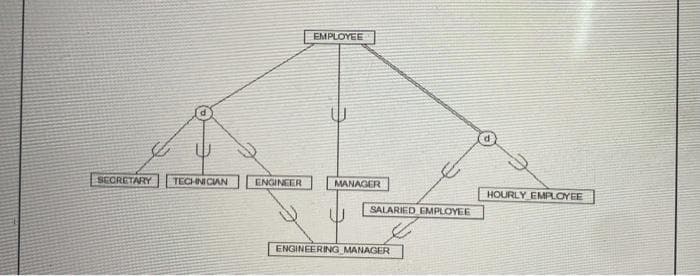
SECRETARY TECHNICIAN ENGINEER EMPLOYEE MANAGER SALARIED EMPLOYEE ENGINEERING MANAGER HOURLY EMPLOYEE
Q: e intermediate stage is the layer positioned between the data
A: Introduction: Three layers make up the three-tier architecture: the display layer, the application…
Q: Examine the two unique designs using the usability criteria you've created as a reference. Is it…
A: Usability comprises three areas: The physical product's usability. Product usability has been coded.…
Q: Do you have any special requirements, either functional or non-functional, for a web or mobile…
A: Introduction: Mobile Web apps just need a Web browser to run.Mobile Web apps are designed using Web…
Q: Demonstrate the fundamental distinctions between Service-Oriented Architecture (SOA) and…
A: Introduction: Show how SPA and micro services are implemented in reality. Technical answer needed.…
Q: How might data profiling help ensure the overall quality of data?
A: INTRODUCTION: A approach known as data profiling is one that examines the information that is used…
Q: What, in your perspective, is "critical infrastructure?" Three examples are required. Cyber attacks…
A: The Patriot Act of 2001 defined critical infrastructure as those "systems and assets, whether…
Q: Use the Lagrangian basis polynomials to construct a polynomial interpolating…
A: Numpy Working with arrays is made possible by the Python package NumPy. Additionally, it provides…
Q: When using SSH to remotely access a Cisco router, can you see the terminal password? Why or why not?
A: No Linux, because it's based on Linux and doesn't show the password, so you can't guess it
Q: What, specifically, is causing wireless networks to perform worse than cable networks, and what can…
A: Introduction: Wireless networks perform poorer than wired networks owing to signal range, linked…
Q: How does Model-View-Controller fit into the broader web application framework? What are some of the…
A: The solution to the given question is: Model View Controller (MVC) is a software development pattern…
Q: What are some of the techniques used to increase the efficiency of managing and deploying virtual…
A: When managing virtual machines, it's important to follow a set of best practices. 1. Assess your…
Q: Numerous data centers are presently using cloud computing models like Big Data Cluster. If we had…
A: According to the information given:- We have to define the numerous data centers are presently using…
Q: It is critical to understand what what comprises a service-oriented architecture.
A: Introduction: A kind of architecture known as service-oriented architecture (SOA) is one that…
Q: Machine Learning: Do Regression models and artificial neural networs have similar common functions…
A: Yes, both regression models and artificial neural networks can be used for predictive modeling.…
Q: What happens when the timer expires, requiring you to switch to a new software?
A: Introduction: Time interruption enables the user to do activities at very exact time intervals. The…
Q: How is the inverse of a matrix used in cryptography? When a matrix is said to be inverted, what…
A: Introduction: Matrix inversionInverse of a matrix is another matrix that generates multiplicative…
Q: Are there advantages to utilizing the Internet for those with physical or mental limitations? What…
A: The internet can help people with disabilities , for example: 1. The internet has made it possible…
Q: How does the application software resume normal functioning when the interrupt service is completed?
A: Introduction: The operating system acts as an interface between application software and the CPU and…
Q: If this is the case, are you up to date on the most recent network security measures? Please…
A: Introduction: The techniques for defending a network listed here are the most recent. Packet…
Q: Notes: -The maximum size of any c-string in this lab is 100 characters and it should be dynamically…
A: Here is the c++ code of the above solution. See below steps for code.
Q: Is It Possible to Find Examples of Social Capital on Social Networking Sites?
A: Introduction: The coherence of a society's culture and social structures is referred to as social…
Q: LinkedList list =new LinkedList(); list.add("Deer"); list.add("Rabbit"); list.add("Squirrel");…
A: - We need code to fill in the blanks for the java list code.
Q: hat are the similarities and differences between a two-tier architecture and a three-tier design?
A: Introduction: The distinction between a two-tier and a three-tier design. has to be answered.The two…
Q: We'd appreciate it if you could sum up the most pressing network security issues.
A: We need to address some critical network security problems. Some of the most urgent network security…
Q: In C++ Output all combinations of character variables a, b, and c, in the order shown below. If a…
A: Declare three variables a, b, and c. Input the values of these variables from the user. Finally,…
Q: What data structures would you use to implement a decision tree? Provide an example in pseudo-code.…
A: A decision tree is a diagram that displays the many solutions to a problem. For many circumstances,…
Q: In the world of cryptography, the process of encrypting data is referred to as the "salt" operation.…
A: Introduction: Why is "salt" used in cryptography? How it's used to make passwords harder to crack…
Q: We'd appreciate it if you could sum up the most pressing network security issues.
A: Introduction: It is imperative that we have a conversation about certain urgent issues about the…
Q: Detail the design principles as well as the overall design idea. What characteristics must a product…
A: Fashion basics: No one agrees on stylistic rules. Next twelve concepts are those most often…
Q: The use of operations that cannot be reversed by asymmetric ciphers helps to the improved degree of…
A: Please vote for or like. The right response is given below. Asymmetric encryption, also known as…
Q: nswer it in Matlab. Cod
A: According to the question MATLAB program to plot the curve of the exponential function esin(t),…
Q: Each active interface of Distance vector gets frequent transmissions of the whole routing table that…
A: Introduction: Data transport in packet switched networks uses distance vector and link state routing…
Q: The similarities and differences between neural networks and learning systems, as well as specific…
A: Both learning systems and neural systems are disciplines of Artificial Intelligence (AI). Because…
Q: Provide an overview of the several ways for hiding data, each of which has its own set of concerns…
A: Introduction: A law enforcement agency (LEA) is an organization that is liable for implementing the…
Q: The intermediate stage is the layer positioned between the database and client servers.
A: Introduction: The display layer, the application layer, and the data layer make up the three-tier…
Q: What is the Big-O notation of the following expression? n3 + n2 + n + 5 a. O(3) b. O(n3)…
A: Considering the subject equation is as follows: n3+ n2 + n + 5 The Big O notation for the given…
Q: Detail the design principles as well as the overall design idea. What characteristics must a product…
A: Style fundamentals: No one agrees on what the most important style principles are. The following…
Q: True or False 4. integrity can apply to a stream of messages, a single message, or selected fields…
A: Below step by step complete solution regarding your problem with explanation :
Q: Give a high-level overview of some of the most significant network security issues.
A: Introduction: Network security ensures the safety of our network.Without it, network data is at…
Q: Describe the proposed system's user interface and provide some design concepts. A decent prototype…
A: Introduction: Strukturprinzip. Your design should arrange the user interface meaningfully and…
Q: Examine how wireless networks are used in developing nations. For unknown reasons, the usage of wifi…
A: Introduction: Wi-Fi links computers, tablets, cellphones, and other devices to the internet. Wi-Fi…
Q: What type of interaction exists between user applications and system services in the context of a…
A: Microkernel architecture: A microkernel design is referred to as a plugin architecture because of…
Q: Assume that a process calls fork() to create a new process. The parent process has PID 500 and the…
A: A new process known as a "child process" is created with the fork system function and runs…
Q: It contains four routers in total. Every one of the four main necessary for router A to recompute…
A: Introduction: A distance-vector routing protocol is called Routing Information Protocol (RIP). When…
Q: A count-controlled loop must possess three elements: 1. 4 It must initialize a control variable to a…
A: When the number of iterations to occur is already known, a count-controlled loop is used.Because it…
Q: 9 11 13 . Facing p
A: I have solved below:
Q: How do I convert this into an sql schema?
A: A Schema in sql is a collection of database objects associated with a database. The username of a…
Q: For the following operation: write the operands as 2's complement binary numbers then perform the…
A: Operation: 2-1 Two's complement representation is used to represent the negative numbers. Two's…
Q: What search discussed had superior efficiency but could only be used on sorted data? a. minimum…
A: The correct answer for the above mentioned question is given in the following steps for your…
Q: Discuss the role of a compiler in code scheduling. Support your response with an example.
A: Determining and resolving dependencies as well as parallel optimization are covered by code…
1
Step by step
Solved in 2 steps

- Computer Science A research report contains a comparision between project leader and manager Where best use Performance Charactrastics Specifications Skills Responsabilitemicrosoft project assignmentComputer science: A work breakdown structure is what? What resources and equipment are utilised to create one?
- computer science - What is the primary goal of this project?"Employee Management System"Analysis the following task functions Initiating Information seeking Information givingcomputer science -Describe the project manager's, sponsor's, business analyst's, and programme manager's duties for the project you chose as a good fit for waterfall.
- Case Study – Personal Trainer Personal Trainer, Inc. Fact-Finding Summary A typical center has 300-500 members, with two membership levels: full and limited. Full members have access to all activities. Limited members are restricted to activities they have selected, but they can participate in other activities by paying a usage fee. All members have charge privileges. Charges for merchandise and services are recorded on a charge slip, which is signed by the member. At the end of each day, cash sales and charges are entered into the BumbleBee accounting software, which runs on a computer workstation at each location. Daily cash receipts are deposited in a local bank and credited to the corporate Personal Trainer account. The BumbleBee program produces a daily activity report with a listing of all sales transactions. At the end of the month, the local manager uses BumbleBee to transmit an accounts receivable summary to the Personal Trainer headquarters in Chicago, where member…Computer science Identify any ten-risks related with IT project management.Project name: job management system i want code
- Define technically documented and provide some examples. Please list four key differences you see between technical documentation and user documentation.Computer systems analysis and design -------------------------- Q1: Create a Simple Gantt Chart project schedule in Excel. 1. The Excel Gantt chart template breaks down a project by phase and task, task start and end dateWhat exactly does it mean to be a member of a certain category of staff?

