for a switching network. Calculate the total data times needed when the follow used: (a) Circuit switching; (b) Virtual circuit and datagram packet switching. T hops (1 hon-4km) the signal propagation speed is 2000 km/s and the line can
Q: What are two examples from your application where you utilize menus, and why would you do that…
A: Program: Informally, "instance" and "object" are synonymous since each has a unique value…
Q: Given: Mini-Sudoku 4x4 Assume the following numbers are place in the following cells: C12 = 4 C24 =…
A: Cells are a space on spreadsheet where individual entry of data be entered and formed by the…
Q: talk 3 (three) examples of pc incidents or pc crime that took place inside the healthcare industry…
A: Incidents related to computer security might range from harmless viruses to the unauthorised…
Q: What are the critical considerations when choosing an operating system for an embedded system?
A: The question is to find the critical considerations when choosing an operating system for an…
Q: Define dot?
A: The full form of DOT is Damage over time
Q: What differentiates a gateway from a bridge? Which is quicker, and why
A: Introduction What differentiates a gateway from a bridge? Which is quicker, and why?
Q: 1. In a BST, if the right sub tree is not empty, then the successor is. The maximum in the left sub…
A: answer starts from step 2
Q: Describe the function of the back button and how it relates to the information back stack.
A: Solution:: A back button is a basic control used by a variety of technologies. In a Web browser, a…
Q: The compiled language is more effective because you don't have to spend time performing individual…
A: Compiled terminology Compilers, rather than interpreters, are used to implement compiled languages…
Q: Between just-in-time compilation and dynamic compilation, what is the difference?
A: Between just-in-time compilation and dynamic compilation, what is the difference answer in below…
Q: What may happen if you leave the mouse cursor on a faulty piece of code for a long time?
A: The answer of the question is given below
Q: Name some IDE of java?
A: IDE is defined as an interactive development environment. By the time multiple IDEs are introduce…
Q: A good cryptographic hashing algorithm should produce random outputs; that is, the probability of…
A:
Q: The word "API" refers to a programming interface for applications. What does this mean in terms of…
A: API is a representation of hardware components on the software level, which is generated from a…
Q: Write Programm using oop in c++ Some form of simplified physics simulation, e.g. multiple…
A: Note : The physics simulation done in this question is to find the potential difference across a…
Q: PROBLEM # 2.25 Show via truth table, then with Boolean algebra that AB=AB+ AB. Cite the laws and…
A: The Truth table and simplified boolean expression is given below A ⊕ B is already given in the…
Q: What part of the operating system is responsible for reading and running programs?
A: Let us see the answer below,
Q: Is it possible to synchronize Ada jobs?
A: Synchronization: This concern relates to the collaborative synchronization that is made available…
Q: The blockchain technology definition. Give a blockchain technology example. List at least three…
A: Please find the answer in below step.
Q: Suppose a user employs one-time passwords as above (or, for that matter, reusable passwords), but…
A: Password authentication may be prone to many attacks, such as replay attacks. One of the strategies…
Q: Give a brief explanation of just-in-time compilation.
A: The answer is written in step 2
Q: Suppose you wanted to use a linear search on a sorted data set. What would be the average number of…
A: The typical number of correlations with find a given component would be n/2, where n is the quantity…
Q: What may happen if you leave the mouse cursor on a faulty piece of code for a long time?
A: There are two possibilities that might occur. Condition 1: If your code is written and run by some…
Q: How might you encode audio (or video) data in two packets so that if one packet is lost, then the…
A:
Q: What are the critical considerations when choosing an operating system for an embedded system?
A: The question is to find the critical considerations when choosing an operating system for an…
Q: What are the properties of a heap
A: A heap is a data structure that satisfies the heap property: If A is a heap, then for every node i…
Q: In a stack, items are added and deleted only at one end, referred to as the of the stack.
A: The question has been answered in step2
Q: PLease explain Construct NFAs that recognize the following languages: a) L1 = (b+ba+baa)*…
A:
Q: A software manager is in charge of the development of a safety-critical software system, which is…
A: The answer is written in step 2.
Q: A cybersecurity expert discovers several users with administrative rights during a security review.…
A: The Answer is given below s tep.
Q: compared the processes used in object-oriented and processed-based software development.
A: Object-Oriented software: Object-oriented a programming (OOP) is a programming paradigm that…
Q: Will the following code run? Why or why not? Assume that the blocks of code are correctly formed…
A: Python: Python is a high level, class based object oriented programming language. It supports both…
Q: The compiled language is more effective because you don't have to spend time performing individual…
A: Language that has been compiled: For the purpose of implementing compiled languages (translators…
Q: What distinguishes TCP session hijacking from UPD session hijacking?
