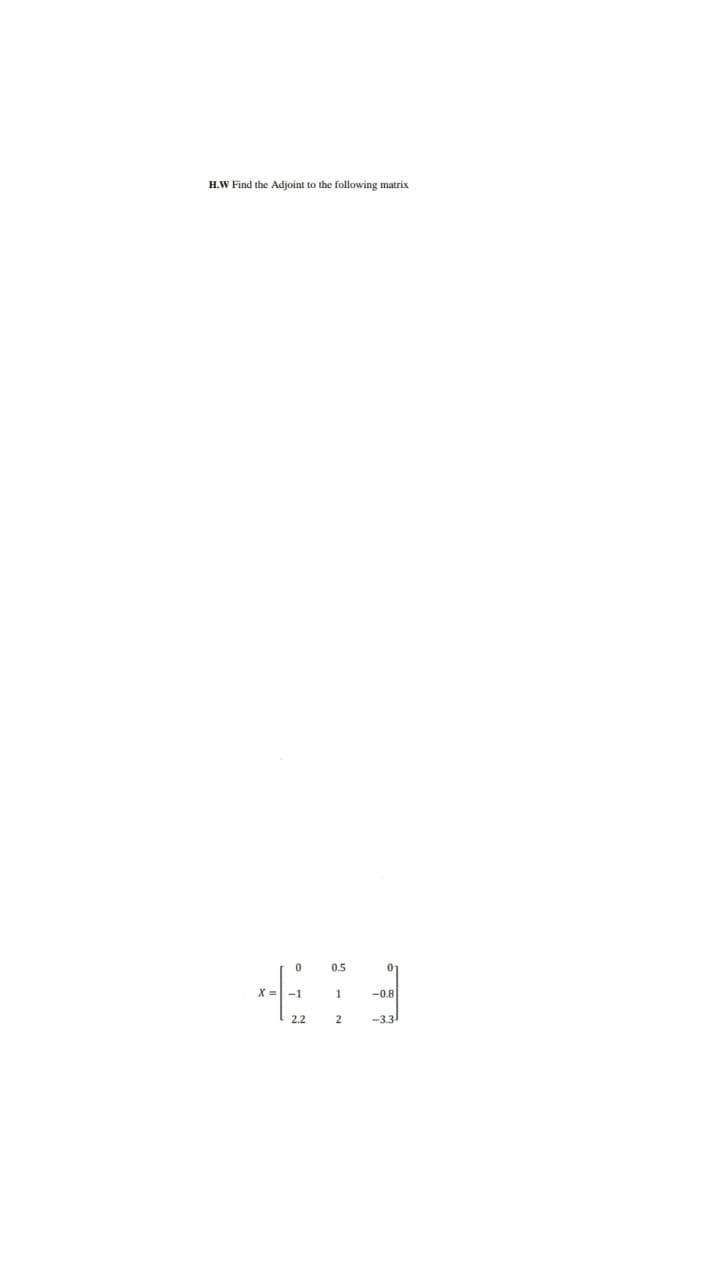
H.W Find the Adjoint to the following matrix 0.5 01 X = -1 -0.8 2.2 -3.3
Q: Identify and explain the Internet of Things (IoT) reference model. Fill in the blanks with the four ...
A: Introduction: In addition, the IoT reference model helps create and standardize IoT architecture and...
Q: Explain what a TCP connection is. Is the concept of a TCP connection incompatible with the reality t...
A: TCP (Transmission Control Protocol): This is a connection-oriented protocol and is used at the tran...
Q: 1. Explore the concept of object responsibility and how it is related to message sending between obj...
A: According to company guidelines we are restricted to answer only first question when other parts are...
Q: oblem 3: How can we use FFT to speed up integer multiplications? For $463456x29584583 takes 9x8 dioi...
A: Lets see the solution.
Q: The decimal equivalent of hex number 1B52 is O 6794 Skip O 6993 6949 O 6994
A: Actually, binary numbers are nothing but a 0's and 1's.
Q: Describe how motion input is used in the entertainment, military, athletics, and medical industries,...
A: Answer the above questions are as follows:
Q: A computer with subsystems as well as logical divisions is superior than one without.
A: Introduction: The workflow and resource usage are combined in the subsystem. The system may be brok...
Q: Within the context of visual analysis a ________ graph depicts an interconnected collection of entit...
A: Network grap is the answer
Q: The decimal equivalent of hex number 1B52 is * O 6794 O skip 6993 O 6949 O 6994 The Simplify of the ...
A:
Q: Guice is a dependency injection library that is commonly used in the Java programming language. Howe...
A: In order to enable multiple configurations, an application or class must be able to independently bu...
