Given the expression below, build the equivalent digital circuit NAND implementation. X - AB + CB + ADc + BCD Supply the input combinations to the circuit and test for the output. Tabulate the result in the table provided.
Q: It's important to know what interrupt latency is, and how the two are related.
A: In computing, interrupt latency refers to the time interval between when an interrupt is produced…
Q: Choose an information system and explain the differences between the functional and non-functional…
A: The functional and non-functional : Functional testing includes API testing, system testing, and…
Q: Discuss the many types of protocols and why they are necessary. (Information technology)
A: Network Protocol: An Overview There are billions of individuals, millions of apps, millions of…
Q: Give a program that benefits health and rescue workers.
A: In employee wellness programs, employers seek to improve employee health and also help individual…
Q: What is the Internet of Things (loT) and how doest work? How might that be possible? How does this…
A: Given: THE INTERNET OF THINGS - The Internet of Things is a network made up of physical objects or…
Q: MULTIMEDIA NETWORKING
A: Create a working directory called tictoc, and cd to this directory. 2. Describe your example network…
Q: What is the most ideal situation for online data entry?
A: Data entry entails entering information from multiple sources into the company's computer system for…
Q: Write an application that allows a user to input customer records (ID number, first & last name,…
A: public class Customer { int idNumber; String firstName; String lastName; double balance;…
Q: Discuss the many types of protocols and why they are necessary. (Information technology)
A: Find the type of protocols below Transmission Control Protocol (TCP): TCP is a popular communication…
Q: If a TLB miss is identified and reported, list and briefly explain the steps that a computer or…
A: Introduction: In the operating system, paging is a mechanism for non-contiguous memory allocation.…
Q: Examine the various sorts of protocols and why they are required in today's world. (Information and…
A: answer is
Q: Is it conceivable to use a peer-to-peer (P2P) solution instead of an FTP server to send huge files…
A: answer is
Q: What methods can be used to deal with massive data sets, which can be terabytes in size and are…
A: Introduction: We may use the following tools to deal with large amounts of data: Platforms for…
Q: When it comes to software development, there are many ways the spiral model may benefit both the…
A:
Q: How do structured, object-oriented, and agile development methodologies differ? Which method do you…
A: Given: Programs are separated into discrete self-contained functions in Structured Programming.…
Q: OWASP Dependency Check is a superior tool for vulnerability evaluation than SimpleRisk and SFK,…
A: OWASP's complete form is the Open Web Application Security Project, an online forum dedicated to…
Q: Explain what is a a trogon horse and express if it ai compositing of other malicious malware.…
A: The Answer start from step-2.
Q: Compare Round-robin (RR) algorithm and the Shortest process next (SPN) algorithm for scheduling…
A: Compare Round-robin (RR) algorithm and the Shortest process next (SPN) algorithm for scheduling…
Q: Examine the various sorts of protocols and why they are required in today's world. (Information and…
A: There are large numbers of users talking with various gadgets in various languages in the realm of…
Q: In the discipline of computer science, what sorts of business rules are most often shown in the EER…
A: The answer to the following question:-
Q: Q1/ Write a program in C++ by using function to remove the spaces before and after the entered text,…
A: Please find the answer below :
Q: as well
A: Antivirus software, or antivirus software (truncated to AV software), otherwise called enemy of…
Q: Interrupt service routines are different from other types of service routines.
A: In this case, the "interrupt" is handled by an interrupt service procedure. What an "interrupt" is…
Q: What does it mean to "interrupt"? By discussing the various sorts of hardware disruptions, you may…
A: The Interrupt: An interrupt is an occurrence that causes the processor's execution sequence to be…
Q: Due to a cyber assault on the network system, the protocol has been disrupted.
A: Any form of an offensive attack that is intended to target the computer network for the purpose of…
Q: In terms of information literacy, what is phenemenographic theory?
A: The Phenomenography: Phenomenography was created in the late 1970s by a group of educational…
Q: Create a one dimensional array that contains the following: "Cath, Donna, Anna, Bob, Mae". Write a…
A: I give the code in C# along with output and code screenshot
Q: What is the purpose of this talk on CSS and forms?
A: Cascading Style Sheets: CSS defines how HTML elements appear on screen, paper, or other media. CSS…
Q: Write a program called Super_Digit.java with a recursive function called superDigit. The function…
A: CODE: import java.util.Scanner; public class Super_digit { public static int…
Q: What does the saying "Resist the urge to code" imply in the context of programming??
A: Introduction: Resist the urge to code: This suggests that a software engineer should first…
Q: Databases in search engines are very large. Is it possible that they have not been normalized by any…
A: INTRODUCTION: Here we need to tell databases in search engines are very large and how a corporation…
Q: The XML document should be stored in an XML database, right?
A: Given: XML documents are represented logically in an XML database, and the data is stored and…
Q: Please implement the Book search(Object e). This method returns the object being search if not found…
A: Here we need to iterate over the ArrayList we have and when we have a matching Book we are going to…
Q: 7) Provide a step-by-step lossless decomposition of R into BCNF normal form.
