epresents (does business with) many insurance companies (insurers). We will need to track each insurer with an agency assigned alphanumeric o chine number, and email address. There may be insurers in the database that have no quotes but an insurer may give an unlimited number of o t requests information about a policy a quotation is created. A quotation has a file number, the client number, date of the quotation, insurance c licy number of the client accepts the quote and purchases the policy. A quotation may be for only one client and insurer. A client may have an un nay be written by 1 to 5 agents. If the policy is finally purchased commissions will be split among the agents as they see fit, as long as it totals 100 ation time. ess rules above, complete the table by choosing the correct connectivity for each of the relationships: onship Connectivity Entity sts Quote 1:M Ouote
epresents (does business with) many insurance companies (insurers). We will need to track each insurer with an agency assigned alphanumeric o chine number, and email address. There may be insurers in the database that have no quotes but an insurer may give an unlimited number of o t requests information about a policy a quotation is created. A quotation has a file number, the client number, date of the quotation, insurance c licy number of the client accepts the quote and purchases the policy. A quotation may be for only one client and insurer. A client may have an un nay be written by 1 to 5 agents. If the policy is finally purchased commissions will be split among the agents as they see fit, as long as it totals 100 ation time. ess rules above, complete the table by choosing the correct connectivity for each of the relationships: onship Connectivity Entity sts Quote 1:M Ouote
Computer Networking: A Top-Down Approach (7th Edition)
7th Edition
ISBN:9780133594140
Author:James Kurose, Keith Ross
Publisher:James Kurose, Keith Ross
Chapter1: Computer Networks And The Internet
Section: Chapter Questions
Problem R1RQ: What is the difference between a host and an end system? List several different types of end...
Related questions
Question
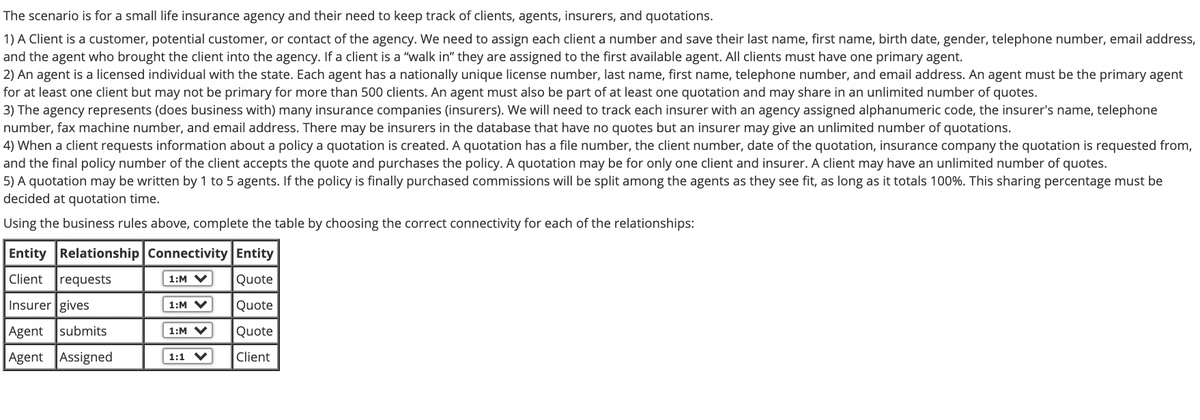
Transcribed Image Text:The scenario is for a small life insurance agency and their need to keep track of clients, agents, insurers, and quotations.
1) A Client is a customer, potential customer, or contact of the agency. We need to assign each client a number and save their last name, first name, birth date, gender, telephone number, email address,
and the agent who brought the client into the agency. If a client is a "walk in" they are assigned to the first available agent. All clients must have one primary agent.
2) An agent is a licensed individual with the state. Each agent has a nationally unique license number, last name, first name, telephone number, and email address. An agent must be the primary agent
for at least one client but may not be primary for more than 500 clients. An agent must also be part of at least one quotation and may share in an unlimited number of quotes.
3) The agency represents (does business with) many insurance companies (insurers). We will need to track each insurer with an agency assigned alphanumeric code, the insurer's name, telephone
number, fax machine number, and email address. There may be insurers in the database that have no quotes but an insurer may give an unlimited number of quotations.
4) When a client requests information about a policy a quotation is created. A quotation has a file number, the client number, date of the quotation, insurance company the quotation is requested from,
and the final policy number of the client accepts the quote and purchases the policy. A quotation may be for only one client and insurer. A client may have an unlimited number of quotes.
5) A quotation may be written by 1 to 5 agents. If the policy is finally purchased commissions will be split among the agents as they see fit, as long as it totals 100%. This sharing percentage must be
decided at quotation time.
Using the business rules above, complete the table by choosing the correct connectivity for each of the relationships:
Entity Relationship Connectivity Entity
Client
requests
1:M V
Quote
Insurer gives
1:M V
Quote
Agent
submits
1:M V
Quote
Agent Assigned
Client
1:1 V
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Recommended textbooks for you

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Computer Networking: A Top-Down Approach (7th Edi…
Computer Engineering
ISBN:
9780133594140
Author:
James Kurose, Keith Ross
Publisher:
PEARSON

Computer Organization and Design MIPS Edition, Fi…
Computer Engineering
ISBN:
9780124077263
Author:
David A. Patterson, John L. Hennessy
Publisher:
Elsevier Science

Network+ Guide to Networks (MindTap Course List)
Computer Engineering
ISBN:
9781337569330
Author:
Jill West, Tamara Dean, Jean Andrews
Publisher:
Cengage Learning

Concepts of Database Management
Computer Engineering
ISBN:
9781337093422
Author:
Joy L. Starks, Philip J. Pratt, Mary Z. Last
Publisher:
Cengage Learning

Prelude to Programming
Computer Engineering
ISBN:
9780133750423
Author:
VENIT, Stewart
Publisher:
Pearson Education

Sc Business Data Communications and Networking, T…
Computer Engineering
ISBN:
9781119368830
Author:
FITZGERALD
Publisher:
WILEY