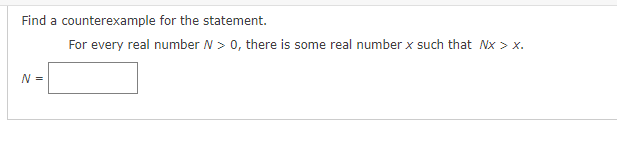
Find a counterexample for the statement. N= For every real number N > 0, there is some real number x such that Nx > X.
Q: work using slotted control protocol, of 8000 bits. The is 10 KBps. The av missions at each
A:
Q: One of the most notable advantages of multiprocessor systems is the added flexibility they give.…
A: Two-dimensional materials offer flexibility, allowing them to be more readily integrated into…
Q: this code gives me an error Traceback (most recent call last): File "main.py", line 2, in from…
A: Advantages of python:- 1)Interpreted Language2)Easy to Read and Learn 3)Easy to Write4)Portability
Q: The intent of the DSL is to specify commands which forward to another object, but which always…
A: The DSL's goal is to provide instructions that forward to another object but always return the…
Q: In a paper mill, what 6 steps provide the final product?
A: Converting the chips into pulp, washing and bleaching, refining, whipping, sizing, dyeing the fibers…
Q: Using Assembly Programming Language x86 .asm 32-bit Create a program that generates 3 random…
A: Theory Explanation: This program can be written in Assembly Programming Language x86 .asm 32-bit.…
Q: Is it the hardware or the software if you don't hear a disk spin and no lights come on when you turn…
A: It's hardware or software, if you don't spin and no light come on when you turn on your computer…
Q: Question 5 Assume a class named Seat. True or False? A default constructor definition has this form:…
A: A default constructor is one that either has no parameters or, if it does, contains default values…
Q: he majority of a company's operations are likely to be handled by servers on a flat network, so the…
A: Demilitarized zones (DMZs), which provide network separation, protect the security of internal…
Q: You have to implement a program that creates three buttons to display the digits of a password a…
A: Solution: Programming Language - Java AWT Program code- (Note: All necessary comments are…
Q: an OS, and each of them uses two R units. For deadlocks to be avoided, a minimum of
A: Deadlock: Each computer process waits for a resource that is being assigned to another process in a…
Q: When sending and receiving emails online, what are the key distinctions between the SMTP, POP, and…
A: Introduction: SMTP sends messages from the sender's email client to the receiver's email server. POP…
Q: Casinos have devised different automated mechanical methods for shuffling the cards. One such method…
A: solution is given in next step:
Q: When planning a high-performance open hash table, keep the following in mind:
A: The hash tableA hash table in hashing represents data in the array form, with each item containing…
Q: Explain the 10 benefits of digital media
A: Digital Technology: Digital technology has transformed nearly every aspect of modern life. Travel,…
Q: Write a java program that reads a mile in a double value from the console, converts it to…
A: The JAVA code is given below with output screenshot Following conversions are taken into…
Q: Prove that the sum of an even integer and an odd integer is odd. Let n₁ be an even integer, and let…
A: Here we proved that the sum of an even integer and an odd integer is odd
Q: When it comes to firewalls in modern businesses, which architecture has become the norm? Why?…
A: Introduction: Security measures for a subnet that include a demilitarised zone firewallThese days,…
Q: Why doesn’t this work? And how does the marcher class work? Thanks!
A: import java.util.Scanner; import java.util.regex.Matcher; import java.util.regex.Pattern; public…
Q: Exactly why is it crucial for people to be proficient in spreadsheets in the modern workplace?…
A: Introduction: Microsoft made it. Microsoft Excel is a spreadsheet that runs on Windows, macOS,…
Q: Consider an online holiday booking system. The users can register to book a holiday package. Which…
A: When a wrapper is required to hide the complexity of the core object from the client, the proxy…
Q: How does a cache hierarchy operate, and could you please explain it to me?
A: Given: How would you characterise a real cache hierarchy's structure? The hierarchy of a cache…
Q: Please share some best practices for configuring a firewall.
A: The answer to the question is given below:
Q: Explain what you mean by the term "logical addressing."
A: Logical addressing A logical address in computer architectures is the address that a memory region…
Q: Examine the impact of wireless networks in developing countries. Where wireless networks are being…
A: Introduction: Wireless networks are a subset of computer networks in which communication between…
Q: Acces Specifiers in Java Create a public method introduce() that displays “MeepMoop, I am {name}.”…
A: Please refer to the following steps for the complete solution to the problem above.
Q: In the table above, Vanesa’s last name was omitted. Write an SQL query to add the last name. Assume…
A: Note: Due to company policies I am compelled to solve only one question and that is the first…
Q: structured references to display the value in the first row and first AcademicGroups table. SUMTE od…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: Write a java program that reads a number in meters, converts it to feet, and displays the result.…
A: The solution is given in the next step
Q: Can you list the limitations of the Tor network?
