Find regular expression for the following DFA using Arden's Theorem a 91 a b q2 (93
Q: Explain why doubling the speed of the systems on an Ethernet segment may result in decreased network…
A:
Q: The derivation of an O(log(N)) program for Fibonacci series also explain it step by step
A: soluton is followed on next step:-
Q: How do software and hardware vary in computers?
A: Definition: The two components of a computer system are hardware and software. To work effectively,…
Q: A computer may generate and analyze information in a variety of ways due to its versatility. Could…
A: Given: Similar to humans, computers process information using their brains. The central processing…
Q: Why are watchdog timers crucial for so many embedded systems?
A: Watchdog timers and their significance in embedded systems: The simplest kind of embedded system has…
Q: How would you define an algorithm in your own words?
A: Definition A set of clear, executable steps that define an ordered, ending process is known as an…
Q: Explain how the probabilistic and deterministic methods to Ethernet vary from one another.
A: Ethernet with determinism: Limited communication in the context of the Industrial Ethernet refers to…
Q: Why does sending emails make it more likely that the receiver may misinterpret what you meant to…
A: Given: We must be careful not to misread one another in email conversations. That's because of two…
Q: In this comparison, the Classical Waterfall model and the Rational Unified model will both be…
A: SDLC includes these two models: Cascade programming involves substantial a advance planning and…
Q: Pick one of the two problems (not both): Question 1: Assignment 4 (Process scores in a text file)…
A: Answer: Algorithms: Step1: We have taken file name form user Step2: If file does not exist the n…
Q: Explain how the probabilistic and deterministic methods to Ethernet vary from one another.
A: Deterministic ethernet -- Deterministic Ethernet refers to a networked communication technology that…
Q: Discuss ways in which the priority inversion problem could be ad dressed in a realtime system. Also…
A: Introduction: Priority Inversion: It is a concept in which a lower\lesser priority process preempts…
Q: Are you able to list the three key sites in your healthcare company where data is gathered and…
A: Introduction: MS Excel is mostly used for reporting, data analysis, and storage. Because of their…
Q: The logical clock timestamp scheme presented in this chapter provides the following guarantee: If…
A: so first we will talk about logical time stamps so the main concept of logical clock is happend…
Q: 111 Consider the sequence {a} = 1, 3, ¹27, 1 (a) Write the sequence using a recurrence relation. (b)…
A:
Q: When opening a file in Python, the exists. O close() function w mode strip() function w+ mode x mode…
A: Answer: The Python "FileExistsError: [Errno 17] File exists" happens when we attempt to make a…
Q: Hey, How would a depth-first search, DFS look for this graph? Thank you in advance!
A:
Q: Describe in pseudo-code an implementation of the methods addLast(e) and addBefore(p,e) realized by…
A: The Answer is in step-2.
Q: A collection of 2" stations uses the adaptive tree walk protocol to arbitrate access to a shared…
A: In according to adaptive tree walk: we make all the stations in tree format so slot is depends on…
Q: The SSTF disc scheduling algorithm's risks are what?
A: Algorithms for operating system scheduling: Scheduling based on first-come, first-served (FCFS). SJN…
Q: What are the advantages of using dedicated hardware devices for routers and gateways? What are the…
A:
Q: virtual memories utilised in embedde
A: Virtual Memories Utilized: A frequent method in an operating system for a computer is virtual memory…
Q: Assume the sender is aware of a constant round-trip delay between the sender and recipient. Given…
A: Answer: Given, constant round trip delay and we need to write points regarding the round trip delay…
Q: What are the three characteristics that a network must have in order to be functional and effective?…
A: Start: Production schedulers now specify the location and methods of production as well as the…
Q: First, write a class named Movie that has four data members: title, genre, director, and year. It…
A: Here I have created the classes as per the question. In each class, I have defined the method to get…
Q: There are several ways that computers produce and process information. There should be two of…
A: Information: Depending on the computer system, information may be created and processed in a variety…
Q: Embed your method in a complete program that requests for three variables all of the types int and…
A: The answer for the above question is given in the below steps for your reference.
