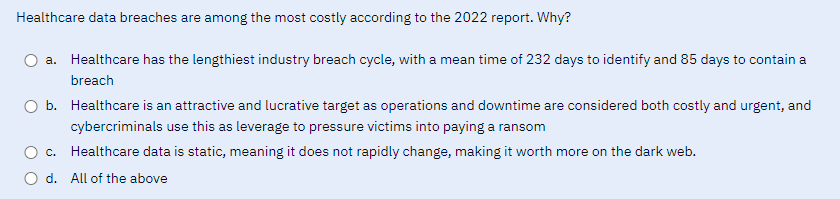
Healthcare data breaches are among the most costly according to the 2022 report. Why? a. Healthcare has the lengthiest industry breach cycle, with a mean time of 232 days to identify and 85 days to contain a breach b. Healthcare is an attractive and lucrative target as operations and downtime are considered both costly and urgent, and cybercriminals use this as leverage to pressure victims into paying a ransom c. Healthcare data is static, meaning it does not rapidly change, making it worth more on the dark web. d. All of the above
Q: What are the most vital factors to think about while creating a presentation? Provide five examples…
A: The five appearance aspects are: 1. What works? Create a slideshow that's really going to connect,…
Q: In Java what does string method concat used for? Write an example code.
A: In Java, the string data type is used to represent a sequence of characters. Java provides several…
Q: Provide an example of how APIs may be used to bridge the gap between legacy and modern software.
A: Application Programming Interfaces (APIs) provide a means for different software systems to…
Q: When is it appropriate to employ dynamic scoping, and how may its efficiency be improved?
A: Your answer is given below.
Q: Tell me what you think about DMP and if you think these devices will aid or hinder mobile device…
A: Use academic references to support your explanation. You may also conduct independent research and…
Q: How does IT SECURITY in the cloud compare to traditional on-premises data centers, and what are the…
A: Introduction :- Both on-premises and cloud security have numerous features in common and…
Q: What sorts of computations do experts predict will be performed exclusively by artificial…
A: An artificial intelligence (AI) system, which simulates human intellectual processes using computers…
Q: When is dynamic scoping helpful, and how can it be made better?
A: Overview: Dynamic planning, Any object or process that is constantly altering is said to be…
Q: Could you elaborate on what you mean by "partitioning" in the context of computer operating systems?…
A: In the context of computer operating systems, "partitioning" refers to the process of dividing a…
Q: Given the following truth table, abc F 000 1 001 1 010 0 011 1 100 1 101 0 110 0 111 0 a) Find the…
A: SOLUTION - The Minterms of the truth table is: F=a′b′c′+a′b′c+a′bc+ab′c′
Q: Describe the changes between a two- and three-tier application architecture. Which one works best…
A: Introduction: Compare two-tier and three-tier programme design in this query. Distinguishing These…
Q: I'm eager to find out what each of the three primary frequency bands is called in wireless networks.…
A: A group of frequencies known as a frequency band is employed for a certain function. Frequency bands…
Q: Local, state, and federal government agencies are establishing e-gov sites in order to improve the…
A: “Since you have posted multiple questions, we will provide the solution only to the first question…
Q: If there are constant, regular changes to the scope of the IT project, there may come a time when…
A: If there are constant, regular changes to the scope of the IT project, there may come a time when…
Q: i pop html pop down menus become evident at mouse floating.
A: This code is an example of a nested dropdown menu using HTML and CSS. The menu has three levels of…
Q: What parameter must be set when redistributing a route into EIGRP? Many factors, such as the…
A: Introduction: EIGRP (Enhanced Interior Gateway Routing Protocol) is a protocol used for routing data…
Q: Think about the advantages and disadvantages of both batch data entry and online data entry. Source…
A: Your answer is given below.
Q: List the transparency features that should be included at a bare minimum in a distributed database…
A: Introduction: A distributed database management system (DDBMS) is a database management system that…
Q: Why do we often confuse segmentation and paging? What does it mean to thrash?
A: Thrashing is a situation that may occur in a virtual storage system when there is an excessive…
Q: What are the three conditions that must be true for a network to function optimally? Give me a…
A: According to the information given:- We have to define three conditions that must be true for a…
Q: You can’t afford that new Nvidia graphics card so you thought you would try to create some old…
A: Please find the answer below :
Q: Can you explain what "memory leaks" are in the context of dynamic memory allocation?
A: Memory that is dynamic: Memory is allotted dynamically at the time of runtime in the technique known…
Q: This example may be derived from "snapshot isolation" airline database. What if, instead of a…
A: Consider the database of an airline, which makes use of snapshot isolation. Take into account the…
Q: Educate upper management on the ins and outs of database use.
A: TO MANAGEMENT FROM DATABASE: In essence, database management refers to the procedure through which a…
Q: For what reasons may stack systems use the inverted Polish notation for mathematical expressions?
A: Reverse Polish Notation is a method of writing mathematical expressions in which the operator comes…
Q: Does the JVM's method region serve any particular function, and if so, what is it used for? There…
A: Wireless data connections are used in a wireless network to connect network nodes. Mobile phone…
Q: It is very difficult to develop a mobile network without relying in some way on wireless…
A: Wireless networks use RF technology. spectrum for data transmission and reception. This network…
Q: Provide some examples of session hijacking techniques. If you were attacked in this way, how would…
A: Depending on the attacker's location and attack vector, the attacker has a variety of methods for…
Q: Where does static type checking differ from dynamic type checking?
A: Programs employ type systems. Type systems are logical. It has rules. These rules type computer…
Q: When talking about databases, what does the phrase "Hybrid Approach" mean?
A: The hybrid data warehousing technique recommends designing an enterprise model for two weeks before…
Q: What is the sum of the probabilities of the pointer landing in the green, blue, yellow, and red…
A: We have to explain that What is the sum of the probabilities of the pointer landing in the green,…
Q: Write a Python function that does the following: Its name is sum_nums It takes two arguments: a…
A: Answer:
Q: Is it feasible for two network interfaces to share the same media access control (MAC) address? Do…
A: Answer is given below:
Q: Analyze the concept of abstraction by opposing and contrasting it with numerous instances from the…
A: Assigned task: The question centres on the notion of abstraction and its applicability to software…
Q: actors that contribute to cyberbullying, its consequences for communities, and potential responses…
A: SOLUTION - As we know Cyberbullying is the biggest concern in today's digital age and we can see…
Q: What are the key advantages and disadvantages of cloud IT SECURITY compared to that of on-premises…
A: Given: What at least five differences exist between cloud settings and on-premises data centres in…
Q: Define the cash hit and hit ratio. Which hit ratio is cost-effective?
A: The question is asking about two concepts related to cache memory: cache hit and hit ratio, and…
Q: In terms of throughput, wireless networks beat out wired ones, but they still lag below the combined…
A: Given: In terms of throughput speed, wireless networks are faster than wired networks, but they are…
Q: Outline a few options for seizing control of the meeting. How would one defend themselves from such…
A: Depending on location and vector, attackers may hijack a user's session. Attackers leverage server…
Q: The use of wireless networks in developing nations merits further scrutiny. For reasons that remain…
A: Introduction: Wi-Fi connects laptops, iPads, telephones, and other gadgets to the internet, as your…
Q: How do computer engineers apply principles of human-computer interaction and user-centered design to…
A: Answer:- HCI refers to the study of designing, evaluating, and implementing computer systems that…
Q: Explain the significance of the differences between a logical data flow diagram and its physical…
A: Logical data flow diagrams and their physical equivalents serve different purposes in the system…
Q: Please Provide the stochiometric output as a matrix on Python. Thank you.
A: Based on the information provided, the question has two parts: Make an organized output of the…
Q: The concept of dynamic memory allocation is broken down for the layman.
A: The act of assigning a process's physical or virtual memory address space on a computer's hard drive…
Q: Packet switching is used in the world's oldest and most well-known (wired) communication network:…
A: Packet switching is a method of transmitting data over a network by dividing it into small packets…
Q: What are the pros and cons, from the perspective of the programmer, of frequent OS upgrades?
A: Operating system (OS) upgrades refer to the process of updating an operating system to a newer…
Q: Which three (3) of practices are core principles of zero trust? (Select 3) a. Continuously verify b.…
A: A security system based on zero trust implies that all network traffic, devices, and users are…
Q: Complete the method “readdata”. In this method you are to read in at least 10 sets of student data…
A: The task is to complete three methods - "readdata", "printdata", and "printstats" in the Java…
Q: Ask the user for a filename. Display the oldest car for every manufacturer from that file. If two…
A: Introduction : It seems that the code you provided is missing the input file car-list-3.txt, which…
Q: perfonth the hoang ootyorion that dapioy The progra Ask the midde inal and last nam wrOodstudent of…
A: Your solution is given jn next step
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- how adversaries can exploit trusted vendor-to-consumer relationships and describe how they violate the CIA triad by providing an example of this happening (who, what, where, why, when, etc.). For instance, the NotPetya attack compromised an Ukranian tax accounting software called M.E. Doc then used it to spread malware onto every company that used this software. In another example, Target was hacked through a trusted contractor's system who was responsible for managing its HVAC system. If possible, provide examples where your APT actors has abused a trusted relationship to gain access to systems or stolen information from the managed security service providers (MSSPs) (sometimes just MSP) to enhance its evasion techniques. Alternative, a software supply chain attack would also count as a "trusted relationship". Note: a data breach does not count as a trusted relationship and will result in a score of 0 for the posting if you elect to use this as an example.For the purpose of this…1. What methods does a social engineering hacker use to gain information about a user’s login ID and password? How would this method differ if it targeted an administrator’s assistant versus a data-entry clerk? 2. Consider the information stored in your personal computer. Do you currently have information stored in your computer that is critical to your personal life? If that information became compromised or lost, what effect would it have on you? 3. There are a number of professional organizations for computer security. Search for two organizations and share the websites and descriptions of those organizations. Share that information here:4. Choose two of the US federal agencies listed in Chapter 3 that deal with computer/cybercrime. List at least three differences, in terms of reach or responsibility, between the two organizations.Q.1.1Using suitable examples, discuss how you would use the three information security layers to secure a student information database for a College.Q.1.2Using suitable examples. differentiate between two types of malware that have the primary trait of circulation. In your answer, justify why these types of malware are considered most problematic compared to others using examples.Q.1.3Describe how the ARP poisoning attack can be used for the actions in (A-C) below using examples:A. Prevent Internet access.B. Steal data. Please help. Thank you
- Given the following data records that includes the employee’s full name, Job, and the salary. The institute has decided to award the instructors a bonus of 200 due to their efforts during the pandemic.Adam Saleet,IT Support,1000Naji Shemmari,Registrar,1250Bilal Tweijari,Instructor,2000Abdallah Mazem,Accountant,1000Nizar Hachem,Instructor,1800Nawwara Sleiman,Admission,900Ameen Sinjer,QA Officer,1400Walaa Saeed,Instructor,1900Hamid Shami,IT Support,850Nadine Khattar,Instructor, 1480Using “csv”, “table_utils”, and “statistics” libraries, you are asked to do the following:a- Create a text file, SP21-Emp1.txt, and copy the above contents to it.3b- Write a python program that does the following:1- Read the contents of the file SP21-Emp1.txt into a list.2- Extract the salaries into a new list.2- For each instructor, you should add 200 to their salary.3- Each name should also be split into first and last.4- Using “statistics” library, calculate the mean and median of the salaries.5- Print the…While SMIS are presented as a benefit to businesses and consumers, they also have a dark side. Read the attached article titled “The Case for Investigating Facebook” by David N. Cicilline, a member of the House of Representatives and chairman of the House Subcommittee on Antitrust, Commercial and Administrative Law, and discuss. A year ago, the world learned that Facebook allowed a political consulting company called Cambridge Analytica toexploit the personal information of up to 87 million users, to obtain data that would help the company’s clients“fight a culture war” in America.Since then, a torrent of reports has revealed that the Cambridge Analytica scandal was part of a much broaderpattern of misconduct by Facebook.It has paid teenagers to spy on their behavior, even asking users “to screenshot their Amazon order history page,”according to the website TechCrunch. The company has secretly collected highly sensitive data through the backdoors of other apps, such as ovulation…According to Microsoft’s estimate, in 2014 about one half if all adults connected to the internet were victims of cybercrime. This costs the world economy 500 billion dollars; 20% of all small and medium- sized enterprises (SMEs) have been hit. These estimations are confirmed by Merrill Lynch Global Research, who, in a 2015 report, also predict a potential “Cybergeddon” in 2020, when cybercrime could extract up to one-fifth of the value generated by the Internet. As far as the African continent is concerned, there are fewer available data this shows the absence of measuring tools and of control of cybercrime. However, and to serve as an illustration: a study conducted by International Data Group Connect showed that each year, cybercrime cost the South African economy an estimated 573 million dollars. For the Nigerian economy the cost was estimated to be 500 million dollars, and for the Kenyan economy, 36 million dollars. Proportionally speaking, for middle income countries this…
