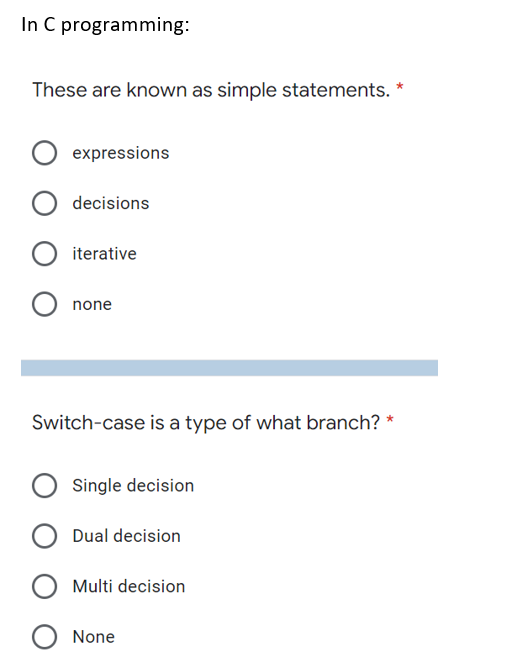
In C programming: These are known as simple statements. * O expressions O decisions O iterative O none
Q: What is NLP (natural language processing) Information Retrieval? What are some of the examples?
A: Introduction: It is a software application that organises, saves, retrieves, and assesses data from…
Q: in briefly how USB ports may be used to charge mobile devices.
A: Introduction - The USB port is used to charge mobile devices or laptops. the USB port facility…
Q: Without encryption or hashing, what security strategy would prevent unauthorized data modification…
A: Introduction: Security is the process of preventing unauthorised access to data or information.…
Q: Determine the kind of cable that will connect the switch and router. Which gadget is used to join…
A: Basics A cable is at least one wire that is covered in plastic and used to transmit force or data…
Q: Write a C PROGRAM that creates an array of 10 integers. The array should be populated with values:…
A: An array can be denoted as the data structure that is utilized to for storing values that consist of…
Q: I. Compute for the running time for each algorithm/code and give its complexity 1. for i = 1 to n do…
A:
Q: Is it ever clear what someone meant when they said they wanted a 4G or 5G phone network?
A: Intro 5G: The fifth generation of mobile networks is in development, colloquially referred to as…
Q: Do you have any recommendations for firewall administration? Explain
A: Introduction In response to the question A people group firewall is your most important piece of…
Q: In a nutshell, what are the four primary causes for the rise in frequency of computer incidents?
A: Old, Unpatched Security Vulnerabilities For quite a long time, data security experts have been…
Q: Which Microcontroller category specifies processing speed before explaining and clarifying which…
A: Definition : Microcontroller Any microcontrollers can use 4-bit words and use as few as 4 kHz…
Q: CPU time is a vital computer resource that should be utilised as efficiently as possible. Explain…
A: Introduction: The DMA module bypasses the CPU and transmits the complete block of data to or from…
Q: Which of the folowing statements abut Scribus is contet? aNone of the obher getims 6 Seribus is…
A:
Q: Is there a wide variety of data structures to
A: The size of the data. The size of the storage. The data dynamics, such as changing or editing the…
Q: What is the name for an algorithm that is faster but takes up more space?
A: The efficiency of an algorithm is determined by the amount of time and space required to execute a…
Q: In data modeling, what is the purpose of a business rule?
A: Business rule A business rule is a statement that is precise and in brief used to impose constraints…
Q: What are the three components of the software engineering paradigm, and what is the definition of…
A: Software is a set of instructions that tells the computer how to operate. This contrasts with the…
Q: What exactly is data communication? What are the essential elements of a data communication system…
A: Introduction Data is made up of basic facts that are processed to provide information. Text,…
Q: What are the legal ramifications of email forensic investigations?
A: Email has become the most important application on the Internet for message transmission, document…
Q: What is the layered approach to operating system design? What are the benefits and drawbacks of this…
A: Intro what is a layered approach to design an operating system? When an operating system is…
Q: What changes have occurred in computer security throughout the years?
A: Intro Information technology security, also known as cybersecurity or IT security, is the process…
Q: Examine how various organisations employ information systems.
A: Information Systems: In addition to these broad types of IT infrastructure, organizations use…
Q: Information technology Describe what the most significant distinction is between Internet access and…
A: Introduction Communication is most important when users are located at remote location. In this…
Q: Toll roads have different fees at different times of the day and on weekends. Write a function…
A:
Q: What are the advantages and disadvantages of the National Incident Management System (NIMS) in terms…
A: Introduction A system called the National Incident Management System (NIMS) helps all levels of…
Q: A direct-mapped cache is designed to store four words per cache line. It has 256 cache lines.…
A: Block size = 4 words = 4*4B = 16B So block offset bits is log 16=4 bits
Q: Many approaches for a processor that can decode encrypted data and system instructions as well as…
A: Introduction: A central processing unit (CPU) is the electrical equipment that executes instructions…
Q: hat are three examples of computer and information system applications in your daily life?
A: Introduction: When people and computers work together to cycle or decode information, the result is…
Q: ng in software engin
A: Software engineering is a systematic engineering way to deal with software development. A software…
Q: Recognize information systems and their users?
A: Basic types of information systems include the following: Management information systemAssistive…
Q: Computer science What is the maximum number of slots in a TDM frame if n signal sources with the…
A: Introduction: A method of transmitting and receiving separate signals across a shared signal route…
Q: Explain the evolution of the internet and its technological foundation.
