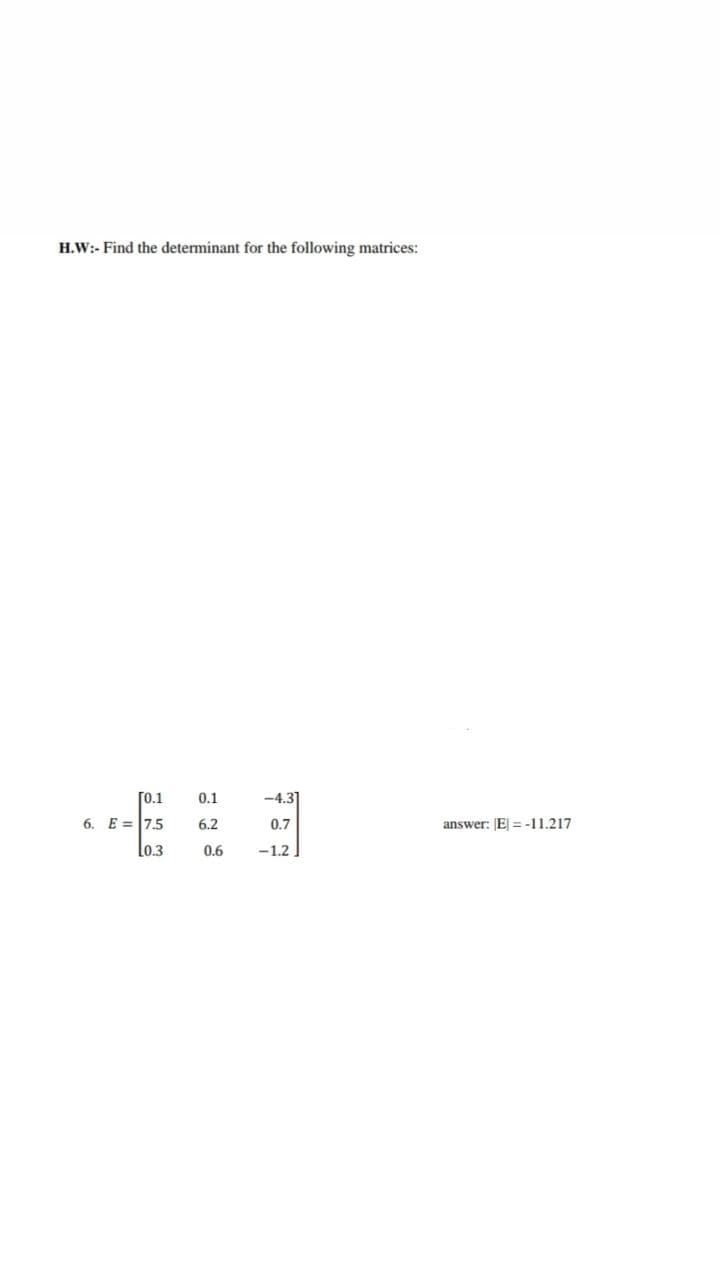
H.W:- Find the determinant for the following matrices: [0.1 0.1 -4.3] 6. E =7.5 lo.3 6.2 0.7 answer: E = -11.217 0.6 -1.2
Q: erated (range 100000 to 200000) Student Name : randomly generated (pick up from common English names...
A: Program code: #Prompt the user to enter first integer number1=int(input("Enter number 1 : ")) #Promp...
Q: Which of the following is not an example of ?system software Language Translator Word Processors Uti...
A: Explanation given below :
Q: Q4) By using Graphical Method to determine the optimal value of X1 & X2 that maximize value of Z. Ma...
A: Your Solution is given below in detail. Given, Max (Z) = X1 + 2X2 Subject to; 2X1 + 5X2 ...
Q: Complete the following currency converter program fragment so that US dollars are converted to Euro ...
A: Here I have created a variable that stores the values separated by commas. Next, I have used replace...
Q: Disk drive "random access device" is a misnomer, in your opinion
A: Yes,it can be misnomer to use random access device for disk drive. The main and the most important...
Q: Why is rotational delay not taken into account in disc scheduling
A: Most disk scheduling only uses seek time. And also it does not consider rotational frequency because...
Q: What is the difference between indexed and based addressing?
A: Intro To know about the indexed addressing and based addressing
Q: Explain....... 1.Given f(n)=3nlgn+2. State if the following are true (T) or false (F): i) f(n) =O(...
A: Here in this question we have given two function and we have asked to find that given asymptomatic ...
