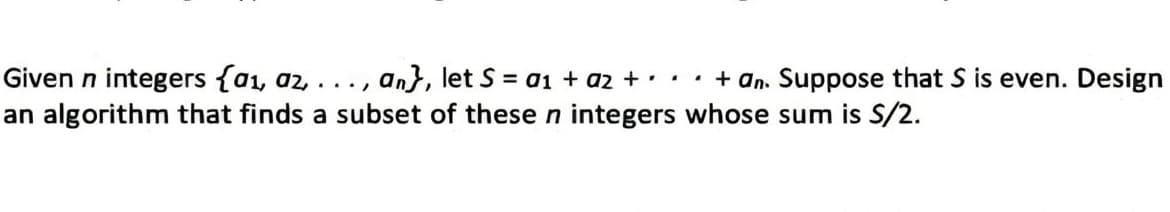
Given n integers {a₁, az, ..., an}, let S = a₁ + a2 + + an. Suppose that S is even. Design an algorithm that finds a subset of these n integers whose sum is S/2.
Q: Why do different OSes place disk folders in different locations on the hard drive's tracks? Please…
A: Different operating systems (OS) place disk folders in different locations on hard drive tracks for…
Q: How can I most effectively gather information using the video recording capabilities of my smart…
A: Smart phone data may be exchanged or transmitted through MMS, Bluetooth, USSD, the internet, and…
Q: What are the upsides and downsides of cloud storage? Include some references to cloud-based service…
A: The storing and use of data and computer resources through the Internet is referred to as cloud…
Q: Lab - Research Password Recovery Procedures Objectives Part 1: Research the Configuration Register…
A: Step 1: The configuration register is a register in a computer system that stores a variety of…
Q: Detail the idea of holographic storage for me.
A: A system known as holographic storage use holograms to store data. Three-dimensional images known as…
Q: Can the BGP router always choose the shortest, loop-free ASpath? Justify your choice by giving…
A: Border Gateway Protocol (BGP): BGP is an Inter-AS routing protocol that gets subnet reachability…
Q: Search for computers that have Linux preinstalled from manufacturers. Is there an OS choice (or…
A: Yes, there are several manufacturers that offer Linux preinstalled on their computers, and some even…
Q: From vendors table, write a query to retrieve records as follows: On the first column, add vendor…
A: The query in step 2 uses the CONCAT function to concatenate the first and last names of the vendor…
Q: Where can I get up-to-date details about IT, IT systems, and IT infrastructure?
A: Introduction: T stands for Information Technology, which encompasses all forms of technology used to…
Q: Please provide some specific instances of the various criminal activities in which Phantom and…
A: Phantom and Filthy appear to be fictitious characters; as a result, I'll present a range of…
Q: (a) Assume there is an adjacency matrix A of an undirected graph G. Further assume a 1 is indicated…
A: - We need to talk about matrix and adjacency list representation for the graph mentioned.
Q: A "peak" is an entry in an integer array that is bigger than or equal to the adjacent integers,…
A: ALGORITHM:- Define a constant variable MAX_INT with the value 1 shifted left by 32. Define a…
Q: Can the BGP router always choose the shortest, loop-free ASpath? Justify your choice by givin
A: AS-PATH-based BGP route selection: The following are the criteria for the BGP router to choose a…
Q: a) Write down the adjacency matrix and adjacency lists specifying this graph. Assume that the rows,…
A: Graph Theory is the study of mathematical structures called graphs, which consist of a set of…
Q: I need help to write a c program code for the following questions Determine the following averages…
A: C program, sample inputs in the file and output are in the below steps.
Q: To be fully defined, a variable must have both its type and its extra characteristics set (and…
A: Introduction: The concept of a variable's scope allows for more precise characterisation of those…
Q: We'd like to provide some suggestions to chief information officers (CIOs) who are thinking about…
A: The move to cloud-based data storage has become increasingly popular over the last decade. This…
Q: Is there anything that can be done to the network infrastructure to ensure that it remains…
A: A program that can copy itself and spread from one machine to another is referred to as a virus on a…
Q: + explain code.
A: Solution: Given , 8 % (3*4) + 8 / 3 - 9 = 1 In general Mathematics this can be solves by using…
Q: Apart of process management, what do you believe are an operating system's other two most important…
A: While operating systems have numerous roles, apart from process management, I believe the other two…
Q: Please include at least five real-world examples demonstrating how augmented reality has been or…
A: AR is a tech economy engine. The AR market may hit $100 billion by 2020. AR apps, devices, and smart…
Q: Tell me the difference between Scenario and Use Case and Test Case? Or difference between Scenario…
A: Introduction: Both scenarios and use cases are general representations of a system's operation. A…
Q: What, precisely, are strings, if you may ask?
A: Programming makes use of many different data types, including integers and floating point units, but…
Q: Is there a method your company uses to identify potential security flaws in its network before they…
A: Network Security threats which exactly means that the threat to your network and data systems. Any…
Q: Where do IT, ITS, and other related fields stand in terms of cutting-edge technological…
A: IT (Information Technology), ITS (Intelligent Transportation Systems), and related fields are…
Q: Mr. sk is just starting started in the salesforce ecosystem and is now enrolled in LWC workshops to…
A: Lightning web components read Salesforce data using dynamic wire services. @wire specifies an Apex…
Q: Create an iterative technique for reverse-engineering a string. Explain why you would not typically…
A: Iterative technique for reverse-engineering a string is to use a loop to traverse the string…
Q: What suggestions do you have for the company's long-term data storage needs?
A: Given: With regard to the storing of private information in long-term data storage devices, what…
Q: The firewall shields your computer from any outside attacks. It's important to stick to certain…
A: A firewall acts as a network's guardian by stopping illegal users from accessing or exiting the…
Q: How should copies of user information be kept? Your answer has to be practical, quick, and well…
A: Answer the above question are as follows
Q: Can you explain with Python and in simple graphs with question number labled
A: Algorithm: 1. Define the graph as a dictionary of lists.2. Define a function to compute the…
Q: a complete program in MIPS assembly language
A: Given :- In the above given question, the statement is mention in the above given question Need to…
Q: What makes Cloud Firestore distinct from Firebase Realtime Database?
A: Background:- In the market for mobile data storage, Fire store is a novel database that is part of…
Q: How would a virus spread across an organization's network, and what may it be looking for while it…
A: Computer bugs are a serious security concern that can spread quickly through a network. A type of…
Q: In this screenshot, a Windows 10 user is using the File Explorer to move a file from the C:data…
A: Windows supports FAT32 and NTFS file systems. To manage access to folders and files, NTFS allows…
Q: While assessing cloud computing, keep in mind the following four (4) criteria. Dependable…
A: INTRODUCTION: Cloud computing: Computing in the cloud refers to the on-demand availability of…
Q: DRAW a PDA that recognizes the language of palindromes over Σ = {a,b} of odd length.
A: Here is the code for a PDA that recognizes the language of palindromes over {a,b} of odd length.…
Q: explain why a life cycle approach is beneficial?
A: A life cycle approach is a holistic way of looking at the entire life cycle of a product, process,…
Q: (a) Describe the structure of a complete binary tree of heighth with maximum number of nod- Derive…
A: (a) The structure of a complete binary tree of height h with maximum number of nodes is as follows:…
Q: Provide examples of two distinct types of problems that simulation models might be utilized to…
A: Simulation models are utilized to show complex frameworks and circumstances where leading tests or…
Q: ciative if you could suggest TWO differ
A: Introduction: Duplicate data, unstructured data, missing data, incompatible data formats, or trouble…
Q: Can you explain the distinction between hardware and software interruptions and provide some…
A: Hardware interruptions: The microcontroller's physical signals or an external GPIO set as an…
Q: Given the pair of statements: A →~Z and Z=[Av (A•~Z)] 20. Construct a complete (ordinary) truth…
A: Given the pair of statements: A →~Z and Z=[Av (A•~Z)]
Q: In C# code: Write a program that will help an elementary school student learn multiplication. Use a…
A: I have provided ANSWER FOR FIRST QUESTION ONLY------ For first question, I have provided C# CODE…
Q: Where can I learn about the most recent advancements in IT, SIS, and IT infrastructure?
A: Introduction:Technology is constantly changing and evolving, and it is important for organizations…
Q: How can I prevent hackers from accessing my information online?
A: To protect your information online and prevent hackers from accessing it, follow these best…
Q: B Write the Boolean expression: 000 001 010 01 1 1 00 101 1 1 0 1 1 1
A: Answer to the given question: A boolean expression is an expression in programming or logic that…
Q: Give two similarities and four differences between Waterfall and Agile methods. NOTE: • Read,…
A: According to the information given:- We have to define two similarities and four differences between…
Q: Consider the Boolean function
A: Given :- In the above given question, the statement is mention in the above given question Need to…
Q: Black box testing is often used to test which of the following aspects of the software?
