Implement a program that will populate a 6x5 matrix with randomly generat integers from 100 to 500. (1) print your matrix in a table form. (2) modify your code to multiply all odd numbers by 2 and print the matrix. Sample run: Initial Matrix: 145 | 437 222 | 101 | 100 | 278 500 | 190 | 415 | 288 | 377 | 240 | 451 | 466 322 432 | 102 | 106 | 248 | 117 | 213 | 355 | 266 | 396 331 186 105 249 499 488 New Matrix: 290 | 874 | 222 | 101 | 100 | 278 500 190 | 830 | 288 466 322 662 186 210| 498 998 488 754 | 432 | 248 | 710 | 240 | 902 | 102 | 106 234 | 426 | 266 | 396
Implement a program that will populate a 6x5 matrix with randomly generat integers from 100 to 500. (1) print your matrix in a table form. (2) modify your code to multiply all odd numbers by 2 and print the matrix. Sample run: Initial Matrix: 145 | 437 222 | 101 | 100 | 278 500 | 190 | 415 | 288 | 377 | 240 | 451 | 466 322 432 | 102 | 106 | 248 | 117 | 213 | 355 | 266 | 396 331 186 105 249 499 488 New Matrix: 290 | 874 | 222 | 101 | 100 | 278 500 190 | 830 | 288 466 322 662 186 210| 498 998 488 754 | 432 | 248 | 710 | 240 | 902 | 102 | 106 234 | 426 | 266 | 396
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter8: Arrays And Strings
Section: Chapter Questions
Problem 24PE
Related questions
Question
ARRAYS
please provide the source code and the screenshot of the output in java eclipse.
please add comments. thank you
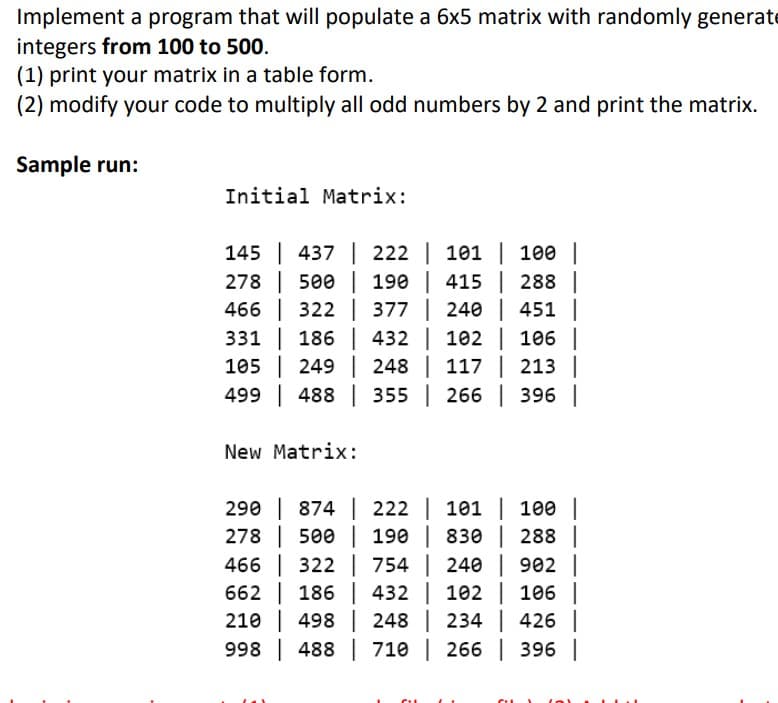
Transcribed Image Text:Implement a program that will populate a 6x5 matrix with randomly generate
integers from 100 to 500.
(1) print your matrix in a table form.
(2) modify your code to multiply all odd numbers by 2 and print the matrix.
Sample run:
Initial Matrix:
145 | 437 222 | 101 | 100 |
278
500 | 190 | 415 | 288 |
466
322 377 | 240 | 451 |
432 | 102 | 106 |
105 249 248 | 117 | 213 |
331
186
499 488
355 | 266 | 396 |
New Matrix:
290 | 874 | 222 | 101 | 100 |
278
500 | 190 | 830 | 288 |
466 322
754 | 240 | 902 |
662
186
432 |
102 | 106 |
210 498
248 |
234 | 426 |
998 488
710 | 266 | 396 |
CIL
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 5 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning