How many line(s) that you need to change in the following code to make the queue a priority queue? #include #include using namespace std; void showq (queue gq) { queue g = gq; while (!gq.empty()) { } cout << endl; } int main() { cout << gq. front () << " gq.pop(); queue gquiz; gquiz.push(10); gquiz.push (20); gquiz.push(30); cout << "The queue gquiz is : "; showq (gquiz); return 0; Answer:
How many line(s) that you need to change in the following code to make the queue a priority queue? #include #include using namespace std; void showq (queue gq) { queue g = gq; while (!gq.empty()) { } cout << endl; } int main() { cout << gq. front () << " gq.pop(); queue gquiz; gquiz.push(10); gquiz.push (20); gquiz.push(30); cout << "The queue gquiz is : "; showq (gquiz); return 0; Answer:
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter18: Stacks And Queues
Section: Chapter Questions
Problem 21SA
Related questions
Question
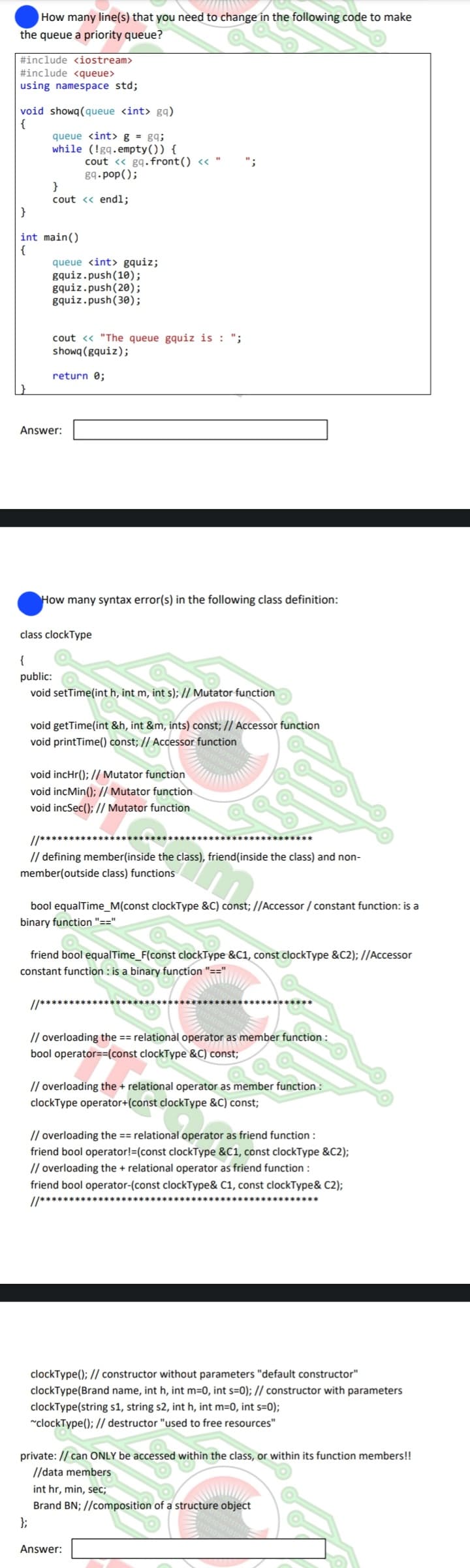
Transcribed Image Text:How many line(s) that you need to change in the following code to make
the queue a priority queue?
#include <iostream>
#include <queue>
using namespace std;
void showq (queue <int> gq)
{
queue <int> g = gq;
while (!gq.empty()) {
}
cout << endl;
}
int main()
{
cout << gq. front () << "
gq.pop();
queue <int> gquiz;
gquiz.push(10);
gquiz.push (20);
gquiz.push(30);
cout << "The queue gquiz is: ";
showq (gquiz);
return 0;
Answer:
How many syntax error(s) in the following class definition:
class clockType
{
public:
void setTime(int h, int m, int s); // Mutator function
void getTime(int &h, int &m, ints) const; // Accessor function
void printTime() const; // Accessor function
void incHr(); // Mutator function
void incMin(); // Mutator function
void incSec(); // Mutator function
//*******************
// defining member(inside the class), friend(inside the class) and non-
member(outside class) functions
***********
bool equalTime_M(const clockType &C) const;//Accessor / constant function: is a
binary function "=="
friend bool equalTime_F(const clockType &C1, const clockType &C2); //Accessor
constant function is a binary function "=="
//**********
// overloading the == relational operator as member function:
bool operator==(const clockType &C) const;
// overloading the + relational operator as member function:
clockType operator+(const clockType &C) const;
// overloading the == relational operator as friend function:
friend bool operator!=(const clockType &C1, const clockType &C2);
// overloading the + relational operator as friend function :
friend bool operator-(const clockType& C1, const clockType& C2);
//******
clockType(); // constructor without parameters "default constructor"
clockType(Brand name, int h, int m=0, int s=0); // constructor with parameters
clockType(string s1, string s2, int h, int m=0, int s=0);
~clockType(); // destructor "used to free resources"
Answer:
private: // can ONLY be accessed within the class, or within its function members!!
//data members
int hr, min, sec;
Brand BN; //composition of a structure object
};
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning