for thi
Q: What tool or technique do you think is most effective at finding vulnerabilities? Why?
A: The answer is
Q: Write a C++ programme to calculate n!, where n! = n* n-1 * n-2 *... *2 * 1
A: Please find the answer below
Q: Consider a variation of sequential search that scans a list to return the number of **occurrences** ...
A: Second image question is solved below: Sequential search: Best Case: When the searched element is th...
Q: write down pros and cons of skipping grid size SxS.
A: A coordinate measuring machine basically contains three axes and hence the axes can form several gri...
Q: arden Glory is a partnership that provides gardening and yard maintenance services to individuals an...
A:
Q: C# Programming Write a program that generates 10 random integers. Display the number only if it is...
A: #include <stdio.h> #include <stdlib.h> int main() { int i,x; int a[10]; ...
Q: 1. Question: What common software problems can lead to network defects? 2. Question: Explain the im...
A: Below are the answers to both questions. I hope this will meet your requirement.
Q: 1. Create a script file that will calculate the hyperbolic cotangent of a user-supplied value ´x’. U...
A: The answer is given below:-
Q: Computer Science I need a C++ program that will take a list of random integers from a .txt file, sc...
A: The solution to the given problem is below.
Q: 5. Use the priority list T1, T3, T4, T6, T2, TS, T8, T7 schedule the project below with two processo...
A:
Q: Compare mathematical programming versus discrete event simulation approaches to the critical path ho...
A: Question1. Compare mathematical programming versus discrete event simulation approaches to the criti...
Q: Imagine a regression model on a single feature, defined by the function f (x) = wx + b where X, W, a...
A: Ans : option 2 is correct
Q: Consider a two-class case with classes fraudulent and nonfraudulent. A data mining routine has been ...
A: Given: 50 records as fraudulent (30 correctly so) and 950 as nonfraudulent (920 correctly so)
Q: ve num
A: We write the pseudocode and a c++ program for the given problem statement. The explanation of its wo...
Q: What is local storage on a computer and how does it work?
A: The technique of storing digital data on physical storage devices such as solid-state drives (SSDs),...
Q: Why and how are local minima a problem for k-means clustering? How can we address these? Explain in ...
A: answer is
Q: The following table lists the freezing and boiling points of several substances. Substance Freezi...
A: Given The answer is given below.
Q: The first 3D printer was invented by who, and it was in the year 2000.
A: Introduction: Three-dimensional things, such as machine components, may be printed using 3D printers...
Q: a sorted array of n comparable items A, create gn. Your algorithm must create the tree in O(r
A:
Q: Make a list of the many types of use cases.
A: There are three different types of use case formats. Brief - A one-paragraph explanation of the mos...
Q: Give an example of a case in which the complete denial of a service to a user (in which the user rec...
A: Introduction: The computer's denial of service attack (DOS attack) represents a cyber-attack. The ...
Q: So, when a cell in Microsoft Excel is filled with hashtags, what does it mean?
A: The hashtag filled into the cells of Excel sheets seems to be like some error, but it is not the cas...
Q: What is the big-O notation for the worst-case runtime of the code fragment below? for (i = 0; i < N;...
A: Ans :- option c:- O(N)
Q: can you write a shell script for searching a world inside of a text file?
A: Algorithm: Start Read word to search If grep -q $word hello.txt, then print word found else print n...
Q: Problem: Use If, If…Else, and Nested If Statements Using Visual C#, create a program that will allo...
A: PROGRAM EXPLANATION: Create the main class and main method. Ask the user to enter the input code. T...
Q: You are given a Binary Search Tree Program. Uses the Decision Table Test Method to find the Rules, C...
A: Below i have answered:
Q: Separate a file processing system from a database management system.
A: Introduction: A database management system, sometimes known as a DBMS, is a computerized data-keepin...
Q: 2. In Python programming language, write a program to input a string and then add the string "progra...
A: In Python programming language, write a program to input a string and then add the string "programmi...
Q: What does the plural form of computer mouse mean?
A: Introduction: According to most dictionaries, the plural for a computer mouse is "mice" or "mouses,"...
Q: 1. Please create a Conceptual Data Model (using Draw.io), containing entities and their relations...
A: creating a Conceptual Data Model(Using draw.io) , containing entities and their relationships as the...
Q: sum of squares
A: read n,sum i=1 if i<=n sum=sum+(i*i) i=i+1 print sum
Q: How do you set server's virtual root directory
A: A remote virtual directory is a directory that's not contained within the Web site's home directory ...
Q: Give the syntax and sample code of the three (3) DIFFERENT TYPES OF ARGUMENT & TYPES OF VARIABLE in ...
A: Note: As per our guidelines we are supposed to answer only one question. Kindly repost other questio...
Q: Write a full class that represents a Phone, described by a name, price, and then whether the phone c...
A: PROGRAM EXPLANATION: Import the java. util package. Create a phone class. Declare the attributes of...
Q: Given the function F = II(0, 1, 4,6, 7,8,9) + Md(5, 10, 11, 12) %3D
A: Solution above this question:
Q: 1. For the following truth table: A B C DG a. [2] Write the equation for G for the canonical SOP for...
A: Here in this question we have given four variable which gives some output G.and we have asked to fin...
Q: 9. Let M = ({g0:91-92}; {a, b}, ð, qo. {41}) be the NFA given by the state diagram: (a) Construct th...
A:
Q: Is it possible to write yara rules with multiple conditions? Examples please.
A: Yes, It is possible to write YARA rules with multiple condition. The image below is an example Y...
Q: Create a C program using a Two-Dimensional Array that will display values below: Note: 2 rows and ...
A: here in this question we have asked to write a program which input 2D matrix size from user and prin...
Q: True or False. (A—B)(A+B) = A^2 —B^2
A: Equation is legal combination of operators and operands which is followed by equality operator.
Q: JAVA LAB PROGRAMMING Write a Java program to find and display all substrings of a user entered strin...
A: Code: import java.util.Scanner; public class Main{ public static void main(String args[]) { ...
Q: Using public Wi-Fi to conduct business is fraught with hazard
A: Dangers of Public Wi-Fi: A wi-fi connection is a kind of tool that electronic devices use to connec...
Q: b) Convert the following if statement to a single switch statement. Don't forget to employ the defau...
A: Here the switch case variable will be Year. Different switch case will have different possible value...
Q: According to Andy Growe, "Spending more time on planning should pay off in execution" what does this...
A: I agree with the belief of Alpha managers that spending more time on planning should pay off...
Q: What is the size in bits of the tag in the cache?
A: A cache is termed as a type of memory that has the most recent data stored in it. It is used to feas...
Q: Write a C# program to accept two integers and check whether they are equal or not
A: Int his question, we are asked to write a c# program to check whether two integers are equal or not ...
Q: 1. For the following truth table: A B C D [2] Write the equation for G for the canonical SOP form 0....
A: Given The answer is given below
Q: What are some of the characteristics of cloud storage?
A: Cloud storage is a cloud computing approach that stores data on the internet via a cloud computing p...
Q: Which of the following best describes what is a Major Clause? O a. None of the other alternatives. O...
A: Ans : option e is correct
Q: Recently, your company’s WAN experienced a disabling DDoS attack. Which of the following devices c...
A: WAN stands for wide area network and there are attack could be happen in the network , we have choos...
Quick Question for this problem
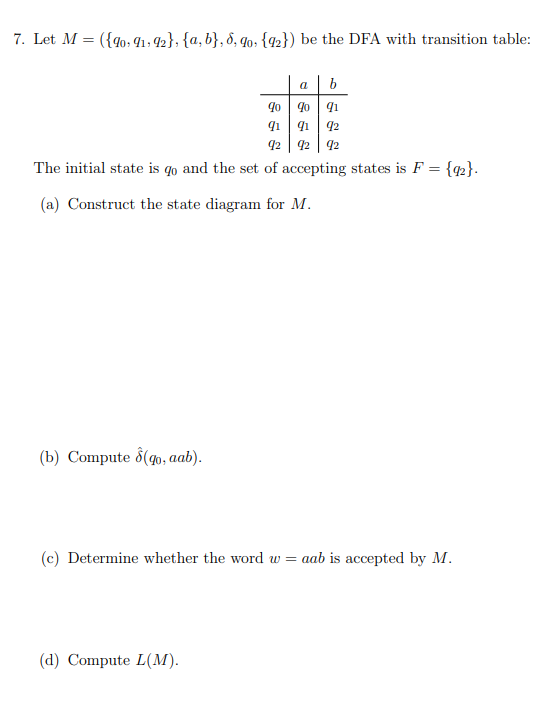
Let Me = ({q0 , q1 , q2 }, {a,b},δ ,q0, { q2 })
Step by step
Solved in 2 steps with 1 images

- 1. Given the state-transition graph (Kripke Structure) below, which of these properties hold?• (AX f1)(s0)• (EG f2)(s2)• A [b1 U f1] (s3)• AG (b1 ⇒ AF f1)• AG (f1 ∨ f2)Correct answer will be upvoted else downvoted. Computer science. in case there are two planes and a molecule is shot with rot age 3 (towards the right), the cycle is as per the following: (here, D(x) alludes to a solitary molecule with rot age x) the primary plane delivers a D(2) to the left and lets D(3) progress forward to the right; the subsequent plane delivers a D(2) to the left and lets D(3) progress forward to the right; the primary plane lets D(2) forge ahead to the left and creates a D(1) to the right; the subsequent plane lets D(1) progress forward to one side (D(1) can't create any duplicates). Altogether, the last multiset S of particles is {D(3),D(2),D(2),D(1)}. (See notes for visual clarification of this experiment.) Gaurang can't adapt up to the intricacy of the present circumstance when the number of planes is excessively huge. Help Gaurang find the size of the multiset S, given n and k. Since the size of the multiset can be extremely huge, you…For the transition probability matrix P = 1 2 3 4 5 1 0.2 0.1 0.15 0 0.55 2 0 1 0 0 0 3 0.35 0.2 0.2 0.1 0.15 4 0 0 0 1 0 5 0.25 0.2 0.15 0.25 0.15 (a) Rewrite P in the canonical form, clearly identifying R and Q. (b) For each state, i, calculate the mean number of times that the process is in a transient state j, given it started in i. (c) For each state i, find the mean number of transitions before the process hits an absorbing state, given that the process starts in a transient state i. (d) For each state i, find the probability of ending in each of the absorbing states.
- Carry out the bisimulation colouring algorithm step-by-step on the labelled transition system defined by thefollowing process definition, and use this to provide an equivalent system with a minimal number of states.X def= a.Y + a.(a.Z + b.W) Z def= a.Z + b.WY def= a.Y + a.Z + b.W W def= a.W how to draw that part: X def= a.Y + a.(a.Z + b.W)Computer Science Which of these statements are true? In a deterministic autonoma, the transition function δ assigns each input symbol to a single state. In a deterministic finite autonoma, the transition relation δ assigns to each pair of a state and input symbol exactly one subsequent state.Matching logic expressions with their truth tables. Question 1 options: a b x 0 0 0 0 1 1 1 0 1 1 1 0 a b x 0 0 1 0 1 1 1 0 1 1 1 0 1. x = a XOR b 2. x = a NAND b 3. x = a NOR b Order the precedence from high to low for following Boolean operators. Question 10 options: OR AND complement Please map commutative, associative, and distributive laws of Boolean algebra theorems with corresponding equations. Question 7 options: (x + y) + z = x + (y + z) (xy)z = x(yz) x+y = y + x xy = yx x + (y · z) = (x + y) · (x + z)x · (y + z) = (x · y) + (x · z) 1. Commutative Law 2. Associative Law 3. Distributive Law
- Create an SVM to calculate the XOR function. Use the values +1 / -1 for inputs and outputs. Map the input [x1,x2] to the space with coordinates [x1,x2x1]. Draw the four possible points of the training set and their maximum linear separator in this space. What is its edge?provide equations for A∗ and B∗(give the unsimplified SoPversion for your answer, simplify for yourself as needed), construct a state table, and complete thetiming trace until no state information remains.Please explain all steps: What Boolean equation is represented by the following K-Maps: a) ~y~z ~yz yz y~z ~x 1 1 1 x 1 1 1 1 b) ~y~z ~yz yz y~z ~w~x 1 1 ~wx 1 1 wx 1 w~x 1 1 c) ~y~z ~yz yz y~z ~w~x 1 1 1 1 ~wx 1 1 wx 1 1 1 1 w~x 1 1 d) ~y~z ~yz yz y~z ~w~x 1 1 ~wx 1 1 1 wx 1 1 w~x 1 1 1
- Computer Science You are told that state machine A has one input x, and one output y, both with type {1, 2}, and that it has states {a, b, c, d}. You are told nothing further. Do you have enough information to construct a state machine B that simulates A? If so, give such a state machine, and the simulation relation.Construct an ε-NFA using 10 states, three of which are final states and at least two are ε -transitions. Now, use the subset construction algorithm to convert this ε-NFA to its equivalent DFA.Given the formal definition of the finite state machine (FSM):M1= { {A, B}, {0,1}, { ((A,0),A), ((A,1),B), ((B,0),B), ((B,0),A) } , A, {B} }· Convert M1 from a non-deterministic FSM into a deterministic FSM.· Draw them both (non-deterministic and deterministic FSMs in STD) and write the State Transition Table and the formal definition of the deterministic FSM.

