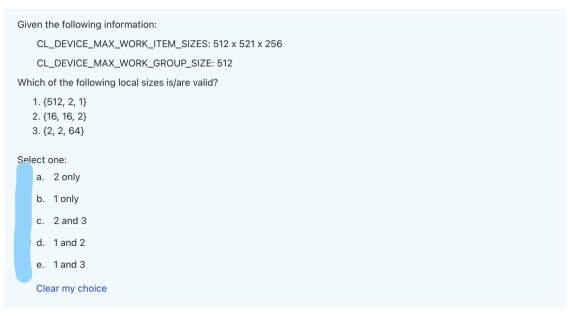
Given the following information: CL_DEVICE_MAX_WORK_ITEM_SIZES: CL_DEVICE_MAX_WORK_GROUP_SIZE: Which of the following local sizes is/are valid? 1. (512, 2, 1) 2. (16, 16, 2) 3. (2,2, 64) Select one: a. 2 only b. 1 only c. 2 and 3 d. 1 and 2 e. 1 and 3 Clear my choice 512 x 521 x 256 512
Q: how cloud-based network services and applications operate and are hosted
A: Cloud-based network provisions and applications are operated and hosted via the cloud, a collection…
Q: Compared to a clustering index, what distinguishes a secondary index?
A: Differences between a clustering index and a secondary index. We will provide an explanation of each…
Q: Which of the following is a function that cannot be used in the kernel? Select one: a. vload4 b.…
A: According to bartleby guidelines we are supposed to answer only 3 subparts in a question so I have…
Q: a) Assume that a direct mapped cache memory stores 1024 blocks and 64 bytes per block. i) What is…
A: Cache memory is a small and fast memory component that stores copies of frequently used data from…
Q: First-order or predicate logic. Show that the sum relation, {(m,n,p)|p=m+n}, is not definable on…
A: First-order logicFirst-order logic is a group of formal systems used in mathematics, philosophy,…
Q: ROM and RAM are the two primary components of a computer's main memory.
A: What is ROM and RAM: ROM stands for Read-Only Memory, a non-volatile memory used to store permanent…
Q: need to find such as number within the given range that it should be a prime number and also a…
A: This code finds numbers within a given range that are both prime and happy numbers.The isHappy…
Q: Content creators have formed communities. What's Google's network like? What drives content…
A: Google's network is a vast and complex infrastructure that supports its wide array of services and…
Q: Please clarify the authentication process's aims. Compare the pros and cons of different…
A: Authentication is a critical process in ensuring the security and identity verification of users…
Q: If a data breach were to occur, what would be the most probable outcomes from a cybersecurity…
A: What is data breaches: A data breach refers to an unauthorized access, disclosure, or loss of…
Q: Which of the following statements about events is/are FALSE? 1. A callback function can be triggered…
A: 1.1. This statement is TRUE. A callback function can indeed be triggered when an event completes,…
Q: How would you discern an error message displayed on your computer? Where do you search for answers,…
A: When encountering an error message on your computer, you can follow these steps to discern the…
Q: Which of the following statements is/are FALSE? 1. Work-groups run on processing elements 2. A…
A: The answers are given in the below step
Q: What are some of the most likely signs that a laptop's operating system has been changed, possibly…
A: What is laptop's operating system:A laptop's operating system (OS) is the software that manages and…
Q: Given the following snippet of kernel code: char8 m = (char8)("w", "'t', 'k', '1', '0', 'zº', 'p',…
A: 1.Correct option: a). ('k', 'p', 'l', 'z')Reason: The code initializes a char8 vector m with the…
Q: Explain Hobb's method and other centering algorithms in the context of the referenced phenomenon.
