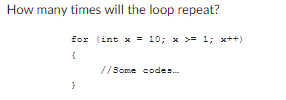
How many times will the loop repeat? for (int x = 10; x< { } //Some codes.... 1; x++)
Q: What programming paradigms exist? Why so many paradigms? Need they? Talk about it in your own words.
A: Programming paradigms are a classification scheme for programming languages based on their…
Q: Transfer times across memory tiers may be reduced by using buffers. In this case, what buffers are…
A: Introduction: The L 2 cache is valuable here despite being slower than the L 1 cache but much more…
Q: A. B. What is the ciphertext of M=9 if Alice chooses the random integer k=4? If Alice uses the same…
A: The answer is
Q: Explain what this code is doing $.ajax({ beforeSend: function() {$("#team").html("Loading...");),…
A: The question is to select the correct option for the given question.
Q: A good investigative tool for any help desk professional is a list of four questions to ask a client…
A: Desk Professional: A help desk specialist is someone who juggles technical proficiency and customer…
Q: aScript resources does the Browser Object Model provide access to?
A: the answer is an give below :
Q: What do the SPEC CPU benchmarks improve upon that the Whetstone, Dhrystone, and Linpack don't?
A: Answer: We have explain in more details point on SPEC CPU benchmarks, Whetstone, Dhrystone, and…
Q: Create a list of four obstacles to healthy hearing, two external and two internal.
A: Efficient listening skills: A strategy known as "effective listening" is one in which the listener…
Q: Analyze the strengths and weaknesses of Ghana's educational information systems in light of the…
A: Benefits: The Ghana Education Service has announced the opening of an online learning environment…
Q: Alice and Bob use the ElGamal scheme with a common prime q = 131 and a primitive root a = 6. Let…
A: Alice and Bob use the ElGamal scheme with a common prime q= 131 and a primitive root a = 6. Let…
Q: Which protocol—SSL or TLS—is used to secure browser-to-webserver connections?
A: SSL- SSL represents Secure Sockets Layer. It is an ancestor to TLS. All the versions of SSL are…
Q: How many times will the loop repeat? for (int ctx = 0; ctx < 10; ctx ++) { } //Some codes....
A: The solution to the question is given in the below step
Q: During the 17th century, gambler de Méré asked Blaise Pascal an explanation for his game losses. His…
A: we can perform faster multiplication of polynomials using the Karatsuba algorithm (O(n) time…
Q: There is a little danger while using SSTF disk scheduling.
A: Disk scheduling method SSTF: The technique known as SSTF, or Shortest Seek Time First, is used to…
Q: Why was the RISC architecture idea developed?
A: introduction: architecture RISC In the latter half of the 1970s, IBM researcher John Cocker and his…
Q: Is the vacation daemon part of the user agent or the message transfer agent? Of course, it is set up…
A:
Q: I'm stumped on how to define the scope and organization of a technical report.
A: how to define the scope and organization of a technical report answer in below step.
Q: When passwords are used for authentication, how might a remote attacker (also known as a client…
A: Please refer below for your reference: When passwords are used for authentication, how might a…
Q: Why was the RISC architecture first proposed?
A: RISC architecture having set of minimal instruction that can run all the essential operation. For…
Q: 1. Discuss why passwordless authentication are now preferred more than password authentication…
A: Disclaimer: “Since you have asked multiple questions, we will solve the first question for you. If…
Q: Microsoft Excel provides some alternatives to consider. Provide an explanation of how the following…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Prim's MST uses a weighted network.
A:
Q: What makes these passphrases good or bad, please? F., Tv9stove, Aristotle, and Washington D.C
A: Washington Unsuitable: The provided password is the location's name, which is readily guessed. The…
Q: Do you think mistake correction boosts the performance of wireless applications? Dot your argument…
A: The Answer start from step-2.
Q: Sort the many DNS record kinds into reasonable classifications. Give a succinct explanation of each…
A: Group the various DNS: Record types into sensible categories. Briefly describe each one, giving…
Q: There has to be a system in place for categorizing DNS records. Using the above examples, please…
A: The DNS records are: DNS records, also called "zone files," on authoritative DNS servers give the IP…
Q: To what extent does SIMD benefit from data or control parallelism? Where does MIMD shine in terms of…
A: Parallelism at the program level refers to the process of decentralizing a single program and…
Q: There are now two competing schools of thought when it comes to the kernel of an operating system.
A: The above question is solved in step 2 :-
Q: Let T be the Turing machine defined by the following 5-tuples: (s0, 0, s1, 0, L) (s0, 1, s1, 0, L)…
A: The Turing machine is the mathematical model which consists of the infinite length tape divided into…
Q: Is it possible that linking offline and online with intelligent technology might compromise privacy?