A: let's see the correct answer of the question
Q: A software manager is in charge of the development of a safety-critical software system, which is…
A: The COCOMO -11 application model uses object points – an indirect software measure that is computed…
Q: Following the development and testing of individual software modules, they must be combined and…
A: Introduction: Software development refers to computer programming, which is the process of writing…
Q: Cloud computing has the potential to have a wide range of societal ramifications. Can computers and…
A: Cloud computing provides the facilities to store and manage the data on the internet. Many…
Q: Between just-in-time compilation and dynamic compilation, what is the difference?
A: LET US SEE THE ANSWER : Compilation : The C compilation process is also known as the conversion of…
Q: How employees who don't have access to the system may nevertheless directly use it even if they…
A: Introduction The Internet: With the evolution of technology, an increasing number of businesses are…
Q: When it was first created, how big was the computer?
A: Your answer is given below. Introduction :- Due to the multiple ways that computers can be…
Q: What’s the effect of using the NOT operator in a WHERE clause?
A: SQL consists of multiple operators like AND, OR , NOT each serve different purposes. TO have the…
Q: You are an Internet Service Provider; your client hosts connect directly to your routers. You know…
A:
Q: BGiven the data X 1.6 2 2 8 2.5 14 3.2 15 4 8 4.5 2 Calculate (2.8) using Newton's interpolating…
A: ANSWER:-
Q: Can you explain why? Q.1: Identify the Big-O notation for given public void function(int…
A: AS PER GUIDELINE I CANNOT ATTEMPT ALL Question-1 public void function(int arr[], int n) { for…
Q: Gustavo Gus has to remove one of his drug chemists due to trust issues. So he comes up with the idea…
A: Input-Output Details: First line will contain TT, number of testcases. Then the testcases follow.…
Q: Differentiate between the following and include examples of each simple attribute versus composite…
A: - Solving the first three parts as per guidelines. - We are talking about attributes here.
Q: What exactly is the function of a boot bloc
A: Introduction What exactly is the function of a boot block?
Q: Q3) Write a recursive function that reads from the keyboard a set of characters and prints them…
A: The answer for the above question is given in the below steps for your reference
Q: What is a relatonal data model? explain any three objectives of the relational model
A: Disclaimer: “Since you have asked multiple questions, we will solve the first question for you. If…
Q: What does Apache stand for? What is the price? What capabilities does it now possess?
A: Software:- software is a set of instructions to perform specific tasks. You cannot touch this.
dont dont post if u are not 100% sure else strict report
Step by step
Solved in 2 steps

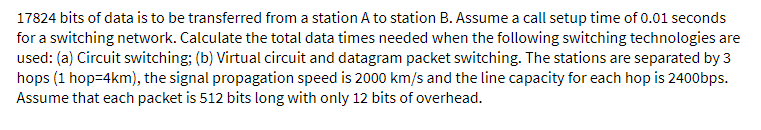
- 17824 bits of data is to be transferred from a station A to station B. Assume a call setup time of 0.01 seconds for a switching network. Calculate the total data times needed when the following switching technology are used: (a) Virtual circuit and datagram packet switching. [The stations are separated by 3 hops (1 hop=4km), the signal propagation speed is 2000 km/s and the line capacity for each hop is 2400bps. Assume that each packet is 512 bits long with only 12 bits of overhead.]17824 bits of data is to be transferred from a station A to station B. Assume a call setup time of 0.01 seconds for a switching network. Calculate the total data times needed when the following switching technologies are used: (a) Circuit switching; (b) Virtual circuit and datagram packet switching. The stations are separated by 3 hops (1 hop=4km), the signal propagation speed is 2000 km/s and the line capacity for each hop is 2400bps. Assume that each packet is 512 bits long with only 12 bits of overhead.17824 bits of data is to be transferred from a station A to station B. Assume a call setup time of 0.01 seconds for a switching network. Calculate the total data times needed when the following switching technologies are used: (i) Circuit switching; (ii) Virtual circuit and datagram packet switching. The stations are separated by 3 hops (1 hop=4km), the signal propagation speed is 2000 km/s and the line capacity for each hop is 2400bps. Assume that each packet is 512 bits long with only 12 bits of overhead.
