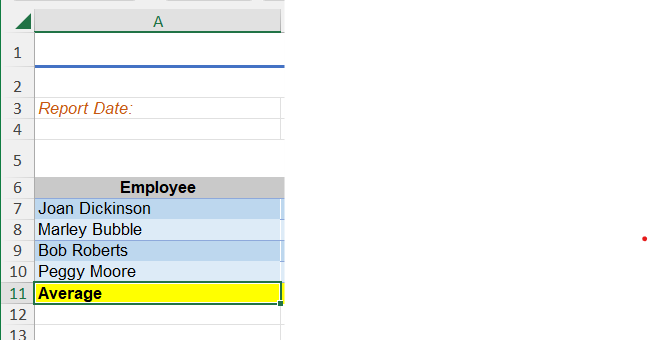
In cell A11, increase the indent of the cell contents twice.
Q: I need help with getting started for this in Java. Codes listed below. Complete the…
A: Here is the implementation for CircularArrayQueue class as follows: CODE: import…
Q: In what ways do advancements in Big Data scare the public?
A: Introduction: The processes of data capture, collection, and processing will all benefit…
Q: Outline how the spiral model may help the Waterfall and Prototyping approaches to software…
A: Introduction: The Spiral Model is an approach to the risk management system development life-cycle…
Q: please answer with proper explanation and step by step solution with final answer conclusion.…
A: To calculate the transmission rate in bits/sec, we need to know the size of the picture frame in…
Q: In the field of software engineering, what exactly is the role that design patterns play? Is there a…
A: Introduction: A reusable response to a typical problem in software design is a software engineering…
Q: The inquiry into the history of the file system's hierarchical structure continues.
A: File system's hierarchical structure: A file system's hierarchical structure is a way of organizing…
Q: Using the IDLE development environment, create a Python script named tryme4.py. (Note: an…
A: The source code of the program def new_line(): print('.') def three_lines(): new_line()…
Q: What are the primary distinctions between a system architecture that uses fat clients and one that…
A: Introduction: While all other layers are built on the server, the presentation layer is introduced…
Q: Could you provide me some specific instances of how virtual servers have been used in schools or…
A: A dedicated capability of a real server may be recreated using a virtual server. By installing a…
Q: Run: 1 2 3 4 56789GENERALEGGE 10 11 12 13 14 15 16 17 18 19 20 个 =1 project.py import pandas as pd…
A: The error message says that the module "pandas" is not found, which means that the library "pandas"…
Q: Just what does it imply when you say "Data Purging"?
A: Definition Data purging is a technique used in database management systems to ensure that only…
Q: Write a console program similar to the one shown in class. Given a quadratic equation: ax² + bx + c…
A: 1. Take input for a,b and c2. Calculate the value of r = b2 - 4ac3. Check the value of r a. If r…
Q: write a java program to demonstrate session tracking
A: The code following is a Java servlet that demonstrates session tracking using HttpSession. The…
Q: What were some of the primary motivating factors that led to the creation of computer languages?
A: Changing Forms of Programming Languages Indeed, programming languages are the building blocks of the…
Q: What qualities do you believe a business with a "offshore 'hot location' " should have? When and why…
A: I'll just respond to the first question, to begin with. Please send it separately the next time if…
Q: Could you please list the top three ways to improve the speed of your program?
A: Code Improvement MethodsThere are three approaches to optimize codes: 1. Common sub-expression…
Q: The Stack is one of the several forms of memory in an 8086 microprocessor. You are expected to…
A: Introduction : Stack push and pop are two operations performed on a data structure called a stack. A…
Q: The main idea behind the Global System Mobile (GSM) cellular radio system is frequency reuse. Due to…
A: The Global System Mobile (GSM) cellular radio system The Global System Mobile (GSM) cellular radio…
Q: Question 11 mah .Add. (1)/(9b)+(5)/(6b) Simplify your answer as much as pos Full explain this…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: Just explain what Big Data is and how it works. When it comes to competitive advantages, what are…
A: Data Overview: Data is information that is collected, organized, and analyzed for the purpose of…
Q: Please give a thorough breakdown of how object-oriented and procedural languages differ from one…
A: Programs that follow procedures are built on subprograms, commonly referred to as functions. Any…
Q: In what ways can we guarantee the security of data while its collection in the field? How can we…
A: security of data:- Data security is the protection of digital information from unauthorized access,…
Q: To what extent are the contents of a Master file intended to be preserved indefinitely?
A: INTRODUCTION: What we mean when we say "data" is a representation of facts, thoughts, or…
Q: Because it keeps information for so long, is it essential to have a Master file?
A: Introduction : A master file is a file that contains all of the data and information related to a…
Q: Write a program to read a text file line by line and display each word separated by '#'
A: Since , specific programming language was not mentioned. So, I have chosen Python Programming…
Q: The CPU, the CMOS, and the I/O cannot all use the same system bus. Pick one: What do you think?
A: The functionality of the Data Bus, Address Bus, and System Bus are combined in the System Bus. It…
Q: There are a number of ways in which the spiral model of software development may benefit both the…
A: Programming development The invention, design, deployment, and maintenance of software are all part…
Q: How does having a connection all over the world affect cloud computing, and what are some of the…
A: In this question we need to explain effect of global connection on cloud computing along with its…
Q: Explain the value of Design Patterns and why they should be used while creating software. Can you…
A: To problems that often arise in a particular context in software design. They are a crucial…
Q: Regarding these three features, where does TCP vary from UDP?
A: TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are two of the most commonly…
Q: What are the most important drawbacks of having two different levels in the system? What are your…
A: What is the primary disadvantage of a two-tier architecture? Can a multitier client–server technique…
Q: what are the key learnings of the article” Machine Learning-Based Analysis of Cryptocurrency Market…
A: Introduction One of the most well-known monetary institutions in existence at the time,…
Q: Why should I invest in software that automates server software installation and configuration? Can…
A: What are the benefits of providing and configuring servers automatically? What are the downsides of…
Q: What are some of the most common objections to implementing IoT?
A: In this question we have to understand most common objections for implementing the Internet of…
Q: let rec longer (xs, ys) match (xs, ys) with | (_, []) -> true (* line 1 *) | ([],_) -> false (* line…
A: In this question we have to discuss and answer the for each of the following alternate orders of the…
Q: Write methods that implement linear, binary, and recursive binary search. Have both methods display…
A: import java.util.Arrays; public class Search { public static void main(String[] args) {…
Q: What kinds of adapters are necessary for servers that are connected to an FCoE storage network?
A: 1) FCoE stands for Fibre Channel over Ethernet, it is a storage protocol that enables Fibre Channel…
Q: We consider a noisy communication link in which the message is encoded into binary digits (0,1)…
A: ANSWER 1: The probability that the received message has errors which go undetected can be…
Q: In the end, what is it that we hope to achieve with the aid of AI? Is it possible for you to go over…
A: In this question we have to understand what is it that we hope to achieve with the aid of AI? Is it…
Q: Give both the benefits and drawbacks of using magnetic secondary storage systems as opposed to…
A: The answer is given in the below step
Q: Which of the following is the correct way to run a .jar file named myProgram.jar from command line…
A: A JAR (Java Archive) file is a file format that aggregates many files into one archive file. It is…
Q: How does the use of foreign keys contribute to the reliability and comprehensiveness of the…
A: An entity or set of entities in a relational database connection known as a foreign key serves as a…
Q: Write a program that first gets a list of integers from input. The input begins with an integer…
A: Algorithm: Resultant algorithm for given problem is: Start def get_user_input(): Initialise myList…
Q: If T₁ (n) and T₂(n) are the time complexities of two program fragments På and P₂, where T₁(n)=…
A: Since T1(?) ≤ ?. ?(?) for some positive number c and positive integer n1 such that ?≥n1 and…
Q: When it comes to software engineering, what exactly is the point and purpose of prototyping?
A: Introduction: In this section, we must explain the objectives of software engineering prototyping.…
Q: In addition to the IP Protocol which is at layer 3, the following protocols are also known except:…
A: The question is seeking to determine which protocol from a list of four (RARP, ARP, DHCP, and ICMP)…
Q: 7. Use the UNION operator to generate a result set consisting of three columns from the Products…
A: The UNION operator in SQL is used to combine the results of two or more SELECT queries into a single…
Q: 2) Analyse the above transmission situation and describe the transmission procedure. In your…
A: CSMA/CA stands for Carrier Sense Multiple Access with Collision Avoidance. It is a type of network…
Q: How Many K-Bytes does a frame buffer needs if the resolution of the display monitor is 600 x 400…
A: As not given, we are considering that each pixel of the display is represented by 1 bit only. Now…
Q: suppose two hosts, A and B, are separated by 20,000 kilometers and are connected by a direct link of…
A: The bandwidth-delay product is the product of the link's bandwidth and the delay caused by the…