A: Given: Next the discussion of equality and development above, the tone of the observations in the…
Q: Write a class that tests and demonstrates that your Candidate and Election classes implement the…
A: The code for the above given question is given below:
Q: Why do we utilize MATLAB to tackle issues in computational geometry?
A: For tasks like deep learning and machine learning , signal processing and communications , image and…
Q: Modular and procedural programming ideas.
A: The question has been answered in step2
Q: 1) Is the following an AVL tree? 2) For each node provide the balance (Balance is the difference…
A:
Q: What aspects of information system architecture contribute to scope creep?
A: INTRODUCTION Information System Design will be utilized to complete the venture. An undertaking is…
Q: During the 17th century, gambler de Méré asked Blaise Pascal an explanation for his game losses. His…
A: Using the following logic, the self-styled Chevalier de Méré reasoned that the two were…
Q: Why isn't runlevel 6 the default or reboot.target the default target?
A: rented was added to all filesystems except '/' to mount automatically at bootup. This fixed the…
Q: Suppose the game is programmed so that the computer uses a binary search strat- egy for making its…
A:
Q: SIMD works better with data- or control-level parallelism, although either may be employed. MIMD…
A: Program-level parallelism: Parallelism at the program level refers to the decentralization and…
Q: Notify the user that virtual machine instruction sets are not supported.
A: Introduction: The number of instructions that must be performed and the time required to imitate the…
Q: Explain how caching works in shared memory.
A: This question asked how caching works in shared memory. What is caching? In a computer system, the…
Q: Identify at least 10 primary categories of network failures.
A: The Top 10 Network Error Are: The absence of internet connectivity is typically the source of…
Q: 1. An abstract class called Pet is defined below: public abstract class Pet { private String id;…
A: The question is to write the JAVA code for the given problem.
Q: How and when to utilize implicit heap-dynamic variables, as well as their benefits.
A: Introduction: When a value is assigned to an IMPLICIT HEAP-DYNAMIC VARIABLE, it is tied to heap…
Q: Let's say you're in need of a Windows Calculator replacement and are thinking about hiring a…
A: Statement of objectives (SOO): It offers a broad goal that forms the foundation of the statement of…
Q: Is it safe to use the SSTF disc scheduling method, and if not, why not?
A: find your answer below
Q: Modular and procedural programming ideas.
A: Modular programming Modular programming (sometimes known as modular architecture) is a general…
Q: What ethical and social impacts do robots and Al have? Would making all jobs robot-friendly make our…
A: The promise of social robotics is that, in the near future, we will be able to have a lasting…
Q: - For the given IP address 196.62.146.174/25, answer the following questions: Subnet Mask Number of…
A: Subnet Mask:- 255.255.255.0 Number of Subnets:- 2 Block-size for the subnet mask:- 128 Valid…
Q: Q2) PDA for language de eq 20 n, um a b CL n, m, p, q>0, n=9; m=p² L-1 a
A: The pushdown automata reads the given input string from left to right. In the each step, it chooses…
Step by step
Solved in 2 steps with 1 images

- Because it is repeated so many times in the code, the statement or block of an endless loop is known as an infinite loop's block.Java - Write a method that uses a loop to figure out the factorial (n!). The method will take an integer n and return the value of n! (return answer, don’t print)What, in your opinion, is wrong with this nested for loop? for(int x = 0; x < 10; x++){ for(int x = 10; x > 0; x--){ System.out.println(x); } }
- JAVA program Write a while loop that prints all the even numbers from 1 to 100 (inclusive). and another while loop to print all the odd numbers from 1 to 100 (inclusive).How many time will the loop run? for( int i = 18 ; i < 65 ; i++ ) { }(Python) Which is the correct answer? This loop is best when you want the loop to run X amount of times. a. loopX b. while c. for d. do while
- Consider the following code segment. What is the value of i and sum2 after the for loop completes? int sum2 = 0, i = 0; for (int i = 0; i < 5; i++) sum2 = sum2 + i; cout << "Sum is: " << sum2 << " i is: " << i << endl;The following code is an example of what kind of loop? int count = 0; while (count < 10) { count++; }How many times is the body of the loop executed? The numbers on left are line numbers. 1 int i=1; 2 while(true) { 3 if(++i==5) { 4 break; 5 } 6 } Group of answer choices 3 Forever 6 4 5 Please explain answer.
- What is the result of the following code? int xNum T 0; int yNum = 0; do { xNum = xNum+yNum; yNum += 1; cout << "xNum: } while (xNum > 2); << xNum; O a.xNum: 2 is printed O b. no output, the loop is never executed O c. xNum: 0 is printed O d. endless loopwrite a loop that will display numbers in reverse order from 20 to 0Check to see what happens if the for loop’s condition is incorrectly written using the <= operator in printHourlyCounts: for(int hour = 0; hour <= hourCounts.length; hour++)



