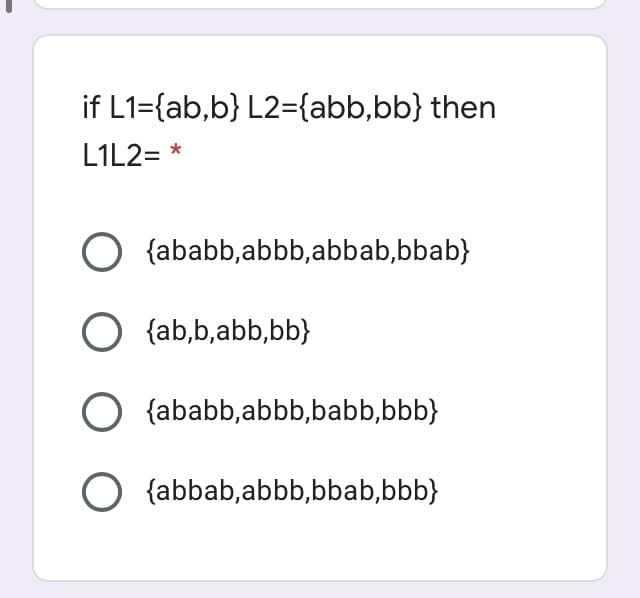
if L1={ab,b} L2={abb,bb} then L1L2= * O {ababb,abbb,abbab,bbab}
Q: STRATEGY AND TECHNIQUES Definitions of modeling words verification and validation.
A: Technique: Technique is a method of accomplishing a certain job, such as the creation or performance…
Q: Derive the formula to get the third forward finite difference (x+3h) to get the coefficient of…
A: The derivation of the finite difference approximations is based on forward and backward Taylor’s…
Q: Assume that a bank's database is safeguarded using snapshot isolation database technology. Do you…
A: Intro Banks safeguard their data: Banks must first reevaluate their existing back-office and…
Q: What exactly does the phrase "scrubbing" refer to in relation to RAID systems, and why is it seen as…
A: Intro Scrubbing at the RAID level implies examining all disc blocks in aggregates (or a specific…
Q: Explain why conditional statements are used in your coding solution and how they will help you…
A: Conditional statements are the statement which contains some condition and a block. Inside the block…
Q: Why is hashing a password file rather than encrypting it a far better alternative for storing…
A: Introduction: Password encryption is a more secure method of password security than password…
Q: Take a look at a well-known SCM tool and describe how it manages version, variant, and configuration…
A: Introduction: SCM (Software Configuration Management) is a software engineering approach for…
Q: The process of identifying and evaluating hazards is known as risk management for information…
A: Introduction: Including risk management methods in a company entails identifying, assessing, and…
Q: Cloud computing designs like Big Data Cluster are currently being used by a number of data centers.…
A: Start: Cloud computing enables massively parallel, complex calculations. No expensive computer…
Q: More than 90% of the microprocessors/micro-controllers manufactured is used in emb
A: The answer is
Q: What types of problems did researchers who were working on early versions of the Internet want to…
A: Introduction: Our world has been changed by the internet, the most sophisticated and…
Q: Explain why conditional statements are used in your coding solution and how they will help you…
A: Institution: In coding, you write restricted articulations to make your PC check conditions. PCs…
Q: How does a program pick up where it left off after an interrupt servicing process has been finished
A: Introduction How does a program pick up where it left off after an interrupt servicing process has…
Q: Cloud computing vs grid computing: what's the difference, and how do you decide?
A: GIVEN: What is the difference between cloud computing and grid computing, and how do you choose…
Q: Imagine for a second that a design team is asking for input on their proposed prototype design in…
A: Determining the Evaluation Framework Definition of the Evaluation Framework: The users or the…
Q: Write a Python program that will ask a user for the weather and display what to do with it, refer to…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Using C++, Write the prototype, sample call, and definition (header and body) of a function…
A: A prototype of a function provides the following info to compiler: return type of function name of…
Q: Objects in many programming languages have the characteristic of __________, which means that even…
A: Given that : Encapsulation is the property that specifies that all vital information is contained…
Q: Exactly how does the operating system deal with the CPU?
A: Answer:
Q: Describe an attack on a web series-based authentication method.
