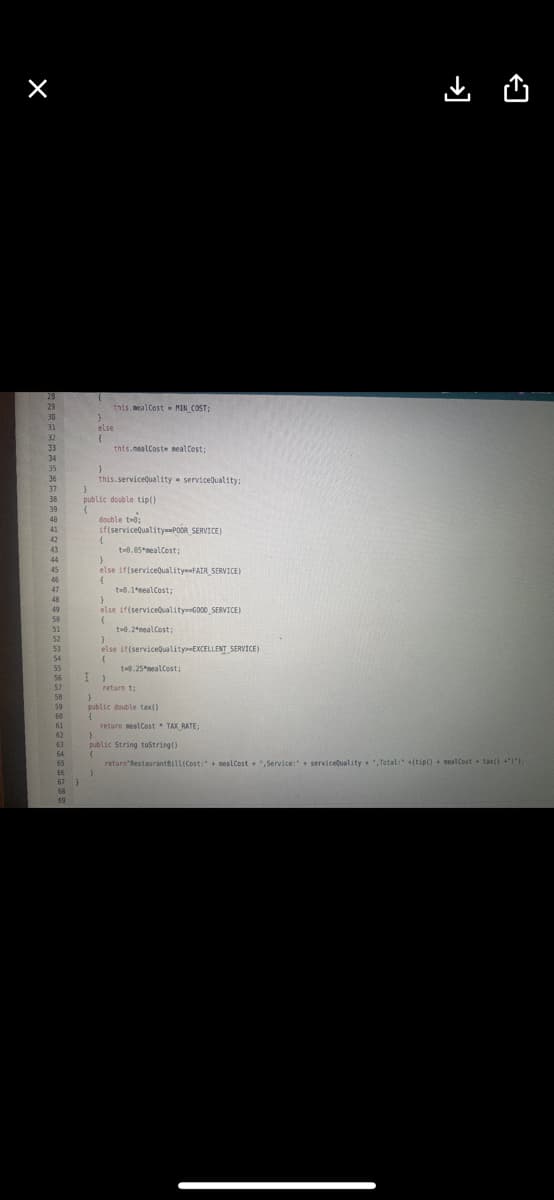
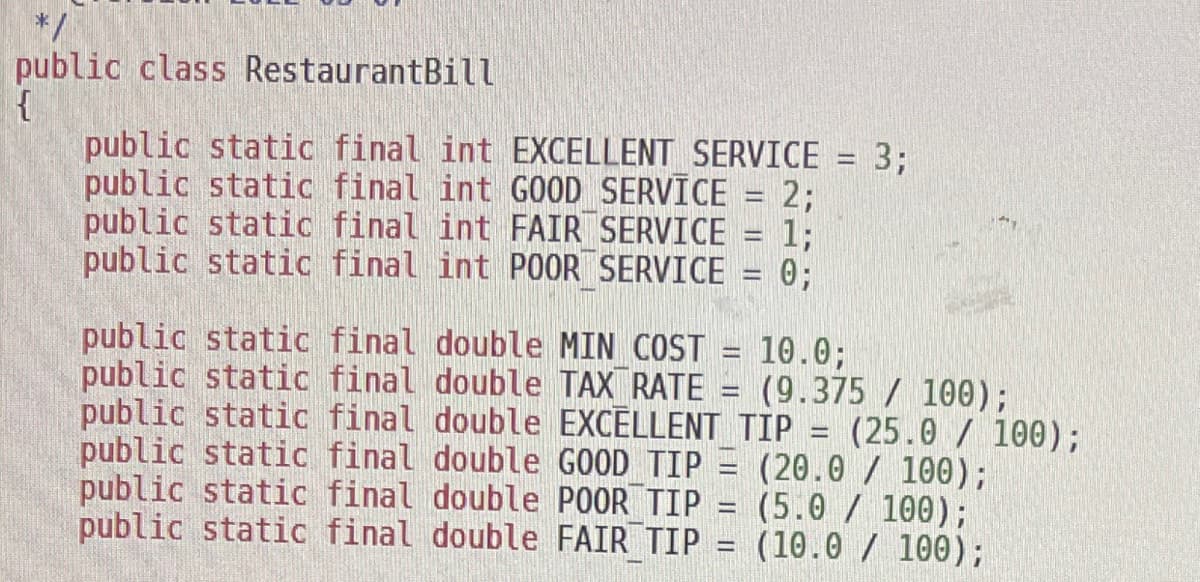
How to write the checking for if serviceQuality is too high or low in the constructor by in the information I grieved to you
Q: The problem can also be approached in a greedy way, based on the intuition that a camera in a locati...
A: Given :- The problem can also be approached in a greedy way, based on the intuition that a camera in...
Q: What is the difference between Apache Spark and Hadoop?
