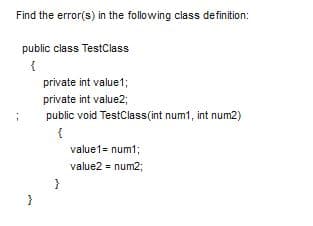
Find the error(s) in the following class definition: public class TestClass { private int value1; private int value2; public void TestClass(int num1, int num2) value1= num1; value2 = num2;
Q: How can man-in-the-middle (MITM) attacks be avoided? Step by step, provide your answer.
A: In a man-in-the-middle attack, the culprit places himself in a continuous communication or data move…
Q: Which VLAN is intended to provide administrative access to network devices?
A: A management VLAN can be used to allow switch administrators access. This may be the same as the…
Q: uting revolution may have several business consequences. Is cooperation on your m
A: Introduction: Below the cloud computing revolution may have several business consequences.
Q: Which of the following statements is TRUE about the space complexity of sorting algorithms?
A: 2. The space complexity of any algorithm do not depends on the original order of array. 3. Merge…
Q: Suppose you want to run thecalcTotal()function each time the user of a web form changes an input…
A: document.getElementById("quantity").onchange = calcTotal; Answer: B option is correct.
Q: How did the term "spool" come to refer to the output from a printer?
A: Answer:
Q: What are distributed denial of service (DDOS) attacks, and how do they work?
A: Introduction: DDoS attacks include: It stands for Distributed denial of service; DDoS attacks are…
Q: Q2\ write an oop program to read and print information about you ? 1 Add file
A: With the help of oop concepts accept user information and print it. I used c++ programming language…
Q: Given array A = [145, 251, 283, 960, 350, 231, 520, 152, 412, 280]. Do the following tasks. %3D a.…
A: Answer is given below-
Q: Changing a database's setup necessitates the DEMS to update its catalog. Changing the catalog by…
A: The database information is stored in the System Catalog.
Q: Cooperation may have been affected by the Cloud Computing Movement, but the degree of that effect…
A: Cloud based infrastructure has gained a lot popularity recently.
Q: An embedded system is a kind of processor that may be programmed to do a specific task. What is the…
A: What exactly is an embedded system? An embedded system is a combination of computer hardware and…
Q: To ascertain how everything is interconnected. Our job may benefit from system engineering in a…
A: Modeling and simulation (M&S): Modeling and simulation (M&S) is the process of generating…
Q: How can the integrity of the data be protected?
A: Start: The physical data model depicts the information that will be utilised to create the database.
Q: H.W. Design the interface circuit that make the interface between 8 switch and control 8 LED where…
A:
Q: Create, compile, and run a recursive program. Choose one of the labs listed below and program it.…
A: Answer is given below-
Q: tion be affected
A: The imperatives of regular IT infrastructure have been progressively clear many years since the…
Q: So, what's the big deal with data encryption anyway?
A: Data encryption: The process of converting plaintext data into ciphertext is known as data…
Q: What is the time complexity of traversing a balanced binary search tree with n nodes? O(1) O Olm)
A: The correct answer is O(n).
Q: What is returned when invoking the method call myFun (4)? int myFun (int n) if (n > 0) 2)); return…
A: Your answer is given below with an explanation.
Q: Is it feasible to distinguish between multiprogramming and multithreading in a computer programme?
A: A multiprogramming operating system can execute multiple applications with a single processor on a…
Q: Describe the protocols that are used.
A: Protocols: A procedure is essentially the same as a rule. Communication happens between elements in…
Q: Preemptive scheduling entails what exactly?
A: Preemptive Scheduling: The system is described as non-preemptive or cooperative if scheduling takes…
Q: What precisely is routing? Describe the distance vector routing method.
A: What precisely is routing? Describe the distance vector routing method.
Q: What are the advantages of doing regular backups in systems administration?
A: The advantages of regular backups in system administration are: Security Ease of management…
Q: We contemplated raising the timeout period after one of our users had a timeout. This is a method of…
A: Foundation: Window-based congestion control is used by the Transmission Control Protocol…
Q: Are there signs that the Cloud Computing Movement having an impact on collaboration? Certainly.
A: Cloud computing is the on-demand availability of computer system resources, most notably data…
Q: What is routing, and how does it work? Defintion of two popular routing methods is necessary.
A: Routing Algorithms: An algorithm for routing is a process that determines the best path to take to…
Q: Consider the following class defintion for class named MyClass and answer the following questions.…
A: The syntax for creating object of the class is as follows: 1. For default constructor Classname…
Q: Explain briefly how you propose to examine this DDoS assault using security engineering techniques.
A: All packets are checked in-line, and out-of-band detection is performed by analyzing traffic flow…
Q: How can a Man in the Middle attack be avoided?
A: Introduction A man in the middle attack occurs when an intruder (specifically, a hacker) enters your…
Q: Analyzing a system is a challenging task. What are the challenges? When examining a system to see…
A: What are some of the challenges associated in evaluating a system? challenges: When dealing with the…
Q: In concurrent programming, what is the impact of the interaction of processes?
A: Concurrent Programming: The term "concurrent programming" refers to the practice of running many…
Q: Why is a top-down approach to data security preferred over a bottom-up one?
A: We have to state that why is a top-down approach to data security preferred over a bottom-up one.
Q: What are some of the most common software-related problems that people encounter?
A: Software-Related Problems: Inaccurate data alterations, faults in out-of-date installed…
Q: 3. Write a C program containing a recursive function that will get the whole number quotient result…
A: Given: To write a C program to find quotient of two numbers.
Q: Are there any applications where a dot-matrix printer is more suited than another form of printer,…
A: A Dot Matrix Printer is the oldest type of printer and one of the good examples of computer printer…
Q: What steps may be taken to avoid man-in-the-middle (MITM) attacks? Answer the question step-by-step.
A: A man-in-the-middle attack is a type of eavesdropping attack: Every workplace application, including…
Q: Create a video showing how your game runs, play the game and explain how it plays. (don't worry…
A: ALGORITHM:- 1. Take an input number from the user in the range 1 to 100. 2. Generate a random number…
Q: 3. Write a C program containing a recursive function that will get the whole number quetient result…
A: Find the required code in C given as below and output :
Q: the study of computers Multithreading's major purpose?
A: Multithreading allows many pieces of the programme to be executed at the same time. Threads are…
Q: How can a distributed denial-of-service assault be effectively countered?
A: A simple explanation: It's a smart idea to reduce the assault surface area. Reduce the surface area…
Q: What is the index of the right child of the node with index 5, given an array representation of a…
A: Answer : option (b) Index of the right child of the node with index n ,will be 2(n) +1;
Q: Define interleaving interleaving.
A: Given 1. To know about the interleaving.
Q: Note: Use Ruby language to write your code. Task Assigned: Write a program to read input two strings…
A: Code: puts "Enter sp_top= "sp_top = gets.chomp puts "Enter sp_bottom= "sp_bottom = gets.chomp…
Q: When constructing an LMS portal, what system development life cycle should we follow?
A: It is prudent to adhere to the Agile system development life cycle.
Q: Describe how a firewall resembles a data stream that has been divided into packets.
A: According to the question A firewall is a community safety tool that monitors incoming and outgoing…
Q: Draw W7 . Be able to draw 10 of its subgraphs.
A: We need to draw W7 and it's 10 subgraphs.
Q: please write code using userdefine class names it Stack to convert expresion from infix to postfix…
A: Code to convert Infix To Postfix using user define a class #include <bits/stdc++.h> using…
Q: What is a routing? Describe how to use distance vector routing.
A: Routing is the process of selecting a path for traffic in a network or between or across multiple…
Step by step
Solved in 4 steps with 2 images

- (programming) A class may be made immutable in a number of ways. with the aid of an illustrationHand-write two Java classes, Car and Truck. They are bothsubclasses of Vehicle.a. A car has an additional instance variable, number of doors.b. A truck has an additional instance variable, number of axlesc. Write a constructor that requires input for the instance variables of each class(including registration number and owner name).d. Write getters and setters for all instance variables for both classes.Java A class always has a constructor that does not take any parameters even if there are other constructors in the class that take parameters. Choose one of the options:TrueFalse
- Static class members are exactly what they sound like. When and how can they be used?Find the error in each of the following code segments: // Superclasspublic class Vehicle{private double cost;(Other methods . . .)}// Subclasspublic class Car extends Vehicle{public Car(double c){cost = c;}}**Python code** Write a class definition line and a one line docstring for the class Dog. Write an __init__ method for the class Dog that gives each dog its own name and breed. Test this on a successful creation of a Dog object.>>> import dog>>> sugar = dog.Dog('Sugar', 'border collie')>>> sugar.name'Sugar'>>> sugar.breed'border collie'
- Java program Make a class Employee with a name and salary. Make a class Manager inherit from Employee. Add an instance variable, named department, of type String. Supply a method toString that prints the manager’s name, department, and salary. Make a class Executive inherit from Manager. Supply appropriate toString methods for all classes. Supply a test program that tests these classes and methods.Type a Java method constructor for the "book" Class, which takes values as parameters for all of these attributes.The" book " Class has the following properties: title (string), author (string), year (int), pages (int).Complete the method in Java. Name of the public class is Assignment1.java
- Draw the UML diagram of the following class: public class Employee { String name; double salary; public Employee() { } public double getSalary() { return this.salary; } public String getName() { return this.name; } }In pseudocode, write the first line of the definition for a Poodle class. The class should extend the Dog class.Use the class diagram below to create a Parking Charge class for an object-oriented parking system. Write your code using java. Classes should contain properties and method implementations. N.B. Try to make your code readable.

