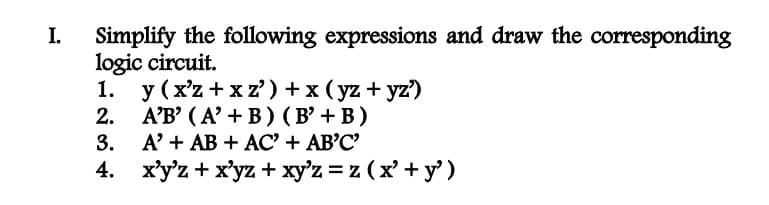
I. Simplify the following expressions and draw the corresponding logic circuit. 1. 2. 3. 4. y (x'z+xz') + x (yz + yz') A'B' (A' + B) (B' + B) A' + AB + AC' + AB'C' x'y'z + xyz + xy'z = z (x² + y')
Q: What does the term "connection status information" mean when applied to a virtual circuit network? A…
A: The answer to the question is given below:
Q: Memory Management Unit: What Is Its Function?
A: Introduction Viable memory management requires framework executives to reliably screen memory use…
Q: Understanding what mapping implies is essential for designing user interfaces. Is it feasible to…
A: User interface The user interface is the place where human users cooperate with a PC, site, or…
Q: Two columns are necessary in a datagram network, but four columns are required in a virtual-circuit…
A: Given: In a datagram network, there must be at least two columns; in a virtual-circuit network,…
Q: Leaner search Program in java
A: Leaner search Program in java :-
Q: In many ways, laptop computers and mobile devices seem to be very unlike. Your argument should be…
A: Introduction: The most obvious distinction between a mobile phone and a personal computer is their…
Q: How does a computer's operating system work?
A: The duties of an operating system in a computer system must be defined. Running System: A…
Q: Describe the Presidential Policy Directive / PPD 28, its impact in general on individual privacy…
A: The Presidential Policy Directive / PPD 28 is a directive that was issued by President Barack Obama…
Q: A source code file, an object code file, and an executable (or program) file are all separate.
A: Introduction A programming language is used by a programmer to create a program. This program is not…
Q: A main method can be placed inside a class definition. O True O False
A: BELOW ? COMPLETE SOLUTION REGARDING YOUR PROBLEM :
Q: What is the function of kernel mode in an operating system?
A: Please find the answer below :
Q: line 6, in original_list = range*l, r+1, 1 TypeError: unsupported operand type(s) for *: 'type'…
A: After updating the given code, I have provided PYTHON CODE along with OUTPUT…
Q: Looking at the evolution of the internet and the technological on which it is based may teach you a…
A: Consider the Internet's technological foundations and history.
Q: Consider the following method, what is the recurrence relation T(n) for the running time? int…
A: Given code :-
Q: Describe the key steps of the waterfall development paradigm.
A: Introduction: Model waterfall: Waterfall software development methodology is sequential. This…
Q: Describe the history of SNMP from its beginning and compare/contrast the features of the different…
A: Given: Describe the evolution of SNMP and compare/contrast the characteristics of the various…
Q: Choose the right answer from the list below. When we say "utilities," we mean things like word…
A: Introduction: Infrastructure software is used to maintain the computer infrastructure, as opposed to…
Q: In the context of systems thinking, how does the idea of "interdependence" differ from others?…
A: Introduction: International system interdependenceInterdependence is essential to understanding…
Q: Consider the NFA N₁ shown in Figure 1 over the alphabet Σ₁ = {0, 1}. 0 1 92 91 € X Figure 1: NFA N₁…
A: In this question we will find elements and transition state and further prove concatenation…
Q: What characteristics differentiate Doom from other video games?
A: In this question we need to explain the characteristics of Doom video game which are different from…
Q: The String class is a mutable class. O True O False
A: The solution is given in the next step
Q: Describe the key steps of the waterfall development paradigm.