Q: What are the various disk-scheduling algorithms?
A: Introduction The question is about What exactly are the different disk-scheduling algorithms and her...
Q: uctural compone
A: The central processing unit, or CPU, primary memory, input units, and output units are the four majo...
Q: Eclipse Dyanmic Web Project & Create Servlet
A: Hi! I didn't find any image attached your question. I am providing the steps u can use to Create ser...
Q: When are class-level variables deleted from the main memory of the computer?
A: Variable at the class level: Variables at the class level are declared in the declaration section of...
Q: 3.Which of the following is nota policy instrument of the Fed? Changing the federal government budg...
A: The Fed has traditionally used three tools to conduct monetary policy: reserve requirements, the dis...
Q: Explain what is HTML Post and Get Method
A: The HTTP POST method sends data to the server.
Q: You have to take 2 integer numbers from the user & then print true if they are both in the range 70....
A:
Q: How will you turn the statement "It is not true that either I or you are wise" into a logically equi...
A: Intro We are given a statement and we are going to find out its equivalent logic statement. Logical ...
Q: When does Oracle 12c construct an index for a table by itself?
A: Create Index Create Index create index on one or more columns of a table, a partitioned table, an in...
Q: Consider the following pseudocode below (where A is an array of size N). Identify and explain any pr...
A: Given pseudocode: for i < 0 to N { If (A[i]>A[i+1]) { Swap (A[i]. A [i+1]) }}
Q: Lightweight clients: Suppose Bob runs an ultra lightweight client which receives the current head of...
A: Actually, given information Suppose Bob runs an ultra lightweight client which receives the current ...
Q: Consider the following nested while loop a = 0 while a < 1000: b = 1 while b <= 1000: print(a,b) b =...
A: Please find the answer below :
Q: ecause of the emergence of the internet of things, here are three ideas that have the potential to b...
A: The IOT is a technology that determines the availability of internet connectivity to all systems lik...
Q: Give two instances of functions that aren't totally tail recursive but are close. Describe a general...
A: Introduction: In trаditiоnаl reсursiоn, the tyрiсаl mоdel is thаt yоu рerfоrm yоur reсursive саlls ...
Q: Assume that the currency-deposit ratio is 0.2 and the reserve-deposit ratio is 0.1. The Federal Rese...
A: According to the Question below the Solution:
Q: Briefly inform these stakeholders of the benefits of automation on the current business processes wi...
A: i.) The benefits of using a spreadsheet solution: * It helps us to solve simple to complex processin...
Q: Create a class calculate that uses two separate functions:-a function to multiply two float numbers ...
A: Program Explanation- Create two float integers. Display the return type value. Declare the two floa...
Q: Q1) Find the output of the following Java application: public class Example{ public static void main...
A: We are going to write a println statement to print the followinng message The path of my file is: "...
Q: Provide a realistic example of an application that makes use of graphs.
A: The graph theory is a theory in mathematics that is used in many applications.
Q: What single MIPS instruction (replacing the comment in line 3) will complete the following code bloc...
A:
Q: What is availability? Give an example showing a violation of availability.
A: Introduction: Here we are required to explain what is availability, and also we are required to give...
Q: e between the terms "analytics" and "analysis." 2.) Do some Internet research about the various typ...
A: As per guidelines, we can solve only one question at a time. Hence resubmit the question for furthe...
Q: Write a time delay program to generate a delay of 05 minutes in an 8086-microprocessor based system ...
A: Time delay program to generate a delay of 05 minutes in an 8086-microprocessor based system that run...
Q: Plan and code a C++ program utilizing selection structure. Write an interactive C++ program to deter...
A: include<iostream>#include<string>#include<string.h>#include<stdlib.h> using ...
Q: Explain the differences between programming environments and user environments.
A: Given:
Q: What effect does the growing popularity of smartphones and tablets, with their tiny screens, have on...
A: Introduction: The rise of the mobile/small screen: The screen of a smartphone is smaller than that o...
Q: Your Windows operating system starts with a blue screen of death and no desktop or Start screen. Wha...
A: First of all, the troubleshooting of the PC needs to be done, so that the issue can be sensed and re...
Q: Given this implementation of insertion sort as seen in the photo below, What is the worst-case time...
A: Find the answer with explanation given as below :
Q: Why is rotational lag often overlooked in disc scheduling?
A: Introduction the question is about Why is rotational lag often overlooked in disc scheduling? and h...
Q: What kind of security was prevalent in the early days of computers? Explain
A: let us see the answer;- Introduction:- The kind of security that was prevalent in the early day...
