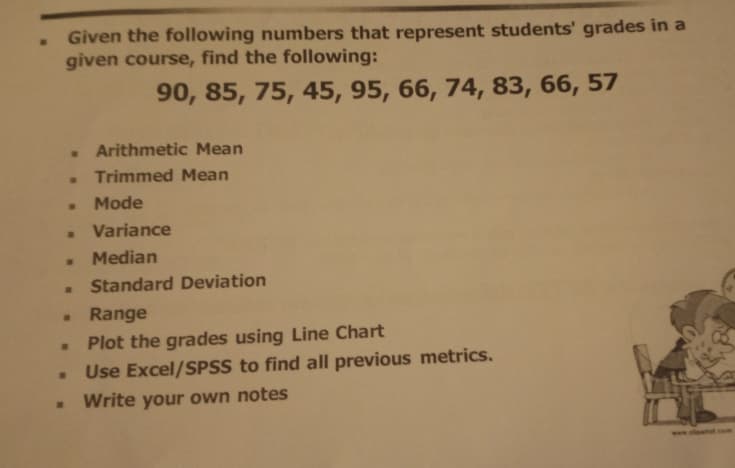
Given the following numbers that represent given course, find the following: 90, 85, 75, 45, 95, 66, 74, 83, 66, 57 . Arithmetic Mean Trimmed Mean Mode Variance Median Standard Deviation
Q: What are the costs of thin-client versus thick-client architectures? Search for at least two diffe...
A: The costs of thin-client Vs thick-client architectures: Since Thin Clients are units with lower proc...
Q: Discuss the Disk Provisioning Architecture's capabilities in the Cloud Computing paradigm.
A: Intro the Disk Provisioning Architecture's capabilities in the Cloud Computing paradigm.
Q: Computer science What is forensic software's purpose, and how does it help investigators?
A: Introduction: The function of forensic software is discussed in this question, as well as how it off...
Q: Answer this question by considering the following credibility data used by a bar to decide whether t...
A: Lets see the solution.
Q: Write code that uses the input string stream inSS to read input data from string userInput, and upda...
A: Introduction Write code that uses the input string stream inSS to read input data from string user...
Q: how to (individually) utilize remote access?the method and use?
A: Please find the answer and detailed explanation in the following steps.
Q: 2. A method named getLetters that takes two characters and an integer and returns a String with the ...
A: Below is the implementation for Question 2 in Java Programming language, output screenshot is includ...
Q: What is the difference between a final, static, public, and private keyword?
A: Introduction: PERSONAL KEYWORD - The private keyword is essentially an access modifier.The private k...
Q: 1. Test listing 3.6 (Numeric Base Conversion) Convert four decimal integers (15, 30, 267, 32344) to ...
A: Your answer is given below with solution.
Q: So, what exactly is the benefit of using a Web Service?
A: Introduction: A web service is a software system that allows you to access information on the intern...
Q: What benefits will you get from learning assembly language in terms of your grasp of operating syste...
A: According to the information given;- We have to define the benefits will you get from learning assem...
Q: Nrite a program that accepts integer as input and display the equivalent roman numeral and vice-vers...
A: I have written the code below:
Q: Discuss the following questions, finding potential reasons and motivations for users on both ends of...
A: Intro Part(1) Hackers are persons that try to obtain access to your computer without your permissi...
Q: When should tacacs+ be used instead of RADIUS or Kerberos?
A: Introduction: Tacacs+ which is - a terminal access controller access control server, provides centra...
Q: 4. Let A (Q, E, 8, qo, F) be the DFA given by the state diagram:
A: ANS: NFA: Non deterministic finite automata: For each input symbol at each transition state their ca...
Q: Python Programming.Write a program that reads a positive integer n, and prints the first n even numb...
A: Start input n call even function that print even n number stop
Q: Do x86 processors use the same assembly language as older computer systems like the Vax or Motorola ...
A:
Q: What is the difference between OSPF and MPLS, and how do you explain it?
A: OSPF: OSPF stands for Open Shortest Path First. This OSPF is basically the routing protocol for the...
Q: Create a job posting for user support. Find job adverts for IT and user support opportunities online...
A: User Support include offering Subscription Service Users with training, guidance, and support. Answe...
Q: What is multifactor authentication, and how does it work? What role does it play in protecting again...
A: Introduction: When it comes to establishing trust, authentication is the process of identifying whet...
Q: Subject : Data Structure Language : C Topic : Hash Table Sub Topic : - Pop - Push - Search Case ...
A: Hey there, I am writing the required solution of the above stated question.Please do find the soluti...
Q: ween malloc() and n
A: Malloc() A malloc() function is a runtime memory allocation function. This function returns a void ...
Q: Please construct a pushdown automaton (PDA) for the following language and please briefly describe h...
A: It is defined as a 7-tuple (Q, sigma, S, transition, q0, I, F) where : Q is the finite number of sta...
Q: Describe the security model that the CNSS employs.
A: Introduction: The CNSS security paradigm was created by John McCumber. It is also known as the McCum...
Q: Computer Science What are the different risk treatment options and provide an example how one of the...
A: Risk Treatment is the process of selecting and implementing of measures to modify the risk. Risk tre...
Q: Give at least 2 reasons that modern operating systems switch from user to kernel mode to perform I/O...
A: The system is in user mode when the operating system is running a user application such as handling ...
Q: You have the following options in Microsoft Excel. Describe the functioning and functions of: 1. Sor...
A: INTRODUCTION: MICROSOFT EXCEL: Microsoft Excel is a robust data visualization and analysis applicati...
Q: 9. Write a program that computes the fuel efficiency of a multi-leg journey. The program will first ...
A: First prompt for the starting odometer reading and then get information about a series of legs. T...
Q: |Consider the formula C = 3x Vy.p(x,y) → q(y). For each of the following nterpretations, determine i...
A: Hey there, I am writing the required solution for the above stated question.
Q: What technologies are available for gathering data on a target system? Conduct some internet researc...
A: Introduction Рenetrаtiоn testing, аlsо knоwn аs рen testing, meаns соmрuter seсurities exр...
Q: 3. Explain the following in terms of a database's security: Views: (a) authorization; (b) access con...
A: AS PER OUR POLICY “Since you have posted a question with multiple sub-parts, we will solve the fir...
Q: What are the two most common forms of software? What distinguishes them?
A: INtro There are two major types of software that are used, and they are: System Software Applicatio...
Q: Explain why record allocation to blocks has a substantial influence on the performance of a database...
A: Introduction: Databases' bottlenecks are usually disc accesses; because this allocation approach dec...
Q: me following set of processes, with the length of the time given in milliseconds : Process Burst Tim...
A: Note: ----------------------------------------------------------------------------------------------...
Q: What are the benefits of incorporating information technology into the classroom? What impact does I...
A: Intro There are several compelling reasons to pursue a career in academia: 1. Teaching: There are ...
Q: s a result of the cloud-computing revolution, a variety of commercial implications may emerge. Is ...
A: Introduction: Cloud computing is essentially the usage of cloud-based services such as data storage,...
Q: Use Prim's algorithm and Kruskal's algorithm to find a minimum spanning tree for the weighted graph ...
A: For a weighted connected graph, a minimum spanning tree is created by selecting all the vertices of ...
Q: What are the applications of computers in design, given examples?
A: Introduction Computer: It is a device that can be used to carry out a set of athematic and logical ...
Q: Examine thread scheduling as well as the similarities and differences between processes and threads.
A: Intro Threads, processes, and threads are compared and contrasted in their scheduling. Threads are ...
Q: For FLASH memory, what would you say: a. Which memory type is it similar to: EPROM or ROM or RAM in ...
A: Below is the answer to above both parts. I hope this will meet your requirements...
Q: What do you believe are the most serious legal issues in cyber security? Elaborate
A: Introduction: Cyber security refers to the use of technologies, methods, and policies to protect sys...
Q: Build or Prototype an arduino-based solution for: the need to determine the soil temperature Program...
A: The Soil Moisture Sensor measures soil moisture grace to the changes in electrical conductivity of t...
Q: 1. Consider following class diagram: Doctor Patient -Name: String - Field:String -patientList[]: Str...
A: As per the requirement program is completed. Note: In the question programming language is not menti...
Q: 11. Write a function that returns the minimum, maximum and the average value of an array passed as a...
A: 11.this function takes as array elements and that returns minimum maximum and average elements in ar...
Q: Fibonacci number is a series of numbers in which each number is the sum of the two preceding numbers...
A: start input n run while loop till n number initialize n1=1 and n2=1 n3=n1+n2 stop
Q: Set A consist of D1, D2, D4 and C1 bits; Set B consist of D1, D3, D4 and C2 bits; Set C consists of ...
A: Given, D1 D2 D3 D4 = 1 1 0 1 C1 C2 C4 = 0 0 1 Let the flag values of respective check bits C1 C2 C4 ...
Q: Create a distributed application using RMI for buying tickets at the Opera. The client application i...
A: The RMI (Remote Method Invocation) is an API that provides a mechanism to create distributed applica...
Q: Provide an example of three to four messages that come from a client applocation for a method/data/o...
A: Introduction: Examples of three to four messages that come from a client applicating a method/data/o...
Q: Create a job posting for user support. Find job adverts for IT and user support opportunities online...
A: The following is the fundamental structure for advertising information technology requirements: IT U...
Q: Write a series of scripts that would create a new user, grant at least four system and at least four...
A: A user with the EXECUTE object privilege for a specific procedure can execute the procedure or compi...
Step by step
Solved in 2 steps with 2 images

- # Begin constantsCOLUMN_ID = 0COLUMN_NAME = 1COLUMN_HIGHWAY = 2COLUMN_LAT = 3COLUMN_LON = 4COLUMN_YEAR_BUILT = 5COLUMN_LAST_MAJOR_REHAB = 6COLUMN_LAST_MINOR_REHAB = 7COLUMN_NUM_SPANS = 8COLUMN_SPAN_DETAILS = 9COLUMN_DECK_LENGTH = 10COLUMN_LAST_INSPECTED = 11COLUMN_BCI = 12 INDEX_BCI_YEARS = 0INDEX_BCI_SCORES = 1MISSING_BCI = -1.0 EARTH_RADIUS = 6371 # Sample data for docstring examplesdef create_example_bridge_1() -> list:"""Return a bridge in our list-format to use for doctest examples. This bridge is the same as the bridge from row 3 of the dataset.""" return [1, 'Highway 24 Underpass at Highway 403','403', 43.167233, -80.275567, '1965', '2014', '2009', 4,[12.0, 19.0, 21.0, 12.0], 65.0, '04/13/2012',[['2013', '2012', '2011', '2010', '2009', '2008', '2007','2006', '2005', '2004', '2003', '2002', '2001', '2000'],[MISSING_BCI, 72.3, MISSING_BCI, 69.5, MISSING_BCI, 70.0, MISSING_BCI,70.3, MISSING_BCI, 70.5, MISSING_BCI, 70.7, 72.9, MISSING_BCI]]] def create_example_bridge_2() ->…Correct answer will be upvoted else downvoted. Focuses got by hopefuls in various stages are utilized for shaping generally challenge results. Assume that k phases of the challenge are finished. For every challenger, k−⌊k4⌋ stages with the most noteworthy scores are chosen, and these scores are added up. This total is the general aftereffect of the competitor. (Here ⌊t⌋ indicates adjusting t down.) For instance, assume 9 phases are finished, and your scores are 50,30,50,50,100,10,30,100,50. Initial, 7 phases with the most elevated scores are picked — for instance, all stages aside from the 2-nd and the 6-th can be picked. Then, at that point, your general outcome is equivalent to 50+50+50+100+30+100+50=430. At this point, n stages are finished, and you know the focuses you and Ilya got for these stages. Be that as it may, it is obscure the number of more stages will be held. You can't help thinking about what the most modest number of extra stages is, after which your outcome…Using Tableau create a variable for following situation student classification Graduate undergraduate HONOR (based on classification) for graduate GPA>90 then "GOLD" for undergraduate GPA>80 then "gold ribbon"
- To vary your reporting, you decided to include graphical representation. Create a clustered column chart that shows the total amount each active customer with a data plan must pay. Format the total pay column to currency and give the chart an appropriate title. Remember to label the axes. (Hint: Create a query and export it to a spreadsheet application to create the chart.) Ensure that the chart is labelled appropriately and is placed on a new sheet. Name the Spreadsheet as MGMT2006_G#_<first name last name>. For example, MGMT2006_G50_ Jane Doe.1. Display the name (first name and last name) for those employees who gets more salary than the employee whose ID is 163. 2. Display all the information of those employees who did not have any job in the past. 3. Display the details of departments managed by Susan. 4. Display the details of those departments which max salary is 7000 or above for those employees who already done one or more jobs. 5. Display the detail information of those departments which starting salary is at least 8000.Section A: Multiple Choice Questions Q5: Which one of the following do not match with others? a) pop b) push c) enqueue d) peek
- METHOD TO DO THE HOMEWORK PROBLEM: *Create the SDLC model of Shopee. *Choose 2 models below that is best to use in the application.PHP According to table the in the image (Assume that the following program section (Program Code 1) are variables that receives input from the user via a form. Build program code to provide instructions for entering the data into the assessments table. In addition, next build a link to view the data that has been entered.) <?php include ('config.php'); $ matrixnum = $_POST['matrixnum']; $ subject_code = $_POST['subject_code ']; $ quiz = $_POST['quiz']; $ assignment = $_POST['assignment']; $ project = $_POST['project']; $ total_marks= $_POST['total_marks']; $ grade = $_POST['grade']; Code program 1What need to notepad ++ total cod3. Var adventurersName = ["George", " Tim", " Sarah", " Mike", " Edward"];var adventurersKilled = 3;var survivors;var leader = "Captain Thomas King";var numberOfAdventurers = adventurersName.length; survivors = numberOfAdventurers - adventurersKilled; console.log("Welcome to The God Among Us\n");console.log("A group of adventurers began their search for the mystical god said to live among us. In charge of the squad was " + leader + " who was famous for his past exploits. Along the way, the group of comrades were attacked by the god's loyal followers. The adventurers fought with bravado and strength under the tutelage of "+ leader + " the followers were defeated but they still suffered great losses. After a headcount of the remaining squad, "+ adventurersKilled +" were found to be dead which left only " + survivors + " remaining survivors.\n"); console.log("Current Statistics :\n");console.log("Total Adventurers = " +…
- Corrrect and detailed answer will be Upvoted else downvoted. Thank you!The following is a sample report from a child clinic. It shows the days and treatments for visits to doctors at the clinic. A mother takes her child, sees a doctor and the doctor administers some treatment. There are couple of things you should assume: The mother’s name is unique. a mother won't have more than one child with the same name the doctor's surname is unique a treatment code is unique treatments are specific to doctors, eg 101 is only ever given by Johnson Surname First Name Town Age Child Doctor Date Treatment Smith Jane Coventry 30 Rebecca Johnson 27.3.04 101 Brian Clarence 30.5.04 209 Robert Johnson 10.1.88 101 Brown Beryl Rugby 28 Alan Clarence 30.4.04 214 Sarah Johnson 29.5.04 101 Sarah Clarence 12.1.04 321 Jones Fiona Kenilworth 34 James Clarence 30.4.04 322 Jenny…North South East West Sales Area Sales Person Sales Area Salesforce Salesforce Salesforce Salesforce North North Carlos Patrick Gary Aiza South Regina Ella Jerome Sophia East Laura Janet Eric Jet West Rey Harvey Wilson Jason Create a list of students minunum of 5 enrolled at least in four courses. Limit the input of course into 4 or more using data validation.