In cell A11, increase the indent of the cell contents twice.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Patient Medication Form Patient Number: P10034 Full name: Elbert McDonald Ward Number: Ward 11 Bed Number: B4 Ward Name: Orthopaedic Drug Number Name Description Dosage Method of Admin Unit per Day Start Date Finish Date 10223 10334 10223 Morphine Tetracyclene Morphine Pain Killer Antibiotic Pain Killer 10mg/ml 0.5mg/ml 10mg/ml Oral IV Oral 50 10 10 24/03/04 24/03/04 25/04/05 24/04/05 17/04/04 02/05/06 Examine the Patient Medication Form above: Put the above form into a relation schema Identify the functional dependencies.hw questionq3.3(student num(1805010554)
- Guido van Rossum guido@python.org +31 0474 33 88 26 Eric Idle eric@ericidle.com +44 20 7946 0958 The required info from instructor.State # letters in name Year entered the Union Rank for entering the Union Area (square miles) Alabama 77 1819 2222 52,42352,423 Colorado 88 1876 3838 104,100104,100 Hawaii 66 1959 5050 10,93210,932 Iowa 44 1846 2929 56,27656,276 Maryland 88 1788 77 12,40712,407 Missouri 88 1821 2424 69,70969,709 New Jersey 99 1787 33 8,7228,722 Ohio 44 1803 1717 44,82844,828 South Carolina 1313 1788 88 32,00832,008 Utah 44 1896 4545 84,90484,904 Wisconsin 99 1848 3030 65,49965,499 We are interested in whether or not the number of letters in a state name depends upon the year the state entered the Union. (a) Decide which variable should be the independent variable and which should be the dependent variable.Year the state entered the Union is the Click for List variable and the number of letters in a state name is the Click for List variable (c) Does it appear from inspection that there is a…DB - Normalization Question # 1 Patient Medication Form Patient Number: P10034 Full name: Elbert McDonald Ward Number: Ward 11 Bed Number: B4 Ward Name: Orthopaedic Drug Number Name Description Dosage Method of Admin Unit per Day Start Date Finish Date 10223 10334 10223 Morphine Tetracyclene Morphine Pain Killer Antibiotic Pain Killer 10mg/ml 0.5mg/ml 10mg/ml Oral IV Oral 50 10 10 24/03/04 24/03/04 25/04/05 24/04/05 17/04/04 02/05/06 Examine the Patient Medication Form above: Put the above form into a relation schema Identify the functional dependencies. Describe and illustrate the process of normalization to produce 3NF relations. Question#2: Given the following Theatre Database form: No.of seats:500 Owner: J.Martin Year Founded: 1890 Owner’s Phone: 2347756 - - - - - Play Name Play Type No. of performances…
- Explain 404 Not Found in simple wordsUsing KNN algorithm to find the 05 similar movies from the movies below. Movie ID Movie Name IMDB Rating Biography Drama Thriller Comedy Crime Mystery History Label 58 The Imitation Game 8 1 1 1 0 0 0 0 0 8 Ex Machina 7.7 0 1 0 0 0 1 0 0 46 A Beautiful Mind 8.2 1 1 0 0 0 0 0 0 62 Good Will Hunting 8.3 0 1 0 0 0 0 0 0 97 Forrest Gump 8.8 0 1 0 0 0 0 0 0 98 21 6.8 0 1 0 0 1 0 1 0 31 Gifted 7.6 0 1 0 0 0 0 0 0 3 Travelling Salesman 5.9 0 1 0 0 0 1 0 0 51 Avatar 7.9 0 0 0 0 0 0 0 0 47 The Karate Kid 7.2 0 1 0 0 0 0 0 0 50 A Brilliant Young Mind 7.2 0 1 0 0 0 0 0 0 49 A Time To Kill 7.4 0 1 1 0 1 0 0 0 30 Interstellar 8.6 0 1 0 0 0 0 0 0 94 The Wolf of…Name Paul J Mitchell Justin M Combs John L Brown Pamela C Dixon Mary M Jackson Marjorie A Stephen Valeria H Jacobs Scott E Williams Ruth A Owens Justin M Combs Derrick O Chacon Omar I Nelson Valeria H Jacobs Justin B Dunleavy Linda M Briones Scott E Williams Telephone number 360-536-8867 925-465-9657 847-708-4329 815-562-9538 760-394-4546 517-549-6632 404-520-2758 956-327-5997 972-988-9510 925-465-9657 417-796-2387 301-902-0592 404-520-2758 518-774-5147 215-235-8596 956-327-5997 Instructions: Conditionally format the cells in the Name column using a custom formula that applies the Default green background if the COUNTIF formula is greater than one. For the first criteria of this first COUNTIF function, fix the rows of the range with $ but do not fix the columns (e.g. A$3:A$18). Write a similar rule that conditionally formats the cells in the Phone number column with the same Default green background. Based…
- Normalize the following table to the 3rd Normal form: Student Student Phone Course Term Grade Instructor Instructor Phone Lauren Fernell 555-7771 MIS 350 F12 A Hess 555-2222 Lauren Fernell 555-7771 MIS 372 F12 B Sarker 555-2224 Lauren Fernell 555-7771 MIS 426 F12 A Fuller 555-2227 Lauren Fernell 555-7771 MIS 375 F12 B+ Wells 555-2228 Brigit Schnieder 555-2215 MIS 350 F12 A Hess 555-2222 Brigit Schnieder 555-2215 MIS 375 F12 B+ Wells 555-2228 Brigit Schnieder 555-2215 MIS 372 F12 A Sarker 555-2224 Brigit Schnieder 555-2215 MIS 374 F12 B Clay 555-2221 Jackie Judson 555-1245 MIS 350 F12 A Hess 555-2222 Jackie Judson 555-1245 MIS 372 F12 B+ Sarker 555-2224 How many tables did you create after normalizing the table? List each of…Need urgent answer. Don't provide wrong answer. Provide typing answer. Sub: Algorithm Dept:CseNormalize the data (use mean and mean absolute deviation). Use a 3 nearest-neighbor algorithm to assign the class label to Bryan [Bryan, 29, $50,000] Note: Please type the solution











