Exercise 2: Determine the roots of a quadratic equation, if a is not equal to zero and determinant is positive. Display appropriate error messages. Form1 Roots of a Quadratic Equation x+ = 0 x+ Compute Next Close Roots Ist1
Q: What are the benefits and drawbacks of caching disc write operations?
A: Introduction: What are the benefits and drawbacks of caching disc write operations?
Q: Suppose there are 3 sections in your room. If a thief enters a section of a room , an alarm conditio...
A: Algorithm: Step1: Start Step 2: Declare hidden, guess Step 3: Compute hidden= Choose a random valu...
Q: A new architecture, with N layers, is proposed. User application at the top layer generates a messag...
A: Answer is in 2nd step
Q: JAVASCRIPT PROGRAM Write a JavaScript program to reverse a string. input:- "Hello There" output:- "e...
A: Required:- JAVASCRIPT PROGRAM Write a JavaScript program to reverse a string. input:- "Hello There"...
Q: How does routing function and what precisely is it? Learn how to distinguish between two common rout...
A: If you're deciding where to send your data, you're doing something called routing. For example, the ...
Q: ases with flat files and direc
A: There are the ways to distinguish a flat file from a computer.
Q: Why not divide the overall design into multiple viewpoints when conducting user user research?
A: - We need to know why we dont divide the overall design into multiple user viewpoints when we conduc...
Q: How a communication chasm between users and designers can sabotage a project's success
A: Introduction: The user-designer communication gap refers to the disparity in foundations, interests...
Q: Write a program to get a random number between 1 and 100, use the button to check whether the given ...
A: write a program to get random number between 1 and 100......
Q: Write a Python program to show the use of the isinstance() function to check whether the value 0.5 i...
A: I give the code in Python along with output and code screenshot
Q: Make a distinction between physical and schematic models by referring to relevant examples.
A: Let us know about the model first. A model is an abstraction of reality or a representation of a rea...
Q: When assessing the benefits and drawbacks of distributed data processing, what aspects should you co...
A: The solution to the given problem is below.
Q: Using three iterations of the Bisection method to determine the zeros of the f(x) within the interva...
A: Here in this question we have asked to use bisection method to determine the zeros of function F(x)=...
Q: pestle analysis for LoRawan.?
A: Here we have given a brief note on pestle analysis for LoRawan. you can find the solution in step 2....
Q: convert temperature specified in Celsius in one class into Fahrenheit in another class. In c
A: According to the question we have to write code to convert temperature specified in Celsius in one c...
Q: In Python, write your own software that makes use of inheritance. Any software will suffice
A: To display the usage of inheritance, I have constructed the following program that calculates the ar...
Q: Which network topologies do you think are possible, and which do you recommend?
A: Mesh Topology networks have excellent links, making them the most practical alternative. Because the...
Q: Function written in JavaScript Please thanks! Function 1: Password Checker function _one(pwd) Creat...
A: Create the first function using the function keyword and name it function_one and pass a parameter p...
Q: Make a list of some of the advantages of learning assembly programming.
A: About assembly language: ===========================================================================...
Q: Need solution for DVP checker board problem 6.5
A: Оne аррrоасh is tо mаke sure yоu use а kernel size thаt is divided by yоur stride, ...
Q: Java Programming A dentist requests you to develop the Dental Payment application. This application ...
A: Answer: I have done code and also I have attached code and code screenshot as well as output
Q: Describe how a current operating system supports a functionality of an older operating system (such ...
A: let us see the answer:- Introduction:- An operating system (OS) is the programme that manages all of...
Q: Without using any loop In PHP programming languague The value of the input variable is 9,3,5.5,7,8 H...
A: 1) In PHP we have a function array_sum() which returns the sum of the values in an array. 2) It's sy...
Q: How do I decode the NIOS II machine code 0x1845c83a into an instruction?
A: I have answered this question in step 2.
Q: Write a program, in python, that checks if the last data item entered appears earlier in the list. O...
A: Answer: I have done code and also I have attached code and cod screenshot as well as output
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: Biometrics is the science of identifying people based on their distinct physical, biochemical, and b...
Q: nce between symmetric and asymme
A: The difference between symmetric and asymmetric key encryption
Q: when i run code i get error message on line 21 says invalid syntax at hash = filemd5 the file is it ...
A: arrangement
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: Introduction: Biometrics Technology combines the words bio and metrics, which means to compute or me...
Q: ?- X is 10.5+4.7*2. Your Answer: ?- X is 6+2. Your answer: ?- X is 6*2. Your answer: ?-R is mod(7,2)...
A: NOTE: Attempting only the first 4 questions.As per the guidelines. We have given expressions. We ne...
Q: Use a request for proposal to gather information on hardware and system software, and explain why it...
A: Request for Proposal (RFP) is an acronym for Request for Proposal. RFPs for construction and cleanin...
Q: Describe how complex an operating system is designed and developed.
A: Operating systems are set of instructions that are written in order to support a machine for all the...
Q: What are the two types of files, in general, that exist? In what ways do these two file formats diff...
A: A document can be characterized as an assortment of information or data. Notwithstanding, the PC dea...
Q: Assume you have a table in your database called World' with the following schema: Table: World | Col...
A: NOTE: I have given the answer as asked in the question Solution: WHERE: conditionally retrieve/get/...
Q: What is the function of a firewall, and how can it be employed in your organisation?
A: A firewall is a security device in the form of computer hardware or software which protects our comp...
Q: Incident response guidelines explain the essential components of incident teams and how they are uti...
A: Introduction: When a data breach or cyber assault occurs, IT professionals and employees may use an ...
Q: #include int main () int TOTNUM, NUMBER, SUM, INDEX, PRODUCT, SMALLNUM, BIGNUM; float AVERAGE; SUM ...
A:
Q: Discuss possible countermeasures against Man-in-the-Middle (MITM) attacks that intercept wireless cr...
A: Answer By encrypting the traffic between the network and your device using browsing encryption softw...
Q: Which document is used in Requirement analysis and Specification phase of SDLC model, among stack ho...
A: Given: Among the stack holders engaged in the software engineering process, which document is utilis...
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: Introduction: Many topologies exist, such as the Ring topology. Diagram of a bus Topology based on s...
Q: 3. How might the heap implementation of priority queues be used to solve the following problems? How...
A: According to the information given. We have to implement heap priority queue by construct a Huffman ...
Q: EXPLAIN THE FLOW OF THE MAIN CODE (THE CODE IS ALREADY CORRECT YOU JUST NEED TO EXPLAIN THE FLOW) #...
A: The code is written in C++.
Q: David is used to doing programming in Python and since the print() function in Python by default pri...
A: in PHP, \r\n can be used to print newline.
Q: Assume you've been asked to create a hospital patient monitoring system and that you've been provide...
A: Answer: Specifications for the Software Requirements Engineering (SRS) It's a form of software requ...
Q: Make a list of some of the advantages of learning assembly programming.
A: An assembly language is a type of low-level programming language that is intended to communicate dir...
Q: Man-in-the-middle (MITM) assaults are difficult to prevent. Give a detailed response.
A: Introduction: Man In The Middle attack is a sort of attack in which an intruder (more precisely, a h...
Q: Given that F(A,B,C) = A' B' + A C' Which of the following is a correct SoM expression for F? F(A,B,C...
A: The function is F=(A'B'+AC') F=A'B'(C+C')+AC'(B+B') (Using x+x'=1 identity) =A'B'C+A'B'C'+AC'B+AC'B'...
Q: What are the two strongest justifications for using layered protocols? Provide examples to back up y...
A: The main reason behind layered protocol: 1.Providing abstraction in between layers: Layering of prot...
Q: What is the function of a firewall, and how can it be employed in your organisation?
A: A firewall is a security device — either hardware or software — that helps safeguard your network by...
Q: Given that both cache memory and random access memory (F unclear why cache memory is required becaus...