A: Introduction: An attack against a web cookie-based authentication scheme:
Q: You work for a large soft drink company as a consultant. Explain to the organisation how the…
A: You work as a consultant for a big soft drink company. Outline for the organisation how the internet…
Q: Cloud computing vs grid computing: what's the difference, and how do you decide?
A: Introduction Cloud Computing Cloud computing employs a client-server architecture to distribute…
Q: Write a r programming code for logistic regression and calculate these classification metrics:…
A: We need to build logistic regression. To calculate the confusion matrix and accuracy and precision.…
Q: In this day and age of RAID storage devices, is it really necessary to make regular backups of an…
A: Answer
Q: compare context-free grammar and regular expression
A: A search pattern can be defined as a string of characters using the concept of a regular expression,…
Q: It is unclear why cache memory is required because random access memory (RAM) is already available…
A: Please find the detailed answer in the following steps.
Q: It is unclear why cache memory is required because random access memory (RAM) is already available…
A: One type of computer memory is known as cache memory, and it is used to temporarily store…
Q: e have emphasised the importance of an operating system in making optimum use of computer hardware.…
A: Introduction: We have emphasized the importance of an operating system in making optimum use of…
Q: STRATEGY AND TECHNOLOGY To further understand these concepts, let's look at how they apply to…
A: SIMULATION AND MODELING: Modeling and simulation employ a physical or logical model of a system to…
Q: In what ways does symmetric key cryptography vary from more conventional methods of encryption?
A: Symmetric Key Cryptography: A secret key is used for both encryption and decryption in symmetric key…
Q: Consider a possible bank robbery. How does the bank prevent future intrusions, recognise those that…
A: Introduction: A network intrusion detection system (NIDS) is vital for network security since it…
Q: Let n N with n > 2 and let G₁ = (V, E) be the graph with vertex set V = {V₁, V₂,..., U2n} and edge…
A: In 1st graph, there are 4 vertices out of which we are asked for v1. If we consider triangles for…
Q: Remove any node from the tree from #1. And replace it with a new value. Draw the resulting BST.
A: Deletion algorithm to delete a node from Binary search tree. Locate the node, which you want to…
Q: What are some of the characteristics that set a computer apart from other devices?
A: A computer is an electrical device that processes data or information. It can store, retrieve, and…
Q: Many controls have characteristics that influence whether or not they are shown on a form during…
A: Controls in graphical user interface programming: Controls are fundamental elements of graphical…
Q: What are your opinions on decentralized dynamic routing as opposed to global (centralized) dynamic…
A: Given: We need to have a conversation about dynamic routing on a global and decentralised scale. -…
Q: Describe the methods of session hijacking. How are you going to avoid this attack?
A: Introduction: Session Hijacking is a type of attack in which unauthorised access is gained to…
Q: Use an example to demonstrate the difference between supervised and unsupervised learning.
A: Supervised learning is a machine learning technique that involves training models with labelled…
Q: What are the main distinctions and similarities, and how do they relate to one another, between…
A: Intro Five differences between on-premises and cloud IT SECURITY solutions Datacenter security is…
Q: What is the most significant contrast that can be drawn between the agile technique of project…
A: Introduction: Agile and waterfall project management methodologies exist on a continuum and should…
Q: In this section, the distinction between application layer protocols and network applications is…
A: Some individuals are confused by the top layer of the OSI model, which some people believe relates…
Q: Examine the threats to higher education emerging from inside the system. If you have any tips for…
A: Higher Education Sector: The Higher Education Sector includes the following R&D statistics:…
Q: What are two ways to avoid being a victim of phishing? What is clickjacking and how does it work?
A: Introduction: A phishing attack occurs when an individual sends a phony message that looks to…
Q: The construction of a genuine cache hierarchy would be much appreciated, if you could kindly…
A: hierarchical caching (namely, reduced network bandwidth consumption, reduced access latency, and…
Q: THE FUTURE OF WIRELESS NETWORKING Describe the advantages of wireless communication technologies in…
A: Communications System: A communications system, often known as a communications network, is a…
Q: What exactly is an overlay network, and how does its functionality manifest itself? Routers are not…
A: Introduction: Multiple network layers: An overlay network is a logical computer network that is…
Q: Make a K-map and encircle the groups
A: K-Map: In this, we can minimize the Boolean expressions of 3, 4 variables very easily by using the…
Q: When it comes to computing, what are the advantages of utilizing CUDA and GPUs?
A: CUDA: CUDA is a computing platform and API that allows programmers to employ individual GPUs for…
Q: Q4|| Write a program in C++ language to print the first letter of your name and your father using…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: Can interruptions occur while another is being handled?If not, how can this be avoided? If so, why,…
A: Introduction: Multiple interruptions can also be handled in the following ways:
Step by step
Solved in 2 steps with 1 images

- pizza (python)Mario owns a pizzeria. Mario makes all of his pizzas from 10 different ingredients, using 3 ingredients on each pizza. Mario’s cousin Luigi owns a pizzeria as well. Luigi makes all his pizzas from 9 ingredients, using 4 ingredients on each pizza. Mario and Luigi have made a bet: Mario believes that customers can order a larger selection of pizzas in his pizzeria than they can order in Luigi’s pizzeria. Use functions for this assignment. Implement a factorial() function yourself (do not use the one from the math module) When choosing k items from n possible items, the number of possibilities can be obtained using the following formula: (??)=?!?!(?−?)!(nk)=n!k!(n−k)! Make a function called choose with two parameters n and k, that implements the above formula. Write a program that calculates the number of pizzas Mario and Luigi can make. The outcome should look like this: Mario can make 120 pizzas.Luigi can make 126 pizzas. Luigi has won the bet.Addition Rule Product Rule Log Exponent Rule Log Base Rule Transitivity In the following section, indicate what reference function (g(x)) we should use when attempting to prove that f(x) is O(g(x)). Use the rules and reference functions above to guide you. f(x)=n+log2n f(x)=n2+log n4 f(x)=n2∗n3 f(x)=n5/n2 f(x)=n∗(log n)∗n f(x)=n+n log n+log nIN HASKELL PROGRAMMING LANGUAGE PLEASE In case you do not know it: the game is played on a 3x3 grid that is initially empty. Two players are playing, by alternatingly making moves. A move by a player places their token (an X for player 1, an O for player 2) into a cell that was empty. We are using algebraic notations for indexing the positions in the board, with A,B,C indexing the columns and 1,2,3 the rows. Specifically, these coordinates would be used in the implementation for moves made by a human player. If the X X O Figure 1: Sample board position same token appears 3 times in any of the three columns, three rows or two main diagonals the game is over and that player wins. If the grid is filled without that happening the game is a draw. For the depicted board, we have Xs in positions C3 and A2, and an O in position B1. It would be O’s turn to make a move; a legal move would be C2, but it is not a good move, because X can force a win by responding A1. O cannot force a win, but…
- Computer Science Write in Javascript please and use high order functions liek map or filter or reduce let obj = [ { mode: "hot" }, { temp: "low" }, { mode: "cold } ] I want to create a function that get object by key such as: myFunc("mode"); returns { mode: "hot" } next call of myFunc("mode") returns { mode: "coldSuppose you works in a library and have the id’s of 12 books as follows 2345 , 125 , 85 , 969 , 789 , 12 , 487 , 66 , 4556 , 48 , 7987 , 412 If you need to made a simple program a) Which data Structure will you chose in order to store these Book ID’s ? Justify your answer b) Does the physical arrangement of books and data structure you chose to store book ID’s have any link with each other? Chose either YES or NO and Give reason why your answer is YES and give reason if your answer is NO c) Write a C/C++ program that saves above ID’s in your chosen data structure d) [Connected with part c] Take integer value as an input that searches from values present in data structure and give output “FOUND” if value matches and, “ DID NOT FOUND” if value didn’t matches, Discuss the searching technique you used with reason Example: Input value: 125 Output: Found Input value: 9 Output: Not FoundC++ PROGRAMMINGTopic: HashTable - PolyHash Quadratic Explain the c++ code below.: SEE ATTACHED PHOTO FOR THE PROBLEM INSTRUCTIONS It doesn't have to be long, as long as you explain what the important parts of the code do. (The code is already implemented and correct, only the explanation needed). You can also explain line by line for an upvote, thanks. EXPLAIN THE CODE BELOW: #include <cstdlib> #include <math.h> #include <cstring> #include <iostream> using namespace std; class HashTable { string* table; int N; int count; // TODO: Polynomial Hash Code using a=7 int hash_code(string key) { int code; int hash = 0; for (int i = 0; i < key.size(); i++) { char ch = key[i]; code += ((ch - 96) * pow(7, key.size() - (i + 1))); } return code; } // TODO: This hash table uses a MAD compression function // where a = 11, b = 461, p = 919 int compress(int code) { return (((11*code)+461) % 919) % N; }…
