymorphism, derived from the Greek words "poly" (many) and "morph" (form), is a critical concept…
Q: Use drawings to show the differences between scalar and superscalar processors. Compared to scalar…
A: Explanation :A processor, or central processing unit (CPU), is the main component of a computer…
Q: IN Java: Complete main() to read dates from input, one date per line. Each date's format must be…
A: I have done the code using Java language, Make sure you are on latest version of Java.
Q: Relationships may help reduce the size of a database by eliminating unnecessary data duplication…
A: In the realm of database management, relationships play a vital role in optimizing data storage and…
Q: The best linkedlist has how many nodes? Which lasts longest?
A: What is linkedlist:A linked list is a data structure consisting of a sequence of nodes, where each…
Q: How do we track data requests?
A: Data request tracking refers to monitoring, logging, and from time to time analyzing the…
Q: When compared, the Internet and the World Wide Web (WWW) have some fundamental differences. What are…
A: 1) The Internet and the World Wide Web (WWW) are two fundamental components of the modern digital…
Q: Describe a mobile agent and explain how it can be a potential security threat? Give two examples of…
A: 1. A software application known as a mobile agent can move freely from one networked computer to…
Q: What should be done first in order to implement a solution for corrupted data?
A: The first step towards implementing a solution for corrupted data is identifying the problem.…
Q: (A deque. A circular N-dimensional one-dimensional array is to be used to implement DQUE. Run the…
A: Follow the instructions below to create a deque using a circular one-dimensional array:Create a…
Q: need help in java. (1) Prompt the user for a string that contains two strings separated by a…
A: Import the necessary Java libraries: java.util.Arrays, java.util.List, java.util.Scanner,…
Q: What exactly is meant by the term "Access Point" when discussing wireless networks? Just how does it…
A: In wireless networking, an 'Access Point' (AP) is ironware that bridges the gap between radio and…
Q: Why is data transmission via serial bus superior to parallel bus? What disadvantages does serial bus…
A: Serial and parallel buses are two common methods for transmitting data within a computer system or…
Q: What are the two types of services available via Internet-downloaded apps? What makes these services…
A: Hello studentGreetingsIn today's digital era, Internet-downloaded apps offer a wide range of…
Q: What new features has StuffDOT added to make it easier to use?
A: 10 StuffDOT is an online and mobile shopping platform that focuses on lifestyle products. It…
Q: What purpose does the information security management system serve?
A: A organization for management information security (ISMS) is a systematic approach to managing…
Q: Explain the current applications of cloud computing and how they have benefited the entire planet.
A: Cloud computer knowledge has paved the way for altering how companies and individuals control and…
Q: Given the following information: CL_DEVICE_MAX_WORK_ITEM_SIZES: CL_DEVICE_MAX_WORK_GROUP_SIZE: Which…
A: In the given scenario, we are provided with the maximum work item sizes and the maximum work group…
Q: Design a Mealy machine to detect when a value is not BCD, for example when 1111 is generated it…
A: To design a Mealy machine that detects when a value is not in BCD (Binary Coded Decimal) format, we…
Q: Create the truth table for F2 without simplifying the expression F₂ = ABC + ACD + ABC
A: A truth table is a table used in logic to display all the possible combinations of truth values…
Q: In Java create an automobile class that will be used by a dealership as a vehicle inventory program.…
A: import java.io.FileWriter;import java.io.IOException;import java.util.ArrayList;import…
Q: You want to design an arithmetic adder/subtractor logic circuit. (a) List the steps you will take in…
A: SOLUTION -
Q: 6 28.5 12 32 25 12 0 7.5 40 4 7 34 36 20 28.5 8 4 28 25 9 33 9 31 32 8 20 28 16 37 11 17 1 2 3 29 1…
A: the steps to analyze the given dataset and answer the questions using statistical calculations.…
Q: I'd be very grateful if you could provide TWO potential ways out of any data security issues.
A: Hello studentGreetingsData security is a critical concern in today's digital age, as organizations…
Q: Create a SinglyLinkedList method named reverse that reverses the order of the list's items. This…
A: Linked lists are data structures that consist of nodes with data and pointers to the next node. The…
Q: We consider the multi-authority secure electronic voting scheme without a trusted center. How do the…
A: Multi-authority secure electronic voting schemes without a trusted center are designed to ensure the…
Q: File systems often use sequential media to store file blocks. Why is it crucial while working with…
A: Magnetic disks store data sequentially, such as hard disk drives (HDDs). This characteristic is…
Q: Weak entities mean what? Key is... Example needed. What's "various specialisation"?Does the ER…
A: weak entity:It is an entity that cannot be uniquely identified by its attributes alone; therefore,…
Q: In Java, what allows for the manipulation of data variables in a class? Group of answer choices:…
A: The manipulation of data variables in a class refers to the ability to perform operations on those…
Q: Compare cloud computing to mobile devices. Cloud computing allows for substantial mobile device…
A: Cloud compute plus mobile devices are two divide but more and more entwined technology areas. Cloud…
Q: How challenging was it to install a system that all employees of the company could use? Please…
A: Installing a system that all employees can use effectively within a company is complex and…
Q: Cloud-hosted apps provide advantages over client-based storage.
A: Cloud-hosted applications offer the ability to access data from some place at any time, given near…
Q: After listing the different cloud computing services, the following part explains how organisations…
A: Organizations utilize cloud computing to manage their resources in a variety of ways. Here are some…
Q: Create a programme that uses a single stack and a single queue to determine whether a string is a…
A: The task requires us to create a programme that identifies whether or not a given string is a…
Q: When compared to other forms of network traffic, why are voice and video calls treated differently?…
A: Voice and video calls are often treated differently from other forms of network traffic due to their…
Q: What capabilities does the operating system of a desktop computer possess?
A: The question is getting some information about the capacities or functions that the operating system…
Max Function
Statistical function is of many categories. One of them is a MAX function. The MAX function returns the largest value from the list of arguments passed to it. MAX function always ignores the empty cells when performing the calculation.
Power Function
A power function is a type of single-term function. Its definition states that it is a variable containing a base value raised to a constant value acting as an exponent. This variable may also have a coefficient. For instance, the area of a circle can be given as:
Step by step
Solved in 3 steps

- (Calculating the Product of Odd Integers) Write a program that calculates and prints theproduct of the odd integers from 1 to 15.Warm-up: Integer Operations Write a program that asks the user to enter two integers and prints the Difference, Product, Area of an Ellipse, and Average of these numbers. Here is an example of the execution of the program:Test Average Write a program that asks for five test scores. The program should calculate the average test score and display it. The number displayed should be formatted in fixed-point notation, with one decimal place of precision. C++
- 3. The formula for determining compound interest is: A represents the amount to earn; P is the principle that is initially invested; r is the interest rate earned; n is the number of times the interest is compounded; and t is the number of time periods for the investment. Write a program that prompts the user to enter P, r, n and t. The program should output the amount earned on the investment. 4. Look up the Pythagorean theorem if you are not already familiar with it. Use the following formula to solve for c in the formula: c = √a2 + b2. Use the proper functions from the cmath header file. Be sure to output the result.l(Calculating the Sum of Even Integers) Write a program that calculates and prints the sumof the even integers from 2 to 30.MAKE PSEUDOCODE AND FLOW CHART FOR THIS CODE #include <iostream> int main() { int num,x,y,z; std::cout<< "Enter a 3 digit number :"; std::cin>> num; x=num%10; num=num/10; y=num%10; num=num/10; z=num; num=100*x+10*y+z; std::cout<<"The reverse of your number: "<<x<<y<<z; return 0; }
- (Algebra: solve 2 * 2 linear equations) A linear equation can be solved using Cramer’s rule given in Programming Exercise 1.13. Write a program that prompts the user to enter a, b, c, d, e, and f and displays the result. If ad - bc is 0, report that “The equation has no solution.”Ready program that prompts the user to input two positive numbers A dividend and divisor(Find numbers divisible by 5 and 6) Write a program that displays, ten numbers per line, all the numbers from 100 to 1,000 that are divisible by 5 and 6. The num- bers are separated by exactly one space. (PYTHON)
- (Find and Correct Code Errors) Identify the error in each of the following statements andexplain how to correct it.a) cout << "Value of x <= y is: " << x <= y;b) The following statement should print the integer value of 'c'.cout << 'c';c) cout << ""A string in quotes"";1. Write an algorithm and flowchart to add the following sequences: a. 1,3,5,7,9. . . N (series of odd numbers) b. 2, 4, 6, 8, 10 . . . N(series of even numbers) 2. Write an algorithm and flowchart that will ask the user to enter a number (n) and display the numbers from 1 to n.Q5: (Count positive and negative numbers and compute the average of numbers) Write a program of C++ that reads an unspecified number of integers, determines how many positive and negative values have been read, and computes the total and average of the input values (not counting zeros). Your program ends with the input 0. Display the average as a floating-point number. Here is a sample run: Enter an integer, the input ends if it is 0: 1 2 -1 3 0 The number of positives is 3 The number of negatives is 1 The total is 5.0 The average is 1.25

