structured references to display the value in the first row and first AcademicGroups table. SUMTE od structured references to display the total
structured references to display the value in the first row and first AcademicGroups table. SUMTE od structured references to display the total
Chapter8: Working With Advanced Functions
Section: Chapter Questions
Problem 3.3CP
Related questions
Question
Need help to do this type of questions for Excel and provide the steps as that given.
Transcribed Image Text:structured references to display the value in the first row and first column of the
AcademicGroups table.
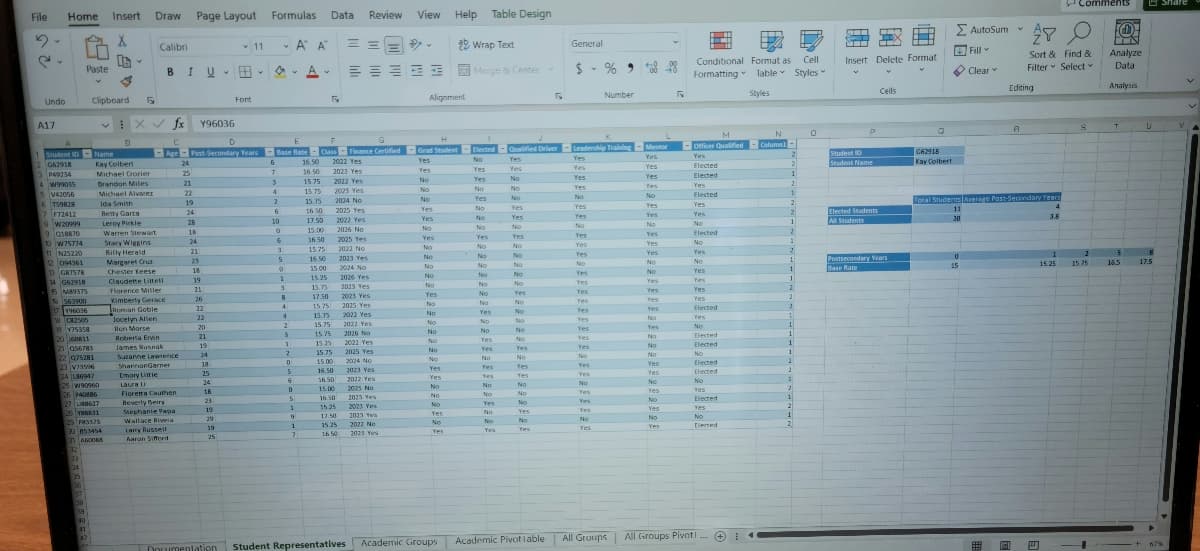
13. In cell A17, use the SUMIF function and structured references to display the total
membership in 2023 for groups with at least 40 members.
14. Lael is also planning for student groups that the office will be working with in the c
year. She decides to create a PivotTable to better manipulate and filter the student
Transcribed Image Text:File Home Insert
2.
Y
X
2.
Undo
A17
4W99035
5V42056
6 T59828
7 F72412
8 W20999
9018870
1 Student ID Name
2 G62918
3 P49234
10 W75774
11 N25220
12 094361
13 G87578
14 G62918
15 M89375
16563900
17196036
18 82505
VISSER
29 Y75358
20160811
21 056783
22 075281
Paste
23 V79506
24 186947
33
134
25 W90960
26 940886
27 8627
135
Clipboard
38
26 VMKK31
29 PM3375
30 853454
39
40
2) AGOONS
32
41
42
3
Kay Colbert
EX
R
B
Y
Michael Crozier
Brandon Miles
Michael Alvarez
Fy
Ida Smith
Betty Garza
Leroy Pirkle
Leroy P
Warren Stewart
Draw Page Layout Formulas Data Review View
Α' Α'
Stacy Wiggins
Billy Herald
Margaret Cruz
Chester Keese
Calibri
BI
fx
C
Age
Claudette Littell
Florence Miller
Kimberly Gerace
Roman Goble
Jocelyn Allen
Ron Morse
Roberta Ervin
James Rusnak
Suzanne Lawrence
ShannonGarner
Emory Little
Laura Li
Floretta Cauthen
Beverly Berry
Stephanie Papa
Wallace Rivera
Larry Russell
Aaron Sifford
I U
24
25
21
22
19
24
28
E
D
Post-Secondary Years Base Rate
Base
6
7
18
24
21
23
18
Y96036
19
71
21
26
22
22
20
U-A-
21
19
24
18
25
24
18
23
19
29
11
Font
19
25
4
2
6
10
0
Y
6
3
5
0
1
3
B
4
4
2
3
1
2
0
5
6
G
Finance Certified
F
flate-Class-Finance Certified
2022 Yes
2023 Yes
2022 Yes
0
5
9
1
7
F
16.50
16.50
15.75
15.75
15.75
16.50
17.50
15.00
16.50
15.75
16.50
15.00
15.25
15.75
17.50
15.75
15.75
15.75
15.75
15.25
15.75
15.00
===
三三三五五
2023 Yes
2024 No
2025 Yes
2022 Yes
2026 No
2025 Yes
2022 No
15.00
16.50
15.25
2023 Yes
2024 No
2026 Yes
2023 Yes
2025 Yes
1015 Ver
2025 Yes
2022 Yes
2022 Yes
2026 No
2022 Yes
2025 Yes
2024 No
16.50 2023 Yes
16.50
2022 Yes
2025 No
2025 Yes
2023 Yes
17.50 2023 Yes
15.25
2022 No
UNO
16.50 2023 Yes
Alignment
Yes
No
H
Grad Student
Yes
Yes
No
No
No
Yet
Yes
Yes
No
No
No
No
No
Yes
No
nes
No
No
No
No
No
No
Help Table Design
Yes
Yes
No
No
No
ab, Wrap Text
Yes
No
Yes
Merge & Center
I
Elected
No
Yes
Yes
No
Yes
No
No
No
Yes
No
No
No
No
No
No
No
Yes
No
No
Yes
Yes
No
Yes
Yes
ve
No
No
Yes
No
No
Yes
No
No
No
Yes
Yes
No
Yes
No
No
No
No
No
Yes
No
No
No
No
No
Yes
No
Yes
Yes
-
Qualified Driver Leadership Training - Mentor
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
No
No
Yes
Yes
No
Yes
No
No
No
5
Yes
No
Yes
General
$ - %
Yes
Yes
No
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
Yes
No
Yes
Yes
No
Yes
Yes
•
Yes
No
Yes
Number
500 98
Yes
Yes
No
Yes
Yes
Yes
No
No
Yes
Yes
Yes
Yes
No
Yes
No
140
No
No
Yes
Yes
No
Yes
No
Var
Yes
No
Yes
√
Cell
Conditional Format as
Formatting Table Styles
M
-Officer Qualified
Yes
Elected
Elected
Yes
Elected
Yes
Yes
No
Elected
No
Yes
H
No
Yes
Yes
Es
Yes
Yes
Elected
Yes
No
Elected
Elected
No
Elected
Elected
No
Yes
Elected
Yes
No
Elected
Documentation Student Representatives Academic Groups Academic Pivotiable All Groups All Groups Pivot!
I
Styles
N
Column1
2
2
1
2
1
2
2
1
2
1
2
1
1
1
2
2
2
1
1
1
1
1
2
2
1
2
1
13
1
2
0
ET TIX
Insert Delete Format
V
Student ID
Student Name
Elected Students
All Students
Cells
T
H
Postsecondary Years
Base Rate
Q
G62918
Kay Colbert
Σ Autosum
Fill
Clear
15
P
27
A
Editing
A
Total Students Average Post-Secondary Years
11
30
4
A
Sort & Find &
Filter Select
Comments
3.8
S
2
15.25 15.75
4
F(0)
Analyze
Data
Analysis
T
5
16.5
U
8
17.5
Share
+ 67%
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781305627482
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781285196145
Author:
Steven, Steven Morris, Carlos Coronel, Carlos, Coronel, Carlos; Morris, Carlos Coronel and Steven Morris, Carlos Coronel; Steven Morris, Steven Morris; Carlos Coronel
Publisher:
Cengage Learning