A: Tor Network Multi-layered encryption and great many relays structure the foundation of the TOR…
Q: Consider an online holiday booking system. The users can register to book a holiday package. Assume…
A: Object-oriented software design The system is seen as a collection of objects when using the…
Q: When does it make sense to divide up complex computer programs or operations into more manageable…
A: Introduction: It makes sense to arrange processes as a subsystem if they share a certain set of…
Q: [D] Is each of the following sequences graphical? (17) 2, 2, 2, 1, 1, 1 (18) 3, 2, 2, 2, 2, 2, 1…
A: Here in this question we have given three graphical sequence and we have asked which sequence is…
Q: Recall that the factorial function is defined as n! = 1·2·3· (n − 1) n and, by convention, 0!= 1.…
A: Given: n! = 1*2*3*..*(n-1)*n = n*(n-1)*...*3*2*1 factorial of n is : numbers multiplied from 1 to n…
Q: Consider an online holiday booking system. The users can register to book a holiday package. Which…
A: Given that, There is a Online holiday booking system in which the users can register to book a…
Q: Specify the TOR system.
A: Users can access the internet anonymously thanks to the Tor network. Web browsers, instant…
Q: Consider an online holiday booking system and the User class in the design. Which of the following…
A: Let's see the answer:
Q: by using the table in the query attached: Show the name, contact number and email address of the…
A: Demo data has been used to solve the query The SQL query is given below with output screenshot
Q: Building #11 is undergoing a major renovation. Implement a query to close all requests from…
A: The sql query is written in step2
Q: Consider an online holiday booking system. The users can register and log in to book a holiday…
A: Please find the answer below :
Q: What was the name of the proprietary Linux firewall that was discussed during the presentation, and…
A: Given: What was the name of the non-free Linux firewall that was mentioned in the presentation, and…
Q: develop a library management system application. More specifically, your application should use an…
A: The solution is given in the next step
Q: Consider an online holiday booking system. The users can register to book a holiday package.…
A: Answer:
Q: How do I fix this code please read intructions( in java)
A: The java program is given below:
Q: An is the name for the type of server used in two-tier architectures to provide clients with data…
A: The client always occupies space on the first layer of a two-tier architecture.
Q: Define a set X of strings in the symbols 0 and 1 as follows. B. 0 and 1 are in X. R1₁. If x and y…
A: Introduction An equation that represents a sequence based on a rule is called a recurrence relation.…
Q: Ara Howard created a project called Fattr which implements a common desire among Ruby developers: a…
A: Here is an illustration of the issue. You would have to create the method yourself in order to…
Q: When it comes to keeping your computer safe, what measures can you take to prevent power surges and…
A: Given: We have to discuss When it comes to keeping your computer safe, what measures can you take…
Q: Just what are the differences between ensuring that a deadlock doesn't occur and merely avoiding it?
A: When a group of processes are in a deadlock, each process is waiting for a resource that is…
Q: Consider the following task of building a zoo for Drexel! You've gathered m donors to fund the…
A: Brief Introduction: We have to write a code in Python that will make sure that the gcd of numbers…
find a counterexample for the statement,
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- What does the function return for any positive values of x and n ? The answer should be a general formula in terms of x and n. int what_do_I_do ( int x, int n ) { if ( n = = 1 ) return x; else return x + what_do_I_do ( x, n – 1 ); } C++ be quick pleaseIf b is a unit modulo m and a is another unit with a=b^d (mod m), we say that d is the _________ of a modulo m to the base b and write d =___________.Consider the following statement: Statement A: ∀ integers m and n, if 2m + n is odd then m and n are both odd. Disprove Statement A. That is, show that Statement A is false
- Rewrite the following statement formally. Use variables and include both quantifiers ∀ and ∃ in your answer. Every even integer greater than 2 can be written as a sum of two prime numbers.Show that the following argument is valid for any natural number n ∈N. p1 →p2 p2 →p3 ... pn−1 →pn ¬pn ∴¬(p1 ∨···∨pn−1................Convert the following statement to a statement that uses the universial quantifier:"There is no largest integer."
- given a positive integer n, greater than 1, assign True to is_prime if n has no other factors other than 1 and itself. using python and for or range statementsWrite a program to compute 1^N + 2^N …. 12^N by using ( While or For or Do-while )Write a program in Scala programming language to check a given integers anx return true if it is within 50 of 100 or 300
- Write a program that computes the following: sigma summation i=0 to N (i^3 +2N)How many can 3 digits be formed using the digits from 1 to 5 if the digit 2 is never there in the number?If f(x) = 2.x^3 and g(x) = x + 1. What is (g o f) (x)?Write a program that reads in two integers and determines and prints whetherthe first is a multiple of the second. [Hint: Use the remainder operator.]

