I'm trying to output a Mad Lib story, but I keep getting an "Exception in thread" error. How do I fix my code?
I'm trying to output a Mad Lib story, but I keep getting an "Exception in thread" error. How do I fix my code?
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
I'm trying to output a Mad Lib story, but I keep getting an "Exception in thread" error. How do I fix my code?
![1 import java.util.Scanner;
2
3 public class LabProgram {
4567 8
10 一
11
12
public static void main(String[] args) {
Scanner scnr = new Scanner(System.in);
String firstName;
String generic Location;
int wholeNumber;
String pluralNoun;
firstName = scnr.next();
genericLocation = scnr.next();
wholeNumber - scnr.nextInt();
pluralNoun scnr.next();
14
15
16
17
Develop mode Submit mode
Run your program as often as you'd like, b
input values in the first box then click Run
second box](/v2/_next/image?url=https%3A%2F%2Fcontent.bartleby.com%2Fqna-images%2Fquestion%2Fbf698295-04c9-431c-9153-2f08912ee134%2F57781f80-931a-4231-875c-d2bb91ff16e6%2F22jxzi_processed.jpeg&w=3840&q=75)
Transcribed Image Text:1 import java.util.Scanner;
2
3 public class LabProgram {
4567 8
10 一
11
12
public static void main(String[] args) {
Scanner scnr = new Scanner(System.in);
String firstName;
String generic Location;
int wholeNumber;
String pluralNoun;
firstName = scnr.next();
genericLocation = scnr.next();
wholeNumber - scnr.nextInt();
pluralNoun scnr.next();
14
15
16
17
Develop mode Submit mode
Run your program as often as you'd like, b
input values in the first box then click Run
second box
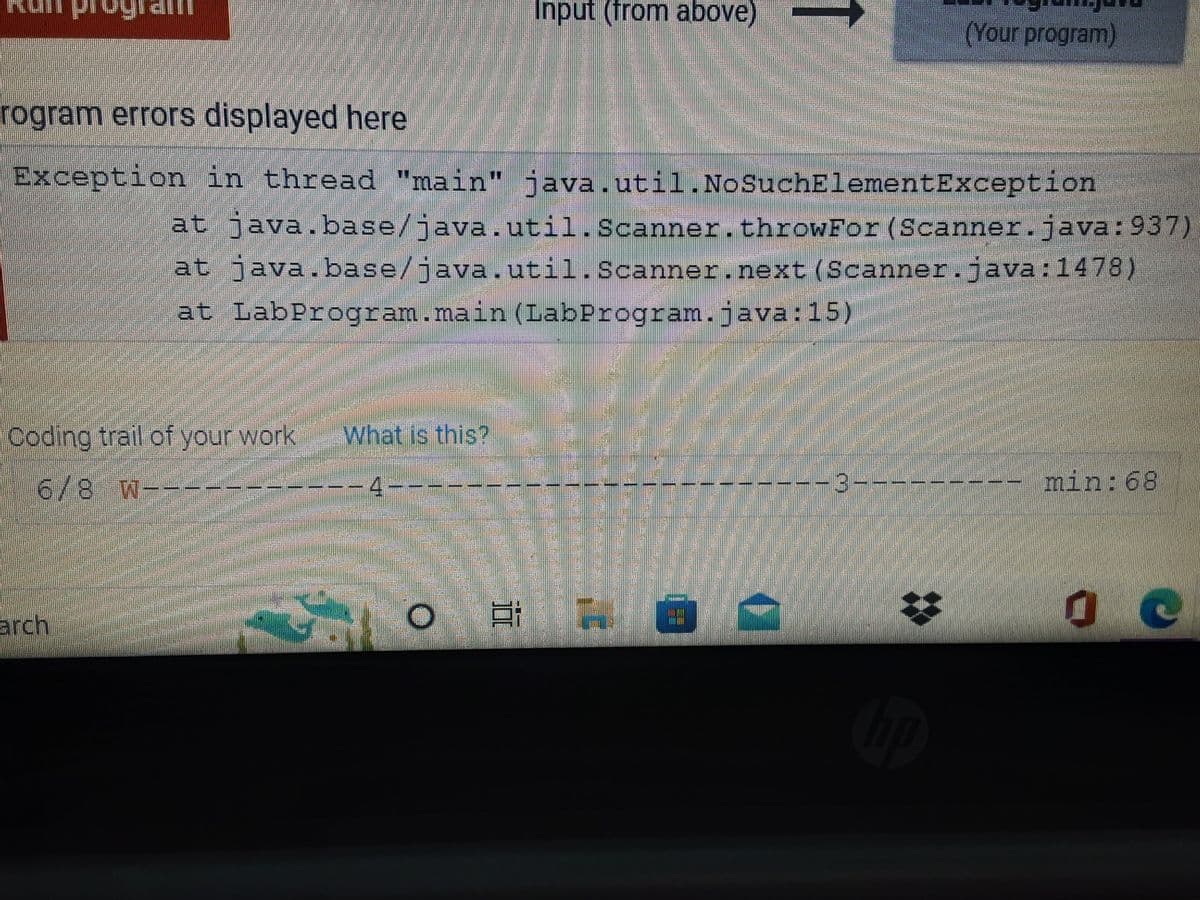
Transcribed Image Text:Input (from above)
(Your program)
rogram errors displayed here
Exception in thread "main" java.util.No SuchElementException
at java.base/java.util.Scanner. throwFor (Scanner.java:937)
at java.base/java.util.Scanner.next (Scanner.java:1478)
at
LabProgram.main(LabProgram.java:15)
Coding trail of your work
What is this?
6/8 W---
min: 68
O
arch
18
T
A
C
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education