For this homework you'll write your first function, a reusable piece of code that allows us to build more complex computer programs. We're going to start simple. Declare and implement a function called addOne. Your function should accept a single int argument and return the result of adding one to its argument. You have until 11:59PM Central Time on 2021-02-07 to complete this problem. WORKING PREVIOUS 1 int called; 2 function addOne = 1+1; 3 public int addOne (int i) 4 called++; return i+1; Question.java:2: error: cannot find symbol function addone = i+1; symbol: class function location: class Question 1 error
For this homework you'll write your first function, a reusable piece of code that allows us to build more complex computer programs. We're going to start simple. Declare and implement a function called addOne. Your function should accept a single int argument and return the result of adding one to its argument. You have until 11:59PM Central Time on 2021-02-07 to complete this problem. WORKING PREVIOUS 1 int called; 2 function addOne = 1+1; 3 public int addOne (int i) 4 called++; return i+1; Question.java:2: error: cannot find symbol function addone = i+1; symbol: class function location: class Question 1 error
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter6: Modularity Using Functions
Section6.1: Function And Parameter Declarations
Problem 3E
Related questions
Question
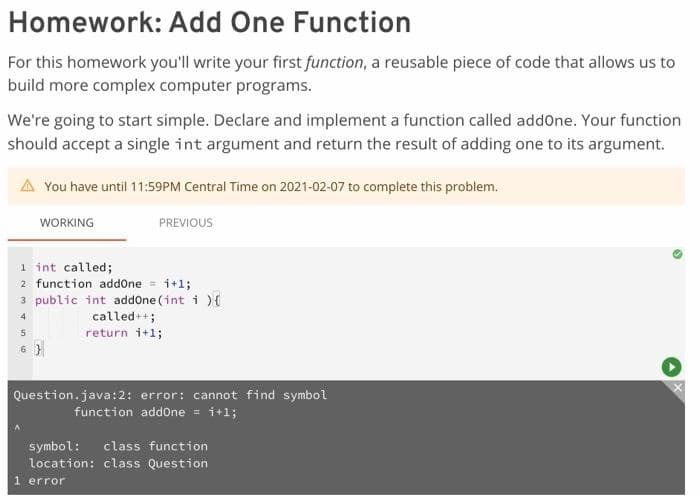
Transcribed Image Text:Homework: Add One Function
For this homework you'll write your first function, a reusable piece of code that allows us to
build more complex computer programs.
We're going to start simple. Declare and implement a function called addOne. Your function
should accept a single int argument and return the result of adding one to its argument.
A You have until 11:59PM Central Time on 2021-02-07 to complete this problem.
WORKING
PREVIOUS
1 int called;
2 function addOne = 1+1;
3 public int addOne (int i) {
4
called++;
return i+1;
5
6}
Question.java:2: error: cannot find symbol
function addone = i+1;
symbol: class function
location: class Question
1 error
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr