F49.
Chapter1: Getting Started With Excel
Section: Chapter Questions
Problem 17RA
Related questions
Question
F49.
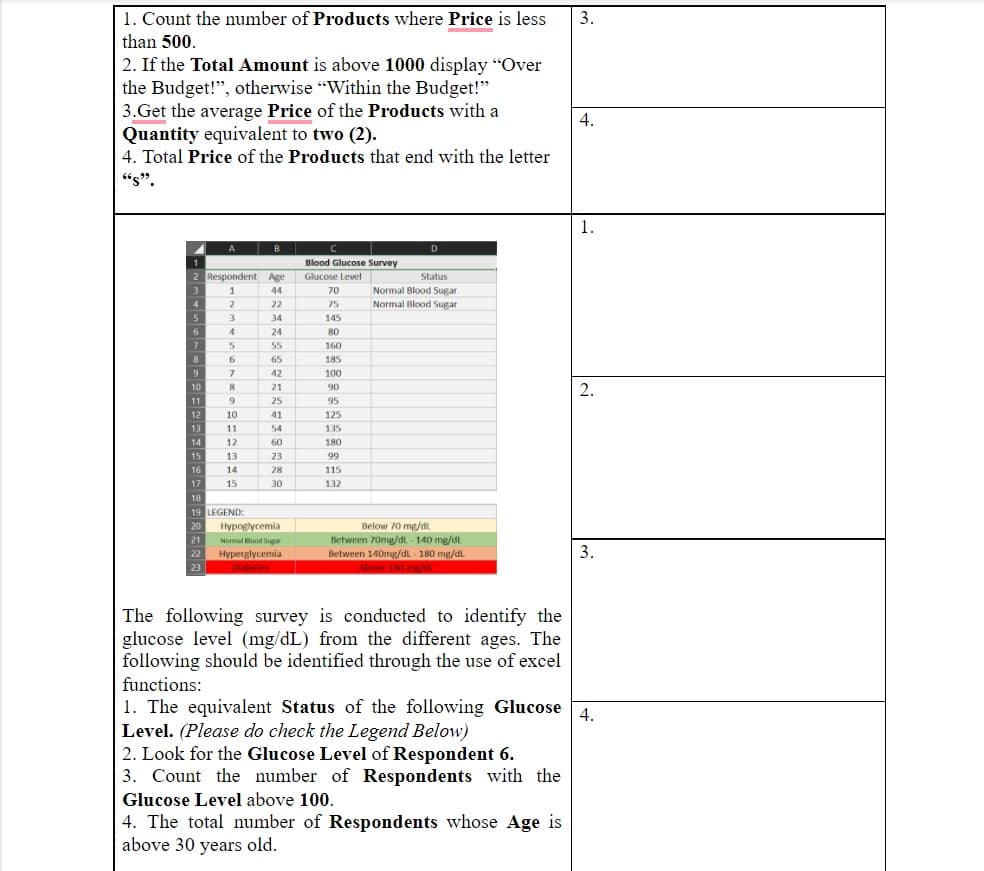
Transcribed Image Text:1. Count the number of Products where Price is less
than 500.
2. If the Total Amount is above 1000 display "Over
the Budget!", otherwise "Within the Budget!"
3.Get the average Price of the Products with a
Quantity equivalent to two (2).
4. Total Price of the Products that end with the letter
665.⁹⁹.
2 Respondent
3
1
4
2
5
3
6
4
7
5
8
6
7
8
9
9
10
11
12
13
14
A
15
16
17
10
11
12
13
14
15
B
LEGEND:
Age
44
22
34
24
55
65
42
21
25
41
54
60
23
28
30
18
19
20 Hypoglycemia
Normal Blood Sug
21
22
Hyperglycemia
Diabetes
23
C
Blood Glucose Survey
Glucose Level
70
75
145
80
160
185
100
90
95
125
135
180
99
115
132
D
Status
Normal Blood Sugar
Normal Blood Sugar
Below 70 mg/dL
Between 70mg/dt-140 mg/dl
Between 140mg/dL-180 mg/dL
Above 180 mg/dl.
The following survey is conducted to identify the
glucose level (mg/dL) from the different ages. The
following should be identified through the use of excel
functions:
3.
2. Look for the Glucose Level of Respondent 6.
3. Count the number of Respondents with the
Glucose Level above 100.
4. The total number of Respondents whose Age is
above 30 years old.
4.
1.
2.
3.
1. The equivalent Status of the following Glucose 4.
Level. (Please do check the Legend Below)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning