Give the truth value of each of these statements where the domain consists of all real
Q: What are the drawbacks to employing global information systems?
A: - We need to know about the drawbacks to employ global information systems.
Q: def no_dups(s: str) -> str: ''' Return a new version of s, but with each sequence of repeated charac...
A: def no_dups(a): b="" for i in a: if i not in b: b=b+i return bprint(no_du...
Q: Q. Big data is explained with 3Vs: Volume, Velocity, and Variety. answer choices True False
A: Answer-True
Q: The functions that can be used in an elements classList() function are:
A: The answer is given in the below step
Q: Q3.Answer the following : a.convert hexadecimal number (fle516) to binary number. b.convert decimal ...
A: 3. a. Given hexadecimal number (f0e5)16 Hexadecimal to Binary: Hex Binary 0 0000 1 0001 2 0...
Q: List and explain the functions of the ten application framework components that are part of the Andr...
A: answer is
Q: en the following in 32-bit single-precision Floating-point number representation (IEEE-754) in norma...
A: Lets see the solution.
Q: 1 bit is equal to * O 6 byte 10 patterns O 8 bytes All choices are incorrect O 2 patterns The CPU pr...
A: The solution to the given problem is below. ***Note: According to Bartleby policy we are not all...
Q: What do you mean by manipulators?Explain different manipulators available in C++.
A: What are manipulators and where we use it? Manipulators are operators used in C++ for formatting out...
Q: What difficulties and issues arise as a result of the use of non-integrated information systems?
A: Introduction: Non-integrated information systems are those that are not linked to one another or hav...
Q: Write a code to change the color of label text every 5 second randomly * Your answer (RND*100)= * Yo...
A: The codes have been provided in visual basic.net
Q: Given: Language L3 = {w e {a,b}* | w starts in ab and ends in bb} Construct the DFA representing the...
A: Given language is L={w ∈ {a,b}*| w starts in ab and ends in bb} The set of strings that satisfy the ...
Q: Answer the following questions: 1. What are the Ten Commandments of Computer Ethics?
A: (Note: According to given guideline, we are supposed to answer only one question, Please repost othe...
Q: What is the major distinction between key-value and document stores?
A: Introduction: There are 4 types of NoSQL databases: 1. Document database2. Key-value stores3. Colum...
Q: ata in A
A: Assembly language Assembly Language is a low-level programming language. It facilitates the convers...
Q: fellowing 12+L÷3+4+(10+9)3 1. covert expression into Postfix expresian
A: We must first know how many types of expressions are there and how to evaluate infix to postfix exp...
Q: "The internet is a computer network that connects billions of computing devices all around the world...
A: Introduction: Individuals and businesses can connect to the Internet through computer terminals, com...
Q: Part 1 Write a program to read in two consumer price indexes and print out the inflation rate. ...
A: PROGRAM INTRODUCTION: Include the required header files. Declare the prototype of the function. Sta...
Q: Find the missing heuristics to ensure it is consistent given the following question. You can provide...
A: X Y A >=3 <=8 E >=4 <=6 D >=3 <=8 ...
Q: Why is the transport layer installed in the end system?
A: The answer is given in the below step
Q: Create the VLAN an as show below: a- Create a four VLAN’s VLAN-10 as CS VLAN-20 as IS VLAN-99 as A...
A: Here, I have to provide a solution to the above question.
Q: loop: and $t0, $s3, $s2 ori $t0, $t0, Ox1234 Iw $t1, 24($s0) sub $t3, $t1, $s1 slti $t9, $t3, 234 bn...
A: 2. loop: and $t0,$s3,$s2 $t0 = $s3 & $s2 R type InstructionInstruction format of R-type instruct...
Q: Create a C program that accepts the inputs hours and minutes and calculates the total number of minu...
A: Code is given below :
Q: 3. Change the following IPV4 addresses from binary notation to dotted decimal notation. [ a. 1000001...
A: We have 2 IPv4 addresses given in binary notation. We need to convert these addresses from binary to...
Q: How to write C++ program using array 1D size: 4 with output: Press r to generate 4 random numbers be...
A: The solution to the given problem is below.
Q: (Integers Added Together) Create a program that employs the for statement to sum a succession of int...
A: PROGRAM INTRODUCTION: Include the required header files. Start the definition of the main function....
Q: Create a software that prompts the user to enter a numerical value. The number and a message indicat...
A: Create a software that prompts the user to enter a numerical value. The number and a message indic...
Q: What are the parts of a computer that allow it to function?
A: Introduction: A computer system is made up of a number of hardware devices that, with the aid of sof...
Q: In order for a TryParse method to work,
A: we have three choices : Parse, Convert, and TryParse. My idea is use which have three choices : Par...
Q: at Is SDLC?
A: SDLC stands or means for "Software Development Life Cycle". It is a methodology or process adopte...
Q: hat are the dangers of building a security infrastructure that is available to everyone?
A: Answer: With all of the buzz about cloud adoption, it's tempting to believe that on-premises IT infr...
Q: (c) Convert the following denary numbers to 8 bit binary numbers and evaluate using the '2's' comple...
A: I'm providing the answer to above question. I hope this will be helpful for you....
