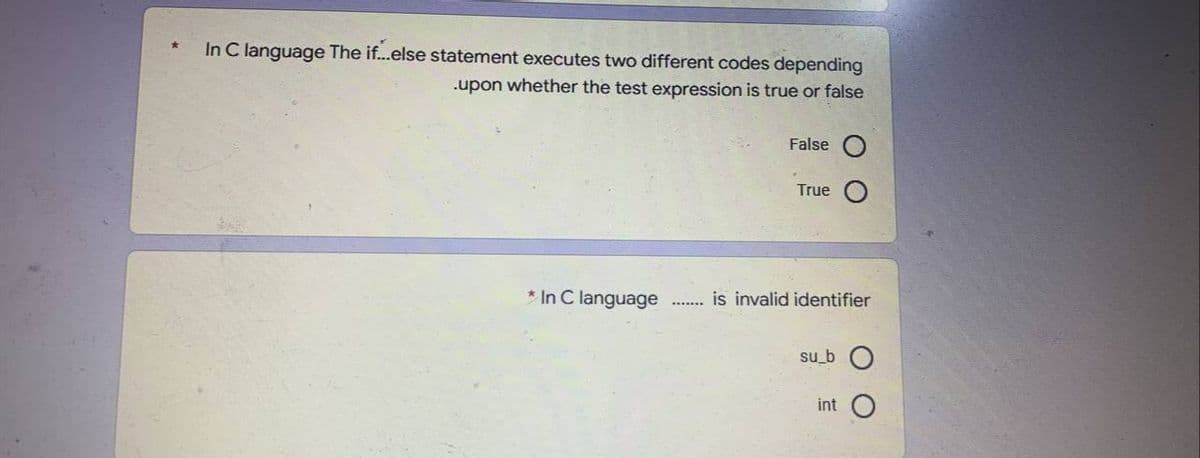
In C language The if...else statement executes two different codes depending .upon whether the test expression is true or false False O True
Q: To that end, what are some heuristics you may use to make your system design better?
A: Given: To that end, what are some of the heuristics that you may use to make the design of your…
Q: ware "in the network" might be difficult to d
A: Introduction: Administrators can use an antivirus solution to detect when a device has been infected…
Q: Please explain why user-defined functions are preferable than pre-defined ones in the context of…
A: Answer is given below. 1.Reduction in Program Size: Since any sequence of statements which are…
Q: The following matrix illustrates the estimated times (days) of an assignment problem. By using…
A: In polynomial time, a combinatorial optimization technique used to solve the assignment problem is…
Q: The static data members and static member functions aren't quite what I'm going for in this…
A: Solution: Both C and C++ make use of the term "static" in their respective programming languages.…
Q: When a project is finished, figure out what paperwork the developer should get.
A: Given: The Project Last Report is the final document in the CCS Project Management Methodology and…
Q: Privacy is a broad term, but what do you mean by that? Does it truly make a difference?? And what…
A: Internet access should be restricted will not be very helpful as the attackers and other crackers…
Q: Are there any other factors that developers should keep in mind?
A: Software developer: Developers is an expert who develops, designs and builds software. Software…
Q: - Computer science : How does the system detect thrashing? Once it detects thrashing, what can…
A:
Q: How many different kinds of multimedia files can you think of?
A: Multimedia: The term "multimedia" refers to the mixing of many different types of material,…
Q: Using the following page replacement algorithms, determine the number of faults in the following…
A: It is a technique used for memory management in paging of frames. During memory management, when…
Q: What is the correct command to find square root of any number, x. sqrt(x) O What is the output of…
A: Answer:
Q: 1. A color image uses 18 bits to represent a pixel. Compute the maximum number of different colors…
A: 0 or 1 are the only two possible values for a binary digit, which is how it is defined. To store…
Q: What is type casting? Explain implicit and explicit type conversion with example.
A: Typecasting Typecasting, or type conversion, is a method of changing an entity from one data type to…
Q: Arduino Due and Arduino Mega have the same number of Digital Input/Output, ........ which is equal…
A: The question is to select the correct option for the given questions.
Q: Why don't you write a letter on how you feel about the software testing that has been done?
A: Answer: After creating the programme, the software testing step is critical to the success of the…
Q: ow do you feel about the difference between genuine and bogus information?
A: The internet is an amazing resource. It enables us to connect with people around the world, trade in…
Q: wo strings "ABNJKLYUOP" and "ABTRLYIGP", What is the length of long
A: Lets see the solution.
Q: Q3: Matrix a= [1 3 5; 2 4 6] b=[0 0 0; 11 1]....... a+b is equal :- C=[ 1 2 3; 3 5 7] a+b=[1 3 5; 3…
A: answer is
Q: A very successful cinema director named "Chef" decided to solve the problem. When a customer wants…
A: It is defined as a powerful general-purpose programming language. It can be used to develop…
Q: The development of software and the modelling of software are two separate processes. What…
A: In software design, specific modules and components are created. Software architecture refers to the…
Q: Provide a description of the process of prototyping in relation to the establishing of requirements.…
A: Answer: Prototyping is the process of creating a working model of a system before it is installed,…
Q: To begin, let's talk about Windows Services.
A: Introduction: Microsoft Windows a services, which were formerly known as NT services, provide users…
Q: Why would you analyse the time complexity of an algorithm? a. To determine how complex the…
A: Time taken by the algorithm to run is called time complexity. There are some different notations to…
Q: daily dema pain P the maximum daily demand for interior paint is 2 tons. Reddy M optimum (best)…
A: Given that, Raw material- exterior- 6,1 Raw materia- Interior- 4,2 Profit- 5,4 Availability- 24,6…
Q: On the Internet, how do you feel about the difference between genuine and bogus information?
A: Introduction: The internet is a terrific information resource. It enables us to communicate with…
Q: A(n) ____ is a piece of programming code that replaces or changes some of the code that makes up the…
A: A patch or fix is a quick repair job for a piece of programming designed to resolve functionality…
Q: COMPUTER PROGRAMMING C++ Select all possible answer:
A: Answer:1) if -else if-else Use the else if statement to specify a new condition if the first…
Q: The Spiral Model may be used to any little project.
A: Given: The spiral model, which is used for risk management in the systems development life-cycle,…
Q: ystem provides support for user-level and kernel-level threads. The mapping in this system is one to…
A: A multi-threaded process consists of a working set for each thread. Because, each kernel thread…
Q: What are the internal components of a computer?
A: Introduction: The following items are contained within a computer: First, the motherboard, then the…
Q: image uses 18 bits to represent a pixel. Compute the maximum number of different colors that can be…
A: It is defined the short for binary digit, which means that it can only have one of two values, 0 or…
Q: To write a main code that calls a function the main code and the function should be:
A: Answer for both mcqs given below with explanation
Q: What other options are there for me to get help with Excel's functions?
A: Solution: You may learn more about Excel's functions by visiting Microsoft's support website.link:…
Q: When do physical security and information technology (IT) security need to collaborate in order to…
A: Physical security is the assurance of faculty, equipment, programming, organizations and information…
Q: Is there anything in software development that is more important than the others? In your opinion,…
A: Software development : Software development is a collection of computer science activities concerned…
Q: Traditional Waterfall Model or Iterative Waterfall Model, which one should you choose for your…
A: Classical Waterfall Model vs. Iterative Waterfall Model Iterative Waterfall Model 1 Feasible for…
Q: Please explain why the interactive method is better than the waterfall model in terms of the amount…
A: The interactive and waterfall models have different maintenance responsibilities: Animated Models:…
Q: What's the distinction between aggregate and composition? Explain briefly
A: Introduction : We must quickly clarify the distinction between aggregate and composition.
