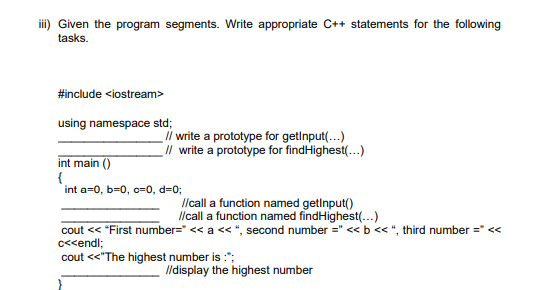
iii) Given the program segments. Write appropriate C++ statements for the following tasks. #include using namespace std; // write a prototype for getinput(...) // write a prototype for findHighest(...) int main() { int a=0, b=0, c-0, d=0; //call a function named getinput() //call a function named findHighest(...) cout << "First number=" << a <<", second number =" << b <<", third number =" << c<
Q: Create a Work Breakdown Structure in Construction of olympic stadium. Your WBS must include up to…
A: The Work Breakdown Structure which refers to the deliverable and it is an oriented hierarchical…
Q: What are some of the objectives of the process of authenticating someone? Compare and contrast the…
A: The process of confirming that someone or something is, in fact, who or what it claims to be is…
Q: Create a Work Breakdown Structure in Construction of olympic stadium. Your WBS must include up to…
A: Work breakdown structure which refers to the project management and the systems engineering which is…
Q: How far can we advance with the aid of authentication? In this part, we will evaluate the benefits…
A: Introduction: The process by which it is determined if something or someone is who or what they…
Q: Who should have access to a private key in a two-key authentication system
A: A private key is an entity or a variable used in cryptography. It is a long sequence of bits…
Q: to crate a circular linked list in c++ where it should have following functions supported: Create…
A: Answer:
Q: How does the capacity analysis react when many processes are operating concurrently?
A: How does capacity analysis respond when many processes are running concurrently? This is the issue…
Q: Describe a situation in which it is necessary to maintain a phoney login. Identify many methods for…
A: Here we have given a brief note on situation in which it is necessary to maintain a phoney login.…
Q: How precisely might mobile UI toolkits aid designers and developers trying to enhance the user…
A: Introduction: Adobe Photoshop is among the top 10 mobile app UI design tools. Microsoft Windows and…
Q: Which of our objectives would be most likely to be realised if we obtained authentication support?…
A: Authentication:- It is a process in which it is verified that something or someone is the same who…
Q: What steps are used to determine which model is the greatest fit for the system?
A: What steps are used to determine which model is the greatest fit for the system answer in below…
Q: Explain why database backup and recovery processes are so crucial. Next, go over the necessary…
A: Database backup and recovery are important and have certain features. The main goal of a backup is…
Q: Authentication management in a hypothetical situation is detailed here. Create a list of the various…
A: Introduction: Scenario management is an efficient way to manage futures and create customized…
Q: Router IP address 192.168.100.1 Subnet mask 255.255.255.0 Max users 29…
A: Here we have given the calculation of the network address, the broadcast address, the first usable…
Q: What do you mean when you say "objectives of authentication"? Contrast the advantages and…
A: Start: Authentication is used when a server wants to know who is accessing their information or…
Q: Regarding effective communication, what role does modern technology play, and how is it utilised?…
A: - We are talking about the role of modern technology in effective communication.
Q: What actions should be performed if there is a breach in a company's security?
A: In this question we have to discuss what all actions should be performed if there is a breach in…
Q: What are the most common errors that might occur throughout the data modelling process?
A: Introduction: Inappropriate denormalization: This approach should only be used in emergency…
Q: Question: FULLY AUTOMATIC VENDING MACHINE - dispenses your cuppa on just press of button. A vending…
A: The Python code is given below with output screenshots Happy Coding?
Q: How does a data breach impact the cloud's security? What are some of the several types of preventive…
A: Data breaches in cloud computing keep up with their status as one of the top network protection…
Q: What is the precise purpose of the canvas element in HTML5?
A: Canvas element in HTML 5 are used to draw graphics via scripting. They can be used to draw…
Q: this code: #include #include using namespace std; // Node struct to store data for each song in…
A: It is defined as a general-purpose programming language and is widely used nowadays for competitive…
Q: Why is it preferable to have a hashed password file as opposed to an encrypted database?
A: Why is it preferable to have a hashed password file as opposed to an encrypted database answer in…
Q: w does a data breach impact the cloud's security? What me of the several types of preventive…
A: Introduction: Cloud computing is notoriously insecure. Cloud computing providers, on the other hand,…
Q: Which of our objectives would be most likely to be realised if we obtained authentication support?…
A: Which of our objectives would be most likely to be realised if we obtained authentication support?…
Q: Create a concise overview of your file integrity monitoring software.