Q: What kind of initialization needs to be done for an open-address hash table? What about a chained…
A: Each array location's key needs to be populated for open-address hash table since all the elements…
Q: What does the phrase "computer network" really mean? What are the many components that combine to…
A: A network comprises multiple nodes, or computers, that are connected to facilitate sharing resources…
Q: In the context of a computer network, explain how dependability and availability are related. the…
A: An electronic network: This system of interconnected computers allows for the sharing of data and…
Q: For instance, you'll need to recruit individuals if you're starting a media firm and want graphic…
A: Social media firm A creative business that creates and manages social media marketing plans and…
Q: CHALLENGE ACTIVITY 1.8.1: Compute an expression. Write a statement that assigns finalResult with…
A: Answer: Algorithms Step1: We have initialized the n1 ,n2 sum and res where n1 and n2 will be user…
Q: (a) the private key; (b) the encrypted ciphertext for 15; (c) the decrypted original message for…
A: Please review the answer. Explanation: Q1: In RSA encryption scheme Public key consist of…
Q: Which three procedural programming language subcategories are available? Give a brief justification…
A: Definition: A programme created using just structured programming constructions is said to be…
Q: When considering about modernizing their data center, potential consumers should take into account…
A: As the most abundant greenhouse gas in the atmosphere, carbon dioxide emissions have a significant…
Q: Discuss ways in which the priority inversion problem could be ad dressed in a realtime system. Also…
A: Before directly going to the question, Let's first see about the priority inversion and the problem…
Q: Declare a method with three arguments all of the type int. The method should return the greatest of…
A: The program is written in java. Please find the program in below step.
Q: How can systems that implement the principle of least privilege still have protection failures that…
A: Let's begin by giving those who are unaware with principal of least privilege (PoLP) a basic…
Q: After formatting a filesystem on a hard drive, it must be used by all partitions on that hard drive.…
A: Given: When you format a hard drive, harmful programmed are removed, which can make your computer…
Q: Write a program that first gets a list of integers from input. The input begins with an integer…
A: Below I have provided java Programming. Also, I have attached the screenshot of the code and output…
Q: The role played by the Internet of Things in the development of smart homes. Give some examples.
A: Introduction: If a home has multiple smart appliances that you can control from a distance by…
Q: Oftentimes, filter tools like as sed and awk are used to prepare data in pipelines. Is this a true…
A: Commands using sed and awk Filtering text manipulation procedures that employ pipes may be…
Q: What particularly should you search for in a firmware update for the printer?
A:
Q: In the realm of computers, architecture and computer organization are two separate ideas.
A: the above question that is in the realm of computers , architecture and computer organization are…
Q: What does the phrase "computer network" really mean? What are the many components that combine to…
A: A computer network or data network is a telecommunication network that allows computers to exchange…
Q: What do you mean by Rate Limiting?
A: Rate Limiting: Rate limiting is the concepts of computer networking which is used to direct rate of…
Q: The SSTF disc scheduling algorithm's risks are what?
A: Scheduling method for SSTF discs: The technique known as SSTF, or Shortest Seek Time First, is used…
Q: Are there any disadvantages or advantages of using the cloud for storage? Give a list of companies…
A: Please find the answer below :
Q: What are some of the possible services that a link-layer protocol can offer to the network layer?…
A: Some of the possible services that a link-layer protocol can offer to the network layer are:…
Q: A system has four processes, viz. P1 to P4, and three resource types. The system is in a safe state…
A: we need to find, if the given resources can be granted to the processes. We use Bankers algorithm.
Provide step by step explanation and provide correct solution.
Sub:Formal System
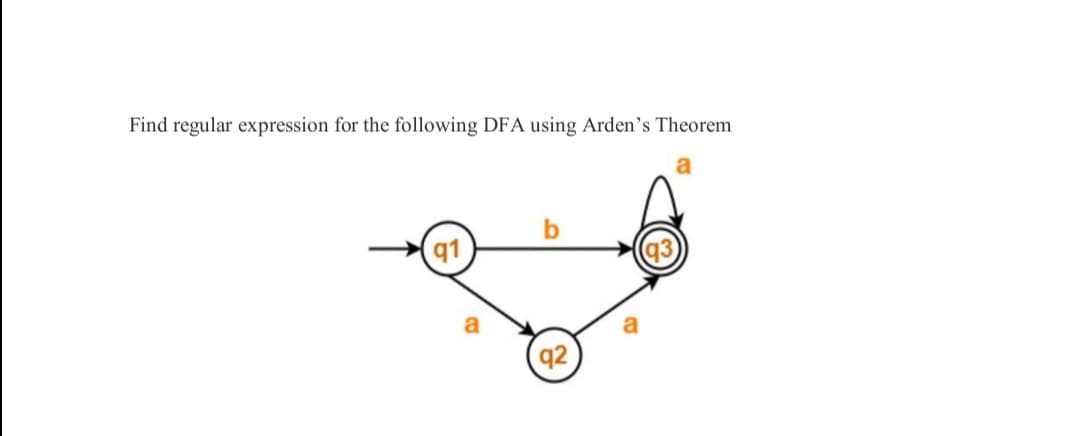
Step by step
Solved in 2 steps

- From the following function : G = A + B (A+C) + AC Use the theorem of boolean algebra and obtain the reduction of the function, then draw the diagram of that function.Using De Morgan’s Law, show (A + B)’ (A’ + B’)’ = 0Find the result of the following subtraction using the first integral (1356) 8 - (137) 8 =?