A: Answer
Q: How can risk be assessed? How do risk assessments work? IT Governance, 6th Edition Calder and…
A: Risk Assessment: A security risk assessment identifies, assesses, and implements important…
Q: Interrupts caused by hardware and software may occur in a variety of ways.
A: below is the response from the giver: - \sorrow forwardProcedure Number Two (Secondary)Interrupts…
Q: How do cohesion and coupling relate to software development? How can logical instructions be…
A: Here's the answer to the question, as well as an explanation: The interconnectedness of the module's…
Q: Discuss the internet's development and the technical foundations upon which it is built.
A: Introduction: Researchers began constructing the "network of networks" that would become the modern…
Q: Identify the vertical and horizontal users of a company's information system..
A: Please refer below for your reference: The vertical and horizontal users of a company's information…
Q: Explain the Main Inputs and Outputs of the TIMES Model What are the Differences between the TIMES…
A: The TIMES is also known as The Integrated MARKAL-EFOM System.
Q: How to convert the following dictionary into expected outcome list in python? dictionary = {…
A: To get the items of this dictionary in a list first iterate over the dictionary. For each key, get…
Q: To put it another way, what do you think is the ideal way to send I/O data? Explain. Interrupts in…
A: I/O data to put in similar words is the data exchanged between computer and the outside world or…
Q: Maintaining an information system is affected by a range of factors.
A: Information System: Hardware, software, databases, networks, and people are the five main components…
Q: Give two examples of how asymmetric and symmetric could be put to use. How is asymmetric encryption…
A: Uses of asymmetric encryption: NIST came up with the digital signature standard, which is in FIPS…
Q: What is the primary distinction between symmetric and asymmetric encryption in operation?
A: Symmetric encryption works: Symmetric encryption converts plain text into ciphertext and back. The…
Q: How can a network be protected against phishing attacks? What efforts should be taken to prevent…
A: Introduction: Phishing tricks are one of the most widely recognized strategies for assault you are…
Q: Using Java to design and implement the class PascalTriangle that will generate a Pascal Triangle…
A: Program Approach:- 1. Include header file 2. Create the class PascalProblem 3. Create the default…
Q: Describe the safeguards you'd put in place to protect your company's network against cyber-attacks
A: Cyber assaults are growing in frequency and complexity, due to elements like a higher range of…
Q: How do structured and object-oriented software development differ? Describe Agile Process Models…
A: Structured and object-oriented software development are different Let's see how:- Structured…
Q: Interruptions are described using the following terms: Explain their types and why no hardware…
A: Hardware Interrupts: An interrupt is a signal received by the processor that causes the program to…
Create the truth table
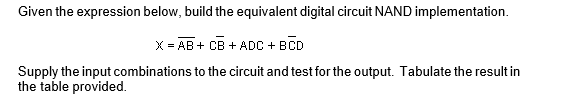
Step by step
Solved in 3 steps with 2 images

- draw a qpsk complete modulator circuit using circuit components of various types not a block diagram.Draw the circuit diagram to output F given in the expression above by referring to schematics for 2-2) and 2-3). Use the space below to draw both the IC with pin assignments and a circuit schematic. Using a single 7400 IC construct a circuit to output the following Boolean function: F = AB + CDDesign a circuit using a Multiplexer, (((USING A MULTIPLEXER NOT A DECODER))) that has two inputs X, and S, where X represents an 8-bit BCD number,S is a sign bit. The circuit has one output Y, which is the Binary representation of thesigned-magnitude BCD number. A negative output is represented in the Binary 2’scomplement form.
- draw a QPSK demodulator circuit using different circuit components. stop rejecting questionsImplement a combinational circuit with three inputs x, y, and z and three outputs A, B, and C.When the binary input is equal to 0, 1, 2 or 3, then the output is equal to the input + 1.When the binary input is 4, 5, 6 or 7 then the binary output is equal to the input – 2.Design the simplest circuit that has three inputs, a, b, and c, which returns an output value of 1 whenever g and b are complements of each other or b and c are complements of each other, otherwise the output is 0. Realize the circuit using 4input , 3output PAL
- Find the Maxterm expansion of the truth table and design the corresponding circuit in Quartus II. Simulate your design and verify that it functions properly according to the truth table. Please draw the truth table on paper so I can understand it.How are the components interralated with each other on this circuitDesign a combinational circuit with three inputs x, y, z, and three outputs a, b, and c. When the binary input is 0, 1,2, or 3 , the binary output is 1 greater than the input. When the binary input is 4, 5, 6, or 7, the binary output is one less than the input.
- please create the schematic on KiCad software for this circuit.Compute the Boolean expression for the digital circuit diagram below with the corresponding Truth table:Design a combinational circuit with three inputs, x , y , and z , and three outputs, A, B, and C . When the binary input is 0, 1, 2, or 3, the binary output is two greater than the input. When the binary input is 4, 5, 6, or 7, the binary output is two less than the input.