A: Introduction: The Internet has dramatically changed the communications and computing industries. The…
Q: Explain briefly the criteria that the CELLULAR CONCEPT's development brought to the field of mobile…
A: Classification: The cellular a concept is a system-level approach that replaces a single high-power…
Q: What is the process for obtaining and categorising data in preparation for data entry?
A: Introduction: Data Preprocessing is a term used in computer science to describe the process of…
Q: What is the main distinction between the Internet and the phone system?
A: Introduction: The Internet is a global network of networks that is interconnected.
Q: Learn how to resolve some of the most common problems associated with Linux hardware, software, file…
A: Introduction: Linux hardware difficulties may occur for a variety of reasons. It's a good idea to…
Q: In terms of safety, how can the benefits and drawbacks of different forms of authentication be…
A: Distinguished: Being differentiated means valuing someone. It's not uncommon for outstanding…
Q: How familiar are you with firewall management techniques? Explain
A: Introduction Several of the most effective firewall management practices include the following:…
Q: Information centers that want to automate some or all of their operations should take a strategic…
A: Given: Automation is a technology that employs a variety of control methods to achieve results with…
Q: What are the requirements for establishing a VPN between two networks?
A: VPN stands for Virtual Private Network. It portrays the valuable chance to lay out a protected…
Q: computer science - What are some examples of organisations that use databases in their information…
A: Introduction: A database is a collection of data that is linked together. It is critical for every…
Q: "Information technology is a benefit," compose a brief paragraph
A: Introduction: Information technology: Provides data access from any location. Multiple perspectives…
Q: Does the Branch Target Buffer have an advantage over the Branch History Table in terms of run time…
A: A branch target buffer is a buffer that is indexed by the branch instruction address with a tag…
Q: Is it possible to speed up the process of reprogramming views?
A: View controllers play an important role in the process of preserving and restoring state. Preserving…
Q: Give THREE (3) examples of network vulnerabilities and explain the term "vulnerability" in the…
A: Introduction: Vulnerability: It refers to a system or network flaw that allows attackers or hackers…
Q: What are the three components of the software engineering paradigm, and what is the definition of…
A: Definition: you must figure out what software engineering is and what the three aspects of the…
Q: Multiple branches of a global company are set up in Pakistan. What kind of network would you…
A: Given: Business networking is the process of forming mutually beneficial relationships with other…
Q: Computer science What is stigmergy? Why is this a beneficial way of communication ?
A: Definition: Stigmergy is a mediated, indirect way of action coordination in which the trace of one…
Q: Utilize social networking sites to the greatest extent possible. Two of the most significant…
A: Social Networking Services: A social networking website (also known as a social networking site) is…
Q: What is the computer memory unit? Describe the various types of computer memories
A: Introduction: The memory of a computer is measured in bits, bytes, kilobytes, megabytes, and…
Q: he most popular cl
A: IntroductionCloud computing comes in three different service models, each of which caters to a…
Step by step
Solved in 4 steps

- Following code in C using random Name Reg no and highschool name Use switch case in C language to do the following: Create a restaurant with the name “Your Name - Reg_No – Name of your highschool” The restaurant should come with the options of delivery and take away and the choice should be displayed as “Delivery – Registration No” and “Takeaway – Name” Each option should have the same menu and an extra 15% charge be included if a customer wants home delivery Both menus should have two items that are customizable, such as a burger can have chillies removed, cheese added and extra mayonnaise. The user should have the option of choosing multiple items with multiple quantity. Print a bill in the end.The programming language is C++, write a program base on the given statement. Write a program that examines the value of a variable called TEMP.Then display the following messages, depending on the valueassigned to TEMP. TEMPERATURE MESSAGE Less than 0 ICEBetween 0 and 100 WATERExceeds 100 STEAMIn C programing complete the prompt in the picture: This is the code we are given to start with: void printTour(const tourType dest);tourType getData(); int main(){ }
- What is the output of this C++ program: #include <iostream> using namespace std; class Test { int x; }; int main() { Test t; t.x = 6; cout << t.x; return 0; } 6 0 compiler error random valueIn Python, local and global variables are both declared inside the method or block. True or FalseIn C++, State if the following variable names are valid or invalid. If it's invalid, state why. Note: invalid here means creating a syntax error. a) 1wayTicket b) employee_pay c) #zombies d) R66Y e) STOP! f) Final Exam
- [In C#] Write an application named SumInts that allows the user to enter any number of integers continuously until the user enters 999. Display the sum of the values entered, not including 999. using System; using static System.Console; class SumInts { static void Main() { // Write your main here. } }C Programming Does the below code segment work? If not, why? fscanf(stdin, "%s", &arrStudentMajorArray);write in c language and the program should read 5 employees RANDOMLY
- Write a C program which should handle books information for a book shop. It should be able to handle atleast 100 records. The program should store following information against a book. Note: Use only C-Programming for its solution (by using struct). Book Id (you may use index number as book ID) Book Code Book Name Author Name Publish Date Price No of copies in hand No of Copies sold Initialize 10 Books and initialize remaining with 0 and spaces. Create a menu, as given below, which should use above information to perform selected action from the given menu on the screen Add book (One book will be added. User will enter book id i.e. index number Record will be placed if code at that index is 0) Display book (Display Books in tabular format with nonzero codes only) Delete book (Place an empty record with 0 code and spaces at the selected index) Search book Sale book (First locate the book Id and check if code is not 0 then update No of Copies in hand and No of Copies sold accordingly)…C# offers a special set of operators known as __________ that are designed specifically for changing the value of a variable without having to type the variable name twice. a. combined assignment operators b. advanced math operators c. variable modifiers d. assignment sequencersThe below code is the code that it’s mentioned in the question! Please write your in C language, and put it in text so i can copy it! Thanks