- According to Microsoft’s estimate, in 2014 about one half if all adults connected to the internet were victims of cybercrime. This costs the world economy 500 billion dollars; 20% of all small and medium- sized enterprises (SMEs) have been hit. These estimations are confirmed by Merrill Lynch Global Research, who, in a 2015 report, also predict a potential “Cybergeddon” in 2020, when cybercrime could extract up to one-fifth of the value generated by the Internet.As far as the African continent is concerned, there are fewer available data this shows the absence of measuring tools and of control of cybercrime.However, and to serve as an illustration: a study conducted by International Data Group Connect showed that each year, cybercrime cost the South African economy an estimated 573 million dollars. For the Nigerian economy the cost was estimated to be 500 million dollars, and for the Kenyan economy, 36 million dollars.Proportionally speaking, for middle income countries this represents…In 2018, the credit rating agency Equifax disclosed a major data breach involving the personal information of nearly 150 million people. Although Equifax's internal policy required patching critical vulnerabilities within 48 hours, a vulnerability was left unpatched for about 2 months. This was the vulnerability that was exploited by hackers to gain access to the system and obtain the personal information. In this exercise, you will analyze the Equifax incident and consider how the RMF could have helped Equifax prevent the incident. Carefully review this report and identify two vulnerabilities from different organizational levels, such as one vulnerability from Level 3 and one vulnerability from Level 1 or 2. Now think about the seven steps of the RMF. Summarize how these steps could have helped Equifax prevent or mitigate the vulnerabilities you identified. Identify at least one step for each vulnerability.Correct answer will be upvoted else downvoted. William comprehends that with all his activities he draws in increasingly more consideration from the trade's security group, so the number of his activities should not surpass 5000 and after each activity no factor can have a flat out esteem more noteworthy than 1018. William can perform activities of two kinds for two picked factors with files I and j, where i<j: Perform task ai=ai+aj Perform task aj=aj−ai William needs you to foster a system that will get every one of the interior factors to the ideal qualities. Input Each test contains numerous experiments. The main line contains the number of experiments t (1≤t≤20). Portrayal of the experiments follows. The main line of each experiment contains a solitary even integer n (2≤n≤103), which is the number of interior factors. The second line of each experiment contains n integers a1,a2,… ,an (1≤ai≤109), which are beginning upsides of inside factors. Output…
- . Choose a publicly traded security for which you can find a series of historical values. Make a conjecture about related data (at least two data series), that might be used as predictors for this series of values. Find online data sources to get current data for both the predictors and the values of the security (up to 12/31/20 or more recent, if possible) Download this data and copy it into Excel, Create graphs of the data . Use Excel to conduct a regression of the values of the security against the predictors and verify the validity of underlying assumptions eliminate outliers if necessary, check for homoscedasticity and serial correlation, look for evidence of multicollinearity and eliminate redundant predictors if necessary . Submit written report & Excel spreadsheet, Report can be .doc or .pdf. Document regression inputs with text comments, Report should clearly state the conjecture being investigated, clearly describe the data sources used & data handling, include links…Human error or failure can be described as acts performed without intent ormalicious purpose or ignorance by an authorised user.Considering the statement above, discuss how social engineering is one of the actsthat necessitate the need for information security for any finance industryorgansiation. In your answer, you must state what social engineering is and use anytwo types or forms of social engineering in the context of information security asexamples.In its role regarding the Secure Freight Initiative, the Department of Energy: A. Provides a backup electrical generating system for all US ports of entry to make sure all cargo is inspected in all emergencies B. Monitors all computer components being imported into the country C. Provides funding for radiographic equipment used in scanning cargo D. All of the above Which of the following systems calls upon competing agencies to work in a unified way without battles over territory or responsibility? A. The National Association of Mayors B. The National Governors Association C. The Incident Command System D. The Span of Control System

