i docs.google.com 5- A methodology used to verify that the
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter9: Supporting Mobile Devices
Section: Chapter Questions
Problem 9TC
Related questions
Question
What is the solution for this question (using networking)
Transcribed Image Text:ll touch ?
11:35 AM
@ 83%
a docs.google.com
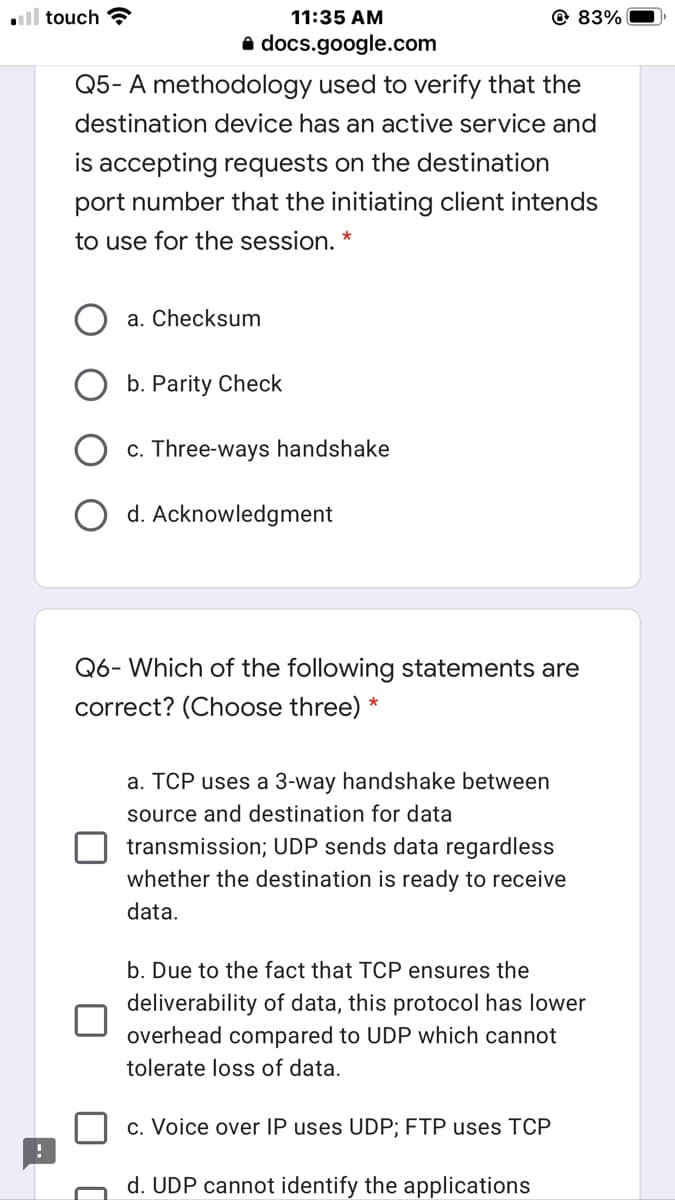
Q5- A methodology used to verify that the
destination device has an active service and
is accepting requests on the destination
port number that the initiating client intends
to use for the session. *
a. Checksum
b. Parity Check
c. Three-ways handshake
O d. Acknowledgment
Q6- Which of the following statements are
correct? (Choose three) *
a. TCP uses a 3-way handshake between
source and destination for data
transmission; UDP sends data regardless
whether the destination is ready to receive
data.
b. Due to the fact that TCP ensures the
deliverability of data, this protocol has lower
overhead compared to UDP which cannot
tolerate loss of data.
c. Voice over IP uses UDP; FTP uses TCP
d. UDP cannot identify the applications
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

Principles of Information Security (MindTap Cours…
Computer Science
ISBN:
9781337102063
Author:
Michael E. Whitman, Herbert J. Mattord
Publisher:
Cengage Learning