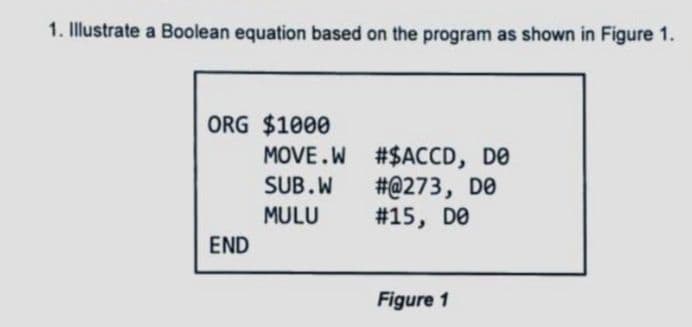
Illustrate a Boolean equation based on the program as shown in Figure 1. ORG $1000 #$ACCD, DO #@273, DO #15, DO END Figure 1 MOVE.W SUB.W MULU
Q: 1. Export data form MATLAB to Excel sheet 2. Save data as text file. 3. Load data form text file. 4.…
A: Data name is='X' And Filename is ' database' 1. Import Data form MATLAB to Excel sheet :-…
Q: When adding or deleting users in Windows 10 and Linux, what issues have you encountered?
A: Introduction: Among the issues encountered while adding or removing users in Windows 10 are the…
Q: Q4: Write an 8086 assembly language program that swaps the content of memory locations starting from…
A: The answer is as follows.
Q: What is an opcode and which information is stored inside an opcode? What are the different ways to…
A: We need to discuss opcode and information that is stored inside an opcode, and different ways to…
Q: How precisely does the Access Security Software perform its duties?
A: Inspection: The idea is to provide people access to just the data that is considered essential for…
Q: exponentiation parentheses modulus division multiplication
A: Hey there, I hope you find my solution helpful .
Q: Explain what inferential statistics are and provide some examples using your own words and…
A: Introduction Inferential statistics is defined as a method for drawing a conclusion or inference…
Q: 5. Which of the following statements is not true? Mid11
A: Answer for given mcq is given below. with explanation
Q: Explain how input validation is used to prevent SQL injection attacks.
A: SQL injection is a technique used by attackers to inject SQL queries into input fields, which are…
Q: taining elements m index 0 to 6. Wh e three values afte ge procedure in the
A:
Q: Draw a deterministic and non--4 deterministic finite automate which accept 00 and 11 at the end of a…
A: DFA is also known as deterministic finite automata.
Q: Process P1: Process P1 begins at time 0. P1 runs for 2 seconds and then creates two child processes…
A: Hey there, I hope my solution is helpful to you. Since you haven't mention any of the scheduling…
Q: ge [-5.....5, 3... ation is 100. E ry cells. Calcu blumn maior c
A:
Q: Explain the allocation of inode for files and directories.
A: The question has been answered in step2
Q: (a) Show the order of evaluation of the following expressions by parenthesizing all subexpressions…
A:
Q: In order to put the data mining approach into practice, what are the prerequisite procedures that we…
A: Data mining is the process of discovering potentially useful patterns in large amounts of data. It…
Q: In what instances do you think it’s impractical to use recursion over loops?
A: The question is in what instances it’s impractical to use recursion over loops.
Q: Iterative deepening and bidirectional search (BFS) are explained and compared. Explain the…
A: Given: BFS, DFS, bidirectional, and iterative Deeping are tree or graph searching techniques. All…
Q: What are the advantages of using all-subsets regression over stepwise regression in computer…
A: Given: Stepwise regression is used to generate regression models; in this method, each individual…
Q: Driving is expensive. Write a program with a car's miles/gallon and gas dollars/gallon (both…
A: import java.util.*;public class LabProgram { public static void main(String[] args) { Scanner scan…
Q: mple description of "process starvation" and how to prevent it in the con
A: Introduction: We employ the concept of Aging to avoid famine. After a certain period of time has…
Q: Precedence Highest < Lowest Associativity Left to right * +11
A:
Q: 11. What folder contains the information about Linux operating system settings and configuration…
A: let's see the correct answer to the question
Q: Using a double linked list, how would you express a data structure?
A: Answer:
Q: following(s) is the diagram below? Note: May have more than 1 answer BI-PHASE Manchester value…
A: Here we have given correct answer for the mention 1,2 nd 3 questions. You can find solution in step…
Q: The vast majority of today's appliances include built-in wireless networking capabilities, thanks to…
A: Wireless networking is defined as the process of telecommunications networks of a connection between…
Q: Through taking this class, you will have a deeper understanding of social networking blogs, cloud…
A: Definition Blogs about social media such as Instagram, Facebook, and Tumble provide statistics or…
Q: bject name: Microcomputer principle application Question: What memory location is accessed by MOV…
A: The correct answer is 5885H
Q: To represent logical behaviour of Boolean functions, what are the three methods?
A: There are three ways to illustrate the logical behavior of Boolean functions:
Q: Name any three programming languages, together with the characteristics that they provide, that are…
A: Introduction: The programming language is a computer language that programmers use to create…
Q: Explain the distinction between a request for proposal (RFP) and a request for quotation (RFQ) (RFQ)
A: Introduction: A request for quotation (RFQ) is a method through which a corporation solicits bids…
Q: HTTP status code "Not Found" is the most well-known.