- SUBJECT: PROGRAMMING FUNDAMENTELS LAB IT provides best solutions for manual work that makes life easier .Suppose a university wants to manage its data in the form of software. Being a programmer you have been asked to create the following structures in C. 1. Student: a. Name b. RegId c. Enrolled courses (Labs + Theory) d. Department e. Semester2. Faculty: a. Name b. Department c. Designation d. Salary:Implement the following scenario using functions: setMarks(): This function will allow faculty members to set Student marks. getGpa(): Takes students as an argument and calculates the student’s GPA. displayStudent(): display the given student’s information. displayFaculty(): display the given faculty’s information. NOTE ; KINDLY PROVIDE THE ANSWER OF THIS QUESTION IN C LANGUAGE ASAP*Java code* Implement a data structure called RunningTotal supporting the following API: a) RunningTotal() - creates an empty running-total data structure b) void add(int value) - adds the given value to the data structure c) void remove() - removes the least-recently added value d) int sum() - returns the sum of values in the data structure e) double average() - returns the average of values in the data structure Here's a Example: RunningTotal rt = new RunningTotal ();rt . add (1); // 1 ( adds 1 )rt . add (2); // 1 2 ( adds 2 )rt . add (3); // 1 2 3 ( adds 3 )rt . sum (); // 1 2 3 ( returns 6 )rt . add (4); // 1 2 3 4 ( adds 4 )rt . remove (); // 2 3 4 ( removes 1 )rt . sum (); // 2 3 4 ( returns 9 )rt . average (); // 2 3 4 ( returns 3.0 )do q3 Question No 1: Create the following structures in C: Student : Name RegId Enrolled courses (Labs + Theory) Department Semester Faculty: Name Department Designation Salary: Implement the following scenario using functions: setMarks():This function will allow faculty member to set Student marks. getGpa(): Takes student as an argument and calculates the student’s GPA. displayStudent(): display the given student’s information. displayFaculty(): display the given faculty’s information. Question No 3: Refer to Question NO 01 Student structure and using pointer determine the senior student among two students. Print information of the senior student.
- IN C++ USING CLASS Write a program in C++ that implements the game tic-tac-toe: Tic-Tac-Toe is a game played on a three-by-three board. Two players, X and O, alternate in placing their respective marks in the cells of this board, starting with player X. If either player succeeds in getting three of his or her marks in a row, column, or diagonal, then that player wins. In this homework, you should use the OOP concepts to implement the tic-tac-toe game(C Language) The Fibonacci sequence begins with 0 and then 1 follows. All subsequent values are the sum of the previous two, for example: 0, 1, 1, 2, 3, 5, 8, 13. Complete the Fibonacci() function, which takes in an index, n, and returns the nth value in the sequence. Any negative index values should return -1.Complete the function solveMeFirst to compute the sum of two integers. In javascript Example Return . Function Description Complete the solveMeFirst function in the editor below. solveMeFirst has the following parameters: int a: the first value int b: the second value Returns- int: the sum of a and b Constraints 1<a; b<1000; process.stdin.resume();process.stdin.setEncoding('ascii'); var input_stdin = "";var input_stdin_array = "";var input_currentline = 0; process.stdin.on('data', function (data) { input_stdin += data;}); process.stdin.on('end', function () { input_stdin_array = input_stdin.split("\n"); main(); }); function readLine() { return input_stdin_array[input_currentline++];} function solveMeFirst(a, b) { return a + b; } function main() { var a = parseInt(readLine()); var b = parseInt(readLine());; var res = solveMeFirst(a, b); console.log(res);}