A: Software is developed in a sequential manner using the waterfall model, which is a sequential…
Q: For instance, a data structure for which there isn't an array- or link-based solution. Exists a…
A: Introduction: In addition, a data structure can be defined as an algebraic structure that stores…
Q: This course will enhance your knowledge of cloud computing, social networking blogs, and a variety…
A: INTRODUCTION: Cloud computing: Processing in the cloud refers to the on-demand availability of…
Q: Write a java program that saves and displays the Student Record. • Ask the user to enter the data •…
A: Java Code: import java.util.Scanner; public class studentRecord { publicstaticvoidmain(String[]…
Q: What does the term "connection status information" mean when applied to a virtual circuit network? A…
A: A virtual circuit identity, or VCI, is tucked away in the header of each and every packet that…
Q: What are the design goals, During the design of the crete framework for binary-level concolic…
A: We have determined the following design objectives for the CRETE framework for binary-level concolic…
Q: Being an e-commerce executive at a local salon business, what E-commerce strategies can be…
A: Some benefits that could be obtained from these strategies include:1. Increased bookings and…
Q: The stack is the most frequent arrangement for the central processing unit (CPU) of a computer, but…
A: The answer to the question is that computers gathered CPUs in the early history of computers. The…
Q: Instructions Through legal and ethical means, locate three different physical networking…
A: The 3 types of physical network connections are Ethernet or copper cables, fiber optic cables, and…
Q: Consequently, event delegation types and components are used often in GUI programming. Why?
A: Models of delegation: The Delegation Event model is used by GUI programming languages to manage…
Q: Consequently, event delegation types and components are used often in GUI programming. Why?
A: Delegation Models: For the purpose of event handling in GUI programming languages, the Delegation…
Q: What steps should be taken to assure a local area network's dependability and availability?
A: The Answer is in step2
Q: In the context of System Analysis, what is a model? To differentiate between them, use logic and…
A: Model:- The definition of a data model is an abstract model that arranges data semantics,…
Q: 7) (a) Show work to find the 6 bit unsigned quotient and remainder of D/ B. (b) What is the decimal…
A: “Since you have asked multiple questions, we will solve the first question for you. If you want any…
Q: Write a program in C that creates a display similar to Figure 2.13.2. Table 2.13.2. A text string…
A: C is a popular general purpose language.It is used to create softwares like databases,compilers,OS…
Q: external fragmentation is caused by anything else.
A: In this question we will understand about the external fragmentation in operating system and how it…
Q: The following are three critical processes in testing a commercial software system.
A: Software testers must pay attention to details to do their jobs well. This is complex and…
Q: JAVA CODE PLEASE Recursive Functions Practice ll by CodeChum Admin Create a recursive function named…
A: Introduction: In this question, we are asked to write a JAVA program to print the factorial of user…
Q: Write down your results and include examples to back up your differentiation between the functional…
A: Solution:- functional requirements: non functional needs: Describe the functions performed by the…
Q: There are three methods for doing user testing.
A: Software Testing:- A software product or application is tested in order to determine whether or not…
Q: To fully comprehend RAID 5, we must first learn more about the technology. When is RAID 5 superior…
A: Introduction: RAID 5 uses equal-circle-striped self-contained plates.Information and equality are…
Q: Unlike datagram and virtual-circuit networks, circuit-switched networks do not need a routing or…
A: In this question we need to explain if in case of datagram or virtual switching networks switching…
Q: Examine the development of the internet and its technological roots.
A: INTRODUCTION: Internet: The internet serves as a way for different networks to share information.…
Q: What are The Use of LySP Services?