A: Apache web servers:- Apache web servers are acted as the main driving force behind the web expansio...
Q: Please keep the simulation neat and well organized. It is a request. NOTE: I AM ASKING FOR SIMULAT...
A: INTRODUCTION: QuickSort, like Merge Sort, is a Divide and Conquer algorithm. It selects a pivot ele...
Q: Use C++. Write a program that searches for a passage through the maze. The labyrinth is represented ...
A: Program Explanation- C++ program to solve Rat ina Maze problem using backtracking. Maze size. A uti...
Q: y N
A: Here in this question we have given a logical network diagram and we have asked to find the boolean ...
Q: Artificial Intelligence - Local Search Starting from a randomly generated state of the 15-puzzle ga...
A: Artificial Intelligence - Local Search Starting from a randomly generated state of the 15-puzzle gam...
Q: Simplify using DeMorgan's theorem A + BC + D (E + F)
A: The De Morgan's theorem:
Q: Routers are typically found in O The network edge O The access ISP O The network core Institutional ...
A: A router is a device which connects ISP and users by sending or receiving data.
Q: Because no wireless networks for the air interface between phones, antennas, and cell towers are ava...
A: In a cellular network, a cell, cell tower, or cell station is a cell-powered cellular facility where...
Q: The following is necessary when multiple users access/modify the database simultaneously. A) Dist...
A: When multiple users access/modify the database simultaneously, many problems may occur. The lost up...
Q: One of the advantages of a pie chart is that it shows that the total of all the categories of the pi...
A: According to the question the best pie chart only create when you add up to the 5-6 category only do...
Q: ate class methods (Setters and Getters) that load the data values. The Setter methods will validate ...
A:
Q: Print the two strings, firstString and secondString, in alphabetical order. Assume the strings are l...
A: import java.util.Scanner;class OrderStrings { public static void main(String [] args) { Scann...
Q: Entity-relationship model is used for designing databases. True or False?
A: About entity relationship model: ===================================================================...
Q: In computer networks, what is the value of an IP address?
A: Introduction: IP addresses may identify your computer, a favourite website, a network server, or eve...
Q: mputes and returns the smallest positive integer n for which 1+2+3+...+n equals or exceeds the value...
A: Lets see the solution.
Q: Convert the following expression into infix: abc-+de-fg-h+/* (without using stack) +a-bc/-de+-fgh (...
A:
Q: Write a simple week log about a project in computer science
A: Introduction: There are few steps before starting on a project: Have to know what exactly you want...
Q: A known distribution company intends to reward it deserving employees with a bonus only for sales ag...
A: According to the question , A known distribution company intends to reward it deserving employees wi...
Q: 10/M* = 0 for a memory read bus operation.
A: IO/M* is one of the operation in microprocessor that shows the status and signal
Q: ne cool.com le ile /home/kdun
A: MODULE 1 - NETWORKS TODAY1.0.5 Packet Tracer - Logical and Physical Mode Exploration Objectives Par...
Q: In microcontroller configuration, which one is preferable? (active low or active high) Why? Q2)
A:
Q: mean when you say
A: When an EC2 instance is stopped: When an EC2 instance is shutdown and cannot be used, then it is in ...
Q: Describe the key characteristics of data. What is their function in computer security research?
A: Introduction: The purpose of computer security (cybersecurity), cybersecurity (cybersecurity), or in...
Q: Determine the communication technique of the wireless local area network.
A: Introduction: WLAN technology is utilised in certain circumstances to save money by avoiding the ins...
Q: (a) Show the internal representation (box-pointer diagram) of the LISP list as obtained below: > ( l...
A:
Q: Which type of language contains commands like this? xor eax,eax A. Machine Code B. Interpreted Langu...
A: Answer : D. Low-level Language
Q: Why would you put two power supply in a mission-critical server?
A: It has two power sources: It is a standard piece of equipment in electronic circuits, and each one r...
Q: Identifying Network Exploitation Malicious Services: explains the first service running, if it w...
A: A denial-of-service (DoS) assault happens when a hostile cyber threat actor prevents legitimate user...
Q: Write a program to create Teacher class and enter data through keyboard. Create another class Studen...
A: 1)Create class Teacher with two variables to store teacher name and subject teaches 2)In class Tea...
Q: sum(n) if n=0 return; return n+ sum(n-1) store intermediate values build a bottom up solution
A: Bottom up solution approaches from bottom to end by calculating intermediate values.
Q: In how many ways the data is represented and what are they?
A: Introduction: A name, a number, the colors in an image, or the notes in a musical composition are al...
Q: Is the SSL protocol enough to ensure network security?
A: Introduction: SSL is fantastic, but it is simply insufficient. Interception of data packets passing ...
Q: Distinguish between DNS record types. Give examples and arguments for utilising each one. Is it feas...
A: Intro DNS Types: Address Mapping record (A Record)—also known as a DNS host record, stores a hostnam...
Q: Q1: Implement a class called House. a) A class named House b) Two private data members: location (st...
A: C++ code to implement class House #include <bits/stdc++.h>#include <iostream> using nam...
Q: I want to move all the vowels of a user entered string to the left side and move all the consonants ...
A: Here in this program we are asked to print vowels on left hand side and consonant on the right hand ...
Q: In the constructor, your web server's RequestHandler class has been set up. Every time a client is c...
A: This library is aimed to make TCP/IP and Client/Server programming so easy. With its multi-threaded ...
Q: 16.3 What difference does the order of the two numbers a and b make when we calculate their greatest...
A: Greatest common divisor using the euclidean algorithm a and b are the two numbers.
Q: What benefits has Vivobarefoot gained as a result of its infrastructure upgrade?
A: Introduction: Vivobarefoot is a shoe company that has gained a lot of attention in a short period of...
Q: n range (ncol): if((i%2==0) and (i<ncol-1) a
A: According to the information given:- We have to follow the instruction mentioned to perform and get ...
Q: A = {1,3,7,9,10} , and let R be the relation on A defined by x < y', {(x, y) e A:x² < y} Write R as ...
A: Here in this question we have given a set A{ 1,3,7,9,10} and a relation is defined as x^2 <= y. W...
Q: Design a complete GUI Application with as many components as combination of different layout Manager...
A: Given Laboratory 4 GUI (Graphical User Interface) in Java Cont... Activity 1: Design a complete GUI ...
Q: A known distribution company intends to reward it deserving employees with a bonus only for sales ag...
A: HI THEREI AM ADDING LOGICAL FUNCTION BELOWPLEASE GO THROUGH IT THANK YOU
Q: JAVA PROGRAM Can You Please describe the method overloading on the subtraction of two numbers. Progr...
A: Method Overloading : When a class has many methods with the same name but distinct parameters. The r...
Q: What security countermeasures could you apply to keep an eye on your SQL databases in case they're b...
A: The following security countermeasures were utilized to keep an eye on the production SQL database f...
Q: Write out the POWER SET. Keep in mind a subset can be made of any combination of elements appearing ...
A: The power set is a set that contains all of the subsets, as well as the empty set and the original s...
Q: What distinguishes materialised views from other perspectives?
A: Introduction Materialized View – In SQL, the materialized view is stored on the physical disc and ...
Step by step
Solved in 4 steps with 3 images

- A company supplies a range of cosmetic products and gives discounts on orders as follows: For orders worth less than $50 a discount of 2% is given. For orders worth $50 and over a discount of 5% is given. These discounts are only given if the customer’s account is less than four weeks in arrears. If the account is more than eight weeks in arrears a pro forma invoice must be sent and settled before dispatch. Prepare a limited entry decision tableThe following table shows the rate of commission that will be paid to the salesman according to the total sales performance of the month:Total Sales Performance (RM) CommissionLess than 10000 No commission10000 – 20000 1% of the total sales20001 – 30000 2% of the total sales30001 – 40000 3% of the total salesMore than 40000 4% of the total sales Lastly, display the salesmanName, totalSalesPerformance,totalCommission and totalSalary.Ex1. Dorm, Meal Plan, and miscellaneous options Calculator: A university has the following dormitories:• Allen Hall: $1,800 per semester• Pike Hall: $2,200 per semester• Farthing Hall: $2,800 per semester• University Suites: $3,000 per semester The university also offers the following meal plans:• 7 meals per week: $600 per semester• 14 meals per week: $1,100 per semester• Unlimited meals: $1,800 per semesterThe university also offers the following miscellaneous options:• Use laundry room: $80 per semester• Use paid-parking areas: $100 per semester• Use in-city school buses: $60 per semester Below is the to-do list:Create an application with the following controls1. the names of the dormitories (i.e. ComboBox controls)2. the meal plans (i.e., RadioButton controls)3. the option list (i.e., Checkboxes). 4. other required controls (e.g., labels, button)5. plus a stylesheet which will set the label control’s font size to 16 when the app…
- Which would be the best way to use the IFS built-in function to determine each employee’s status based on the number of projects they have completed? IFSEmployee.PNG Group of answer choices =IFS(B230,"Junior",B250,"Senior") =IFS(B2>20,"New",B220,"New",B2>30,"Junior",B2>40,"Experienced",B2>50,"Senior") =IFS(B2Cozy Inn is a low-cost family accommodation in a New Zealand resort town. Cozy Inn reception is open 24/7. Reception desk staff take bookings over the phone and in person. Rooms at Cozy Inn are large, family-style rooms. There are tea-making facilities in each room. Breakfast is served to all the occupants. At the time of check in, reception desk staff ask the customers to choose the breakfast menu option for the duration of their stay. This information will be noted in a spreadsheet. At 6.00 am every day, a printed copy of this spreadsheet will be given to the kitchen staff.The current business is using a simple informative website, a workstation, five desktops, three laptops and two network printers that are all connected using a small local area network (LAN) in the reception office. 1.Identify and briefly discuss three main issues that Cozy Inn could face in the absence of an information system to integrate the business processes. 2.Discuss briefly how Cozy Inn can make use of…Cozy Inn is a low-cost family accommodation in a New Zealand resort town. Cozy Inn reception is open 24/7. Reception desk staff take bookings over the phone and in person. Rooms at Cozy Inn are large, family-style rooms. There are tea-making facilities in each room. Breakfast is served to all the occupants. At the time of check in, reception desk staff ask the customers to choose the breakfast menu option for the duration of their stay. This information will be noted in a spreadsheet. At 6.00 am every day, a printed copy of this spreadsheet will be given to the kitchen staff. The current business is using a simple informative website, a workstation, five desktops, three laptops and two network printers that are all connected using a small local area network (LAN) in the reception office 1.When the Cozy Inn decides to use online systems, what is the customer-related information that needs to be protected and what are the major ways by which they should protect individual privacy of…
- Cozy Inn is a low-cost family accommodation in a New Zealand resort town. Cozy Inn reception is open 24/7. Reception desk staff take bookings over the phone and in person. Rooms at Cozy Inn are large, family-style rooms. There are tea-making facilities in each room. Breakfast is served to all the occupants. At the time of check in, reception desk staff ask the customers to choose the breakfast menu option for the duration of their stay. This information will be noted in a spreadsheet. At 6.00 am every day, a printed copy of this spreadsheet will be given to the kitchen staff. The current business is using a simple informative website, a workstation, five desktops, three laptops and two network printers that are all connected using a small local area network (LAN) in the reception office. List and briefly discuss five of the business processes in the organisation.rick oversees Make Your Own Music, a business specializing in musical instruments such as guitars, drums, and synthesizers. Commission rates for staff are determined by sales at the store, with the following tiered rates: - 11% for sales under $10,000- 13% for sales between $10,000 and $14,999- 15% for sales between $15,000 and $17,999- 17% for sales between $18,000 and $21,999- 19% for sales of $22,000 or more. Employees have the option to withdraw up to $2,500 monthly from future commissions. Shortfalls in commission repayments must be covered by employees. The monthly pay formula is: pay = (sales * commission rate) - advanced pay. rick seeks a program to automate this process. The algorithm: 1. Obtain the monthly sales figure from the salesperson.2. Retrieve the amount of advanced pay taken by the salesperson.3. Determine the appropriate commission rate based on monthly sales.4. Calculate the salesperson's pay using the provided formula. A negative amount indicates repayment owed to…When a customer contacts the company to ask for an estimate, the proprietormakes a note of the customer’s contact details and an outline of the proposedwork. He agrees a date with the customer to view the property in order to givean estimate of the cost for the work. When visiting the property on the agreeddate the proprietor adds more detail to the outline of the proposed work. Within3 days of visiting the property the proprietor produces a fully detailed estimateand sends it to the customer. If the customer agrees the estimate, the proprietorschedules a date to start the job (this is based on the size of the job and otherjobs that have already been scheduled).A few days before the agreed start date of a job, the proprietor contacts thecustomer to confirm the start date, and then orders the required buildingmaterials from suppliers to be delivered on the date the job starts. At theend/completion of the job the proprietor calculates the actual cost of the job toproduce an invoice which…
- QUESTION 4 Order the following proctols from the most efficient to the least CSMA CSMA/CD Pure ALOHA Slotted ALOHAQuestion One (1) You participated in an evaluation of proposals for consulting services. At the end of the Technical Evaluation which required a minimum of 70 points, you got the following results: CONSULTANTS KANYIHAMPA MUSANGILA Technical Score 75.17 76.17 Amount USD475,000.00 USD625,000.00 The lowest evaluated financial proposal (Fm) is given the maximum financial score of 100. The formula for determining the financial score is as follows: SF = 100 x Fm /F in which SF is the financial score, Fm is the lowest price and F is the price of the proposal under consideration. The weights given to the Technical and Financial proposals are 80 and 20 respectively. Calculate for each consultant below (a – c): Weighted Technical score. Financial score Combined weighted Technical and weighted Financial score Indicate the best evaluated bidder and their pointsFind all employees in Dallas who make more than 3000 dollars in salary. EMP Table: Field --------------------------------------- EMPNO ENAME JOB MGR HIREDATE SAL COMM DEPTNO NUMBER(2) DEPT Table: Field ------------------------------- -------- -------------------------------------------------------------------- DEPTNO DNAME LOC