Q: Construct a PDA that matches all strings in the language over {x,y} such that each string has at lea...
A:
Q: Describe the Web analytics maturity model, as well as some of its applications.
A: Introduction: In any organization, business analysis is a necessary role. The most well-known arrang...
Q: Define and explain the limitations of serial processing in the first generation of operating system
A: Actually, processor is used to processing the data.
Q: A. Once you click on Submit, Using javascript you will print a message: Thank you "first name" "last...
A: Given: A We need to Write the code of this HTML document with javascript code. that , Once you clic...
Q: vhat is the difference between network architecture and application architecture
A: Application Layer: In the Open Systems Interconnection (OSI) model and Transfer Control Protocol (TC...
Q: Is it possible to define object-oriented programming analysis and design?
A: Introduction: It is a software engineering technique that represents a system as a collection of int...
Q: Invent a program that will determine whether or not a given number is a Perfect Number. An Example ...
A: PROGRAM INTRODUCTION: Include the required header files. Start the definition of the function to ch...
Q: wavelength monopole antenna for a dual-band Wi-Fi networking system. Explain in detail your step-by-...
A: Characteristics of Half wave dipole Antenna are: The frequency of its operation is half of its wav...
Q: What is the job of the database administrator (DBA) in a NoSQL database?
A: INTRODUCTION: DBA: Database Administrator is the abbreviation for Data Base Administrator. DBA can ...
Q: 4. Use the encoding formula: y =x+12 (mod 26). a. Encode CF S. b. Find the decoding formula and deco...
A: Here we have given encoded format for CFS and have given decoding formula to decode YHC
Q: Create a software that accepts 10 digits from the user and displays the number that is the smallest ...
A: Note: The needed software is written in the C++ programming language.
Q: Discuss the benefits and drawbacks of High Performance Computing systems in terms of
A: High Performance Computing (HPC) High performance computing is just the computing which happens by t...
Q: open source in computer science?
A: What is open source? It can be a software or a platform that is accessible to anyone and it also all...
Q: Describe a cloud storage application and how it varies from a traditional client storage software in...
A: Introduction: Under the cloud computing architecture known as cloud storage, an Internet service pro...
Q: Issue a single Linux command to display all lines of text in the file ~/text.txt that begins with a ...
A: Introduction: Linux Command: The grep command stands for “global regular expression print”, and it i...
Q: You're looking for software to help you with the interior design of your house. The packaging for th...
A: Intro the above question is about You're looking for software to help you with the interior design...
Q: The kth quantiles of an n-element set are the k divide the sorted set into k equal sized sets (to wi...
A: Here is the detailed explanation of the solution
Q: Is it possible to write a brief message on the UNIX system? Identify and explain six UNIX-based util...
A: Introduction: UNIX is an operating system created in the 1960s and has been under continuous develop...
Give the truth value of each of these statements where the domain consists of all real
numbers.
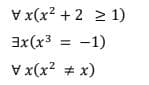
Step by step
Solved in 2 steps

- Computer Science In Python: You have exchange rates from one currency to another USD -> BTC [some value]. Use a list of exchange rates for currencies and determine the greatest value you could get. Find all paths from Start currency -> End currency. Maintain the max and then after explored all paths from start -> finish. Return the max exchange(python) There are 100 light bulbs lined up in a row in a long room. Each bulb has its own switch and is currently switched off. There are 100 people lined up outside the entry door. Each bulb is numbered consecutively from 1 to 100 and so is each person.Person No. 1 enters the room, switches on every bulb, and exits. Person No. 2 enters and flips the switch on every second bulb (turning off bulbs 2, 4, 6...). Person No. 3 enters and flips the switch on every third bulb (changing the state on bulbs 3, 6, 9...). This continues until all 100 people have passed through the room.What is the final state of bulb No. 64? Output the state of bulb 64 and all of the bulbs that are turned on at the end (Bulb #).(IN C LANGUAGE) Cumulative Addition: Computer selects a number between 7 and 23 at random. User will only add 2, 3 or 5 numbers to reach that number.For example: To reach 14: User will enter 5 5 2 2 (4 input).Also he can enter 2 2 2 2 2 2 2 (7 input) or 3 3 3 3 2 (5 input). https://www.bartleby.com/questions-and-answers/in-c-language-cumulative-addition-computer-selects-a-number-between-7-and-23-at-random.-user-will-on/0509c740-d993-44ed-a468-7e02da552600
- Create a program in python which perform instruction as given below: you need to create a network of variable devices, wirelessly connected with each other. You need to simulate a network just like real-time network,where each node (device) is connected to its neighbors based on its transmission range. Network Deployment: 1. Create 50 nodes randomly in a square region of 100x100 m? deployment region. Hint: (You can create two arrays of dimensions 1×50 representing coordinates and coordinates of the nodes with values less than 100.) 2. Calculate the distance matrix, containing distance among the nodes. 3. For each node, create a neighbor list containing the identity of neighbors that lies within the transmission range (TR) of that node. 4. Create connection matrix, saving the information about the connections within the network. Route Establishment (Figure 2): 1. Establish the shortest distance route from source (S) to destination (D). 2. The identity of source and destination will…int xy=3;if (xy==2) xy=0;else if (xy==3); xy++;else xy=xy+2;What is the value of xy? Select one: a. invalid b. 2 c. 4 d. 0 It is the first company where the drag and drop programming interface was developed. Select one: a. Oracle Corporaion b. Tripod c. IBM d. MIcrosoftin spike prime using python help me fix this spin algoirthm it is supposed to spin in a circle and get bigger per spin until it is a certain distance away from the wall then the distance sensor tells it to stop. this is the code i have now but it does not work from spike import MotorPair, DistannceSensor, PrimeHub from spike.control import Timer, wait_for_seconds motor_paid = MotorPair('C','D') distance_sensor = DistanceSensor('F') def search1 while true" distance_sensor.wait_for_distance_farther_than(5,'in', short_range = False) motor_pair.move(1000, unit='in', steering= -30, speed = 30) motor_pair.stop() motor_pair.move(10, unit = 'in', steering =-100, speed= 70) motor_pair.stop()
- Using JAVA code: Please make a graphical interface that will convert infix to postfix expression. Please show also the process of the conversion (line by line).Code in C language. Follow instructions in photo. Use text provided as input.txt file. A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 B1, B2 19831 Henshaw St Culver City, CA 94023 C1, C2 5142 Dumont Pl Azusa, CA 91112 D1, D2 20636 De Forest St Woodland Hills, CA 91364 A1, A2 20294 Lorenzana Dr Woodland Hills, CA 91364 E1, E2 4851 Poe Ave Woodland Hills, CA 91364 F1, F2 20225 Lorenzana Dr Los Angeles, CA 91111 G1, G2 20253 Lorenzana Dr Los Angeles, CA 90005 H1, H2 5241 Del Moreno Dr Los Angeles, CA 91110 I1, I2 5332 Felice Pl Stevenson Ranch, CA 94135 J1, J2 5135 Quakertown Ave Thousand Oaks, CA 91362 K1, K2 720 Eucalyptus Ave 105 Inglewood, CA 89030 L1, L2 5021 Dumont Pl Woodland Hills, CA 91364 M1, M2 4819 Quedo Pl Westlake Village, CA 91362 I1, I2 5332 Felice Pl Stevenson Ranch, CA 94135 I1, I2 5332 Felice Pl Stevenson Ranch, CA 94135 N1, N2 20044 Wells Dr Beverly Hills, CA 90210 O1, O2 7659 Mckinley Ave Los Angeles, CA 90001python programming text files student.txt = P21013088,Kylie Tan Zen Dong,CSC1101 86,CSC1102 75P21013177,Tan Soo Hong,CSC1101 76,CSC1103 76,CSC1104 92,CSC1105 88P21013200,Peh Jia Xuan,CSC1101 88,CSC1102 80,CSC1103 90,CSC1106 75 subjects.txt = CSC1101,Computer FundamentalCSC1102,Computer ArchitectureCSC1103,Fundamentals of DatabasesCSC1104,NetworkingCSC1105,Programming with PythonCSC1106,Design ThinkingCSC1107,Human Computer InteractionCSC1108,Programming with R CSC1109,Systems Analysis and Design CSC1110,Machine LearningCSC1111,Data Structure and AlgorithmsCSC1112,Big Data ArchitectureCSC1113,Fundamentals of Data Science
- C programming: Fill Out the TODO'S IN THE PROGRAM : #include <stdlib.h> // EXIT_ codes#include <stdbool.h> // bool#include <stdio.h> // printf, scanf#include <string.h> // strlen, strcmp#include "udp.h" // udp library#define CLIENT_LISTENER_PORT 4097#define SERVER_LISTENER_PORT 4098#define MAX_CHARS_PER_MESSAGE 80//-----------------------------------------------------------------------------// Main//-----------------------------------------------------------------------------int main(int argc, char* argv[]){char *remoteIp;char *mode;int remotePort;char str[MAX_CHARS_PER_MESSAGE+1];bool quit = false;bool sendMode;// Verify arguments are goodbool goodArguments = (argc == 3);if (goodArguments){remoteIp = argv[1];mode = argv[2];goodArguments = (strcmp(mode, "server") == 0) || (strcmp(mode, "client") ==0);}if (!goodArguments){printf("usage: chat IPV4_ADDRESS MODE\n");printf(" where:\n");printf(" IPV4_ADDRESS is address of the remote machine\n");printf(" MODE is…Write in assembly language LC3 LC3 simulator to use: https://wchargin.com/lc3web/ Write a program that implements a while loopa. Loop while(R0 > -10)b. For every iteration of the loop subtract 2 from R0c. R0 should start at 0 Use LC3 simulator : https://wchargin.com/lc3web/ Psuedo code: .ORIG x3000 ; NOTE: it says to use R0 for the result; instead, use R3 so the result does not get overwritten when HALT command executes. ; Initialize R3 with #0 ; Set R1 to #10 LOOP ; Decrease R3 by #2 ; Add R1 and R3 and store into R2 ; Branch if positive back to top of loop (we have reached our end condition) DONE ; HALT CPU .END