A: To ingest documents into the system, the following tasks are performed: (1) convert files into Lynx…
Q: Choose the right answer from the list below. When we say "utilities," we mean things like word…
A: Choose the right answer from the list below. When we say "utilities," we mean things like word…
Q: what if I don't wont use import math in my code
A: After updating the program , I have provided PYTHON CODE along with CODE SCREENSHOT and…
Q: For hiking on the trail to be safe, it is necessary and sufficient that mangoes not be ripe along…
A: given p: wild pigs have been seen in the area q: hiking is safe on the trail. r: mangoes are ripe…
Q: Consider how the internet has changed over time and how it is reliant on existing technological…
A: Introduction: Current objective is to present an Internet history.Two computers at MIT Lincoln Lab…
Q: Which event delegation model do we chose for GUI development, and how do we implement it? Specific…
A: Introduction: The delegation event model provides a set of uniform and standardised methods for…
Answer #2
Step by step
Solved in 4 steps with 3 images

- (Mechanics) The deflection at any point along the centerline of a cantilevered beam, such as the one used for a balcony (see Figure 5.15), when a load is distributed evenly along the beam is given by this formula: d=wx224EI(x2+6l24lx) d is the deflection at location x (ft). xisthedistancefromthesecuredend( ft).wistheweightplacedattheendofthebeam( lbs/ft).listhebeamlength( ft). Eisthemodulesofelasticity( lbs/f t 2 ).Iisthesecondmomentofinertia( f t 4 ). For the beam shown in Figure 5.15, the second moment of inertia is determined as follows: l=bh312 b is the beam’s base. h is the beam’s height. Using these formulas, write, compile, and run a C++ program that determines and displays a table of the deflection for a cantilevered pine beam at half-foot increments along its length, using the following data: w=200lbs/ftl=3ftE=187.2106lb/ft2b=.2fth=.3ft1.) If f(x) = 2.x^2 - x + 5. What is f(-3)? 2.) If A = {a, b, d, e}, B = {b, c, e, f} and C = {d, e, f, g}. What is (A ∩ B) ∪ (A ∩ C)?2) Simplify the following Boolean expressions, using three-variable K-maps:F(x,y,z) = x′y′ + yz + x′yz′ PS:Please type instead of paper writing
- Please help with all of them and show work please Simplify the following expressions F(x, y, z) = xy + x’y’z’ + x’yz’ F(x, y, z) = x’yz + xy’z + x’yz’ F(x, y, z) = xy’z’ + xz + x’y’z F(w, x, y, z) =x’z + w’xy’ + w(x’y + xy’) F(w, x, y, z) =w’x’y’z’ + wy’z’ + x’yz’ + w’xyz + xy’z2. Given a boolean expression below, find the value of the expression if the values of P = 1, Q = 0, R = 1. Y = P.Q + Q.(R+P+Q)2. Look for the dual of the following Boolean expressions:a. xyz + x'y'z'b. xz' + x⋅0 +x'⋅1
- Write the robot program using the VAL+ for the following automation case. First draw the problem; then handwrite the VAL+ code. The robot picks up FIVE blocks of size 100x100x100 mm that are stacked at a fixed position and place them at the corners and center of a square table of size 500 x 500 mm. Select the original position on the table on your own.write a c++ program that creates all 4-digit combinations from 1 - 7 for example, the first combination should be 1 2 3 4... but instead of numbers, the output should be letters. for 1 = a, 2 = b, 3 = c, 4 = d, 5 = e, 6 = f, 7 = g and the output for 1 2 3 4 should be a b c d the output for 2 3 4 5 should be b c d e42. Consider the expression given below. The value of X is:X = 2+9*((3*12)-8)/10 a. 30.0 b. 30.8 c. 28.4 d. 27.2
- Keep the Diagram neat. Thanks. Implement the following boolean function using a) 16:1 mux b) 8:1 mux c) 4:1 mux F(A,B,C,D) =∑(0,1,2,7,8,10,11,13, 15)What is the output from the following print statement: print (1 / 3) print (10 + 3 * 7) print ((10 + 3) * 7) print ("Hi" + "there") print ("Hi" + 10) print ("Hi" + "10") Does e and f display the same result? Why? print ("Hi" * 10) print ("Hi" * "10") Does h and i display the same result? Why?1) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’yz+x’yz’+xy’z’+xyz+xyz’ , can be written as: 2) The simplified version of the Boolean function, F(x,y,z)= x’y’z+x’y’z+x’yz+x’yz’+xy’z’+xyz’ , can be written as: 3)convert the following decimal fractions to binary with a maximum of six places to the right of the binary point: 1)25.84375 2)57.55 3)80.9065 4) Convert the following binary fractions to decimal: 1)100001.111 2)111111.10011 3)1001100.1011 5) Fill in the blank. The representation of 60 in binary using 8-bit signed magnitude is ______, in ones complement is ______, in two’s complement is ______, and in excess-127 is ______.