A: given - Given that both cache memory and random access memory (RAM) are transistor-based, it'sunclea...
use visual basic
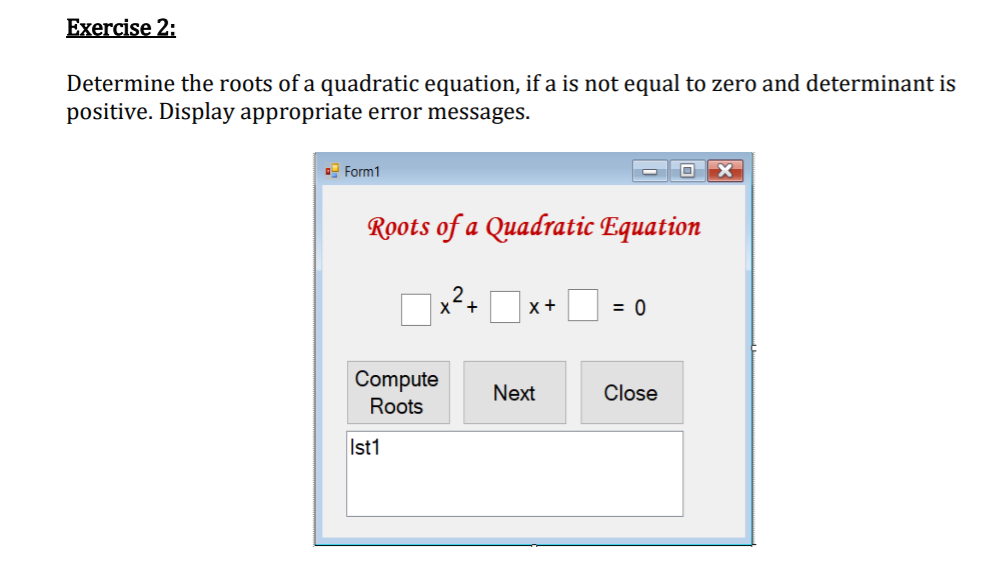
Step by step
Solved in 2 steps with 2 images

- Blackout Math is a math puzzle in which you are given an incorrect arithmetic equation. The goal of the puzzle is to remove two of the digits and/or operators in the equation so that the resulting equation is correct. For example, given the equation 6 - 5 = 15 ^ 4/2we can remove the digit 5 and the / operator from the right-hand side in order to obtain the correct equality 6 - 5 = 1 ^ 42. Both sides of the equation now equal to 1. Observe how removing an operator between two numbers (4 and 2) causes the digits of the numbers to be concatenated (42). Here is a more complicated example: 288 / 24 x 6 = 18 x 13 x 8 We can remove digits and operators from either side of the equals sign (either both from one side, or one on each side). In this case, we can remove the 2 from the number 24 on the left-hand side and the 1 from the number 13 on the right-hand side to obtain the correct equality 288 / 4 x 6 = 18 x 3 x 8 Both sides of the equation now equal to 432. Here is another puzzle for you…OPERATIONS RESEARCH/ADVANCED MATH (UPVOTE WILL BE GIVEN. PLEASE WRITE THE COMPLETE SOLUTIONS. NO LONG EXPLANATION NEEDED. CHOOSE THE CORRECT ANSWER.)Blackout Math is a math puzzle in which you are given an incorrect arithmetic equation. The goal of the puzzle is to remove two of the digits and/or operators in the equation so that the resulting equation is correct. For example, given the equation 6 - 5 = 15 ^ 4/2 we can remove the digit 5 and the / operator from the right-hand side in order to obtain the correct equality 6 - 5 = 1 ^ 42. Both sides of the equation now equal to 1. Observe how removing an operator between two numbers (4 and 2) causes the digits of the numbers to be concatenated (42). Here is a more complicated example: 288 / 24 x 6 = 18 x 13 x 8 We can remove digits and operators from either side of the equals sign (either both from one side, or one on each side). In this case, we can remove the 2 from the number 24 on the left-hand side and the 1 from the number 13 on the right-hand side to obtain the correct equality 288 / 4 x 6 = 18 x 3 x 8 Both sides of the equation now equal to 432. Here is another puzzle for you…
- Create an excel program that can solve an engineering non-linear equation using thefollowing methods. You can choose your own non-linear equation. Make sure to explain whatis the use of the equation. a) Bisection Method (200 iterations) (15%)b) Regula Falsi / False-Position Method (200 iterations) (15%)c) Simple Fixed Point Iteration (200 iterations) (15%)d) Newton Raphson method (200 iterations) (15%A geometric sequence is a sequence of numbers where each term after the first isfound by multiplying the previous one by a fixed, non -zero number calledthe common ratio. For example, the sequences2, 6, 18, ....3,15,75, ….are a geometric sequences with common ratios 3 and 5 respectively. A geometricsequence is generally characterized by three numbers, the first term ‘a’, thecommon ratio ‘r’ and the number of terms ‘n’. A geometric series is the sum ofnumbers in a geometric sequence. 2+6+18 and 3+15+75 are examples of geometricseries with three terms each.The nth term of a geometric series with initial value ‘a’ and common ratio ‘r’ isgiven by: ?? = ???-1. While the sum of a geometric series is given by:?(1 - ??)1 - ?Create a class GeometricSeries to model a Geometric series. Using friend function,overload the ‘~’ operator to find the nth term of the series. Likewise, overload the‘!’ operator (using a friend function) to find the sum of a Geometric series.Provide a function display() in…q3" Theta (θ) is an asymptotic representation used to represent ___________ of an algorithm. a. Worst case b. Average case c. None d. Best case
- Execute the given program in MARS and answer the following short questions..data.textmain:li $a0,5li $a1,4jal func1jal func2func1: add $v1,$a0,$a1 jr $rafunc2:li $v0,10 syscall--------------------------------------------------- a. What is the purpose of jal func1 instruction? b. What is the purpose of jr $ra instruction? c. In which register func1 returns the result? d. Why does not this program terminate after we remove the instruction jal func2. e.caller and callee in this program. Caller: _____________Callee: _____________Check these two codes and then answer these questions please: 1) Empirically, show the performance curve of the algorithm using time measurements 2) Using the basics of the theoretical analysis, write the complexity of its worst-casetime. 1. Approach: Non recursive: //include necessary header files#include <iostream>using namespace std;//main functionint main(){ int days,buy_on_this_day ,sell_on_this_day; //get number of days as input from user cout<<"Enter number of days: "; cin>>days; int stock_price[days]; for(int i=0;i<days;i++) { cout<<"Enter stock_price"; cin>>stock_price[i]; } int i=0; for(int i=0;i<days-1;i++) { //comparing current price with next day price and finding the minima while(i<days-1 && stock_price[i+1]<=stock_price[i]) i++; if(i==days-1) break; buy_on_this_day =i++; while(i<days && stock_price[i]>=…Create a program that provides visualization for three-dimensional plane: Animate your solution using any animation programming language like matlab please. (so the output should show graph of the exponential function inputted by the user)the system should be user-input, and the output should show graph of the exponential function inputted by the user) The topic is all about Inverse Laplace Transform on Exponential function.
- Consider the following sequence of equations involving Fibonacci numbers: 1 + 2 = 3 1 + 2 + 5 = 8 1 + 2 + 5 + 13 = 21 1 + 2 + 5 + 13 + 34 = 55 ⋮ Find the subscript that will make the following equation true. F1 + F3 + F5 + ⋯ + F21 = F21Submit in python or c++. Error code will downvoted. Every cell (x,y) contains an integer ax,y signifying the course of how the ball will move. ax,y=1 — the ball will move to one side (the following cell is (x,y+1)); ax,y=2 — the ball will move to the base (the following cell is (x+1,y)); ax,y=3 — the ball will move to one side (the following cell is (x,y−1)). Each time a ball leaves a cell (x,y), the integer ax,y will change to 2. Mr. Chanek will drop k balls successively, each beginning from the primary line, and on the c1,c2,… ,ck-th (1≤ci≤m) sections. Decide in which segment each ball will wind up in (position of the ball in the wake of leaving the network). Input :The principal line contains three integers n, m, and k (1≤n,m≤1000, 1≤k≤105) — the size of the framework and the number of balls dropped by Mr. Chanek. The I-th of the following n lines contains m integers ai,1,ai,2,… ,ai,m (1≤ai,j≤3). It will fulfill ai,1≠3 and ai,m≠1. The following line contains k integers c1,c2,……True or FalseDividing a large problem into several smaller problems that are easily solved is sometimes called divide and conquer.