Q: 3. a) A relation that does not have a composite primary key still has partial functional dependency....
A: Answer: Answer -3(a): The correct answer is 1. TRUE Explanation: Yes, the relation is uniquely dete...
Q: In the HTTP protocol, what is the primary different between a GET request and a PUT request? GET req...
A: By using this HTTP -- Hyper Text Transfer Protocol user is able to communicate between client and se...
Q: a) Explain the term handle and illustrate with 3 examples how they are used in Windows system progr...
A: Here is the detailed explanation of the program
Q: equest 2 You have to send the following data to a server: a) a hat brand of Stetson and b) a style o...
A: Answer : The POST method transfers information via HTTP headers. The information is encoded as descr...
Q: U1 n=5 V1 V2 U5 U2 V5 U4 U3 V3 V4
A: A dominating set for a graph G = (V, E) is a subset D of V such that every vertex not in D is adjace...
Q: Are the protective procedures sufficient to ensure the security of the information system? Alternati...
A: Introduction: Information security is much more than preventing unwanted access to data. The practic...
Q: Computer science Is it true that Amazon supports region-based services across all of its services?
A: The services offered by Amazon services are either regional, Global, or they are specific to the loc...
Q: Computer science What are some of the benefits of automating the testing procedure?
A: Introduction: The use of software tools to automate a human-driven manual process of examining and c...
Q: 1. Many languages distinguish between uppercase and lowercase letters in user-defined names. What a...
A: The following are some of the reasons why a language would differentiate between uppercase and lower...
Q: Explain what the "for each item in list" procedure (pictured below) does and/or why you might need t...
A: for each loop: The for-each loop is used to iterate each element in the list which means the loop wi...
Q: Assume you have a client who has never utilized a network. Explain the function of network servers a...
A: Introduction: Client-Server Architecture is a computer architecture in which the server hosts, provi...
Q: Create a Java program that will compute the Netpay of the employees. Compute the grosspay by multipl...
A: The above output is created using Java Swing GUI Components 1.Design the form using swing components...
Q: ive the difference between the compilers and just in time (JIT) compilers in your own w
A: Lets see the solution.
Q: processed in a loop. The program should ‘dump’ the contents of the array before and after modificati...
A: 10. Write a program that modifies an array of 10 full words by replacing every negative value with...
Q: Write a subroutine which copies a string starting from address $1100 to a location starting from add...
A:
Q: Write a JavaFX Program to locate ATM. Get the current city name and bank name. Search the database ...
A: Actually, program is an executable software that runs on a computer
Q: Can additional widgets be added to home/dashboard?
A: A software widget is a simple and easy-to-use software program or component designed for one or more...
Q: ill the following code display in the lblSum control? Dim intSum As Integer Dim intY As I...
A: Lets see the solution.
Q: What is a learning system? Give an example of a learning system and explain
A: A learning system is basically an assortment of antiques that are 'united', in a proper way, to esta...
Q: Describe how organizational culture is related to project management. What type of culture do you th...
A: Organisational culture is related to project management in many ways.
Q: Questions for you to try 1. Convert each of the following values to an 8-bit unsigned binary value. ...
A: . Convert each of the following values to an 8-bit unsigned binaryvalue. 3510 -110110110110 (10110...
Q: What exactly is a policy? What distinguishes it from a law?
A: Policy: "Policy is the blueprint of what a government will do and what it can accomplish for society...
Q: l the
A: given - Write pseudocode to recognize all the operators Lexemes Token Name Attribute Value ++ artop ...
Q: What are some of the most important aspects to consider when it comes to data backup and recovery?
A: Introduction : Planning is done throughout the data backup and recovery process to keep track of vit...
Q: Write a Java program named searchForLastOccurence that : Asks the user to enter an integer value tha...
A: Introduction: This question explains about JAVA program
Q: A. ASCII В. ЕВCDIC C. Unicode D. ASCII 8. Bit map images are made up of A. phonemes B. vectors C. pi...
A: let us see the answer:- "Since you have multiple question i am solving first 2 for you if you want a...
Q: B. Partial - Fraction Expansion with MATLAB Determine the partial fraction expansion of the followin...
A:
Q: The approximate word is when the value on the left of th word is equal to the total value on the rig...
A: Algorithm - Create a function with argument a string. define the two variable with sum of left ...
Q: What are the purposes of partitions?
A: INTRODUCTION: Partition: It is a section of the hard drive that is distinct from the rest of the dr...
Q: nsider a schedule with 4 transactions with 1, 2, 3, and 4 operations respectively. Calculate the pos...
A: Lets see the solution.
Q: When a program is executed by the CPU, it must be copied into what type of memory each time?
A: The CPU is also known as central processing unit.
Q: In BCD Addition, if and only a 4-bit sum is greater than 9, it is an invalid result. *
A: True In 4-bit binary addition it is invalid if sum is greater than 9.
Q: A teen ager Sport Club offers many sports to the registered members write a java code to keep facili...
A: To get the solution of the given problem we create all the classes as follows:
Q: Write a program that keeps on taking numbers from the user, until the user enters any input that it ...
A: Answer: Java Source Code: import java.util.*;import java.lang.*;public class Main { public static...
Q: What exactly is a program that is event-driven?
A: An event-driven program is one that largely responds to user events or other similar input.
Q: A local pizza shop is selling a large pizza for $9.99. Given the number of pizzas to order as input,...
A: import java.util.Scanner; public class LabProgram{ public static void main(String[] args) { Sc...
Q: What exactly is game theory, and why is it relevant in AI?
A: Introduction: In a multi-agent environment, choosing from a set of reasonable options is known as ga...
Q: What is the difference between an output device and a dot-matrix printer?
A: Introduction: Output Devices It's an electromechanical device that accepts data from a computer and ...
Q: What steps should we take to ensure that a dot matrix printer lasts as long as possible?
A: Given: What steps should we take to ensure that a dot matrix printer lasts as long as possible?
Q: Please give an example of a machine/system or programming language that is TuringEquivalent or Turin...
A: Introduction : What does it mean to be Turing Equivalent The term "Turing equivalent" refers to a ma...
Step by step
Solved in 2 steps with 1 images

- Enter the 5 × 5 Hilbert matrix using MATLAB software 1 1/ 2 1/ 3 1/ 4 1/ 5 1/ 2 1/ 3 1/ 4 1/ 5 1/ 6 1/ 3 1/ 4 1/ 5 1/ 6 1/ 7 1/ 4 1/ 5 1/ 6 1/ 7 1/ 8 1/ 5 1/ 6 1/ 7 1/ 8 1/ 9 H i) Find the determinant of H. ii) Find the transpose and inverse of H iii) Using the commands in the text, find the dimensions of H, the column sums, and the row sums of H.Minimize using Q-M f(a,b,c,d,e) = £m(0,1,4,5,6,13,14,15,22,24,25,28,29,30,31)C++ WAP that reads from the user an integer matrix of 10x10 and then rotate that matrix at 180 degree upside down after that calculate sum ,average of main diagonal .print the matrix after rotation. Don't copy from internet Solve with in 10 min else you can skip
- Write the Python code to find the transitive closure when given zero-one matrix. DO NOT use the Warshall Algorithm in this code. Pseudo code: A := MR B := A for i := 2 to n A:= A ⊙ MR B:= B ∨ A return B (the zero-one matrix for R*)Replace the second column of * matrix Y to vector b, b=[4 68 10]Draw the following graph as represented in the adjacency matrix below. a b c d A 1 1 1 0 B 0 1 1 0 C 0 0 1 1 d 0 0 0 1
- I do not understand this expression. so is c[i][j] += a[i][h] * b[h][j] mean c[i][j] = a[i][h] * b[h][j] + c[i][j]?? ; We do not know about the + matrix c right?PLEASE SHOW STEPS:Use K-Maps to simplify each of the following: ~x~y~z + ~xyz + ~xy~z ~x~y~z + ~xy~z + x~y~z + xy~z ~y~z + ~yz + xy~z1 0 0 2 1 0 4 3 1 Compute the inverse of the matrix
- Construct a square matrix with NN rows and NN columns consisting of nonnegative integers from 00 to 10^{18}1018, such that its determinant is equal to 11, and there are exactly A_iAi odd numbers in the ii-th row for each ii from 11 to NN, or report there isn't such a matrix. Standard input The first line contains a single integer NN. Each of the next NN lines contains a single integer A_iAi. Standard output If there is no solution, output \text{-}1-1. Otherwise, print NN lines, each consisting of NN integers, representing the values of the constructed matrix. If there are multiple solutions, print any. Constraints and notes 2 \le N \le 502≤N≤50 1 \leq A_i \leq N1≤Ai≤N For 40\%40% of the test files, N \le 17N≤17.Consider the matrix A=[3 −8 −7 5 −9 7 −15 22 −13 6] a) Copy positive numbers into B b) Copy negative numbers into C c) Find the locations in A where the numbers are between −10 and 10 inclusively Please use matlabWrite a program to create a matrix A(5*5), then replace the diagonal with zeros. Add “break” or “continue” when it is suitable. used matlab