A: Black box testing can be used to test the following aspects of the software: Functionality…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- A finite sequence of symbols from a given alphabet will be called a string over the alphabet. A string that consists of a sequence a1, a2, a3, a4, … … … … , an of symbols will be denoted by the juxtaposition a1 a2 a3 a4 … … … … an. Given the strings: u = a2bab2and v = bab2, Evaluate the following operations for strings: (i) ԑu(ii) u + v(iii) u(u| v)(iv) v | (v | u)You are given nn points in the plane: (x1,y1),(x2,y2),...,(xn,yn). On the page , in English, give an algorithm that determines if there is a circle on which all of the points lie. In English, write your algorithm to determine if there is a circle on which points(x_1, y_1), (x_2, y_2), . . ., (x_n, y_n) lie. Algorithm:If your first name starts with a letter from A-J inclusively: Perform an experimental analysis of the two algorithms prefixAverage1 and prefixAverage2, from lesson examples. Optionally, visualize their running times as a function of the input size with a log-log chart. Use either Java or Python graphical capabilities for visualization. Hint: Choose representative values of the input size n, similar to StringExperiment.java from class examples. class PrefixAverage { /** Returns an array a such that, for all j, a[j] equals * the average of x[0], ..., x[j]. * A[j] = (X[0] + X[1] + … + X[j])/(j+1) * * ******************************************************/ // inner loop size will be 1, 2, 3, ..., n (based on j=0,1,2,...,n-1) // we know that 1+2+3+...+ n-1+n = n(n+1)/2 // so, the running time os O(n^2) public static double[] prefixAverage1(double[] x) { int n = x.length; double[] a = new double[n]; // filled with zeros by default for (int j=0; j < n; j++)…
- The Fibonacci series is an infinite sequence of natural numbers, starting from 0 and 1, from which the terms are generated from the sum of the previous sequence elements. a0=0, a1=1, a2=a0+a1, ... , an+1=an+an-1 Implement an algorithm in Java that get n from console and that print the first n terms of the Fibonacci series.Consider the following problem: given a list of integers N and an individual integer n, is there any element of N that is a factor of n? (2) There is a decision procedure for the problem. If your answer is true, try to describe the procedure in English or pseudocode for learning purposes. Group of answer choices True FalseThere is a cube and an ant is performing a random walk on its vertices,every step it will start from one vertex and walk to another along the connected edge, it willrandomly select any of the 3 adjoining vertices with equal probability. If it starts at one vertex,what is the expected number of steps it needs to reach the diagonally opposite vertex? Write a c++ program for the same
- Write an algorithm that inputs a number n followed by an array of n numbers and outputs the number of values of i, with i between 1 and n-1 such that ai < ai +1. {i| i is a natural number and 1 <= i <= n-1 and ai < ai +1} *The output is the cardinality of the set Can be written in pseudocodeJava Programming Consider a set of n intervals I1,...,In, each given as an integer tuple (si,fi) with si<fi, such that the ith interval starts at si and ends at fi. We want to determine the maximum number of nonoverlapping intervals. More formally, we want to determine the size of a largest subset S⊆{1,...,n} such that for i, j∈S, with i≠j we have fj≤si or fi≤sj. Note that the intervals [1,2] and [2,3] are not considered to be overlapping. Input The first line of input consists of an integer n∈{1,...,105}, the number of intervals. Each of the following n lines consists of two space-separated integers ss and ff, indicating an interval starting at s and ending at f, with 0≤s<f≤109. requirements: CPU Time limit: 4 seconds Memory limit: 1024 MB Output Output a single integer, the largest number of nonoverlapping intervals.Computer Science There is an n × n grid of squares. Each square is either special, or has a positive integer costassigned to it. No square on the border of the grid is special.A set of squares S is said to be good if it does not contain any special squares and, starting fromany special square, you cannot reach a square on the border of the grid by performing up, down,left and right moves without entering a cell belonging to S. 5 3 4 9 4 X 3 6 1 9 X 4 1 2 3 5 - Design an algorithm which receives an arbitrary n × n grid, runs in time poly-nomial in n and determines a good set of squares with minimum total cost.
- Pseudo-random numbers Randomly generating numbers is a crucial subroutine of many algorithms in computer sci- ence. Because computers execute deterministic code, it is not possible (without external influence) to generate truly random numbers. Hence, computers actually generate psuedo- random numbers. The linear congruential method is a simple method for generating pseudo-random numbers. Let m be a positive integer and a be an integer 2 < a <m, and c be an integer 0 ≤ c<m. A linear congruential method uses the following recurrence relation to define a sequence of pseudo-random numbers: In+1=a+c mod m (a) Use the linear congruence method with a = 8, c=5, and m = 14, to compute the first 15 pseudo-random numbers when co= 1. That is, compute zo,X1, X 14- (b) From part (a) we should notice that, with m = 14, the sequence does not contain all 14 numbers in the set Z14. In particular because the sequence is periodic. Using m = 8, determine the value of a which does give all 8…Consider the following problem: given a list of integers N and an individual integer n, is there any element of N that is a factor of n? (1) There is a semi-decision procedure for the problem. If your answer is true, try to describe the procedure in English or pseudocode for learning purposes. Group of answer choices True FalseLet's consider a long, quiet country road with houses scattered very sparsely along it. (Picture the road as a long line segment with an eastern endpoint and a western endpoint.) Further let’s suppose that despite the bucolic setting, the residents of all these houses are avid cell phone users. You want to place cell phone base stations at certain points along the road, so that every house is within four miles of one of the base stations. Give an efficient algorithm that achieves this goal using as few base stations as possible. Prove its correctness and explain its time complexity.