A: Not Found: The HTTP 404, 404 Not Found, and 404 error message is a Hypertext Transfer Protocol…
Q: Use NRM to solve (the ro x² - 2x - 13 = 0 2- 32²³²-10x-14=0 3- 3 \nx +4x-5=0 roots) Correct to 3 dic…
A: Use Newton Raphson Method to solve the roots 1) x2 -2x-13=0 Given, x2-2x-13=0 ∴x2-2x-13=0 Let…
Q: A beam with a length L is attached to the wall with a cable as shown. A load W = 400 lb. is attached…
A: Find the required code in matlab given as below and output :
Q: The Windows Service Control Manager will be analysed in great depth throughout this essay.
A: The Windows service control manager is a special type of process for the Windows NT family operating…
Q: What is the CPU time if the number of instructions executed by the program is 500, cycles per…
A:
Q: Q2/writhe M-file script code to solve and plot the following system: With all concepts of the…
A: hold on t = 0:2 * pi : 101; % t value from 0 to 101 with step of 2pi x = sin(t); % set sin(t) y =…
Q: An example of "Bad Timing" in the OSI Reference Model may be given.. Talk about it for a short…
A: Introduction: Stepwise regression is used to build regression models, in which each individual…
Q: In terms of Internet and World Wide Web, what's the difference?
A: The Answer is in step-2.
Q: The link between cohesion and coupling in software design may be summarised as follows:
A: Cohesion and Coupling: Coupling depicts the connections between modules. The relationship within the…
Q: digital signal processing: Select one component of DSP and explain the importance of having a clear…
A: Answer :
Q: in-depth explanations from a predictive and descriptive analytics viewpoint
A: Introduction: Prescriptive analytics utilizes past, current, and future information to show up in…
Q: Provide an explanation as to why SNMP cannot be referred to as a programme that modifies things.
A: Introduction: SNMP stands for simple network management protocol and comes under the application…
Q: 13. The FileVault is: a. Microsoft solution for encrypting computer user data; b. The antivirus…
A: If you save sensitive information on your Mac, you can encrypt the files with FileVault to prevent…
Q: Within the scope of this tutorial, we will take a look at the Windows Service Control Manager.
A: Manager of Service Control: (SCM) is a unique framework process that begins, stops, and interacts…
Q: What can Windows Service Manager do for you? Here, we'll find out.
A: Windows Service Manager (SrvMan) Service Manager is a particular folder in Windows which allows…
Q: e, the search key fi I size is 512 bytes, and a block pointer e order of a non-lea
A:
Q: Any information about Windows Service Control Manager would be much appreciated.
A: The Service Control Manager is a process that launches the various Windows services on Windows…
Q: When it comes to doing research, how do library subscription databases stack up against well-known…
A: Introduction: Many subscription databases in the area of library and information science may be…
Q: Describe the benefits and drawbacks of the various thread implementations.
A: Modern systems can support two thread types: Threads: user and kernel. Programmers use user threads…
Step by step
Solved in 2 steps

- Subject: Software Engineering / Computer Science Note: Answer in your own words. copy from internet will not help me. Question: Given the following values, compute function point when complexity adjustment factor (CAF) is significant and weighting factors are complex. User Input = 50User Output = 40User Inquiries = 35User Files = 6External Interface = 4 (now see the picture)Please help me with this. I am not understanding it I want to get into computer science program in one these universities (U of T, Ryerson, and York) Are the 6 U/M course okay ENG 4U (English) MHF 4U (Advanced functions) MCV 4U (Calculus and vectors) ICS 4U (Computer Science) TEJ 4M ( Computer Engineering Technology) SPH 4U (Physics) DO I NEED TO TAKE SCH 4U (CHEMISTRY)What are a computer system's four most crucial tasks? Use the following graphic to your advantage.
- Alert : Dont't submit AI generated answer and given step by step solution with proper explantion. Question 1: Answer the following questions. The first mechanical calculating machine was made by William Oughtred Gottfried Leibnitz Blaise Pascal Charles Babbage None of the aboveThe first mechanical calculating machine was made by William Oughtred Gottfried Leibnitz Blaise Pascal Charles Babbage None of the above Which programming language is much in vogue among users of microcomputers ALGOL APL LOGO FORTH None of the aboveWhat are the four most important tasks that a computer system is accountable for completing? Kindly make use of the accompanying illustration to illustrate2. (c). Distinguish between Graphical user interface andCommand line interface in computer systems. (d). Describe two services that the operating system providesfor process management in computer systems
- Investigating the nature of what makes computers so powerful. Where would you locate the following four computer functions most often used in schools today?What are the four most important functions of a computer system? Make good use of the accompanying illustration.If you click on to a different question, this response will be kept. 's function is to facilitate interaction between the core elements of a computer, so that they can work together effectively. Transferring people and goods inside a country Like, say, the cash registers. The System's Central Processing Unit (Ob. c.) If you click on to a different question, this response will be stored.
- Computer science Describe the dining philosophers problem and how it related to operating systems?Kenneth H. Olsen is considered the 'father' of the minicomputer and one of the founder fathers of the modern computer industry world-wide? Explain ?Bob loves foreign languages and wants to plan his course schedule to take the following nine language courses: LA15, LA16, LA22, LA31, LA32, LA126, LA127, LA141, and LA169. The course prerequisites are: • LA15: (none) • LA16: LA15 • LA22: (none) • LA31: LA15 • LA32: LA16, LA31 • LA126: LA22, LA32 • LA127: LA16 • LA141: LA22, LA16 • LA169: LA32 Find a sequence of courses that allows Bob to satisfy all the prerequesites.