A: Start: You must use file integrity monitoring to protect your organization's data from unauthorized…
Q: Describe a situation in which it is necessary to maintain a phoney login. Identify many methods for…
A: The user must provide a unique ID and key, which are then validated against stored data. Each…
Q: What does it signify in respect to a number when a bit is "activated"? What does the numerical…
A: Introduction: Depending on how you got your copy, you'll either need a digital licence or a…
Q: As a computer manufacturer, one of your difficulties will be to provide high-quality machines with…
A: Computers Manufactured: Most computers, laptops, and smartphones are now produced in China. Foxconn,…
Q: Explain how technological advancements have made it simpler for workers to interact inside…
A: Introduction: Internal communication refers to an organization's deliberate efforts to inform and…
Q: Create a program flowchart that generates and displays the Fibonacci sequence numbers of n(as…
A: As the programming language is not mentioned here, we are using PYTHON The Python code is given…
Q: Please include samples for each of the three most used file management techniques.
A: On a computer system, organizing, storing, and manipulating files is referred to as file management.…
Q: Describe a single memory architecture.
A: The answer for the above mentioned question is given in the below steps for your reference.
Q: What exactly do you mean when you claim you understand the phrase "Data Modeling"?
A: Data modelling is a fundamental component of data management. Providing a visual representation of…
Q: What is the difference between starting a data modelling project with a pre-packaged data model and…
A: Introduction: You should think about data before designing an app, just like architects do before…
Q: Examine the advantages and disadvantages
A: ADVANTAGES By automating processes and tasks and by giving companies access to information and…
Q: Is there a disadvantage to using several authentication methods? Consequently, how does it aid in…
A: Is there a disadvantage to using several authentication methods? Consequently, how does it aid in…
Q: What exactly do you mean when you claim you understand the phrase "Data Modeling"?
A: Data modeling is the process of designing a data structure for a database. This data structure can…
Q: Describe a made-up scenario requiring the administration of login credentials. Identify various…
A: Introduction: Give a fictional login circumstance. Identify authentication methods. Password…
Q: Where can I identify and build a list of the websites of the parent and child standardisation…
A: The data transmission and computer networking standards specify the interoperability of network…
Q: I am unsure of what you mean when you discuss the purposes of authentication. Determine what each…
A: The question has been answered in step2
Q: Write the appropriate algorithm for each mathematical problem 1. X = (a+b) - c 2. Get the…
A: In this question we need to write algorithm for the mathematical problems. Algorithm:- An algorithm…
Q: What happens if the creation of a stack resource fails?
A:
Q: Problem2: Conditional: (30 points) Create an algorithm that will display the average of all numbers…
A: The algorithm will be: 1. Get input from user for x and y. 2. Initialize sum to 0 and count to…
Q: Provide a fictional example of login management. Consider a range of user authentication methods. Is…
A: Answer:
Q: The objective of authentication is to achieve what, precisely? Examining the pros and downsides of…
A: Introduction In this question, we are asked about The objective of authentication and Examine the…
Q: Do imperfect and ambiguous models pose a challenge to non-monotonic reasoning?
A: Solution for do imperfect and ambiguous models pose a challenge to non monotonic reasoning
Q: What is the difference between library resources and those available in indigenous media? What…
A: Libraries have the ability to expand access to indigenous knowledge by developing an environment…
Q: Let's suppose, for the sake of simplicity, that 581132 is the position of a file block on the disc.…
A: To answer this query, we must comprehend the location and storage of the file blocks in the disc.…
Q: What precisely is communication technology? Please use the proper means of communication technology…
A: Communication technology is the use of technology to transport messages (information) between humans…
Step by step
Solved in 3 steps with 1 images

- (Conversion) a. Write a C++ program to convert meters to feet. The program should request the starting meter value, the number of conversions to be made, and the increment between metric values. The display should have appropriate headings and list the meters and the corresponding feet value. If the number of iterations is greater than 10, have your program substitute a default increment of 10. Use the relationship that 1 meter = 3.281 feet. b. Run the program written in Exercise 6a on a computer. Verify that your program begins at the correct starting meter value and contains the exact number of conversions specified in your input data. c. Modify the program written in Exercise 6a to request the starting meter value, the ending meter value, and the increment. Instead of the condition checking for a fixed count, the condition checks for the ending meter value. If the number of iterations is greater than 20, have your program substitute a default increment of (ending value - starting value) / 19.PLEASE CODE THIS IN C AND NOT C++. ONLY USE IF/CASE AND USER-DEFINED FUNCTIONS. PLEASE DO NOT USE LOOPS,STRUC, AND POINTERS. PLEASE ONLY DECLARE AND CALL VARIABLES IN THE MAIN FUNCTION, EVERYTHING ELSE IS IN A DIFFERENT USER-DEFINED FUNCTION. PLS CHECK IF IT WORKS TOO.Complete the blank in C++ program in Figure 1 below to display the space, lower case and upper case numbers for “Great Day\n”. The answer should be the appropriate built in function that will perform the operation based on comment given.
- Write a C statement to accomplish each of the following tasks.a) Define variables sum and x to be of type int.Please do the following and show execution code and output! Write two Haskell functions to calculate ticket prices. Tickets for those ages 12 and under are $8.50, tickets for those between 13 and 65 are $14.50 and those older than 65 are $9.00. The second function should calculate tax – assume tax is 12%. Using function chaining to calculate the total cost. The main function should ask what type of ticket the person wants (child, adult, or senior) and call the functions that you wrote. Show the type signatures of the functions you write.C++ Please give a similar example as the previous example in photos (language C++) -Provide a hand-tracing example based off this previous example in the book Big C++ that tests the program like the previous example in the photos. Make sure it’s similar but not the same. -Use a simple program using 2 variables that require user input with 2 constants that are initialized upon declaration, and either a decision or repetition control structure the program uses to control the flow of logic. Thank you :) I will give a rating!
- For this c++ homework fill in the code Use functions and function declarations (headers) to calculate the payment schedule for a loan. Read from the user: initialLoan, annualInterest, MonthlyPayment Create a loan payment function based on the 3 params above. For each month, print on one line, for each month#: Month, Balance, Payment, PaidOnBalance, Interest, Total Int. Paid Until the monthbalance (currentBalance)<=0 At the end of every year (12 months), draw a line of 65 '$' characters. If the MonthlyPayment < 1st month's monthlyInterest, reject the payment code: #include <iostream>using namespace std; // make a header here for drawline // make a function called printLoanPayments that// takes in the loanAmount, annualInterest, and monthly payment// (each of the above are doubles) // print a header for multiple columns// convert annualInterest to monthly interest // keep updating the current balance// keep updating the total Interest paid// calculate the…-Program C 2. Not my Favorites by CodeChum Admin We've already done looping through a series of numbers and printing out its squares, so how about we level it up and go with cubes this time? I have a condition though; I don't want to be associated with numbers that are divisible by 3 or 5 so if an integer is divisible by either of the two, don't make their cube values appear on the screen, please. Care to fulfill my request? Instructions: Print out the cube values of the numbers ranging from 1 to 1000 (inclusive). However, if the number is divisible by either 3 or 5, do not include them in printing and proceed with the next numbers. Tip: When skipping through special values, make use of the keyword continue and put them inside a conditional statement. Output Multiple lines containing an integer. 1 8 64 343 512 . . .Mark the following statements as true or false: a. To use a predefined function in a program, you need to know only the name of the function and how to use it. (1) b. A value-returning function returns only one value. (2, 3) c. Parameters allow you to use different values each time the function is called. (2, 7, 9) d. When a return statement executes in a user-defined function, the function immediately exits. (3, 4) e. A value-returning function returns only integer values. (4) f. A variable name cannot be passed to a value parameter. (3, 6) g. If a C++ function does not use parameters, parentheses around the empty parameter list are still required. (2, 3, 6) h. In C + + , the names of the corresponding formal and actual parameters must be the same. (3, 4, 6) i. A function that changes the value of a reference parameter also changes the value of the actual parameter. (7) j. Whenever the value of a reference parameter changes, the value of the actual parameter changes. (7) k. In C++, function definitions can be nested; that is, the definition of one function can be enclosed in the body of another function. (9) l. Using global variables in a program is a better programming style than using local variables, because extra variables can be avoided. (10) m. In a program, global constants are as dangerous as global variables. (10) n. The memory for a static variable remains allocated between function calls. (11)
- (Conversion) a. Design, write, compile, and run a C++ program to convert temperature in degrees Fahrenheit to degrees Celsius. This is the equation for this conversion: Celsius=5.0/9.0(Fahrenheit32.0) Have your program convert and display the Celsius temperature corresponding to 98.6 degrees Fahrenheit. Your program should produce the following display (replacing the underlines with the correct values): For a Fahrenheit temperature of ___ degrees, the equivalent Celsius temperature is ___ degrees. b. Manually check the values computed by your program. After verifying that your program is working correctly, modify it to convert 86.5 degrees Fahrenheit to its equivalent Celsius value.(Electrical eng.) a. The voltage gain of an amplifier is given by this formula: voltagegain=[275 23 2 +0.5 f 2 ]n f is the frequency in Hz. n is the number of stages in the amplifier. Using this formula, write, compile, and run a C++ program to determine the value of the voltage gain for a four-stage amplifier operating at a frequency of 120 Hz. Your program should produce the following display: At a frequency of xxxxx hertz, the voltage gain is yyyyy Your program should replace xxxxx with the frequency and yyyyy with the voltage gain. b. Manually check the value your program produces. After verifying that your program is working correctly, modify it to determine the voltage gain of a 12-stage amplifier operating at a frequency of 9500 Hz.State the following is true or false. If false, explain why."Empty parentheses following a function name in a function definition indicate that the function does not require any parameters to perform its task."