- Consider two nodes, A and B are attached to opposite ends of an 1200 meter cable with signal propagation speed is 2 x 10^8 m/sec. Frame size used by both nodes is 1500 bits including header and preambles. Assume transmission rate is 100 Mbps and there are four switches between node A and B each insert 20 bit delay as a processing time in addition to store and forward delay. If only A has packet to send, then the time taken to reach A's packet at B is?A frame of 1200 bytes travel through five switches along the path. Each link has a bandwidth of 100 Mbps, a length of 100 m, and a propagation speed of 2 × 10*8 m/sec. Assuming a queuing and processing delay of 2 ms at each switch, what is the approximate end-to-end delay for this packet?Assume a 10Mbps Ethernet has two nodes, A and B, connected by a 360m cable with threerepeaters in between, and they each have one frame of 1,024 bits to send to each other. Further assumethat the signal propagation speed across the cable is 2*10^8 m/sec, CSMA/CD uses back-off intervals ofmultiples of 512 bits, and each repeater will insert a store-and-forward delay equivalent to 20-bittransmission time. At time t=0, both A and B attempt to transmit. After the first collision, A draws K = 0and B draws K = 1 in the exponential back-off protocol after sending the 48bits jam signal. a. What is the one-way propagation delay (including all repeater delays) between A and B inseconds? At what time is A's packet completely delivered at B? b. Now suppose that only A has a packet to send and that the repeaters are replaced with switches.Suppose that each switch has an 8-bit processing delay in addition to a store-and-forward delay.At what time, in seconds, is A's packet delivered at B?
- In the communication in the figureFor Link 1; Bandwidth 150 Mbps Line Length 5 km For Link 2; Bandwidth 50 Mbps Line Length 2000 km For Link 3; Bandwidth 1000 Mbps Line Length 1 km For 4000 bit packet length and the case where fiber optic and light speed of all connections are 3x10^8 m / sec; Question 1. What is the transmission and propagation delays for each line?Question 2. Assuming there are no queue and processing delays, calculate the end-to-end delay in milliseconds.A TCP PDU of length 40,513 octets (including the TCP header) is to be transmitted over a physical link between two nodes at 1,064,218,818 bps using 802.3 with an MTU of 826 octets. Assume a LLC-PDU has an overhead of 4 octets and that the IP-PDU has no options. i) How many bits are sent over the connection from the source to destination assuming only full frames are sent? ii) What is the effective data rate from the TCP-PDU point of view (to nearest integer)? iii) If the propagation time between the two nodes is 5 microseconds what is the line efficiency to 3 decimal places assuming stop and wait is used between the two nodes?Unless specified otherwise, use the free space propagation speed of light 3x108 m/s to calculate the propagation delay. For numerical calculations, the results must show the appropriate unit. Show a complete solution for each problem1. Consider a client-server system with the following parameters and requirements. The client transmits 10x10^6 bits of data every minute to the data server connected directly to it. The transmission link speed is 20x10^6 bps. Each packet is 2,000 bytes long which includes a 20-byte packet header.a. Calculate the number of packets generated per second for data transmission at the client node.b. The system requires every packet must be delivered within 4 ms of generating a data packet. Calculate the maximum link distance between the client and the server that still can meet this requirement. Ignore processing and queuing delays.c. Calculate the number of overhead bits transmitted per second from the client to the server.
- Computer A is sending a 100 kByte long file to Computer B via packet-switching over two consecutive 10 Mbps links of 1000 km length each.Assume that the signal propagation speed on both links is 2.5 x 108 m/s.Furthermore, assume that the maximum length of a packet is 1500 bytes and that Computer A fills each packet to the max, if possible. If transmission starts at time t=0, at which time (in seconds) does the first bit arrive at the switch connecting link 1 and link 2?How would you write a system of linear equations based on the given scenario and directions? Scenario You are employed as a network engineer and have been asked to analyze a communication network to determine the current data rates and ensure that the links aren’t at risk of “reaching capacity.” In the following figure of the network, the sender is transmitting data at a total rate of 100+50 = 150 megabits per second (Mbps). The data is transmitted from the sender to the receiver over a network of five different routers. These routers are labeled A, B, C, D, and E. The connections and data rates between the routers are labeled as x1,x2, x3, x4, and x5 . Directions For this assignment, you will analyze the communication network and solve for the unknown data rates using a variety of techniques. The system can be modeled mathematically as a system of linear equations by writing an equation for each node/router in the network. Each of these equations can be written by noting that the sum…Computer A is sending a 10 MByte long file to Computer B via packet-switching over two consecutive 100 Mbps links of 2000 km length each.Assume that the signal propagation speed on both links is 2 x 108 m/s.Furthermore, assume that the maximum length of a packet is 1480 bytes and that Computer A fills each packet to the max, if possible. If transmission starts at time t=0, at which time (in seconds) does the first bit arrive at the switch connecting link 1 and link 2? (What is the propagation delay for link 1?)

