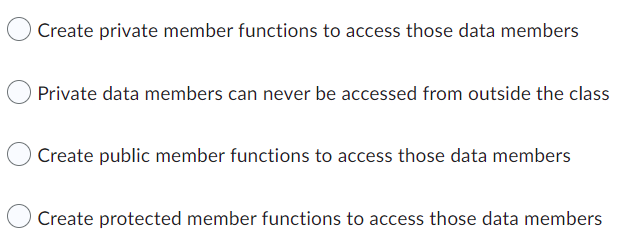
If data members are private, what can we do to access them from the class object?
Q: Given the language {a^n b^m where m>n}, create a 2 tape Turing machine that accept it.
A: language is given {a^n b^m where m>n},
Q: Which aspect should be defined for each class when creating a class diagram?
A: Class diagram is a static diagram. It represent the static view of an application. Class diagram is…
Q: If you think a real-time operating system is necessary, explain why in depth in three specific…
A: Real-Time Operating System: In particular, real-time operating systems may let you: Complete tasks…
Q: The software development life cycle (SDLC) and approaches now have a significant knowledge gap…
A: SDLC is a process, while Agile is a methodology, thus both SDLC versus Agile must be taken into…
Q: So, what exactly do you think of the email? One way or another, an email will get from A to B. Take…
A: This definition states that a mental model is an intuitive perception that a user has or develops…
Q: As a direct result of this, end users may choose to input data via the command line rather than…
A: Users may become adept at using a graphical user interface (GUI) much more rapidly than with a…
Q: Is it possible that the need for in-house systems analysts will decline as more companies outsource…
A: An individual applying analytical and design approaches to address business difficulties via…
Q: What are the shortcomings of "Wi-Fi Direct" technology?
A: Introduction: WiFi Direct Vulnerabilities: WiFi Direct now supports 802.11 WPA2 PSK for further…
Q: Give an example of a data structure for which there are no viable array or link-based solutions.…
A: Introduction: The carrying out, execution, or practise of a plan, technique, or any concept, idea,…
Q: A class plays a fishing game in which a large tub is filled with plastic fish that are identical,…
A: 1. Data in a dot plot:
Q: It is important to both describe and explain the major responsibilities associated with system…
A: Management of Information System(MIS): MIS is an acronym for Management of Information System. It…
Q: Interrupt: Explain why no hardware disruptions are foreseen fo
A: A interrupt is a sign from a gadget joined to a PC or from a program inside the PC that requires the…
Q: The process of making changes to a software product after it has been delivered in order to fix…
A: Complete the system shown below: After delivery, a software product may be modified to fix bugs,…
Q: How do I know if I'm deploying or publishing an application correctly?
A: Deployment is defined as the method of deploying the pre compiled DLLs to the IIS server. However,…
Q: It's important to provide tangible examples to explain the concept of a real-time operating system.…
A: Given: Operating systems designed for real-time applications must manage data and events crucial to…
Q: Give examples of each of the several types of security you may provide.
A: It protects data from unapproved access, theft, damage, disclosure, change, or destruction.…
Q: Define a real-time operating system using examples. How does this operating system differ from…
A: Operating systems designed for real-time applications must manage data and events crucial to the…
Q: In Betjemanian University, everyone has to enter his/her name on a computer when entering or leaving…
A: Input-Output The first line of the input contains an integer T denoting the number of test…
Q: Using real-world operating system examples might help illustrate the idea. What distinguishes this…
A: The Answer is given below step.
Q: How and why do we need structured programming in today's world? What are the most important concepts…
A: The paradigm of structured programming: Which is also known as standard programming, is a kind of…
Q: Do you think a data leak may have a big impact on cloud security? What dangers exist? Can anything…
A: Solution: Yes, it affects An unauthorised individual gains access to confidential, sensitive, or…
Q: A look at Windows Service Control Manager and its advantages will be discussed in this article.
A: Windows Service Control Manager: The Windows NT series of operating systems uses a specific process…
Q: An artificial intelligence (AI) system may be modelled using functional decomposition.
A: Introduction: This effectively breaks down the difficulty into a number of smaller, more manageable…
Q: Describe the variables that influence the dependability of software.
A: Answer:
Q: As a direct result of this, end users may choose to input data via the command line rather than…
A: The Command Line Interface which means it is the text based user interfaces where we used to run the…
Q: What precisely is an Interrupt? By discussing the various sorts of hardware disruptions, you may…
A: Introduction: An interrupt is an event that causes the processor's execution arrangement to be…
Q: What's Hiding Amongst the Crowd? Language - Java Script A word is on the loose and now has tried to…
A: Coded using JavaScript.
Q: In Betjemanian University, everyone has to enter his/her name on a computer when entering or leaving…
A: Input-Output Steps The first line of the input contains an integer T denoting the number of test…
Q: Write a SQL statement that will add the below row to the Task table.
A: Introduction: SQL is a standard language for querying to manipulate and access database information,…
Q: A routed firewall is logical node with an IP address, which segments the network like a normal…
A: The Answer is in step2
Q: The this pointer is accessible (i) Within all the member functions of the class (ii) Only within…
A: ‘this’ pointer is basically passed as a hidden argument to all nonstatic member function calls and…
Q: Describe the influence that software evaluation, control, and change methods have had on the amount…
A: INTRODUCTION: Program upkeep is the method of changing, adjusting, and upgrading program to keep up…
Q: assigns cell_count with cell_count multiplied by 10. * performs multiplication. If the input is 10,…
A: Given : Write a statement that assigns cell_count with cell_count multiplied by 10. * performs…
Q: Linux is an example of open-source software. Explain in your own words what open-source software is…
A: Open-source software:open-source software is a free and openly available for everyone These…
Q: Discuss in some detail the right technologies. Determine and explain how a particular piece of…
A: The term "appropriate technology" refers to any item, set of ideas, method, or practice that…
Q: 19. Perform the following twos complement arithmetic 10001101 10101 20. Please explain data hazards…
A:
Q: Using real-world operating system examples might help illustrate the idea. What distinguishes this…
A: Given: In this issue, we will examine the performance and reliability of real-time and traditional…
Q: How does information technology play a crucial part in modern organisations' communication…
A: Answer: Information technology plays a vital role in today's organizations in the area of…
Q: What is the memory allocation procedure? Distinguish between logical and physical addresses using…
A: Introduction: The memory allocation method provides real or virtual memory space to computer…
Q: The "Inference rules" are what? With specific examples, define "ahead chaining" and "reverse…
A: Filters.(Proof theory, logic)A rule for truth-pressingly combining (modifying) well-formed formulas…
Q: Why is testing insufficient to ensure correctness?
A: Introduction: Testing is the process of analysing a programme to see whether it is capable of…
Q: Distinguish between the existence of system calls and the absence of system calls in an operating…
A: Introduction: The operating system isn't expected to settle on framework decisions autonomously. At…
Q: In conclusion, provide five examples of how fuzzy logic is employed in engineering (especially in…
A: In boolean logic, calculations have two possible outcomes: a 1 or a 0. However, fuzzy logic is used…
Q: What are the implications of the shared responsibility paradigm and identity and access management…
A: Introduction: A shared responsibility model is a cloud security paradigm that establishes the…
Q: Before you begin writing code for a software, you must first design the application's user…
A: This can be done quickly by dragging the pointer down the wavy line. A statement is quickly checked…
Q: I would appreciate it if you could provide a comprehensive summary of the most important steps that…
A: The primary responsibilities of implementation: The process of developing the application begins…
Q: What exactly are the duties involved in maintaining a system?
A: Intro The capacity of a system to provide a service should remain in a functional state at all…
Q: Data storage and visualisation are two of the most important aspects of data management. Explain how…
A: Introduction: The data store is a repository that may handle both structured and unstructured data.…
Q: Why are some Internet search engine features and apps controversial in terms of privacy?
A: Introduction: It is described in informational privacy as data or information meant to be kept…
Q: RAM, ROM, hard disc, and compact disc are all types of primary memory.
A: Introduction: Goal: Select the option that is called main memory. One that is referred as main…
OOPs
In today's technology-driven world, computer programming skills are in high demand. The object-oriented programming (OOP) approach is very much useful while designing and maintaining software programs. Object-oriented programming (OOP) is a basic programming paradigm that almost every developer has used at some stage in their career.
Constructor
The easiest way to think of a constructor in object-oriented programming (OOP) languages is:
Question 11
If data members are private, what can we do to access them from the class object?
Step by step
Solved in 2 steps

- Create a class student which has register number, mode type (Academic, sports, both), and average as data members. Create two friend classes Academic and Sports for student class. Input three marks for Academic and two marks for sports. Create a common non-member friend function for all the classes to calculate the average of marks based on the mode type. Create constructors for mark details. Display the Register number and average of the student. Mark must be checked for “Mark must not be zero” exception.Create a class named Laboratory containing• Two data fields i.e. name (a string) and location (string)• A no-argument constructor to initialize all data fields with default values “NoName” and “NULL”• A member function named input()• A member function named show() to display the details associated with an instance of this classDerive a class named WetLab from class Laboratory that includes• data members no_of_microscopes and Scientist_name,• respective mutator and accessor functions • overriding function named input() to take input from user in all data members• overriding function named show() to display the details associated with an instance of class WetLabFrom the Laboratory class, derive a class named DryLab that contains• a data field named no_of_computers and Capacity • Setters and getters• an overriding function named input()• overriding function named show() to display the details associated with an instance of this class Implement these classes and in the main() create…Planet: Based on the information given in tablebelow, write: •a class called Planetthat contains information (only for data members mass, diameterand density) presented in the Planetary Data. •a default constructor to initialize every data member. •a member function called setInfo(...) to set the values for all data member. •a member function called printInfo(...) that will output all information about the planet. Set this member function as const. •a main function that will simulate the instantiation of a class Planet’sobject called Mercuryand set its information according to the data in figure below. •Then, print the information about Mercuryusing printInfo(...). Save your file as MatricNo_Planet.py NOTE: i need (#) comment and explanation
- Write a class Medical Staff that contains an attribute ID to store staff’s identity. The class contains member functions to input and display ID. Write a child class Doctor that inherits Medical Class. It additionally contains an attribute to store doctor’s PMDC number. It also contains member functions to input and show the PMDC number. Write another class Skin Specialist that inherit Doctor Class. It additionally contains an attribute to store working experience as specialist. It also contains member functions to input and show the experience. Test these classes from main() by creating objects of derived classes and testing functions in a way that clear concept of multi-level Inheritance.b) Recall the Complex class that we implemented in operator overloading concept. Your task is to provide implementation of the following method. friend ostream& operator<< (ostream& , const Complex& )create a class called employee 2. use the init function to collect the employee information (name, email and mobile phone) 3. Instantiate the employee class two times with different information 4. display all the properties of the objectDesign a class named Automobile that includes • A data member named currentSpeed• A setCurrentSpeed function to set currentSpeed of an automobile• A getCurrentSpeed function to get currentSpeed of an automobile Derive a class named Car inherited from Automobile class and contains• An additional data member named color• A parameterized constructor to initialize its own data fields along with the inherited data field • Two functions named setColor and getColor to set and get the color of a Car object, respectivelyDerive a class named Limousine inherited from class Car and has its own functions (i.e. setCurrentSpeed, getCurrentSpeed, setColor and getColor) to set/get speed and color for each of its specific instance
- Create a class called Person with suitable data members to represent their name and age. Use member function to initialize and display these information. Derive Student and Employee from the Person class with their unique features. Initialize object of these class using constructor and display the information.Class members are accessed via the________ operator in conjunction with the name ofan object (or reference to an object) of the class or via the_____________ operator in conjunction with a pointer to an object of the classCreate a class Player that stores following information of players:1. Name of player2. Country of player3. Name of game participating in4. Age of playerDefine a member function getplayer() and showplayer() for displaying information about playerin class.Create Second object Player “P2” of a Player class and initialize this object with First Player “P1”and access member functions of this class.
- Create a class called students with 4 private member variables, name quiz midterm and final term include all necessary member function with constructor, get function and grading function declare 3 object of students type read from the keyboard three sets of values of name quiz midterm and final and assign them to each object using objects member function to calculate grade =quiz *0.2 +midterm *0.4+final*0.4 display on the screen only name and gradeSome of the characteristics of a book are the title, author(s), publisher, ISBN, price, and year of publication. Design a class bookType that defines the book as an ADT. Each object of the class bookType can hold the following information about a book: title, up to four authors, publisher, ISBN, price, and number of copies in stock. To keep track of the number of authors, add another member variable. Include the member functions to perform the various operations on objects of type bookType. For example, the usual operations that can be performed on the title are to show the title, set the title, and check whether a title is the same as the actual title of the book. Similarly, the typical operations that can be performed on the number of copies in stock are to show the number of copies in stock, set the number of copies in stock, update the number of copies in stock, and return the number of copies in stock. Add similar operations for the publisher, ISBN, book price, and authors. Add the appropriate constructors and a destructor (if one is needed). Write the definitions of the member functions of the class bookType. Write a program that uses the class bookType and tests various operations on the objects of the class bookType. Declare an array of 100 components of type bookType. Some of the operations that you should perform are to search for a book by its title, search by ISBN, and update the number of copies of a book.Some of the characteristics of a book are the title, author(s), publisher, ISBN, price, and year of publication. Design a class bookType that defines the book as an Abstract Data Type (ADT).• Each object of the class bookType can hold the following information about a book: title, up to four authors, publisher, ISBN, price, and number of copies in stock. To keep track of the number of authors, add another member variable.• Include the member functions to perform the various operations on objects of type bookType. For example, the usual operations that can be performed on the title are to show the title, set the title, and check whether a title is the same as the actual title of the book.Similarly, the typical operations that can be performed on the number of copies in stock are to show the number of copies in stock, set the number of copies in stock, update the number of copies in stock, and return the number of copies in stock. Add similar operations for the publisher, ISBN, book…

