Draw the position of the letter "e" as viewed under the Scanner, and the actual position of letter "e" if you were to put it on the stage. Explain why this happens. "e" under Scanner Actual position of "e"
Q: Describe the memory addressing capabilities of the 20-bit address bus. microcontroller?
A: Introduction: The address bus is used to transport the memory location or I/O device address for dat...
Q: Convert the following expression to its Prefix and Postfix equivalents. ((A + B) * C - (D - E) ^ (F ...
A: Introduction: Convert the following expression to its Prefix and Postfix equivalents. ((A + B) * C -...
Q: 1. Under the user location. scenario, all record- and file-locking activities are performed at the e...
A: Choose the correct answer for the given question.
Q: 2. Write a recursive JAVA program to input a natural number N and using recursion print all the natu...
A: Write a recursive JAVA program to input a natural number N and using recursion print all the natural...
Q: write a program that shows the valid moves of chess pieces. Your program will draw a board with 64 s...
A: Write a program that shows the valid moves of chess pieces. Your program will draw a board with 64 ...
Q: ed with the followi a Hexadecimal syster 0 20 06 00 00 7C 4E A' Bytes, the numbe
A:
Q: Let's finish working on our booking system. The last part for our booking system will be to manage...
A: Given :- Let's finish working on our booking system. The last part for our booking system will be t...
Q: necessary to describe VRAM.
A: We are going to understand VRAM in computers. VRAMs stand for Video Random Access Memory. Let's unde...
Q: Create a JavaScript Arrow function that meets the following requirements: Authored using arrow expre...
A: Step 1 : Start Step 2 : Define a function _replaceCharacter() which takes a string as parameter. Ste...
Q: Summarize applications, source code, executable files, tools, installation guides, or user guides th...
A: In this question, we are asked to summarize or explain the different terminology Applications: It is...
Q: 1. Fill in the following table with the correct subproblem solutions for the weighted longest common...
A: I have answered this question in step 2.
Q: What does a Details view entail?
A: Introduction: The "DetailsView" control must be used if the programmer wishes to display the columns...
Q: What is output? public enum TrafficLight {RED, YELLOW, GREEN} TrafficLight myLight; myLight = Traffi...
A: question 1: In the first code enum TrafficLight has three values that are RED , YELLOW GREEN. Since ...
Q: Sony PlayStation Network hack in April 2011. Which Sony controls failed?
A: PlayStation 3 and PlayStation Portable control get failed in April 2011
Q: What is the significance of standard recipes? What is the operation of automated recipe management s...
A: Introduction: Recipe management system: A recipe management system is a piece of software that keeps...
Q: To format a number stored in the variable x using the local standards for displaying numeric values ...
A: to format a number stored in the variable x using the local variable for displaying numeric value
Q: DMA access to main memory is given higher priority than processor access to main memory in almost al...
A: Introduction: Direct memory access (DMA) is a computer system capability. It enables some hardware s...
Q: Java Program 1.Carmens’s Catering provides meals for parties and special events. Write a java progr...
A: As per the given question below is the program and output:
Q: The ImageList control is found in which part of the Toolbox?
A: Introduction: Images may be added to the control both during design and during runtime. Drag an Ima...
Q: Describe briefly your perspective on the technical transition from first-generation to fifth-generat...
A: First Generation 1) This first generation of computers was based on vacuum tube technology used for...
Q: What is the difference between a subsystem and a logical division, and why is it important?
A: Given: What is the distinction between a subsystem and a logical division, and why does it matter?
Q: Assume that all the course syllabus in your working directory are named by a major çode of three alp...
A: Given :- Assume that all the course syllabus in your working directory are named by a majorcode of t...
Q: Explain the challenges of mining knowledge at various levels of abstraction in mining methodology.
A: Data mining: Data mining is a process of extracting knowledge from massive volumes of data. it re...
Q: Problem #3 - Search a string. Write a program which counts the number of a particular character foun...
A: I give the code in C along with output and code screenshot
Q: Creating Artificial Intelligence Systems for Medical Applications Explain the concept of human natur...
A: Artificial intelligence is defined as the ability of computer or robot to perform operation like hum...
Q: For which values of r,s and t is the complete tripartite graph K planar? r.s.t
A: Triparite graph can be defined as the vertices of graph that gets decompose into three disjoint sets...
Q: Which of the following statement is true goto statement is harmful because it increases memory requi...
A: Given:
Q: JS Write a function named sum_between_indices whose parameter is a list/array of decimal numbers. Yo...
A: I give the code in javascript as well as python along with output and code screenshot
Q: python" Write a function named add_value that has a single parameter. This parameter will be a list/...
A: start define a function that takes list as a parameter append 21 in list stop
Q: benchmark program to evaluate the performance of a processor spends 80% of its time on floating-poin...
A: According to the Question below the Solution:
Q: Determine two methods for finishing the identical object, one of which employs a more technologicall...
A: Introduction: Plays are still a tremendous source of entertainment nowadays, but their medieval equi...
Q: Give example of Substring from IndexOf in JAVA.
A: Substring refers to the part of the string as when we call substring function then it prints the pa...
Q: Explain in detail what data security is, as well as the three categories of data ownership and their...
A: The definitions asked are:- Data security The types of data ownership
Q: etwork hack that occurred in April 2011. What type of attack was it? Was the success of the attack d...
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: What is the primary function of a firewall? What are the general rules for employing packet filterin...
A: Introduction: Firewall is nothing but a barrier or layer of security between the traffics of two net...
Q: Digits to word. In the class program Example0903-DigitsToWords.py we can enter a sequence of numbers...
A: Use a try-catch block to validate the input and then while iterating print the respective number
Q: Make any program with control structure...
A: given - Java Program Make any program with control structure... Explain every line...
Q: What are the two most common types of UPSs?
A: Introduction: Usually there are three types of UPSs. Two primary types of UPSs would be:- Online ...
Q: 5. Explain the documents needed for Scope Change Control
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: hy should the DEMS update the catalogue when the database configuration changes? Is it possible for ...
A: Introduction: The System Catalog is where the database information is kept.
Q: All technicians require the appropriate equipment and experience to evaluate and handle troubleshoot...
A: Lets see the solution in the next steps
Q: What is multifactor authentication, and how does it work? What role does it play in password securit...
A: Introduction: Multiple forms of identification may be used to verify a user, such as a password, a s...
Q: rithm from the lecture/textbook): 8 4 16
A: Basically, binary search tree Operation insertion and deletion explained below step by step .
Q: Is it possible to safeguard communications using message secrecy and integrity security? Is it the ...
A: Introduction: Because smart objects frequently communicate data across insecure communication medium...
Q: Exercise 5.5 Widest Fragment in a Sequence Write a program to read a sequence of integer numbers end...
A: I provide same solution in 2 different languages PYTHON and C++
Q: What are some of the similarities between string and lists?
A: Lists can be changed, but Strings cannot. Second, list members can be of many types, whereas a Strin...
Q: Bugs, what precisely are they?
A: Introduction: A bug is an error in a program's source code that leads it to produce unexpected resu...
Q: You have port scanned an Internet-facing web server. The following ports are open. 23, 80, 443, 8080...
A: A TCP or UDP port number that is actively accepting packets is referred to as an open port. To put i...
Q: What is the value saved after executing the following code? .data var1 WORD 1000h var2 WORD 2000h...
A: answer in next step -
Q: What is an Object Repository, and how does it work? In Selenium, how can we make an Object Reposito...
A: Introduction: What is an Object Repository, and how does it work? In Selenium, how can we make an O...
Explain why this happens.
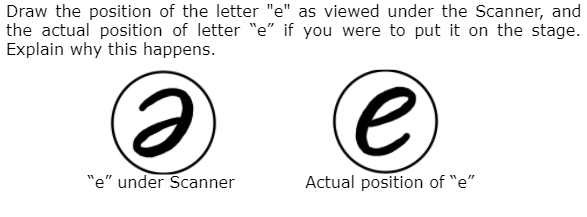
Step by step
Solved in 2 steps

- Later, the student uses the oscillator to create a single pulse with initial speed vo at at the left end of the string, as shown above. The student wants to quantify the observation that the pulse slows down on the right half of the string. The student comes up with the following equation relating the string’s diameter D at a given point on the string to the speed v of the pulse at that point: v=vo(Do/D) (c) Is the equation consistent with the observation that the pulse slows down on the right half of the string? ____Yes ____No (d) Using frame-by-frame analysis of video of the pulse, the student plots the speed v of the pulse as a function of the string diameter D, as shown below. Are the data in the graph consistent with the student’s equation above? ____Yes ____NoWrite a program i C language to make the RGB LED start in the Red color state, then fade to Green, then fade to Blue and finally back to the Red color. Complete the code that is giving in the picture. Remember, the LED should FADE from a color to another. So, make sure that the LED fade.What is the mathematical statement of the following, using the following statements on the image? 1. It is raining and I am not wearing my rubbers. a. P v ~Q b. P ^ Q c. P ^ ~Q
- Java program. Please follow the rule and show screenshot same with the sample output.Change your previous temperature conversion program so that it willconverts the temperatures from 1 to 50 Celsius to Fahrenheit and Kelvin. The outputshould look like this:Celsius Fahrenheit Kelvin1 33.8 274.152 35.6 275.153 37.4 276.154 38.2 277.15This continues up to 50.Based on the sample output in the provided image and given below, With the use of python, write a program that takes the x-y coordinates of a point in the Cartesian plane and displays a message telling either an axis on which the point lies or the quadrant in which it is found. Sample Output: (-1.0, -2.5) is in quadrant III (0.0, 4.8) is on the y axis
- Please use MatLabThe second picture is a supplement to the title of the first picture. You just need to solve the problem in the first picture ThanksWhat is the mathematical statement of the following, using the following statements on the image? 6. "It is raining, still I am neither wearing my rubbers nor carrying my umbrella." *a. P ^ (~Q ^ ~R)b. P v (~Q v ~R) c. P v (~Q ^ ~R)Please using python to implement the following task. Given a RGB color image ‘test.jpg’ noised by salt and pepper noise, first choose a good filter to remove noise on each channel, then based on the gray image of this new RGB color image, use canny edge detection to get edges. Finally show the original image and its edge image.
- Reimplement the digital clock from the preceding exercise, representing the time as the minutes from midnight. This makes the pulse member function very easy, but you have to work harder to recover the hours and minutes. For example, 100 minutes after midnight is 1 hour and 40 minutes.Write a program that moves a circle up, down, left, or right using the arrow keys as shown in Figure (b). Check the boundary to prevent the ball from moving out of sight completely.Write a brief overview about the problem inside the title "Employing Audio-Reading Material in Improving Reading Fluency"

