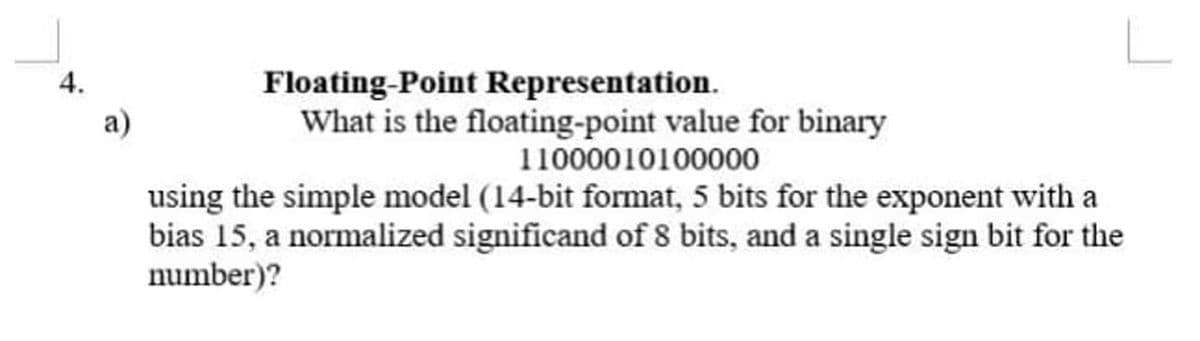
Floating-Point Representation. What is the floating-point value for binary 4. a) 11000010100000 using the simple model (14-bit format, 5 bits for the exponent with a bias 15, a normalized significand of 8 bits, and a single sign bit for the number)?
Q: What are the benefits of employing Firewall rules?
A: Introduction: There Are so many benefits benefits of Firewall.
Q: What are some broad methods that firms use to get a competitive advantage? What are some examples of…
A: INTRODUCTION: Here we need to tell some broad methods that firms use to get a competitive advantage…
Q: You need to know how to distinguish between some of the most important development tools and…
A: Introduction: As system development projects grow and the discipline of software development starts…
Q: What does a pointer variable imply? What is the purpose of it? What is a dynamic array, and how does…
A: A pointer is the memory address of a variable. Recall that the computer’s memory isdivided into…
Q: "Infrastructure mode" refers to how wireless networks are set up. During non-infrastructure mode,…
A: Infrastructure mode: The repeater is a wireless connection architecture in which the cable network…
Q: There are four separate forms of Nmap port scanning, so how does the three-way handshake fit in? Is…
A: Solution: A network map was created to help the Network Administrator understand the network that he…
Q: Which of the following statements most accurately sums up your perspective on the significance of…
A: Authentication: Encryption is necessary for data security while it is in use or in transit. When…
Q: Identify the network troubleshooting tool that is used to examine the cable test and validity test?…
A: The options “Cable tester”, “Speed test site”, and “Fiber optic cable” are incorrect options for the…
Q: organisational, and t
A: Organizational, administrative, and technical considerations Senior administration much of the time…
Q: Create a brief note about the fundamental Input / Output functions in C. Provide a list of the most…
A: The above question that is given above is answered below step. in step 2 i have answered the…
Q: Describe the steps of the Existential Forgery Attack against the RSA Digital Signature, as discussed…
A: Intro In a system, digital signature forgery is the ability to create a pair consisting of a…
Q: Q1. What is meant by the term Application Programs? How it is different from System Programs? Q2.…
A: Given To know about the 1. Application program and difference between application program and system…
Q: Computer science What are the arguments, pros and cons, for Python's use of indentation to specify…
A: Introduction: What are the arguments, pros, and cons, for Python's use of indentation to specify…
Q: During the system development process, would it be required to identify and briefly explain the…
A: Intro During the system development process, would it be required to identify and briefly explain…
Q: I am wondering are those two c++ code express similar meaning? **val=2; *val *=2;
A: The problem is based on the basics of pointers in C++ programming language.
Q: Write a console-based application that displays every perfect number from 1 through 10000. A number…
A: The C# code using System; namespace PerfectNumberApp { class Program { static bool…
Q: what exactly is a Web form
A: Introduction: A web form is similar to paper or database forms that we usually fill forms by…
Q: Assume that X1 is initialized to 11 and X2 is initialized to 22. Suppose you executed the code below…
A:
Q: When it comes to delivering services, TCP is a dependable full-duplex transport layer protocol. It's…
A: The Transmission Control Protocol (TCP) is in charge of managing data transmissions. combining the…
Q: What do you think about the FSF?
A: Introduction FSF is abbreviated as Free Software Foundation. It is a non profit organization founded…
Q: Discuss and explain the importance of emerging cloud computing technologies that enhance…
A: Introduction Cloud Computing: Customers can use cloud computing to obtain comparable programmes…
Q: There should be a list and description of the four memory allocation methods taught in Operating…
A: Introduction There should be a list and description of the four memory allocation methods taught in…
Q: What are the advantages and disadvantages of TCP?
A: Advantages of TCP/ip 1) It is standard model that can be deployed in practical networking…
Q: Why do certain authentication techniques work better than others in protecting user information
A: Introduction: Information sent across a functional interface between a source user and a…
Q: 1. Explain the functionalities and the relationships among the following essential components: 1.…
A:
Q: Is there a distinction between computer science and computer engineering?
A: Introduction: Both computer science (CS) and computer engineering (CE) are high-tech fields that…
Q: define the phrase "non-technical" in the context of cyberattacks?
A: Non-Technical: Non-technical cybersecurity assaults are defined and explained. Non-technical…
Q: Discuss why you need to protect certain data and files. Do you have data backups, and if so, where…
A: A data set, sometimes known as a file, is a collection of information. Data or files containing…
Q: What role do you believe technology will play in a new company?
A: Introduction: It enabled businesses to do transactions in a more timely, easy, and efficient manner.
Q: According to this assertion, Apache Spark performs RDD transforms "lazily."
A: Transformation of RDD: Spark Transformation is a function that transforms existing RDDs into new…
Q: Your opinion matters. Do you think the cloud is a good concept or a poor one? Why?
A: What Is A Cloud In Cloud Computing? In Cloud Computing, the word "cloud" refers to…
Q: Three Schema Architecture features have been included into third and fourth generation DBMSS systems…
A: Introduction Three Schema Architecture features have been included into third and fourth generation…
Q: Hey, I have already received a good answer to this question but I am looking for greater detail to…
A: Using Banker's algorithm:- Instances of resource R1 = 3 Instances of resource R2= 2 Instances of…
Q: Is it possible for you to explain the concept of inheritance?
A: Answer 1. Inheritance: Inheritance is a powerful feature of object-oriented programming which allows…
Q: 3. Write an application for Limpopo's Car Care Shop that shows a user a list of available services:…
A: we will create carShopDemo.java file and in main method we write our logic.
Q: ComputerscienceWhat unique rules apply to drawing context diagrams?
A: Introduction Context diagrams have only one process that shows the overall system being modeled…
Q: The usage of mobile phones in the workplace is a hot-button issue for many firms.
A: It Is very obvious that you know What The Mobile Phone is but let just go into it to understand it…
Q: Explain why utilizing model checking rather than evaluating a program's correctness against a formal…
A: In model checking, systems are modeled by finite state machines, and this finite state model is…
Q: What do you mean by "transitive dependency" in your definition?
A: Answer: A transitive dependency in a database is a backhanded connection between values in the very…
Q: 1. Enumerate all your desired attributes/features/functionalities for your file organization 2.…
A: As per the guideline, we can only solve one question at a time. Hence resubmit the question for…
Q: You are given an empty hash table of size 7 that uses open addressing. The Q4) following sequence of…
A:
Q: Discuss the four main issues that interactive system designers face while creating them.