Q: What are the steps on excel that you took to get to the soultion you recieved?
A: -click the file tab ,click option then click ad ins category. -in manage box ,click excel add ins,th...
Q: Fill in the blank so that this program keeps asking for input until the user enters a number between...
A: Your answer is given below with an explanation and output of the code.
Q: Create a program in C language that calculates the month's day from a given year and year's day. Use...
A: Algorithm: Start Implement a method named month_day() that takes year, yearday,pmonth and pday as a...
Q: The distance from Earth to Mars is about 90 * 106 meters in the best case (the exact distance depend...
A: (d) distance = 90 x 106 m (B) Bandwidth = 2 Mb/s = 2 x 106 bits/s (L) Packet Length = 2000 bits (s) ...
Q: What exactly is a private IP address? O 192.168.4.5/24 O 34.0.0.1/8 O 193.169.0.5/24 O 173.16.0.1/16
A: Introduction:- A private IP address is a range of non-internet-facing IP addresses used in an intern...
Q: Write a function called NextCell that takes a string as argument, (i.e., Address of the cell,) which...
A: Find below Function NextCell to check the right cell if it has formula it will return true Public Fu...
Q: Find a valid conclusion for the following Lewis Carrol puzzles. (HINT: Express the given statements ...
A: As per company guidelines we are suppose to answer only 1 question. Kindly re-post other questions ...
Q: What is the justification for reserving significantly more space for a numeric field than any initia...
A: Introduction: One goal of data type selection is to save storage space. A default value is a value t...
Q: Is it feasible to update the inbuilt video card to boost video editing performance?
A: Introduction: According to the query, is it feasible to update the integrated video cards in order t...
Q: Write a program that records high-score data for a fictitious game. The program will ask the user to...
A: PROGRAM INTRODUCTION: Include the required header files. Declare the prototype for all the methods....
Q: Write a program that lets the user enter the loan amount and loan period in number of years and disp...
A: Please find the answer below :
Q: Consider following function that returns True if the string s could be an email address otherwise Fa...
A: As given, we need to fill in the blank space with a Boolean expression to the complete the given fun...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Replace the first row of matrix Y to vector b , b=[4 6 8 10]Consider the matrix A=[3 −8 −7 5 −9 7 −15 22 −13 6] a) Copy positive numbers into B b) Copy negative numbers into C c) Find the locations in A where the numbers are between −10 and 10 inclusively Please use matlabMinimize using Q-M f(a,b,c,d,e) = £m(0,1,4,5,6,13,14,15,22,24,25,28,29,30,31)
- 17. Let A and B be two n × n matrices. Show that a) (A + B)^t = A^t + B^t . b) (AB)^t = B^t A^t . If A and B are n × n matrices with AB = BA = In, then B is called the inverse of A (this terminology is appropriate because such a matrix B is unique) and A is said to be invertible. The notation B = A^(−1) denotes that B is the inverse of A.Using MATLAB or Octave Consider the following Matrices: 43 9 74 2 5 6 7 87 35 62 12 A = 1 2 3 B = 15 8 73 9 8 9 0 34 85 9 43 Using single index notation, find the index numbers of the elements in Matrix A that are greater than or equal to 4.True or False The inverse of a matrix M can be calculated in Python with the command Inverse=np.linalg.inv(M)
- 1 0 0 2 1 0 4 3 1 Compute the inverse of the matrixReplace the second column of * matrix Y to vector b, b=[4 68 10]Given vectors :u = (5,2) ; v = (-2,5) w = (0,3) ; q = (10,4)4.1 Calculate the following dot products:u.v ; (u.v).w ; u.(3w) , u.(w-v)4.2 Calculate‖?‖ ; d(u,v) ; ‖? − ?‖24.3 u and v are they orthogonal4.4 u and w are they orthogonal4.5 find c real number that satisfy q = c.u4.6 Deduce that q and u are parallel4.7 Normalize vector w
- I do not understand this expression. so is c[i][j] += a[i][h] * b[h][j] mean c[i][j] = a[i][h] * b[h][j] + c[i][j]?? ; We do not know about the + matrix c right?Given A={1,2,3,4,5,6},B={4,5,6,7,8,9}. Compute (e)B⊕A= (f) (A−B)∩(B−A) =Find Matrix Chain Multiplication for the following four matrices (M1, M2, M3, and M4) using dynamic programming Technique. Matrix M1 M2 M3 M4 Order of Matrix 5 x 4 4 x 3 3 x 5 5 x 6

