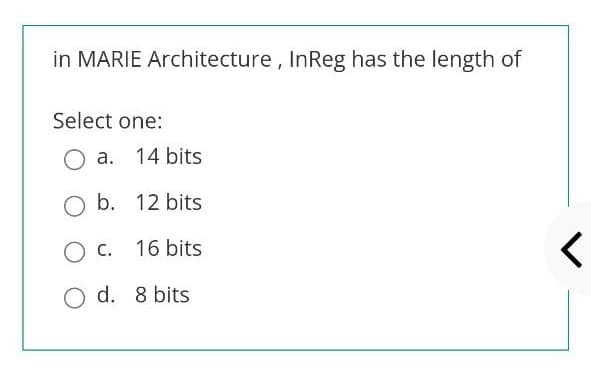
in MARIE Architecture, InReg has the length of Select one: O a. 14 bits O b. 12 bits O c. 16 bits O d. 8 bits
Q: Make five recommendations for increasing email privacy in an organization after reading this chapter…
A: Five tips for enhancing an organization's email privacy- 1) Having a decent antivirus programme…
Q: The relationship between cohesion and coupling in software development is a complex issue. How may…
A: Definition: Here's the answer to the question, as well as an explanation. The interconnectedness of…
Q: However, the incident report team must have defined duties and a plan of action.
A: Introduction: Individuals are required for the incidence response because an effective reaction…
Q: Do you know how to tell the difference between hardware and software interrupts
A: Please find the answer below :
Q: In what ways does the usage of a siloed information system create concerns and problems?
A: In what ways does the usage of a siloed information system create concerns and problems?
Q: What does the saying "Resist the urge to code" imply in the context of programming??
A: Introduction: Resist the urge to code: This suggests that a software engineer should first…
Q: Demonstrate fundamental knowledge of several system development life cycles (prototyping; Agile;…
A:
Q: Commands Show/hide help * Set the Fibonacci number to calculate. n = 10; our own script - turn it…
A: Code: function fn = fib(n)if n<=2fn=1;elseF=ones(1,n);for…
Q: A vet clinic "XYZ Vets" has a website with registration and login pages for its clients. The…
A: Our guidelines is answer the first three question so we will do first three and this data i have…
Q: High Availability vs. Fault Tolerance: What's the difference?
A: JUSTIFICATION: A twin-engine aero plane is a fault-tolerant system, meaning that if one engine…
Q: Describe how third-party cookies are made in your own words.
A: Cookies from third parties: A third-party cookie is one that is placed on a website by someone other…
Q: 1011 BASE 2 + 1011 BASE 2 + 1101 BASE 2 + A BASE 16=_______BASE 10
A: As per our guidelines we are supposed to answer only one question. Kindly repost other questions as…
Q: Computer Science Think of an example of an innovation you have studied at work or school. How would…
A:
Q: Merge sort algorithm is about to complete the sort and is at the point just before the last merge.…
A: The program is written in Java. Check the program screenshot for the correct indentation. Please…
Q: What are the benefits and drawbacks of using the logical representation and the semantic network…
A: let us see the answer:- Logical Representation A language having precise rules for dealing with…
Q: What methods can be used to deal with massive data sets, which can be terabytes in size and are…
A: Massive Data Sets: Simply said, big data refers to larger, more complicated data sets, particularly…
Q: Choose one of the Base Cases you created in Spring Breaks "R" Us Travel Booking Case Study , that…
A: Please find the detailed explanation in the following steps.
Q: Make five recommendations for increasing email privacy in an organization after reading this chapter…
A: A data leakage incident often referred to as an information leakage incident is the unlawful…
Q: Do software development and software modeling differ? Describe how each aids the other in software…
A: The Methodology of Software Development In software engineering, a software process divides…
Q: What tools and technologies are available to help with software testing and development? Provide…
A:
Q: The five most frequent network topologies should be outlined. Which one do you consider to be the…
A: Given: We have to discuss The five most frequent network topologies should be outlined. Which one…
Q: What is an interruption? Describe their types and why no hardware interrupts arrive.
A: An act of interrupting something or someone or the state of being: A signal to interrupt the…
Q: Distinguish between Agile and XP system development methods.
A: Agile and XP System: Extreme Programming, like other Agile techniques, involves the client in the…
Q: The XML document should be stored in an XML database, right?
A: Given: XML documents are represented logically in an XML database, and the data is stored and…
Q: using a code in Linux As a developer, a local Library approaches you and requests you to develop a…
A: import java.awt.event.ActionEvent; import java.awt.event.ActionListener; import java.sql.*; import…
Q: Interruptions are described using the following terms: Explain their types and why no hardware…
A: Hardware Interrupts: An interrupt is a signal received by the processor that causes the program to…
Q: Examples of when each is utilized should be provided, along with a description of the differences…
A: Interruptions caused by hardware: To produce hardware interrupts, physical impulses from inside the…
Q: Describe how third-party cookies are made in your own words.
A: A third-party cookie is placed on a website by someone other than the owner (a third party) to…
Q: Which of the three kinds of information systems are you most familiar with?
A: An information system is a collection of interconnected components that enable the collection,…
Q: For each serializable schedule, determine the equivalent serial schedules. a. r1(X); r3(X); w1(X);…
A: The Answer is in step-2.
Q: What are the components of a computer system that is fault tolerant?
A: Fault tolerance refers to a system's capacity to continue working uninterrupted when one or more of…
Q: & Moving to the next question prevents changes to this anwer. Question 6 Decrypt the following…
A:
Q: Can you please explain around six hundred fifty words about the process of spanning tree protocol…
A: Various hardware screw ups, misconfigurations, or miscabling reason the bulk of STP screw ups,…
Q: Super@WUDOL MINGW64 ~/Desktop/cse1001/lab23 $ java Countdown.java Enter a number: 10 10 9 8 3 2 1…
A: Here I have defined the method named recursiveCountdown(). In this method, I have printed the…
Q: A semaphore's role in the coordination of two or more operations may be explained.
A: SEMAPHORE: A variable in the operating system is used to control the number of processes that are…
Q: How do a processor that processes instruction sets differs from an embedded system, an embedded…
A: Embedded Processor: A microprocessor explicitly created for an embedded system is known as an…
Q: Discuss the internet's development and the technical foundations upon which it is built.
A: Introduction: Researchers began constructing the "network of networks" that would become the modern…
Q: To connect patient monitoring devices to EHRS safely and reliably, what steps must EHR software…
A: Computerized Health Record (EHR): An Electronic Health Record is a computer-readable record of an…
Q: explain why it's critical to understand these links when designing network systems
A: Network Influence- The topology of a network is a diagram that depicts the current state of the…
Q: Consider how reporting systems, data mining systems, and Big Data systems differ. What do they have…
A: The distinctions between reporting systems, data mining systems, and big data systems are as…
Q: What are the four most basic elements of software development? Please let us know which of the other…
A: Introduction: These are the four primary process tasks that are organized differently in different…
Q: In what ways do websites contribute to an individual's health-care needs? In what ways are…
A: In what ways do websites contribute to an individual's health-care needs? In what ways are…
Q: JAVA PROGRAM JFRAME FORM please help on what code should I use to get these jframe forms:
A: As per the requirement program is developed. Note: use username = 'john' and password ='1234' for…
Q: Exactly what is the difference between the "system" and "user" areas?
A: System and user Areas: The user area might include everything from broad declarations of required…
Q: Explain briefly the sorts of interruptions and why they are crucial to the machine.
A: Interrupt and its classification When a process or event requires rapid attention, an interrupt is a…
Q: Comparing all potential network topologies requires a table.
A: Introduction: This topic asks to develop a table comparing all potential network topologies. A…
Q: What are the advantages and disadvantages of using the cloud to store data? Examples of cloud-based…
A: There are a handful of well-known, major public: According to the question, cloud storage is always…
Q: Consider the case of a page fault. What aspect of the operating system are they tied to? In the most…
A: reaching a long distance from a surface or area: for example. a: a deep well, a deep abyss that…
Q: information system
A: An information system (IS) is a structured, sociotechnical organisational structure used to gather,…
Q: So why is software development vital? .. How do you think the software development process may…
A: Software development vital: Software engineers have aided society by making our lives easier,…
Step by step
Solved in 2 steps

- Explain why, in MARIE, the MAR is only 12 bits wide while the AC is 16 bits wide. Hint: Consider the difference between data and addresses.Explain why, in MARIE,the MAR is only 12 bits wide while the AC is 16 biys wide.give the 9-bit microoperation field for the following micro- operations: a. AC←AC + 1, DR←DR + 1 b. PC←PC + 1, DR←M[AR] c. DR←AC, AC←DR
- Question 33334 Computer Architecture Use 4-bit version (result 8-bit), do the division with the given data 5ten (dividend) and 2ten (divisor), or 0101two and 0011two. Use Algorithm1 only that has 64-bit ALU.Assume that IEEE 754 floating point format is used and $f1 and $f2 store the floating numbers as below: $f1: 1000 1010 0110 1110 1001 1000 0000 0000 $f2: 1000 1010 0100 1111 0100 0010 0000 0000 What are the values of each register? What is the result computing for ($f1+$f2)What is the binary encoding of the following RISC-V assembly instruction? Please write your answer as an 8-digit hexadecimal number. slli x6, x7, 8
- Write an appropriate assembly language code for the following operation and interpret to Von Neumann IAS architecture Z=A/B Where A-greater than 40 bit data B-greater than 40 bit dataComputer Architecture Given the below IEEE single precision FP format: 1-bit Sign , 8-bit Biased Exponent , 23-bit Mantissa , Bias = 127 Convert (9.625)10 to IEEE 32-bit floating-point format.(RISC-V) Write an instruction that calculates the bitwise Exclusive OR of x3 and 466 (in decimal) and stores the result in x18.