Q: Understanding the heap's purpose is critical when working with dynamic data. For a programmer, what…
A: Introduction: By allocating and deallocating memory from a location known as the heap, dynamic data…
Q: he correct answer * In Flowchart............... Denotes an input operation Diamond O Oval O…
A: Let us see the below answers,
Q: and contrast command interfaces with menu interfaces
A: CLI is that the word structure is used for the Command Line Interface. CLI grants clients licenses…
Q: When designing a software system, what are the unique inputs and outputs of the process?
A: The answer of the question is given below
Q: Explain the various security management concepts and the underlying security management principles…
A: Introduction Security's management principles are confidentiality, integrity, and availability. The…
Q: 1. Name the advantages of optical fiber over twisted-pair and coaxial cable.…
A: Below are the advantages of optical fiber over twisted pair and coaxial cable:- Speed Optical fibres…
Q: Q4/A/ Convert the the following flow chart in the attached figure into a proper program steps using…
A: The question is to write MATLAB code for the give question.
Q: What are the most important email security concerns?
A: Introduction: The most serious concerns regarding the safety of electronic mail communications…
Q: Provide a succinct explanation of what the implication of memberwise assignment is.
A: Encryption: In a member-wise assignment, any member of one object may be assigned to another object…
Q: python: Which one of the following options best describes a good reason to define functions when…
A: 1) A function is simply a chunk of code that you can use over and over again, rather than writing it…
Q: Consider a privacy issue so serious that it would force you to stop using the social media platform…
A: Privacy refers to a person's or group's ability to conceal oneself or information about themselves…
Step by step
Solved in 3 steps

- Write a program that accepts five numbers from the user and displays the lowest to the highest number. Assume that there are no duplicate values. Please use c++ language and selection control structures such as if-else. Thank you.c++ The code segment will display Hello: int a = 1; switch (a){ case a: cout<<"Hello"; break; default: cout<<"Hello"; } Select one: True False1. Write an if statement that assigns 0 to p if q is equal to 30. In C++ programming language.
- C programming (please type answer not writy by hend)IN C LANGUAGE CODE:Write a code snippet that can arrange the alphabets of a name entered by user in alternate cases.Note: Ignore white spaces. Input String:Timothy Olyphant Output String :TiMoThY OLyPhAnT Input String: Olga Kurylenko Output string: OlGa KuRyLeNkOThis statement can cause other program statements to execute only under certainconditions.a. Conditionalb. Decidec. Ifd. Execute
- In C++ Language: (Check password) Some websites impose certain rules for passwords. Suppose the password rules are as follows: - A password must have at least eight characters. - A password must consist of only letters and digits. - A password must contain at least two digits. Write a program that prompts the user to enter a password and displays valid password if the rules are followed or invalid password otherwise.Each cout statement has a syntax error. Type the first cout statement, and press Run to observe the error message. Fix the error, and run again. Repeat for the second, then third, cout statement.cout << "Num: " << songnum << endl; cout << int songNum << endl; cout << songNum " songs" << endl; #include <iostream>using namespace std; int main() { int songNum; songNum = 5; /* Your solution goes here */ return 0;}in Python, an if statement does not need to have a boolean condition. true or false?
- In c program Write an interactive program that contains an if statement that may be used to compute the area of a square ( area=side2) or a circle ( area=p*radius2) after prompting the user to type the first character of the figure name ( S or C).Computer Science **C language not C++!** ** Write C program (NOT C++) which takes as input a positive integer n and decides whether or not n is prime. The decision is made by the int isPrime(int) function whose return value is 1 if the number is prime, otherwise 0. **C language not C++!** **For each problem write a C++ program that asks the user for input, then calculates and displays correct output. Write an application that prompts the user for a checking account balance and a savings account balance. Display the message “Checking account balance is low” if the checking account balance is less than $10. Display the message “Savings account balance is low” if the savings account balance is less than $100. Save the file as AccountBalance.cpp.