A: Interactive systems are computer systems characterized by significant amounts of interaction between…
Q: Because computers are so sophisticated, this is the reason. Since when has the use of computers…
A: In Early 1980's, College/School grounds involved PC centralized servers in training since the…
Q: Are there any differences between computer-based media and more traditional forms of media that…
A: The following are the qualities that separate the computer and information technology environments…
Q: omputing and fog c
A: Introduction Cloud computing refers to the on-demand availability of computer system resources like…
Q: What distinguishes an interrupt service routine from a regular subroutine?
A: Introduction: The main distinction is that you know where the subroutine is executed. A subroutine…
Q: C automatically passes arrays to functions by reference, the called functions can modify the element…
A: Function Calling: A call to a function is a crucial feature of the C programming language. When a…
Q: what are the best practises for businesses
A: 1)Choose a good password Don’t use data that other people know, such as birthdays or pets’ names…
Q: Which type of identifier is const? A. preprocessor directive B. programmer defined identifier C.…
A: Preprocessor directives are used to instruct the compiler to include other source files in the…
Q: Explain what a "cursor" is.
A: Introduction A cursor is a little moving object on the computer desktop that moves with respect to…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

- A(n) __________ is an integer stored in double the normal number of bit positions.For 10 bits floating point representation using: seeeefffff, what is the bias for denormalized numbers? A. 7 B. 6 C. 4 D. 3 E. 2 What is the range of integers that can be represented using 8 bits 2's complement? A. -127 to 127 B. -128 to 127 C. -127 to 128 D. 0 to 255 E. 0 to 256Given a floating point representation 10110 11101101000 (5-bit exponent and 11-bit significant) 3. if the exponent is in signed magnitude and the significant is in two’s, what are its normalized floating point representation in hexadecimal and its real value in hexadecimal?
- Examples of 8-bit binary representations of the decimal value 30 are shown below. definition a) the opposite of a term; b) Excess-M;?1) Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?1)Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below.Show the sign, exponent, and mantissa (significand).a. -2.40625b. 11.2265625 2) Given the following binary number: 1101.0111, what will be its decimal numberequivalent?
- Explain the term masking. How is it useful for data representation? Explain the concept using an example For a floating-point format with a k -bit exponent and an n -bit fraction, give a formula for the smallest positive integer that cannot be represented exactly (because it would require an n + 1 –bit fraction to be exact).Calculate (3.41700875 *10-3 + 6.34005625*10-3)* 1.25625* 102 by hand, assuming each of the values are stored in the 16-bit half precision format describedin in the textbook. Assume 1 guard, 1 round bit, and 1 sticky bit, and round to thenearest even. Show all the steps, and write your answer in both the 16-bit floating point format and in decimal.Given a floating point representation 10110 11101101000 (5-bit exponent and 11-bit significant) if the exponent is in two’s and the significant is in one’s, what are its normalized floating point representation in hexadecimal and its real value in hexadecimal?
- Consider a hypothetical 8 bit floating point machine representation with a sign bit, a 3 bit exponent, and a 4 bit mantissa (se1e2e3b1b2b3b4), where the exponent bias is 3 (add 3 to exponent of number to form machine representation). Recall that actual mantissa has 5 bits, since the leading 1 is not stored on the machine. (a) What is the number ?≈2.718 in this 8-bit format? (b) What is the number that (10100111)2 represents in this 8-bit format? (c) What is the upper bound of the relative error when representing a real number in this 8-bit format?6. In IEEE 32-bit representations, the mantissa of the fraction is said to occupy ______ bits. a. 24 b. 23 c. 20 d. 166. Using IEEE 754 representation for single precision floating point, give the 32-bit binary encoding for the numbers below. Show the sign, exponent, and mantissa (significand).b. 11.2265625