A: Centering algorithms engage in recreation a very important role inside computer graphics plus…
Q: Write a Python program to sort a list of tuples using Lambda. Original list of tuples:…
A: According to the information given:-We have to follow the instruction in order to get desired…
Q: Hello! I could really use help for these two problems. Program 1 Show how well dressed you and…
A: Algorithm of the Date Night Styling:Create a new instance of the Scanner class: Scanner sc = new…
Q: Could you please provide more context or specify the academic field in which you would like the…
A: Certainly! For the context of discussing whether embedded computers store their programs in flash…
Q: Consider the historical evolution of the internet and its present-day technological foundations.
A: The internet has undergone a remarkable historical evolution, transforming the way we communicate,…
Q: Run experiments to determine empirically the probability that DepthFirstDirectedPaths finds a path…
A: The topic at hand focuses on conducting empirical experiments to determine the probability of…
Q: First-time computer startup produces no sound or light. Is it software or hardware? why? What…
A: A computer not showing any signs of life upon startup - no lights, no sound - suggests that it's…
Q: What are the next three actions you can take if debugging has been attempted and you are still…
A: If you’re, however, experiencing problems even after an initial correcting attempt, it could be…
Q: To explain, API means "application programming interface." Interface for applications programming. I…
A: An API Application Programming Interface is a set of rules and protocols that allows software…
Q: Can you explain how the structure of the software will be evaluated?
A: Software structure evaluation involves assessing a software system's organization, design, and…
Q: There are numerous potential uses for compiler phases. Can we describe each and every step?
A: Understanding Compiler PhasesCompilers are complex software tools used to translate high-level…
Q: From a cybersecurity perspective, what are the most probable repercussions of a data breach? Explain
A: What is Cybersecurity: Cybersecurity refers to the practice of protecting computer systems,…
Q: RAM definition? First two categories. Flash memory for embedded computer programmes? Explain
A: RAM stands for Random Access Memory. It is a type of computer memory that is used for temporary…
Q: does software project management serve in the creation of computer programmes?
A: Software project management refers to the discipline and set of practices that focus on planning,…
Q: Compose a Python program to find the convergence of two given clusters utilizing Lambda. Unique…
A: Start by defining the two given clusters, cluster1 and cluster2.Initialize an empty list called…
Q: What do you mean by the term "final result" when referring to the objectives of the authentication…
A: What is authentication: Authentication is the process of verifying the identity of a user or entity…
Q: Multifactor authentication: what happens? Does this device prevent password theft?
A: What is authentication:Authentication is the process of verifying the identity of a user or entity…
Q: It is essential to understand what multicore architecture is and how it operates in practise.
A: A single integrated circuit in a computer processor that has many processing units, or cores, that…
Q: archiving and presenting information. Provide an example of how each BI tool would be integrated…
A: Integration of business intelligence (BI) tools with a distributed data warehouse for archiving and…
Q: How can the advantages and disadvantages of the numerous authentication techniques, particularly in…
A: Authentication in computer security is a process that ensures and confirms a user's Identity. There…
Q: When you discuss the purposes of authentication, I am unsure of what you mean. Determine what each…
A: Authentication, in the context of computer systems, is the process of authorizing the identity of a…
Q: I hardly know multi-factor authentication. How does it protect passwords?
A: Multi-factor Multiple-factor verification (MFA) is a security assessment that uses a hybrid line of…
Q: Does the company's procedure use Internet technology? Use a case to calculate the risk.
A: What is Internet technology:Internet technology refers to the set of protocols, tools, and systems…
Q: How does an embedded system differ from an embedded control system and an instruction set processor?…
A: Processor is the core of an embedded framework. The essential unit takes information sources and…
Q: Is memory reserved for a specific number of declaration statements or just a subset of them?
A: Memory allocation is a crucial aspect of programming, as it determines how much space is reserved…
Q: Data mining's influence on privacy and safety?
A: Introduction:- Data mining refers to the process of extracting and analyzing large sets of data to…
Q: Is memory reserved for a
A: Memory allocation is a crucial aspect of programming, as it determines how much space is reserved…
Q: Would you check out an identical website? Why?
A: In the digital information age, websites play an important role in shaping our online experience.…
Q: ame consists of a 7x7 board of which 10 of those 49 slots are “stars”. The objective of the game is…
A: The goal is to create a solver function for the Tentaizu puzzle, where the input is a 7x7 list…
Q: مهمه Ø Ø Å™ 8 a FIGURE 4. Figure of Question 12 Q12 Which of the following is the language…
A: DFA: It refers to the deterministic finite automate if machine reads as input and string and one…
Q: I would like to brainstorm how to create a C++ program that could count calories consumed in a day.…
A: Developing a health-conscious application that can help users keep track of their daily calorie…
Q: Given the following snippet of code: cl::NDRange offset(4); cl::NDRange globalSize(128); cl::NDRange…
A: For the first question correct answer is c. 32 work-groups will be created.For the second question…
Q: I hardly know multi-factor authentication. How does it protect passwords?
A: In order to safeguard accounts and systems, multi-factor authentication (MFA) goes beyond the usual…
Q: How precise is this, then? The Text property of a newly created form is initialised with the form's…
A: What is text property: The "Text" property refers to a property of a graphical user interface (GUI)…
Q: Do programmers have a moral obligation to deliver easily updatable code, even if the client…
A: Ethical considerations surrounding this matter and discuss the potential obligations of programmers.
Step by step
Solved in 3 steps

- 6 Cell Phone PackagesCell Solutions, a cell phone provider, sells the following packages:300 minutes per month: $45.00 per month800 minutes per month: $65.00 per month1500 minutes per month: $99.00 per monthThe provider sells the following phones (a 6 percent sales tax applies to the sale of a phone):Model 100: $29.95Model 110: $49.95Model 200: $99.95Customers may also select the following options:Voice mail: $5.00 per monthText messaging: $10.00 per monthWrite an application that displays a menu system. The menu system should allow the userto select one package, one phone, and any of the options desired. As the user selects itemsfrom the menu, the application should show the prices of the items selected.Netflix Streaming. Which of the following (one or more) statements are true about Netflix streaming (check all that are true) or video streaming services in general. pLEASE PICK ONE Group of answer choices A. Once a video starts streaming from a given Netflix server to a given client player, that server will be the only server assigned to transmit that video to that client throughout the viewing session for this video. B. Once a video starts streaming from a Netflix server to a client player, the video quality remains constant throughout video playback. C. In many video streaming services, the client requests chunks of video from a server using the HTTP protocol.Mr.Fayyaz is a milkman who is supplying milk to many customer. Each customer has its name CNIC Home_Address and phone number. Mr Fayyaz wants to keep the track of daily milk supply quantity and price. He also wants to monthly record of each customer. Customer could also login and use the milkman application to view its bill. Mr Fayyaz could see the total sales of each customer. The milk has two types buffalo milk and cow milk. Mr Fayyaz also want to maintain the record of workers in the application. The final project could have the functionality of Searching of a customer by its name the project would be able display the details e.g. Customer CNIC and Address etc. Searching a customer bill detail the project would be able to display its monthly details of milk, quantity, and total bill. Searching a milk detail date wise, it means when milkman search for milk detail by giving the month, the project should be able to display the details of milk and its quantity sold in a month. The…
- 6. Which of the following is false concerning keystores and keys? Select one: a. A keystore can contain multiple keys b. Each key in a keystore should have its own password c. A keystore can be used to store a Google Play App Signing upload key d. It's possible, when signing manually, to generate multiple signed APKs simultaneously for product flavors but they must all use the same key e. If you think none of the above are false concerning keystores and keys, select this optionDue to Ramadan, your nearby community wants to launch an “Online Grocery Store” so that, people can purchase groceries from home and able to maintain social distance. This precaution will allow reducing the movement of people in Ramadan and minimize the spread of disease COVID-19. The XYZ store will offer various products. The user will be shown a list of products, which can be selected or deselected from the provided list. The user will need to get registered to buy Products. At the end of shopping, the customer can double-check all the Products added into his Cart and verify the total amount before payment. The Store Administrator will manage Products and assign orders to Delivery Boys.Draw an Object Model (Class Diagram) for the given scenario showing main objects, their attributes, functions and relationships.The tasks you have to do are: Extract the main objects (entities) of above system. Find the necessary attributes and functions that need to be associated with each object.…Medical Unlimited Medical Unlimited (the brainchild of a group of young philanthropic medical professionals) is interested in setting up a mobile medical unit that provides free medical services for students. The mobile medical unit will require a patient record and scheduling application that will be used by the medical staff (doctors/nurses) and receptionists working there. The receptionists will use the system to capture new patient information when firsttime patients visit the doctor. Receptionists will also be responsible for scheduling all appointments. Nurses on the other hand will use the s ystem to keep track of the results of each visit including diagnosis, medications, prescription and treatment. Multiple medications may be prescribed during each visit. The nurses can also access the information to print out a history of patient visits. Th e doctors will primarily use the system to view patient history. The doctors may enter some patient treatment information and…
- Medical Unlimited Medical Unlimited (the brainchild of a group of young philanthropic medical professionals) is interested in setting up a mobile medical unit that provides free medical services for students. The mobile medical unit will require a patient record and scheduling application that will be used by the medical staff (doctors/nurses) and receptionists working there. The receptionists will use the system to capture new patient information when firsttime patients visit the doctor. Receptionists will also be responsible for scheduling all appointments. Nurses on the other hand will use the s ystem to keep track of the results of each visit including diagnosis, medications, prescription and treatment. Multiple medications may be prescribed during each visit. The nurses can also access the information to print out a history of patient visits. Th e doctors will primarily use the system to view patient history. The doctors may enter some patient treatment information and…Netflix Streaming. Which of the following (one or more) statements are true about Netflix streaming (check all that are true) or video streaming services in general. Group of answer choices A. Once a video starts streaming from a given Netflix server to a given client player, that server will be the only server assigned to transmit that video to that client throughout the viewing session for this video. B. Once a video starts streaming from a Netflix server to a client player, the video quality remains constant throughout video playback. C. In many video streaming services, the client requests chunks of video from a server using the HTTP protocol.Excel Question: (Excel 365) Can one please confirm if there's only a pop-up dialog box/warning when moving data to another location with existing data? I'm getting this warning for when moving data, but when it comes to copying data and pasting it to another location with existing data, there's no pop-up dialog box/warning. My settings in Excel already enable the "Alert before overwriting cells." I copy data by using just the Ctrl key, where pointer changes from a multi-headed arrow to a small + sign, and dragging it to the designated location.
- Question 14 papa C# please screen shot please Full explain this question very fast solution sent meThe university, ask the student to enter his/ her e-mail address then check if it valid or not the address must meet the following requirements: end by @ksu.edu.sa, it must contain exactly 9 digits. If the address is valid ask them to type a valid password for the campus computer system, the password must meet the following requirements: The password must be at least seven characters long. It must contain at least one uppercase letter. It must contain at least one lowercase letter. It must contain at least one numeric digit. When a student sets up his or her password, the password must be validated to ensure it meets these requirements. You have been asked to write the code that performs this validation for email and password. You decide to write a function named “valid_ address” and “valid_password” that accepts the e-mail address and password as an argument respectively and returns either true or false, to indicate whether they are valid or not. If all are valid save it…The university, ask the student to enter his/ her e-mail address then check if it valid or not the address must meet the following requirements: end by @ksu.edu.sa, it must contain exactly 9 digits. If the address is valid ask them to type a valid password for the campus computer system, the password must meet the following requirements: The password must be at least seven characters long. It must contain at least one uppercase letter. It must contain at least one lowercase letter. It must contain at least one numeric digit. When a student sets up his or her password, the password must be validated to ensure it meets these requirements. You have been asked to write the code that performs this validation for email and password. You decide to write a function named “valid_ address” and “valid_password” that accepts the e-mail address and password as an argument respectively and returns either true or false, to indicate whether they are valid or not. If all are valid save it…





